CENTRAL MANAGEMENT
SYSTEM ADMINISTRATION GUIDE
RELEASE 9.1.4
Trellix, FireEye, and Skyhigh Security are the trademarks or registered trademarks of
Musarubra US LLC, FireEye Security Holdings US LLC, and their affiliates in the US
and/or other countries. McAfee is the trademark or registered trademark of McAfee
LLC or its subsidiaries in the US and/or other countries. Other names and brands are
the property of these companies or may be claimed as the property of others.
FireEye Security Holdings US LLC assumes no responsibility for any inaccuracies in
this document. FireEye Security Holdings US LLC reserves the right to change, modify,
transfer, or otherwise revise this publication without notice.
Copyright © 2022 FireEye Security Holdings US LLC. All rights reserved.
Central Management System Administration Guide
Software Release 9.1.4
Revision 1
Trellix Contact Information:
Website: www.fireeye.com
Technical Support: https://csportal.fireeye.com
Phone (US):
1.408.321.6300
1.877.FIREEYE
Contents
PART I: Overview
23
CHAPTER 1: About the Central Management Appliance
25
"Single Pane of Glass"
25
Alert Management
25
Alert Correlation
26
Signature Distribution
26
Submit to Malware Analysis for Deep Forensics
26
Appliance Groups
27
Central Management Deployment
27
Standard Deployment
27
Network Address Translation (NAT) Deployment
28
Single-Port Deployment
28
High Availability (HA) Deployment
28
Split DTI Traffic Deployment
29
MVX Cluster Deployment
29
Management Path
30
Central Management Appliances That Receive DTI Updates
30
Environments That Restrict Outbound Access to Certain IP Addresses
31
CM Appliances with Domain-based Proxy ACL Rules
31
Integrated CM Communications Protocol and Port Configurations
32
FIPS 140-2 and Common Criteria Compliance
32
CHAPTER 2: User Interfaces
33
Overview of CM User Interfaces
34
The CM Appliance Web UI
35
© 2022 FireEye Security Holdings US LLC
3
Contents
Browser Support
36
Screen Resolution Requirements
36
Logging In Locally to the Helix Appliance Web UI
36
Notifications of Appliance Health Problems
37
Notifications of Appliance Health Problems
37
Central Management Web UI Tabs
38
PDF Generation
40
The CM Appliance Command-Line Interface
40
The CM Appliance LCD Display
41
Navigating the LCD Menus
41
LCD Panel Menus
42
The CM Appliance IPMI Interface
44
IPMI Browser Support
45
Logging In to the IPMI Interface
45
Power Cycling and Resetting the Device
46
Accessing the Device Serial Console
47
Checking the Status of Device Sensors
48
Resetting the IPMI Interface Using the CLI
48
CHAPTER 3: The Appliance Dashboard
51
Central Management Dashboard Widgets
53
Alerts Summary
54
Cluster Connection Status
55
Supported Features
56
Service Health Statistics Trend
56
Cluster Utilization
57
Malware Analysis Widgets in the Central Management Dashboard
58
Email Security — Server Edition Widgets in the Central Management Dashboard58
File Protect Widgets in the Central Management Dashboard
59
Network Security Widgets in the Central Management Dashboard
60
Custom Dashboards
Cloning a Dashboard
4
61
62
© 2022 FireEye Security Holdings US LLC
Contents
Creating a New Dashboard
62
Reordering the Dashboard Names
63
Renaming a Custom Dashboard
63
Designating the Default Dashboard
63
Deleting a Custom Dashboard
64
Adding Widgets to a Custom Dashboard
64
Resizing a Widget in a Custom Dashboard
64
Moving a Widget in a Custom Dashboard
65
Removing a Widget from a Custom Dashboard
65
Dashboard and Widget Management
66
Configuring the Automatic Refresh Interval
67
Filtering the Data by Appliance or Appliance Group
67
Refreshing the Data Displayed in All Widgets
67
Configuring the Time Period Covered by All Widgets
68
Saving or Printing a Dashboard
68
Refreshing the Data Displayed in a Single Widget
68
Configuring the Time Period Covered by a Single Widget
69
Viewing a Single Widget in Full Screen Mode
69
Generating and Scheduling Dashboard Reports
69
PART II: Configuration
71
CHAPTER 4: Accessing the Physical or Serial Console
73
CHAPTER 5: Initial Configuration
77
Initial Configuration Overview
78
Initial Configuration Prerequisites
78
Configuring Initial Settings Using a Keyboard and Monitor
79
Configuring Initial Settings Using the Serial Console Port
80
Using a Windows or Mac Laptop
80
Using a Linux System
81
Using a Terminal Server
81
© 2022 FireEye Security Holdings US LLC
5
Contents
Configuration Wizard Steps
82
Configuring Initial Settings Using the LCD Panel
84
Configuring the IPMI Interface
85
Viewing the IPMI Configuration
86
Configuring the IPMI Port
86
Configuring IPv6 Addresses for the IPMI Interface
CHAPTER 6: Virtual Central Management Appliances
89
CHAPTER 7: License Keys
91
About Trellix License Keys
91
Types of Licenses
93
Subscription-Based Appliance License
93
Perpetual Appliance License
93
Overriding One-Way Sharing License
93
Override One-Way Sharing License Using the CLI
Automatic License Updates
94
95
How It Works
95
Enabling Automatic License Updates
96
Manual License Installation
98
Installing Licenses Using the Web UI
98
Removing Licenses Using the Web UI
99
Installing Licenses Using the CLI
100
Removing Licenses Using the CLI
101
Viewing License Notifications Using the Web UI
CHAPTER 8: The DTI Network
102
105
About the DTI Network
105
Threat Intelligence
105
Automatic License Updates
106
System Health Monitoring and Software Updates
107
About DTI Network Communication
6
87
108
© 2022 FireEye Security Holdings US LLC
Contents
About Support and Content License Sharing Combinations
109
Changing the Active Setting for a DTI Service
109
Changing the Active Source for a Standalone Appliance Using the Web UI
111
Changing the Active Source for a Managed Appliance Using the Web UI
112
Changing the Active Source for a Central Management Appliance Using the
Web UI
112
Changing the Active Source for a Central Management Appliance Using the
CLI
113
Changing the Global Active Source for Managed Appliances Using the Web UI 114
Changing Global Active DTI Settings for Managed Appliances Using the CLI
114
Using an HTTP Proxy for DTI Service Requests
116
Understanding the DTI Cache
117
Downloading Software Updates to the DTI Cache
119
Managing the DTI Cache
124
Validating DTI Access
129
Validating DTI Access Using the Web UI
130
Validating DTI Access Using the CLI
130
Configuring DTI Credentials
Configuring DTI Credentials Using the CLI
Automatic Validation of Security Content
132
132
133
About Automatic Validation of Security Content
133
Conditions That Indicate a Compatible Security Content Package
133
Error Codes for Incompatible Security Content Packages
134
Sharing Appliance Telemetry and Statistics
135
About Sharing Appliance Telemetry and Statistics With the DTI Cloud
136
Uploading Appliance Telemetry and Statistics Automatically Using the CLI
137
Uploading Appliance Telemetry and Statistics Manually Using the CLI
138
CHAPTER 9: System Security
139
AAA
139
Certificates
139
© 2022 FireEye Security Holdings US LLC
7
Contents
CHAPTER 10: System Email Settings
141
Configuring the Mail Server
142
Configuring the Mail Server Using the Web UI
143
Configuring the Mail Server for Health Check Notifications Using the CLI
144
Configuring the Mail Server for Scheduled Reports Using the CLI
146
Configuring Email Recipients
147
Configuring Email Recipients Using the Web UI
148
Configuring Email Recipients Using the CLI
149
Configuring System Events
151
Configuring System Event Notifications Using the Web UI
151
Configuring System Event Notifications Using the CLI
152
Configuring Auto Support for System Event Notifications
154
Configuring Auto Support for System Event Notifications Using the CLI
CHAPTER 11: Date and Time Settings
157
Manual Time Configuration
157
Setting the Date and Time Using the Web UI
157
Setting the Date and Time Using the CLI
158
NTP Server Configuration
159
Configuring NTP Servers Using the Web UI
160
Configuring NTP Servers Using the CLI
161
Configuring NTP Authentication Using the CLI
164
Time Zone Configuration
168
Setting the Time Zone Using the Web UI
169
Setting the Time Zone Using the CLI
169
Synchronizing the System Clock to DTI Server Time Using the CLI
170
PART III: Administration
173
CHAPTER 12: Network Administration
175
Basic Network Configuration
175
Configuring Basic Network Settings Using the Web UI
8
155
177
© 2022 FireEye Security Holdings US LLC
Contents
Configuring Basic Network Settings Using the CLI
IP Filtering
180
181
Interfaces Supported by IP Filtering Rules
181
Viewing IP Filtering Rules
181
Enabling IP Filtering Using the CLI
182
Creating IPS Custom Variables Using the Web UI
Prerequisites
Configuring HTTP Proxy Server Settings
184
184
186
Configuring HTTP Proxy Server Settings Using the CLI
186
Disabling HTTP Proxy Server Settings Using the CLI
187
Defining Another Management Interface
Defining Another Management Interface Using the CLI
DTI Traffic and Management Traffic
Splitting DTI and Management Traffic Using the CLI
CHAPTER 13: Upgrading the FireEye Software
188
189
191
193
197
Before You Begin the Upgrade
197
Upgrading the Appliance Using the Web UI
198
Select an Upgrade Source
199
Check for Available Update Software
200
Download the Software
200
Install the Software Update
201
Validate the Software Updates
201
Upgrading the Appliance Using the CLI
201
Download and Install the Appliance Software Image
202
Restart the Appliance and Accept the EULA
203
Download Guest Images
203
Install Downloaded Guest Image Profiles
205
Download and Install Guest Images in a Single Command
206
Verify the Upgrade
206
Configuring Auto-Mounting on a USB Device
Enabling or Disabling Auto-Mounting on a USB Device Using the CLI
© 2022 FireEye Security Holdings US LLC
207
207
9
Contents
Configuring HTTP Access to Install Software Updates Using the CLI
208
Installing Guest Images from a USB Device Using the CLI
209
Mounting or Unmounting a USB Device Using the CLI
210
CHAPTER 14: IPMI and BIOS Firmware Updates
213
Updating IPMI and BIOS Firmware
214
Updating IPMI Firmware
214
Updating BIOS Firmware
215
Enabling and Disabling IPMI Firmware Notifications Using the CLI
215
CHAPTER 15: Log Management
217
Managing Logs Using the Web UI
