Network Security —
Welcome and introduction
T-110.5241 Network security,
Nov-Dec 2011
Tuomas Aura
Aalto University
Lecturer
Lecturer: Tuomas Aura
PhD from Helsinki University of Technology in 2000
Microsoft Research, UK, 2001–2009
Professor at Aalto 2008–
Research:
Network security
DoS resistance
Security protocol engineering
Security of mobility protocols (Mobile IPv6, SEND, etc.)
Privacy of mobile users
2
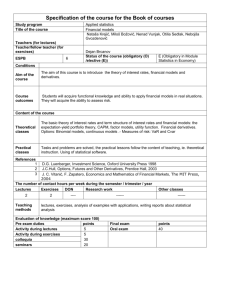
Required background
Students are expected to understand:
Networking technologies: TCP/IP, 802.11, UMTS etc.
Basic security concepts, e.g. T-110.4206 Information
security technology
Basic cryptography, e.g. T-110.5211 Cryptosystems
3
Lectures
Lecturer: Tuomas Aura
12 lectures in Nov-Dec 2011
Wednesdays 14:15-16 T4
Thursdays 14:15-16 T6
Attendance not mandatory but much of the
material will only be covered in the lectures
No tutorial or exercise sessions
4
Exercises
5 exercise rounds, starting next week
Exercise problems in Noppa by Sunday each week (first
round on 6 November)
Deadline on the following Sunday 23:59;
reports to be returned to Rubyric
Course assistants
Aapo Kalliola and Jaakko Salo
email: t-110.5241@tkk.fi
Course assistants available in the Playroom for advice and
equipment:
Tuesdays 16:15-18 room A120
Thursdays 16:15-18 room A120
Any exercises not returned in period II can be done in period
III on a similar weekly schedule
Please do not ask to redo exercises unless critical to pass the course
5
Advice for exercises
Try to solve all problems at least partly
The goal in many of the exercises is to learn how to
find information and read standards
Individual work: It is ok to discuss with other
students but do not copy or even read the written
answers of others students. Do all practical
experiments independently
You are allowed to cut and paste relevant short
passages from standards, but mark it clearly as a
”quotation” and give the source, e.g. [RFC 1234,
section 5.6.7]
6
Assessment
First examination 12 Dec 2011 9-12 in T1
Register for exams 1-2 weeks before
Examination scope: lectures, protocol standards,
recommended reading material, exercises, good general
knowledge of the topic area
Exercises are not mandatory but strongly recommended
Marking:
exam max. 30 points
exercises max 5 x 20 = 100 points
grading based on
total points = exam + (exercises / 10)
(total max 30+10=40 points)
Course feedback is mandatory
7
Goals
Know common communications systems, classic
security mechanisms, standard security solutions,
and some of the latest ideas
Understand network security technologies, their
properties and limitations to use them right
Be aware of the pitfalls in security engineering: security is
not just mathematics or just code
Learn the adversarial mindset of security engineering
Basic security analysis of network security protocols
Starting point for learning more on the job or in
further studies
Another goal: learning to read protocol standards
8
Tentative course outline
Network security threats and goals
2. Email security, advanced PKI
3. TLS / SSL internals
4. Security protocol design, Kerberos
5. WLAN security
6. Multicast and routing security
7. Firewalls, IPsec
8. Cellular network security
9. Securing mobility
10. Network intrusion detection (NN)
11. Denial of service (Aapo Kalliola)
12. Anonymity
1.
Changes to this plan are likely.
9
Recommended reading
William Stallings, Network security essentials:
applications and standards, 4th ed., Pearson
Prentice Hall, 2010 (or 3rd ed.)
Kaufman, Perlman, and Speciner, Network security:
PRIVATE communication in a PUBLIC world,
Prentice-Hall, 2002 (somewhat old)
RFCs and standards, web links from Wikipedia
10
Course feedback and development
Students felt the course was not too much work. Credits increased from
4 to 5. The weight of the exercises in the grading increased accordingly.
We have increased the role of hands-on exercises, which were popular.
The fall semester is rather busy for many students. We added the option
to do all or some exercises in period III.
No introductory wireshark exercise because it was already familiar to
students.
Leaving out parts that overlap with more basic courses. Slides on some
such topics are included in the reading material, though.
Trying to explain better the purpose of the standards-related exercises.
The aim is to learn to read protocol standards and to find authoritative
answers to questions. Thus, it is not sufficient to Google for the answers
in Wikipedia but everyone should refer to the original standard text.
Adding a protocol design or analysis puzzle to each lecture. Decided to
do this instead of additional homework to limit the course workload.
11
 0
0