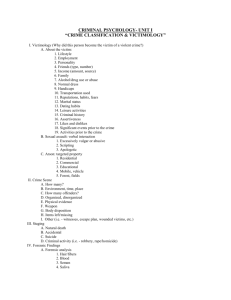
Chapter 15
Computer crime and information technology security
When you finish studying this chapter, you should be able to:
Explain Carter’s taxonomy of computer crime
Identify and describe business risks and threats to information systems
Name and describe common types of computer criminals
Discuss ways to prevent and detect computer crime
Explain COBIT’s information criteria and accountability framework
Explain how COBIT can be used to strengthen internal controls against computer crime
I.
Carter’s taxonomy
Target: targets the system or its data
Instrumentality: computer furthers a criminal end
Incidental: computer is not required for the crime but is related to the criminal act
Associated: new versions of traditional crimes
II.
Risks and threats to information systems
Fraud: Any illegal act for which knowledge of computer technology is used to commit the
offense
Service interruptions and delays: Delay in processing information
Intrusions: Bypassing security controls or exploiting a lack of adequate controls
Information manipulation: Can occur at virtually any stage of information processing from input
to output
CHAPTER 15 / Page | 1
III.
Risks and threats to information systems
Denial of service attacks: Prevent computer systems and networks from functioning in
accordance with their intended purpose
Error: Can vary widely
Disclosure of confidential information: Can have major impacts on an organization's financial
health
Information theft: Targets the organization's most precious asset: information
Malicious software: Virus, Trojan horse, worms, logic bombs
Web site defacements: Digital graffiti where intruders modify pages
Extortion: Threat to either reveal information to the public or to launch a prolonged denial of
service if demands are not met
IV.
Computer criminals
Script kiddies: Young inexperienced hacker who uses tools and scripts written by others for the
purpose of attacking systems
Hacker: Someone who invades an information system for malicious purposes
Cyber-criminals: Hackers driven by financial gain
Organized crime: Spamming, phishing, extortion and all other profitable branches of computer
crime
Corporate spies: Computer intrusion techniques to gather information
Terrorists: Target the underlying computers and networks of a nation’s critical infrastructure
Insiders: May be the largest threat to a company’s information systems and underlying
computer infrastructure
CHAPTER 15 / Page | 2
V.
VI.
Prevention and detection techniques
CIA triad
•
Confidentiality
•
Data integrity
•
Availability
Internal controls
•
Physical: locks, security guards, badges, alarms
•
Technical: firewalls, intrusion detection, access controls, cryptography
•
Administrative: security policy, training, reviews
COBIT framework (3 + 4 = 7)
Control Objectives for Information and Related Technology
Published by Information Systems Audit and Control Association (ISACA)
•
Three points of view
• Business objectives
• IT resources
• IT processes
•
Four domains of knowledge
• Plan and organize
• Acquire and implement
• Deliver and support
• Monitor and evaluate
Seven information criteria
• Effectiveness
• Efficiency
• Confidentiality
• Integrity
• Availability
• Compliance
• Reliability of information
CHAPTER 15 / Page | 3
 0
0