217
Viewing the Current Log Configuration
220
Configuring a Syslog Server Using the CLI
221
Configuring the Minimum Severity of Messages Sent to Syslog Servers Using the
CLI
222
Configuring the Minimum Severity of Messages Stored on the Local Drive Using
the CLI
224
Excluding System Internal Audit Messages from the Audit Log File Using the CLI 226
Configuring Log Rotation for Specific Types of Log Files
227
Viewing Log Rotation Configuration Using the CLI
227
Configuring the Timestamp Format Using the CLI
229
Uploading the Active Log File to a Network Location Using the CLI
231
CHAPTER 16: Database Backup and Restore
233
Database Backup and Restore Introduction
233
Task List for Database Backup and Restore
234
Viewing the Last Backup and Restore Results
234
Viewing the Last Backup and Restore Results Using the Web UI
235
Viewing the Last Backup and Restore Status Using the CLI
235
Estimating the Space Needed for the Backup File
236
Estimating the Space Needed for the Backup File Using the Web UI
10
236
© 2022 FireEye Security Holdings US LLC
Contents
Estimating the Space Needed for the Backup File Using the CLI
Backing Up the Database
237
237
Backing Up the Database Using the Web UI
238
Backing Up the Database Using the CLI
239
Limiting the Number of Backup Files on Your Appliance
242
Scheduling Automatic Backups
242
Scheduling Automatic Backups Using the CLI
Downloading Backup Files
Downloading Backup Files Using the Web UI
Uploading Backup Files
Uploading Backup Files Using the Web UI
Restoring the Database from a Backup File
243
245
246
246
246
247
Restoring the Database from a Backup File Using the Web UI
248
Restoring the Database from a Backup File Using the CLI
249
Deleting Previous Backup Files
251
Deleting Previous Backup Files Using the Web UI
251
Deleting Previous Backup Files Using the CLI
252
CHAPTER 17: System Health and Performance
Viewing System Health and Performance Check Results
Viewing System Health and Performance Check Results Using the Web UI
Checking System Health and Status
253
253
254
257
Checking System Health Using the Web UI
257
Checking System Health Using the CLI
263
CHAPTER 18: SNMP Data
269
Retrieving SNMP Data
269
Providing Access to SNMP Data
270
Downloading the MIB
270
Sending Requests for SNMP Information
272
Sending Traps
Enabling and Configuring Traps
© 2022 FireEye Security Holdings US LLC
273
273
11
Contents
Logging Trap Messages
274
CHAPTER 19: Login Banners and Messages
277
About Login Banners and Messages
277
Customizing Login Banners and Messages Using the Web UI
278
Customizing Login Banners and Messages Using the CLI
279
CHAPTER 20: Supported Features
283
Viewing Supported Features Using the Web UI
283
CHAPTER 21: Event Notifications
285
Configuring Event Notifications Using the Web UI
285
Configuring Event Notifications
286
CSV Fields for Daily Digest Notifications
287
Configuring Email Notifications Using the Web UI
289
Configuring HTTP Notifications Using the Web UI
291
Configuring Rsyslog Notifications Using the Web UI
295
Configuring SNMP Notifications Using the Web UI
299
Configuring Event Notifications Using the CLI
301
Configuring Event Notifications
301
Configuring Email Notifications Using the CLI
302
Configuring HTTP Notifications Using the CLI
311
Configuring Rsyslog Notifications Using the CLI
318
Configuring SNMP Notifications Using the CLI
325
Configuring the Proxy Server for Notifications
330
Configuring the Proxy Server for Notifications Using the CLI
Configuring ATI Alert Updates for Notifications
331
Configuring ATI Alert Updates for Notifications Using the CLI
332
CHAPTER 22: Disk Space Management
335
On-Demand Cleanup Using Profiles
335
Viewing a Summary of Disk Space Use Using the CLI
12
330
336
© 2022 FireEye Security Holdings US LLC
Contents
Viewing Disk Space Use By Profile Using the CLI
337
Deleting Data to Free Disk Space Using the CLI
337
CHAPTER 23: Boot Manager Utilities
339
Working with the Tools Menu
340
System Requirements
340
Setting the Tools Menu Password
342
Accessing the Tools Menu
344
Disabling the Tools Menu
346
Viewing Tools Menu Availability
347
Wiping Persistent Media
Wiping Persistent Media Using the Tools Menu
348
349
PART IV: Appliances
351
CHAPTER 24: Adding and Removing Appliances
353
Adding an Appliance Using the Central Management Appliance
354
Adding an Appliance Using the Central Management Web UI
354
Adding an Appliance Using the Central Management CLI
355
Accepting a Management Request
357
Requirements for Accepting a Management Connection Request
357
Preparing to Accept a Management Request Using the CLI
358
Preparing to Accept Requests for Management Connections that Support
Shifting Appliance IP Addresses Using the CLI
358
Accepting a Management Request Using the Central Management Web UI
360
Accepting a Management Request Using the Central Management CLI
361
Removing a Managed Appliance from the Central Management Network
363
Removing a Managed Appliance from the Central Management Network
Using the Web UI
363
Removing a Managed Appliance from the Central Management Network
Using the CLI
364
© 2022 FireEye Security Holdings US LLC
13
Contents
CHAPTER 25: Viewing and Modifying Managed Appliance Information 365
Viewing Managed Appliance Information Using the Web UI
367
Viewing Managed Appliance Information Using the CLI
370
Modifying Managed Appliance Information Using the Web UI
371
Modifying Managed Appliance Information Using the CLI
372
CHAPTER 26: Configuring Managed Appliances
375
Configuring Managed Appliances Using the Web UI
376
Configuring Network Settings for Managed Appliances Using the Web UI
377
Setting the Appliance Date and Time Manually on Managed Appliances Using
the Web UI
377
Managing Licenses for Managed Appliances Using the Web UI
377
Configuring NTP Servers for Managed Appliances Using the Web UI
378
Configuring System Email Settings for Managed Appliances Using the Web UI 378
Configuring DTI Network Settings for Managed Appliances Using the Web UI 378
Customizing Appliance Login Messages for Managed Appliances Using the
Web UI
379
Configuring Guest Images for Managed Appliances Using the Web UI
379
Uploading Certificates to Managed Appliances Using the Web UI
379
Managing Users on Managed Appliances Using the Web UI
380
Configuring Event Notifications for Managed Appliances Using the Web UI
380
Configuring File Types for Managed Malware Analysis Appliances to Analyze
Using the Web UI
380
Generating Reports for Managed Appliances Using the Web UI
381
Scheduling Reports for Managed Appliances Using the Web UI
381
Enabling or Disabling Riskware Detection Custom Policy Rules for Managed
Appliances Using the Web UI
383
Configuring Inline Operational Modes for Managed Network Security
Appliances Using the Web UI
383
Configuring Alert Policy Exceptions for Managed Network Security Appliances
Using the Web UI
384
Configuring Whitelists for Managed Network Security Appliances Using the
Web UI
14
384
© 2022 FireEye Security Holdings US LLC
Contents
Defining Filters for Managed Network Security Appliances Using the Web UI
384
Uploading YARA Rules to Managed Appliances Using the Web UI
385
Uploading Custom Rules to Managed Network Security Appliances Using the
Web UI
385
Configuring Forensic Analysis Integration on Managed Network Security
Appliances Using the Web UI
386
Configuring IPS Settings for Managed Network Security Appliances Using the
Web UI
386
Configuring IPS Policy Synchronization for Managed Network Security
Appliances Using the Web UI
387
Checking the Status of IPS Policy Synchronization for Managed Network
Security Appliances Using the Web UI
387
Configuring SSL Interception for Managed Network Security Appliances Using
the Web UI
388
Configuring the Helix Integration for Managed Network Security Appliances
Using the Web UI
389
Configuring the ICAP Integration for Managed Network Security Appliances
Using the Web UI
389
Configuring Port Mirroring for Managed Network Security Appliances Using
the Web UI
390
Allowing Increased Detection for Managed Appliances Using the Web UI
390
Enabling Advanced URL Defense on Managed Email Security — Server Edition
Appliances Using the Web UI
391
Configuring Email MTA Settings for Managed Email Security — Server Edition
Appliances Using the Web UI
392
Configuring Email Policy Using the Web UI
392
Configuring Impersonation Rules Using the Web UI
392
Configuring Rules on an Allowed List for Managed Email Security — Server
Edition Appliances Using the Web UI
393
Configuring Rules on a Blocked List for Managed Email Security — Server
Edition Appliances Using the Web UI
393
Configuring Attachment Decryption Settings for Managed Email Security —
Server Edition Appliances Using the Web UI
394
Configuring Retroactive Remediation for Managed Email Security — Server
Edition Appliances Using the Web UI
394
© 2022 FireEye Security Holdings US LLC
15
Contents
Configuring Malware Analysis Settings for Managed Malware Analysis
Appliances Using the Web UI
395
Configuring File Types for Managed Malware Analysis Appliances to Analyze
Using the Web UI
395
Configuring Malware Repository Settings for Managed Malware Analysis
Appliances Using the Web UI
395
Configuring and Managing Scans for Managed File Protect Appliances Using
the Web UI
396
Configuring and Managing Storage for Managed File Protect Appliances Using
the Web UI
396
Configuring Managed Appliances Using the CLI
396
Canceling Outstanding Commands
398
CHAPTER 27: Using Appliance Groups and Command Profiles
Grouping Appliances
399
Creating and Managing Groups Using the Web UI
400
Creating and Managing Groups Using the CLI
402
Adding Appliances to Groups Using the Web UI
404
Adding Appliances to Groups Using the CLI
404
Removing Appliances from Groups Using the Web UI
405
Removing Appliances from Groups Using the CLI
406
Working with Command Profiles
406
Creating and Managing Profiles Using the CLI
407
Adding Commands to Profiles Using the CLI
409
Removing Commands from Profiles Using the CLI
411
Applying Profiles Using the CLI
412
CHAPTER 28: Monitoring Aggregated Alert Data
415
Managing the Distribution of Alert Notifications
415
Centralized Notifications
415
Mixed Notifications
416
Decentralized Notifications
417
Monitoring Appliances Using the Web UI
16
399
418
© 2022 FireEye Security Holdings US LLC
Contents
Viewing Alerts and Events for Managed Network Security Appliances Using
the Web UI
418
Managing Suppressed Alerts on Managed Network Security Appliances Using
the Web UI
419
Monitoring Malware and Callback Activity for Managed Network Security
Appliances Using the Web UI
420
Viewing Malware Summaries for Managed Network Security Appliances
Using the Web UI
420
Viewing Riskware for Managed Appliances Using the Web UI
420
Viewing SmartVision Alerts on SmartVision Appliances Using the Web UI
421
Configuring AD Logger for Enhanced SmartVision Alerts
421
Viewing the Campaigns for Managed Email Security — Server Edition
Appliances Using the Web UI
422
Managing Quarantined Emails for Managed Email Security — Server Edition
Appliances Using the Web UI
422
Viewing Email Analysis Results for Managed Email Security — Server Edition
Appliances Using the Web UI
422
Viewing and Exporting the Results of Processed Emails on a Managed Email
Security — Server Edition Appliance Using the Web UI
423
Viewing the Messages in the Email Queue on a Managed Email Security —
Server Edition Appliance Using the Web UI
423
Viewing URL Click Reports for Managed Email Security Appliances Using the
Web UI
424
Viewing Malware Analysis Results for Managed Malware Analysis
Appliances Using the Web UI
425
Managing File Quarantines for Managed File Protect Appliances Using the
Web UI
425
Managing File Alerts for Managed File Protect Appliances Using the Web UI
426
Monitoring Appliances Using the CLI
426
Network Security and Email Security — Server Edition Event Correlation
427
Reviewing Email Alerts Correlated with Web Events
428
Reviewing Web Alerts Correlated with Email Events
431
Enabling Remote Email Security — Server Edition Appliance Event Correlation 433
Endpoint Security Event Correlation
434
Collecting Information to Triage Alerts
434
© 2022 FireEye Security Holdings US LLC
17
Contents
CHAPTER 29: Working with Reports for Managed Appliances
About Reports
437
437
Predefined Report Templates
437
Custom Reports
438
Customizing Reports for Managed Appliances
438
Task List for Customizing Reports for Managed Appliances
438
Creating and Configuring Settings for a Custom Report
439
Configuring Graphs for Custom Reports
444
Configuring Tables for Custom Reports
454
Creating a Custom Report from a Predefined Report Template
465
Editing and Cloning Reports That Have Been Generated
469
Sending, Downloading, and Deleting Custom Reports
475
Generating and Scheduling Reports for Managed Appliances
479
Generating Reports for Managed Appliances Using the Web UI
480
Scheduling Reports for Managed Appliances Using the Web UI
481
Generating and Scheduling Reports for Managed Appliances Using the CLI
482
CHAPTER 30: Checking Status and Health of Managed Appliances
485
Checking Status and Health of Managed Appliances Using the Web UI
486
Refreshing the Status Information
487
Checking Status and Health of Managed Appliances Using the CLI
488
Defining Status and Health Check Settings for Managed Appliances Using the CLI 492
CHAPTER 31: Updating Managed Appliances
495
Updating Managed Appliances Using the Web UI
496
Updating Managed Appliances Using the CLI
499
CHAPTER 32: Configuring Custom IOC Feeds
501
About Custom IOC Feeds
Task List for Managing Custom IOC Feeds
Enabling or Disabling Custom IOC Feeds
501
502
503
Enabling or Disabling Third-Party IOC Feeds on All Appliances Using the CLI 504
18
© 2022 FireEye Security Holdings US LLC
Contents
Enabling or Disabling the Local Feed on All Appliances Using the CLI
505
Enabling or Disabling Third-Party IOC Feeds on a Specific Appliance Using the
CLI
507
Enabling or Disabling the Local IOC Feed on a Specific Appliance Using the
CLI
509
Creating a Custom Blacklist from Third-Party Feeds
510
Uploading a Third-Party Feed
512
Uploading a Third-Party Feed Using the Web UI
Viewing Custom Feed Details
512
514
Viewing Custom Feed Details Using the Web UI
515
Viewing Custom Feed Details Using the CLI
515
Viewing Custom Feed Details Grouped by Alert Using the Web UI
516
Deleting Third-Party IOC Feeds Using the Web UI
517
Downloading a Third-Party Feed Using the Web UI
519
CHAPTER 33: Filtering Alerts Using Tags and Rules
521
Overview of Filtering Alerts Using Tags and Rules
521
Task List for Filtering Alerts Using Tags and Rules
Configuring Tags and Values
522
522
Adding Tags Using the Web UI
523
Editing Tags Using the Web UI
524
Deleting Tags Using the Web UI
525
Adding Values to a Tag Using the Web UI
526
Editing Values for a Tag Using the Web UI
528
Deleting Values From a Tag Using the Web UI
529
Configuring Rules to Manage Alert Tags
530
Adding a Rule to Match a Condition for a Particular IP Address Using the Web
UI
531
Adding a Rule to Match a Condition for a Particular VLAN Using the Web UI 533
Adding a Rule to Match a Condition for a Particular Appliance Using the Web
UI
535
Adding a Rule to Match a Condition for a Particular Product Type Using the
Web UI
© 2022 FireEye Security Holdings US LLC
536
19
Contents
Adding a Rule to Match a Condition for a Particular Severity Type Using the
Web UI
538
Adding a Rule to Match a Condition for a Particular Email Using the Web UI
539
Editing a Rule Using the Web UI
541
Deleting a Rule for an Alert Tag Using the Web UI
543
Setting or Changing the Priority of Rules Using the Web UI
544
Viewing Tags for an Alert for Managed Email Security — Server Edition
Appliances Using the Web UI
545
Viewing Tags for an Alert for Managed Network Security Appliances Using the
Web UI
546
Adding Tags to Alerts Manually for Managed Appliances Using the Web UI
546
Adding a Tag to an Alert for Managed Appliances Using the Web UI
547
Editing a Tag for an Alert for Managed Appliances Using the Web UI
548
Deleting a Tag From an Alert for Managed Appliances Using the Web UI
549
PART V: Appendices
551
APPENDIX A: Configuring Secure Shell (SSH) Authentication
553
About SSH Authentication
553
User Authentication
554
Creating a Public Key Using the CLI
555
Pushing a Public Key Using the CLI
556
Configuring User Authentication Using the Web UI
558
Configuring User Authentication Using the CLI
559
Host-Key Authentication
20
561
Obtaining a Host Key Using the Web UI
562
Obtaining a Host Key Using the CLI
563
Importing a Host Key into the Global Host-Keys Database Using the Web UI
564
Importing a Host Key into the Global Host-Keys Database Using the CLI
566
Enabling Strict and Global Host-Key Checking Using the CLI
568
© 2022 FireEye Security Holdings US LLC
Contents
APPENDIX B: Configuring Network Address Translation (NAT)
About NAT Address Mapping
571
571
Port Accessibility for Single-Port Communication
572
Port Accessibility for Dual-Port Communication
572
Mappings Used When the Central Management Appliance Initiates the Connection 572
Central Management Appliance Is Behind a NAT Gateway
573
Managed Appliance Is Behind a NAT Gateway
574
Central Management and Managed Appliance Are Behind Different NAT
Gateways
575
Central Management and Managed Appliance Are In an External Network
576
Mappings Used When the Managed Appliance Initiates the Connection
576
Central Management Appliance Is Behind a NAT Gateway
577
Managed Appliance Is Behind a NAT Gateway
578
Central Management and Managed Appliance Are Behind Different NAT
Gateways
578
Central Management and Managed Appliance Are in External Networks
580
Adding an Appliance in a NAT Deployment (Using the Central Management
Appliance)
580
Adding an Appliance in a NAT Deployment Using the Central Management
CLI
Accepting a Management Request in a NAT Deployment
580
582
Accepting a Management Request in a NAT Deployment Using the Central
Management Web UI
583
Accepting a Management Request in a NAT Deployment Using the Central
Management CLI
584
Configuring Global Host-Key Authentication in a NAT Deployment
APPENDIX C: Configuring the CM Peer Service
About CM Peer Service
Task List for Configuring the CM Peer Service
Enabling or Disabling the CM Peer Service
Enabling or Disabling the CM Peer Service Using the CLI
Generating and Importing Authentication Tokens Between CM Peers
© 2022 FireEye Security Holdings US LLC
586
589
589
590
591
592
593
21
Contents
Generating and Importing Tokens for CM Peers Using the CLI
594
Importing New Tokens for an Existing CM Peer Using the CLI
596
Exporting an Existing Token from a CM Peer Using the CLI
597
Enabling or Disabling All the Features of the CM Peer Service on the Peers
598
Enabling or Disabling All the Features of the CM Peer Service on the Peers
Using the CLI
599
Deleting a CM Peer Using the CLI
601
CM Peer Distributed Correlation
601
Enabling or Disabling CM Peer Distributed Correlation Using the CLI
602
Viewing CM Peer Distributed Correlation Alerts in the Web UI
604
CM Peer Signature Sharing
605
Enabling or Disabling CM Peer Signature Sharing Using the CLI
605
Viewing the Number of Rules for CM Peer Signature Sharing Using the CLI
607
Allowing or Preventing a CM Peer to Use a Proxy Server
Allowing or Preventing a CM Peer to Use a Proxy Server Using the CLI
608
609
APPENDIX D: Monitoring Email Alerts from the Email Security - Cloud
Edition
611
Enabling the ETP Cloud Endpoint Using the CLI
611
ETP Cloud Aggregation
612
Solving Connection Issues
613
Viewing Email Alerts from the ETP Cloud in the Web UI
22
613
Technical Support
615
Documentation
615
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
PART I: Overview
l
About the Central Management Appliance on page 25
l
User Interfaces on page 33
l
The Appliance Dashboard on page 51
© 2022 FireEye Security Holdings US LLC
23
Central Management System Administration Guide
24
PART I: Overview
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
"Single Pane of Glass"
CHAPTER 1: About the Central
Management Appliance
The Trellix Central Management appliance provides a centralized way to configure,
manage, and update groups of connected Trellix security appliances. It serves as both a
security event storehouse and central management device for the appliances it manages.
This section highlights the primary Central Management appliance features.
"Single Pane of Glass"
Rather than using several interfaces for multiple appliances, the Central Management
appliance streamlines the workflow by consolidating the functions of all managed
appliances into a single interface—all individual or grouped appliances are fully
configurable and operational from the Central Management appliance. You can perform
the following functions remotely from the Central Management appliance on behalf of its
managed appliances:
l
Application configuration
l
Policy enforcement
l
Alert monitoring
l
Software image, security content, and guest images updates
l
Report generation
l
Appliance health monitoring
Alert Management
The Central Management Dashboard provides tables, graphs, and charts that afford
instant visibility into malware threats and appliance status. You can drill down to view
details and take appropriate action. The pages you access from the Alerts tab in the Central
Management Web UI mirrors the comprehensive information available on the managed
© 2022 FireEye Security Holdings US LLC
25
Central Management System Administration Guide
CHAPTER 1: About the Central Management Appliance
appliances about detected malware. As with the Dashboard, you can drill into this
information for deeper forensic analysis.
You can use the following methods to send alerts to notification servers:
l
l
l
Centralized—Notifications are sent from the Central Management appliance only
Mixed—Notifications are sent from both the Central Management appliance and
from managed appliances.
Decentralized—Notifications are sent from managed appliances only.
For details, see Managing the Distribution of Alert Notifications on page 415.
Alerts in Central Management are retained in the CM database as long as they are retained
by the connected FireEye appliances. When the data is removed from the databases of
connected FireEye appliances, it is removed from Central Management. See the
documentation for the connected FireEye appliances for details about their alert retention
periods.
Alert Correlation
All results of malware detected by any managed appliance can be monitored by the
Central Management appliance. To offer advanced protection against spearphishing
attacks and converged threats, the Central Management appliance identifies correlations
between email- and Web-based malware events. When characteristics of malware detected
by a Network Security appliance are identified in an Email Security — Server Edition
event, the Central Management appliance alerts users of a blended attack. For details, see
Network Security and Email Security — Server Edition Event Correlation on page 427.
Signature Distribution
Locally generated malware profiles and detection information can be shared among
appliances using the Central Management appliance. Once malware is detected by one
blocking appliance, its profile can be uploaded to other appliances in the network to make
it easier to identify and protect against that threat in the future.
Submit to Malware Analysis for Deep
Forensics
Malware detected by any managed appliance can be submitted from the Central
Management Web UI to the Malware Analysis appliance for deeper forensic analysis.
26
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Appliance Groups
Appliance Groups
You can manage and monitor appliances individually or in groups. By default, a group is
created for each product type when an appliance of that type is added to the Central
Management appliance. You can create custom groups and add appliances to them as
needed.
The benefits of appliance groups include:
l
l
l
Limiting the displayed event data to specific appliances.
Making the same configuration changes to multiple appliances at one time, instead
of individually.
Organizing appliances in logical groups (for example, based on geographic region
or security level) and specifying configuration and policy settings accordingly.
For details, see Grouping Appliances on page 399.
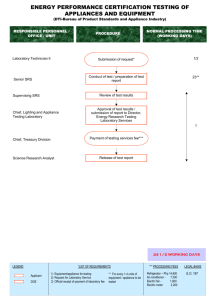
Central Management Deployment
This section describes the supported Central Management deployment scenarios.
Standard Deployment
To manage other Trellix appliances, the Central Management appliance simply needs a
connection that allows it to communicate with the managed appliances. This connection
can be practically anywhere in the network. The diagram below illustrates the typical
deployment of managed appliances and a CM 9400 connected to a typical network device.
© 2022 FireEye Security Holdings US LLC
27
Central Management System Administration Guide
CHAPTER 1: About the Central Management Appliance
Network Address Translation (NAT) Deployment
When the Central Management appliance or the managed appliance is behind a network
address translation (NAT) gateway, it has an internal address that cannot be reached. NAT
techniques hide the internal address, so requests appear to originate from the NAT
gateway instead of the internal network. For details about the required address mapping
and the procedures for establishing a connection between the Central Management
appliance and the appliances, see Configuring Network Address Translation (NAT) on
page 571.
Single-Port Deployment
By default, the Central Management appliance and a managed appliance use a single port
(the SSH port, 22 by default) for the following types of communication:
l
l
Remote management—Initiates the connection and configures the managed
appliance.
DTI network service—Requests software updates (such as guest images, security
content, and system images) from the DTI network.
The single-port configuration reduces the complexity of firewall rules, and provides an
additional layer of security and privacy between the Central Management appliance and
the appliances it manages. In environments in which the Central Management appliance
is behind a Network Address Translation (NAT) gateway, using a single port also
eliminates the need to open an additional HTTPS port (443) for the managed appliance to
request software updates from the Central Management appliance. (For details about
NAT deployment, see Configuring Network Address Translation (NAT) on page 571.)
You can instead configure the dual-port address type, in which the management traffic
uses the SSH port (22) and the DTI network service traffic uses the HTTPS port (443). If you
change the configuration on an appliance that was already added to the Central
Management appliance using a client-initiated connection, that managed appliance will be
briefly disconnected and then reconnected using the new configuration.
NOTE: Single- and dual-port communication is configured on the managed
appliance, not on the Central Management appliance. For details, see the System
Administration Guide or Administration Guide for the managed appliance.
High Availability (HA) Deployment
With Central Management high availability (HA), you can cluster two Central
Management appliances for failover. The primary Central Management appliance (or node)
is available continuously. If the primary node fails, your entire configuration fails over
automatically to the secondary node; the secondary node then becomes the primary
appliance. Central Management HA can be configured for high availability in local area
28
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
MVX Cluster Deployment
network (LAN) environments and for disaster recovery in wide area network (WAN)
environments. The following configurations fail over to the secondary node:
l
Security content
l
Software updates
l
Aggregated Trellix database information
l
Central Management management configuration (except interface, licensing, and
host-specific configurations)
IMPORTANT! Network address translation (NAT) is not supported in Central
Management HA deployments. Client-initiated connections are only supported in a
Central Management HA LAN deployment with a configured VIP address.
Central Management HA is not supported on all virtual CM models. See the FireEye
Device Deployment Guide.
For details about Central Management HA deployment, see the Central Management High
Availability Guide.
Split DTI Traffic Deployment
By default, both management and DTI traffic use the ether1 network interface, which needs
Internet access for DTI network downloads and uploads. For security, you might want to
isolate the management traffic by streaming it from an out-of-band network interface with
no Internet access. For details, see DTI Traffic and Management Traffic on page 191.
IMPORTANT! Splitting DTI traffic is not currently supported in Central
Management HA deployments.
MVX Cluster Deployment
A standard (or integrated) appliance performs both monitoring and analysis. Trellix
Distributed Network Security separates these two functions. Appliances that function as
sensors extract objects and URLs from the traffic they monitor, and send submissions to an
MVX cluster for inspection and analysis. A sensor and an integrated appliance have
identical features and detection efficacy.
An appliance running in MVX hybrid mode can send submissions to an MVX cluster, but
only when a predefined capacity threshold is reached. This offloads the analysis function
from the appliance to the MVX cluster, which prevents delays and reduced efficacy when
volume and other processing demands are high. When the capacity falls below this
threshold, the appliance resumes sending submissions to its on-board analysis engine.
© 2022 FireEye Security Holdings US LLC
29
Central Management System Administration Guide
CHAPTER 1: About the Central Management Appliance
Sensors can be managed by the Central Management appliance that manages the MVX
cluster or by another Central Management appliance. The sensors can also be standalone
appliances that are not managed by a Central Management appliance.
Hybrid appliances must be managed by the Central Management appliance that manages
the MVX cluster. They cannot be standalone appliances.
The MVX cluster contains compute nodes, which are Virtual Execution appliances with
MVX analysis engines. Compute nodes are designated as brokers. The brokers receive the
submissions from the sensors and manage them in a queue that is distributed across the
brokers in the cluster. The compute nodes pull submissions from the queue, perform the
analysis, and send the verdict to the sensors through the brokers.
The sensors generate alerts based on the verdict. A managed sensor sends the alerts to its
managing Central Management appliance, which aggregates the alerts and displays them
on a single interface. A standalone sensor displays its own alerts.
In an MVX Smart Grid deployment, the cluster is hosted on-premises in the customer
network. In a Cloud MVX deployment, the cluster is hosted in the Trellix cloud.
For a list of the appliances that can function as sensors or hybrid appliances and for
deployment details, see the MVX Smart Grid Guide and Cloud MVX Guide.
Management Path
CM appliances can download security content and software updates from the FireEye
Dynamic Threat Intelligence (DTI) network. With a two-way content license, the appliance
can also upload threat intelligence information to the DTI network.
Central Management Appliances That Receive DTI
Updates
The Central Management appliance and standalone appliances use the ether1 port to
communicate with the DTI network. In the default configuration, where you receive
updates from the DTI network (cloud.fireeye.com), allow outbound access to all IP
addresses on the following ports:
l
DNS (UDP/53)
l
HTTPS (TCP/443)
Management interface ether1 requires a static IP address or reserved DHCP address and
subnet mask.
30
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Management Path
Environments That Restrict Outbound Access to Certain
IP Addresses
If your security policy requires that you restrict outbound access to certain IP addresses,
you cannot use the DTI network. Instead, point to staticcloud.fireeye.com for DTI updates,
and allow access to the *incapdns.net domain.
For appliances that get threat intelligence from the DTI cloud, you need to enable access to
the Amazon Web Services (AWS) cloud for ATI communication. The intel context service is
hosted in multiple AWS regions and resolves to multiple IP addresses based on geographic
location.
To configure and access staticcloud.fireeye.com:
1. Enable CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Enter the following command from the appliance CLI:
hostname (config) # fenet dti source default DTI
3. Save your configuration.
hostname (config) # write mem
4. Add IP addresses here to the firewall.
To allow access to *incapdns.net:
1. Add the block of IP addresses found at https://incapsula.zendesk.com/hc/enus/articles/200627570-Restricting-direct-access-to-your-website-Incapsula-s-IPaddresses- to the firewall.
2. Allow access to the *.incapdns.net domain at the proxy device.
To allow access to the AWS cloud for threat intelligence:
1. Go to https://dnschecker.org/#A/context.fireeye.com to determine the IP addresses for
your location.
2. See the AWS IP address range documentation for information about whitelisting the
IP addressses.
CM Appliances with Domain-based Proxy ACL Rules
If your configuration includes domain-based proxy ACL rules, allow access to
*.fireeye.com.
For appliances connected to the Central Management appliance, use only a static IP
address and subnet mask. The appliance should use the ether1 port to communicate with
the Central Management appliance.
© 2022 FireEye Security Holdings US LLC
31
Central Management System Administration Guide
CHAPTER 1: About the Central Management Appliance
Integrated CM Communications Protocol and Port
Configurations
Establish SSH connectivity between the Central Management appliance and each managed
appliance. For details about port and protocol configuration, see the CM Hardware
Administration Guide.
FIPS 140-2 and Common Criteria
Compliance
Use the Compliance Settings page to configure compliance features on the CM appliance.
You can instead use the following CLI commands to configure compliance features on the
appliance:
l
compliance apply standard
l
compliance declassify zeroize
l
compliance options
l
show compliance
l
show compliance options
l
show compliance standard
For details, see the FIPS 140-2 and Common Criteria Addendum and the CLI Command
Reference.
32
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 2: User Interfaces
This section covers the following information:
l
Overview of CM User Interfaces on the next page
l
The CM Appliance Web UI on page 35
l
The CM Appliance Command-Line Interface on page 40
l
The CM Appliance IPMI Interface on page 44
l
The CM Appliance LCD Display on page 41
© 2022 FireEye Security Holdings US LLC
33
Central Management System Administration Guide
CHAPTER 2: User Interfaces
Overview of CM User Interfaces
Trellix Helix enables you to access all of your Trellix on-premises and Cloud-based
services from a single view.
The CM appliance has the following user interfaces:
l
l
l
l
l
Web UI—A Web-based UI used to configure and manage the appliance. This is
described in The CM Appliance Web UI on the facing page. The appliance Web UI
includes a Dashboard, described in The Central Management Appliance Dashboard
.
Web UI—A Web-based UI used to configure and manage the appliance and the
appliances it manages. This is described in The CM Appliance Web UI on the facing
page. The appliance Web UI includes a Dashboard, described in Central
Management Dashboard Widgets on page 53.
CLI—A command-line interface used to configure and manage the CM appliance.
To access the appliance CLI, see The CM Appliance Command-Line Interface on
page 40.
LCD Display—The LCD display and associated controls (available on some
appliance models) can be used to initially set up the CM appliance. It can also be
used to check system status and make certain configuration changes. This is
described in The CM Appliance LCD Display on page 41.
IPMI Interface—The IPMI interface enables you to access the CM appliance over
the network and perform recovery activities even if the system is powered down or
otherwise unresponsive. This is described in The CM Appliance IPMI Interface on
page 44.
Two user interfaces that are external to the CM appliance pertain to using the CM
appliance in a Trellix Helix environment:
l
34
Trellix Helix Web UI―An interface that provides a single view of alerts from all
the Helix appliances in your network. For more information, see the Helix User Guide
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
The CM Appliance Web UI
Trellix Cloud IAM Web UI―An interface to the Cloud IAM server. It is used
primarily by your IAM organization administrator (a user account that Trellix
provides for you along with your IAM organization). The administrator creates
Trellix Cloud accounts for users and applies role-based and rule-based access
controls. This is described in "Trellix Cloud IAM User Accounts" in the System
Security Guide.
The owners of these user accounts can also log in to the Trellix Cloud IAM Web UI.
Their access privileges in the Trellix Cloud IAM Web UI are generally limited
updating their account preferences and changing their passwords. This is described
in "Your Trellix Cloud IAM User Account" in the System Security Guide.
Access to the Trellix Cloud IAM Web UI is necessary for you to configure support for single
sign-on (SSO) authentication. When SSO authentication is enabled and Helix mode is
enabled on Trellix appliances, users can sign in once to authenticate to their Trellix Cloud
Account and then navigate among the components without having to log in locally to each
appliance. This is described in "Single Sign-On Authentication" in the System Security
Guide.
Do not change the password for the permanent api_analyst user account on the
Endpoint Security server. Doing so could break the connection between the
Endpoint Security server and Helix. If you need API connectivity between the
Endpoint Security server and a third-party product, add another user account
with the api_analyst role.
The CM Appliance Web UI
The CM appliance Web UI uses HTTPS to provide a secure connection for configuring the
appliance. The Web UI functions you have access to depend on the privileges granted by
your role.
You access the CM appliance Web UI by directing a browser to the management port's
IP address or hostname using HTTPS. The IP address and hostname are set during the
initial configuration of the appliance. The hostname must be resolved by a DNS server if
you use it to access the Web UI.
The CM appliance Web UI includes controls for logging in and out using local, appliancespecific credentials. The Web UI also indicates whether Helix mode is enabled and whether
alerts are Helix alerts.
© 2022 FireEye Security Holdings US LLC
35
Central Management System Administration Guide
CHAPTER 2: User Interfaces
Browser Support
Use a recent version of one of the following browsers to access the CM appliance Web UI:
l
Microsoft Edge on supported versions of Windows
l
Firefox on supported versions of Windows and Mac
l
Google Chrome on supported versions of Windows and Mac
Screen Resolution Requirements
The CM appliance Web UI supports the following screen resolutions:
1152 x 864 pixels
1440 x 900 pixels
1280 x 800 pixels
1600 x 900 pixels
1280 x 1024 pixels
1680 x 1050 pixels
1360 x 768 pixels
1920 x 1080 pixels
1366 x 768 pixels
1920 x 1200 pixels
Logging In Locally to the Helix Appliance Web UI
To log in locally to the Helix CM appliance Web UI, you need the appliance IP address or
hostname, and you need the local username and password that the appliance
administrator created for you.
Prerequisites
l
Before the default Admin user can log in to the appliance Web UI and create other
user accounts, the manufacturing default password (admin) must be changed to a
new password that is 8 to 32 characters long. This step is included in Initial
Configuration on page 77.
To log in locally to the Helix CM appliance Web UI:
1. Open a Web browser and enter https://<appliance> in the address line, where
appliance is the IP address or hostname of the appliance. For example, if the
configured IP address of the appliance is 10.1.0.1, enter https://10.1.0.1.
2. In the appliance Web UI login page, enter the local user name and password for this
appliance as provided by your administrator.
36
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
The CM Appliance Web UI
Notifications of Appliance Health Problems
The bell at the top right of the Web UI indicates the number of appliance health issues that
need to be addressed. When you click the bell, the notifications are displayed with links to
the relevant Web UI pages. The bell is not displayed when there are no notifications.
The following illustration indicates that one issue needs to be addressed.
Notifications of Appliance Health Problems
If an appliance needs your attention, a notification bell is displayed at the top right corner
of the Dashboard and all other Web UI pages. Click the bell to open a window that lists the
messages. Some messages include a link to the relevant Central Management Web UI page.
(For details, see Notifications of Appliance Health Problems above).
For example:
l
l
This message indicates that at least one appliance needs to be updated to be
compatible with this Central Management appliance version. Clicking the button
opens the Sensor Updates page, where the managed appliance can be updated.
This message indicates that at least one node in MVX cluster needs to be updated or
has some other issue that needs your attention. Clicking this link opens the
Appliances > Nodes page.
© 2022 FireEye Security Holdings US LLC
37
Central Management System Administration Guide
l
l
l
l
CHAPTER 2: User Interfaces
This message indicates that an appliance sent a request to be managed by this
Central Management appliance. The button opens the Connection Requests dialog
box, where the request can be accepted or rejected.
This message indicates that a problem prevents at least one appliance from being
managed properly. Clicking the button opens the Sensors page, where you can
refresh the status, or reset the connection after the underlying problem is resolved.
This message includes a link that opens a dialog box with options for sending
additional information to FireEye for analysis to increase detection rates. For more
information, see Allowing Increased Detection for Managed Appliances Using the
Web UI on page 390.
This message includes a link for enabling Advanced URL Defense on qualified
Email Security — Server Edition appliances. For more information, see Enabling
Advanced URL Defense on Managed Email Security — Server Edition Appliances
Using the Web UI on page 391.
Central Management Web UI Tabs
This section describes the Central Management Web UI tabs. The following illustration
shows the tabs on a Central Management appliance that manages one or more Email
Security — Server Edition and Network Security appliances.
38
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
l
l
l
l
l
The CM Appliance Web UI
Dashboard—Provides a high-level view of the threat intelligence gathered by the
appliances the Central Management appliance manages.
Appliances—Displays information about all currently managed appliances, and
allows you to add or remove appliances, configure connection parameters, configure
appliance groups, import host keys for global host-key authentication, and update
managed appliances.
Alerts—Displays aggregated alert, detection, and quarantine information.
IPS—Displays information about Integrated Intrusion Prevention System (IPS)
events and alerts, and allows IPS configuration and setting of policy exceptions and
custom rules.
Search Emails—Allows you to search for all emails the Central Management
appliance processed, and to view and manage the emails that are being processed
or in queue to be processed.
Settings—Provides options for configuring system administration and policy
settings for the Central Management appliance and its managed appliances.
Reports—Allows you to generate and schedule reports in various formats on behalf
of managed appliances.
About—Provides access to the following pages:
o
Summary — Displays system information, such as software version and
Security Contents version. See Viewing System Health and Performance
Check Results on page 253.
o
Supported Features — Displays features available for the appliance and
whether they are enabled or disabled. See Supported Features on page 283.
o
Health Check—Provides comprehensive and current system status
information such as software version, patch version, content version, MVX
engine version, DTI connection, and configured interfaces. This page also
provides an Appliance Health link, which takes you to the page where you
can view the health status of managed appliances. See System Health and
Performance on page 253.
o
Log Manager—Allows you to manage system logs. See Log Management on
page 217.
o
Upgrade—Allows you to upgrade software for the Central Management
appliance, and provides an Upgrade Appliances link, which takes you to the
page where you can upgrade software and guest images for managed
appliances. See Upgrading the FireEye Software on page 197.
Other tabs are displayed depending on the appliances the Central Management appliance
is currently managing. For example, the Alerts tab displays aggregated alert and detection
statistics from managed appliances, the Search Emails tab allows you to search for
© 2022 FireEye Security Holdings US LLC
39
Central Management System Administration Guide
CHAPTER 2: User Interfaces
processed and queued emails on a managed Email Security — Server Edition appliance,
and so on.
NOTE: The Central Management appliance cannot search for emails processed
by Email Security — Cloud Edition. You must search in the Email Security —
Cloud Edition interface and have an IAM account with at least the entitlement
ETP.Read.only.
PDF Generation
Some Web UI pages, such as those that display analysis results, have a Print PDF button
at the top right side of the page that allows you to save the content of the page to PDF so it
can be printed or saved. Only the content that is visible on the page is included in the PDF
output. For example, if an item on the page is not expanded, the details about that item are
not displayed and will not be included in the PDF output. Depending on your Web
browser settings, the generated PDF opens in the Web browser or is downloaded to your
computer.
The amount of time needed to generate the PDF depends on the current load on the system.
By default, the system will try to generate the PDF using Standard Processing Time, the
fastest way possible. If the PDF generation times out, you can try again using other options
by clicking the arrow on the button and then selecting Extra Processing Time or Heavy
Processing Time, where heavy processing time takes the longest.
The CM Appliance Command-Line
Interface
The CM appliance includes a standard command-line interface (CLI) that can be used to
configure, manage and monitor the CM system, including its managed appliances.
To log into the CLI using a terminal window or SSH client:
1. Using the SSH protocol, log in to the appliance using the management interface’s
IP address or hostname.
40
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
The CM Appliance LCD Display
$ ssh <username>@<ipAddress> | <hostName>
where ipAddress specifies the IPv4 or IPv6 address of the management interface.
2. When prompted, enter your password.
Password: <password>
The hostname > prompt is displayed after you are logged in.
The CM Appliance LCD Display
An LCD panel is available on the front of some appliance models. You can perform the
initial configuration of the appliance using the LCD panel, as described in Configuring
Initial Settings Using the LCD Panel on page 84. You can use the LCD panel to perform
other basic configuration tasks as well.
Navigating the LCD Menus
The following illustration of the LCD panel shows how to use the navigation buttons to
configure settings. For details about the menus, see LCD Menu on page 44.
On some models, you need to remove the front panel to access the LCD panel navigation
buttons.
To remove the front panel:
1. Unscrew the front panel to unlatch it.
© 2022 FireEye Security Holdings US LLC
41
Central Management System Administration Guide
CHAPTER 2: User Interfaces
2. Remove the front panel.
LCD Panel Menus
The LCD panel has four menus: Network Menu below, Config Options Menu on the facing
page, LCD Menu on page 44, and Restart Options Menu on page 44.
See Navigating the LCD Menus on the previous page for information about moving
through the menus and selecting options.
Network Menu
The following table provides information about the Network menu.
42
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
The CM Appliance LCD Display
Prompt
Description
Hostname
Hostname for the appliance.
DHCP
enabled
Enter “yes” to use DHCP on the ether1 (management interface) port.
Enter “no” to manually configure your IP address and network settings.
Static IP
address
This prompt is available if DHCP is disabled. Enter the IP address for
the ether1 (management interface) port.
Netmask
This prompt is available if DHCP is disabled. Enter the network mask.
Default
gateway
This prompt is available if DHCP is disabled. Enter the gateway IP
address for the management interface.
Primary DNS
This prompt is available if DHCP is disabled. Enter the Primary DNS
server IP address.
Domain
name
This prompt is available if DHCP is disabled. Enter the domain name
for the management interface; for example, it.acme.com
IPv6 enabled
Enter “yes” to enable IPv6 protocol, which changes the network IP
routing from IPv4 to IPv6.
SLAAC
enabled
This prompt is available if IPv6 is enabled. Enter “yes” to enable IPv6
autoconfig on the ether1 (management interface) port. Enter "no" to
disable IPv6 autoconfig on the ether1 (management interface) port.
Admin net
login
Enter “yes” to enable the administrator to log in to the appliance
remotely. Enter "no" to disable remote access.
Config Options Menu
The following table provides information about the Config Options menu.
Prompt
Description
Save settings
Saves changes made during a session so they will persist after a reboot.
Revert to
factory
defaults
Reverts the appliance to its factory default settings, which include user
name and password, and network configuration information.
© 2022 FireEye Security Holdings US LLC
43
Central Management System Administration Guide
CHAPTER 2: User Interfaces
Prompt
Description
Reset admin
password
Resets the admin password for accessing the appliance itself. (This does
not set the password for accessing the LCD panel.) The new password is
randomly generated. The LCD will display the password. When you
have memorized it, press a button to move to the next prompt or menu.
You can change to a password of your choice using the appliance CLI or
Web UI after the basic configuration is complete.
LCD Menu
The following table provides information about the LCD menu.
Prompt
Description
Password
Sets a password for LCD panel access. (This does not set the password
for accessing the appliance.)
Brightness
Sets the LCD panel’s level of brightness from 0 to 9, with 9 being the
brightest.
Contrast
Sets the LCD panel’s level of contrast between the background and text
from 0 to 9, with 9 being the highest contrast.
Restart Options Menu
The following table provides information about the Restart Options menu.
Prompt
Description
Reboot
system
Restarts the system.
Halt system
Brings the system down to its lowest state while remaining on.
Next boot loc
Specifies disk partition (1 or 2) to boot from during the next reboot.
The CM Appliance IPMI Interface
IMPORTANT: The IPMI interface port is only enabled in CM Release 8.2.0 or later
and IPMI firmware version 2.07 or earlier.
The Trellix Intelligent Platform Management Interface (IPMI) allows you to perform the
following tasks remotely from a Web browser:
44
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
The CM Appliance IPMI Interface
Cycle the power on your appliance when it is unresponsive.
NOTE: The IPMI is active even if the appliance was powered down from the
appliance CLI or from the power button on the front panel, as long as the
main power is on.
l
l
l
Reset the server.
Access the serial console when the management interface is unavailable or
unresponsive.
Check the status of server sensors.
For IPMI interface configuration details, see Configuring the IPMI Interface on page 85.
The IPMI interface uses a network connection to the IPMI port of the appliance and is
accessed through a secure Web browser session. (The standard IPMI interface allows
connections using third-party tools such as Supermicroʼs IPMI View; however, all such
external access to the IPMI interface from the appliance is disabled.)
IMPORTANT! The IPMI remote control cannot perform a graceful power down of
the appliance.
IPMI Browser Support
Use a recent version of one of the following Web browsers to access the Web UI:
l
Microsoft Edge on supported versions of Windows
l
Google Chrome on supported versions of Windows and Macintosh
IMPORTANT! Do not use Firefox to access the IPMI port. The Firefox browser
interprets a regenerated HTTPS certificate as a possible attack, and it generates an
Invalid Certificate Error code ("sec_error_reused_issuer_and_serial"). Instead of
completing the connection, Firefox displays a "Secure Connection Failed" page.
Logging In to the IPMI Interface
This procedure describes how to log in the CM appliance IPMI interface from a Web
browser.
Prerequisites
l
The 100BASE-T IPMI port on the rear of the appliance is cabled and configured as
described in Configuring the IPMI Interface on page 85.
© 2022 FireEye Security Holdings US LLC
45
Central Management System Administration Guide
CHAPTER 2: User Interfaces
l
The IP address that was configured for the IPMI port is known.
l
You are using a Web browser listed in IPMI Browser Support on the previous page.
To log in to the IPMI interface:
1. Using a Web browser, access the IPMI port through a secure Web browser session.
In the browser address bar, enter https:// followed by the IP address of the IPMI
port.
2. Log in to the IPMI Web UI using ADMIN as the username and the password that
was configured for the IPMI user.
TIP: The IPMI interface supports passwords of up to 16 characters. To use
a password of up to 20 characters, contact Trellix Support
(https://csportal.fireeye.com).
Power Cycling and Resetting the Device
This procedure describes how to use the IPMI interface to power cycle the CM appliance.
Prerequisites
l
You are logged in to the appliance IPMI.
To cycle power or reset the server:
1. Click the Remote Control tab.
2. Click Power Control in the sidebar.
46
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
The CM Appliance IPMI Interface
3. Select the option you need:
l
Reset Server
l
Power Off Server – Immediate
l
Power Off Server – Orderly Shutdown
l
Power On Server
l
Power Cycle Server
4. Click Perform Action.
Accessing the Device Serial Console
This procedure describes how to use the IPMI interface to access the CM appliance through
a serial console.
IMPORTANT! Use the IPMI Web UI to access the compute node serial console only
during a power or system reset or when the system is not otherwise responding on
the management interface.
Prerequisites
l
You are logged in to the appliance IPMI.
l
The appliance is not using its management interface.
To access the serial console:
IMPORTANT! Use the IPMI Web UI to access the serial console only during a
power or system reset or when the system is not otherwise responding on the
management interface.
1. Click the Remote Control tab.
2. Click Console Redirection in the sidebar.
© 2022 FireEye Security Holdings US LLC
47
Central Management System Administration Guide
CHAPTER 2: User Interfaces
3. Click Launch Console.
You might be prompted to install a Java program to launch the console, which
could require changes to your Java security settings. If your security policy does not
allow this, and if your appliance uses a recent IPMI firmware version, you can
instead open ports on the firewall. To view the installed and available firmware
versions, click System and then System Information, or follow the instructions in
IPMI and BIOS Firmware Updates on page 213.
Checking the Status of Device Sensors
This procedure describes how to use the IPMI interface to check the status of the CM
appliance sensors.
Prerequisites
l
You are logged in to the appliance IPMI.
To check the status of server sensors:
1. Click the Server Health tab.
2. Click Sensor Readings in the sidebar.
3. Click options at the bottom of the page as needed:
l
Refresh
l
Show Thresholds
l
Intrusion Reset
Resetting the IPMI Interface Using the CLI
This procedure describes how to reset the IPMI interface.
48
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
The CM Appliance IPMI Interface
Prerequisites
l
Admin access to the CM appliance.
If the IPMI interface stops working, follow these steps to reset it. You might need to
schedule a maintenance window to do this.
To reset the IPMI interface:
1. Log in to the CM CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Reload the IPMI firmware:
hostname (config) # ipmi firmware reload cold
4. Wait five minutes.
5. Check whether the IPMI interface is up:
hostname (config) # show ipmi
6. If the IPMI interface is down:
a. Shut down the appliance:
hostname (config) # reload halt
b. Unplug all power cables.
c. Wait 90 seconds.
d. Plug in the power cables.
e. Push the power button to restart the appliance.
© 2022 FireEye Security Holdings US LLC
49
Central Management System Administration Guide
50
CHAPTER 2: User Interfaces
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 3: The Appliance
Dashboard
The Dashboard displays a collection of widgets that provide high-level views of the threat
intelligence gathered by the managed appliances and sensors.
This chapter covers the following information:
Central Management dashboard widgets
The Web UI opens to the Dashboards tab. The predefined dashboard FireEye Dashboard
displays all of the widgets available for the appliance. Widgets are categorized as
Analysis, Operational, or Detection. Use the Category dropdown menu to filter the Trellix
Dashboard to show all widgets in the selected category. You can view a widget in fullscreen mode and then restore the standard dashboard view. The dashboard widgets are
introduced in Central Management Dashboard Widgets on page 53.
Dashboard widgets displayed for managed appliances
Only those panels that pertain to the types of appliances under management are
included. Some panels of the Dashboard do not appear if the information is not relevant
to the configuration of those appliances. By default, information about all managed
appliances is displayed on the Dashboard. You can filter the display by selecting an
appliance group or a specific appliance from the menus at the top of the page. A label at
the top of each panel identifies the appliance type to which the information pertains.
Custom dashboards
You can create custom dashboards by selecting Central Management dashboard widgets
and arranging them in a layout of your choosing. Any dashboard can be designated as
the default dashboard that appears when you log in to the appliance Web UI. You can
also change the order in which dashboard names appear across the top of the page. These
Web UI operations are described in Custom Dashboards on page 61.
© 2022 FireEye Security Holdings US LLC
51
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Configuring dashboards and widgets
You can configure the auto-refresh interval that applies to all widgets in all dashboards.
You can also apply a one-time refresh of the data displayed in all of the current
dashboard widgets or just for a single widget. You can specify the time period covered by
all of the current dashboard widgets or just for a single widget. These Web UI operations
are described in Dashboard and Widget Management on page 66.
Generating and scheduling dashboard reports
You can generate a single report, and schedule reports to run hourly, daily, weekly, or
monthly. Select CSV, JSON, or XML format. Reports contain data on all the widgets on
the dashboard. For more information, see Generating and Scheduling Dashboard
Reports on page 69.
52
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Central Management Dashboard Widgets
Central Management Dashboard
Widgets
The Central Management dashboard displays widgets that give you a summary view of the
threat intelligence gathered by the appliances and sensors it manages. Only those widgets that
pertain to the types of appliances under management are included. Some widgets do not
appear if the information is not relevant to the configuration of those appliances.
You can filter the display by selecting an appliance group or a specific appliance from the
menus at the top of the page.
The Dashboard is accessible by the Admin, Analyst, and Monitor roles. The Operator role
can access the Dashboard, but can view only the Cluster Utilization widget.
Role
Accessible Dashboard Widgets
Admin
All widgets
Analyst
All widgets except the Cluster Connection Status and Cluster Utilization
Monitor
All widgets
Operator Cluster Utilization only
The following dashboard widgets can appear on any Central Management dashboard:
Alerts Summary
Displays the total number of alerts and events for the managed appliances in common
categories and in categories that are specific to each type of appliance. For details, see
Alerts Summary on the next page.
Cluster Connection Status
Displays status information about submission connections between managed sensors
and their MVX clusters. For details, see Cluster Connection Status on page 55.
Supported Features
Displays a card for each features supported by the managed appliances. Each card
shows the feature status (enabled or disabled), name, category, and description. For
details, see Supported Features on page 56.
Service Health Statistics Trend
Displays a graph of the aggregate health level (Healthy, Warning, or Critical) over time
for the service categories you select. For details, see Service Health Statistics Trend on
page 56.
© 2022 FireEye Security Holdings US LLC
53
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Cluster Utilization
Displays the numbers of submissions, submission processed, and submissions
dropped. To view this widget, select the cluster from the Group drop-down menu. For
details, see Cluster Utilization on page 57.
The Central Management dashboard can display widgets that are specific to managed
appliance types. These widgets are listed in Malware Analysis Widgets in the Central
Management Dashboard on page 58, Email Security — Server Edition Widgets in the
Central Management Dashboard on page 58, File Protect Widgets in the Central
Management Dashboard on page 59, and Network Security Widgets in the Central
Management Dashboard on page 60.
Alerts Summary
The Alerts Summary widget displays the total number of alerts and events for the
managed appliances in common categories (such as APT Attacks and Not Seen Before),
and in categories that are specific to each type of appliance.
If a color-coded badge (such as “Network Security“, “File Protect“, or “Email“) appears in
the upper left corner of the Alerts Summary widget, all of the alert or event counts are
specific to the indicated appliance type.
l
l
54
In this example, the widget displays alert and event counts for managed Network
Security appliances only.
In this example, the widget displays alert and event counts for managed File Protect
appliances only.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Central Management Dashboard Widgets
NOTE: If none of the alert or event categories is represented, or if no data is available for
the selected appliances and time period, the Alerts Summary widget does not appear in
the Central Management dashboard.
Cluster Connection Status
If a Central Management appliance is operating in sensor mode, the Cluster Connection
Status widget shows status information about the sensor’s submission connection to its
MVX cluster.
If the appliance is operating in sensor mode, the Broker State field should be “Connected.”
If the Broker State field is “Failed”, use the information in the other fields to troubleshoot.
© 2022 FireEye Security Holdings US LLC
55
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Supported Features
The Supported Features widget lists all the supported features for the selected managed
appliances. You can select a group of managed appliances or a single managed appliance.
The names of enabled features are indicated by shaded cards. To view the description and
category of a feature, hover over the card.
You can filter the display to show only enabled features or only disabled features.
This information is also available in the About tab.
Service Health Statistics Trend
The Service Health Statistics Trend widget graphs the aggregate health level (Healthy,
Warning, or Critical) over time for the service categories you select. You can enable health
tracking for one or any combination of the following service categories:
56
l
Cloud detection
l
Metadata streaming
l
Analysis
l
System
l
Network processing
l
DTI
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Central Management Dashboard Widgets
Each category button displays either the current health level or “Disabled.”
To view the breakdown of service health levels at any point in time, hover over the graph.
Cluster Utilization
The Cluster Utilization widget contains charts that show MVX cluster use statistics. To
view this widget, select the cluster from the Group drop-down menu.
NOTE: The Operator role can access the Cluster Utilization widget only.
To view utilization data at a particular date and time, hover above the chart graph point.
The widget consists of the following charts:
Cluster Utilization
This chart graphs the appliance usage level over time: Normal (0), High (1), or Critical (2).
A High or Critical level of use can indicate that the appliance is oversubscribed.
© 2022 FireEye Security Holdings US LLC
57
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Submission Statistics
This chart graphs the number of files or URLs submitted for analysis over time. Total
submissions, analyzed submissions, and dropped submissions are graphed separately.
Malware Analysis Widgets in the Central Management
Dashboard
The following widgets can display Malware Analysis-specific information:
l
Submissions Per User
l
Submission Summary
Email Security — Server Edition Widgets in the Central
Management Dashboard
When the following badge appears in the upper-left corner of a Central Management
dashboard widget, the widget displays information that is specific to the selected managed
Email Security — Server Edition System Administration Guide appliances only:
The following widgets can display information specific to managed Email Security —
Server Edition appliances:
l
Email Statistics Trend
l
Top Emails By Sender, Recipient, URL (Top 5)
l
Recent (25) Alerts
l
Email Campaign Trend
l
Emails Infection Trend
For details about these dashboard widgets, see the Email Security — Server Edition System
Administration Guide.
58
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Central Management Dashboard Widgets
File Protect Widgets in the Central Management
Dashboard
When the following badge appears in the upper-left corner of a Central Management
dashboard widget, the widget displays information that is specific to the selected managed
File Protect appliances only:
The following widgets can display File Protect-specific information:
l
Alerts Summary
l
Analyzed File Types (Top 5)
l
Infected File Types (Top 5)
l
Files Analyzed By Storages
For details about these dashboard widgets, see the File Protect System Administration Guide.
© 2022 FireEye Security Holdings US LLC
59
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Network Security Widgets in the Central Management
Dashboard
When the following badge appears in the upper-left corner of a Central Management
dashboard widget, the widget displays information that is specific to the selected managed
Network Security appliances only:
The following widgets can display Network Security-specific information:
l
Alerts Summary
l
Callback Events (Top 25)
l
Recent (25) Alerts
l
Critical Malware Detection
l
Threat Attacks
l
Infected Subnets (Top 25)
l
Infection Type Trend
l
Top Malware by Host and Activity
l
Monitored Traffic
l
IPS Trend
For details about these dashboard widgets, see the Network Security System Administration
Guide.
60
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Custom Dashboards
Custom Dashboards
You can create personal named dashboards that display only the dashboard widgets you
choose and cover the time periods you configure.
NOTE: The custom dashboards that you create can be accessed from your user
account only.
Any of the operations described in Dashboard and Widget Management on page 66 can be
performed on custom dashboards as well as the predefined dashboard FireEye Dashboard.
You can create a new dashboard by cloning an existing dashboard, or you can begin with
an empty dashboard. The dashboard names appear across the top of the Dashboard tab,
and you can change the order in which the names appear.
l
Cloning a Dashboard on the next page
l
Creating a New Dashboard on the next page
l
Reordering the Dashboard Names on page 63
The following operations apply to the current custom dashboard:
l
Renaming a Custom Dashboard on page 63
l
Designating the Default Dashboard on page 63
l
Deleting a Custom Dashboard on page 64
The following operations apply to widgets in the current custom dashboard:
l
Adding Widgets to a Custom Dashboard on page 64
l
Resizing a Widget in a Custom Dashboard on page 64
l
Moving a Widget in a Custom Dashboard on page 65
l
Removing a Widget from a Custom Dashboard on page 65
Prerequisites
l
Admin, Analyst, Monitor, or Operator access to the appliance.
l
You are logged in to the appliance Web UI.
© 2022 FireEye Security Holdings US LLC
61
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Cloning a Dashboard
Cloning creates a copy of a dashboard that is accessible to your user account only.
To clone a dashboard:
1. Click Dashboard and choose the dashboard you want to clone.
2. Click the dashboard-level More Options menu ( ) and choose Clone.
3. Enter a name for the new dashboard.
4. Click Clone.
5. To add a widget―Click Widget Libraries, then click Add for that widget.
Some widgets include configuration options. You can configure those settings now and
change them at any time:
l
Threat intelligence comparison options (such as Region and Industry)
l
Time period options (such as Day, Week, Month)
l
Data filtering options (such as whether to include acknowledged alerts)
6. To rearrange widgets―Drag a widget by its title bar to a new location in the
dashboard.
7. To remove a widget―Click the widget-level More Options menu ( ) and choose
Remove.
Creating a New Dashboard
Use the +Add option in the Dashboard page to create a new, empty dashboard that is
accessible to your user account only.
To create a new dashboard:
1. Click Dashboard, then click +Add.
2. Enter a name for the new dashboard, then click the check mark.
3. To add a widget―Click Widget Libraries, then click Add for that widget.
Some widgets include configuration options. You can configure those settings now and
change them at any time:
62
l
Threat intelligence comparison options (such as Region and Industry)
l
Time period options (such as Day, Week, Month)
l
Data filtering options (such as whether to include acknowledged alerts)
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Custom Dashboards
4. To rearrange widgets―Drag a widget by its title bar to a new location in the
dashboard.
5. To remove a widget―Click the widget-level More Options menu ( ) and choose
Remove.
Reordering the Dashboard Names
To rearrange dashboard names across the top of the Dashboard page, drag the dashboard
names.
Renaming a Custom Dashboard
Follow these steps to rename a custom dashboard. You cannot rename the predefined
dashboard FireEye Dashboard.
To rename a custom dashboard:
1. Access the custom dashboard that you want to rename.
2. Click the dashboard-level More Options menu ( ) and choose Rename.
3. Type the new name for the dashboard, and then click the check mark.
Designating the Default Dashboard
Follow these steps to designate any dashboard as the default dashboard. The default
dashboard appears when you log in to the appliance Web UI.
To designate the default dashboard:
1. Access the dashboard that you want to set as the default.
2. Click the dashboard-level More Options menu ( ) and choose Mark as Default.
© 2022 FireEye Security Holdings US LLC
63
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Deleting a Custom Dashboard
Follow these steps to remove a custom dashboard. You cannot delete the predefined
dashboard FireEye Dashboard.
To delete a custom dashboard:
1. Access the custom dashboard that you want to remove.
2. Click the dashboard-level More Options menu ( ) and choose Delete.
3. Click Yes, Delete.
Adding Widgets to a Custom Dashboard
Follow these steps to add widgets to a custom dashboard. You cannot add widgets to the
predefined dashboard FireEye Dashboard.
To add widgets to a custom dashboard:
1. Click Dashboard and choose the dashboard you want to edit.
2. Click Widgets Library.
3. Click Add to add a widget to the dashboard.
Resizing a Widget in a Custom Dashboard
Follow these steps to resize a widget in a custom dashboard. You cannot resize widgets in
the predefined dashboard FireEye Dashboard.
To resize a widget in a custom dashboard:
1. Access the custom dashboard that you want to resize.
2. Hover over the bottom right corner of the widget to change the cursor into a small
diagonal down arrow ( ).
3. Click and drag the corner to increase or decrease the widget width, height, or both.
64
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Custom Dashboards
Moving a Widget in a Custom Dashboard
Follow these steps to rearrange the order of widgets in a custom dashboard. You cannot
rearrange widgets in the predefined dashbiard FireEye Dashboard.
To rearrange widgets in a custom dashboard:
1. Click Dashboard and choose the dashboard you want to edit.
2. Drag individual widgets within the dashboard.
Removing a Widget from a Custom Dashboard
Follow these steps to remove a widget from a custom dashboard. You cannot remove
widgets from the predefined dashboard FireEye Dashboard.
To remove a widget from a custom dashboard:
1. Click Dashboard and choose the dashboard you want to edit.
2. Hover over the upper-right corner of the widget.
3. Click the widget-level More Options menu ( ) and choose Remove.
© 2022 FireEye Security Holdings US LLC
65
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Dashboard and Widget Management
You can view and manage the widgets accessible to your user account only. All user accounts
can access the predefined dashboard named FireEye Dashboard.
NOTE: A user account can access the custom dashboards that were created from that
account only. For more information, see Custom Dashboards on page 61.
The following operation applies to all dashboards accessible to your user account:
l
Configuring the Automatic Refresh Interval on the facing page
The following operations apply to the current dashboard:
l
Filtering the Data by Appliance or Appliance Group on the facing page
l
Refreshing the Data Displayed in All Widgets on the facing page
l
Configuring the Time Period Covered by All Widgets on page 68
l
Saving or Printing a Dashboard on page 68
The following operations apply to a single widget in the current dashboard:
l
Refreshing the Data Displayed in a Single Widget on page 68
l
Configuring the Time Period Covered by a Single Widget on page 69
l
Viewing a Single Widget in Full Screen Mode on page 69
Prerequisites
66
l
Admin, Analyst, Monitor, or Operator access to the appliance.
l
You are logged in to the appliance Web UI.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Dashboard and Widget Management
Configuring the Automatic Refresh Interval
Follow these steps to configure the interval at which the system automatically refreshes the
data displayed in all widgets in any dashboard accessible to your user account. By default,
the data displayed in the dashboard widgets is automatically refreshed every 10 minutes.
The appliance retains this account-wide setting until you change it.
To view and change the automatic refresh interval:
1. Click the page Settings menu (
) and choose Set Refresh Interval.
2. Choose the new auto-refresh interval: 5 minutes, 10 minutes, 15 minutes, or Custom.
If you choose Custom, specify an interval from 1 minute to 60 minutes.
3. Click Yes, Proceed.
Filtering the Data by Appliance or Appliance Group
Follow these steps to filter the data displayed in the current dashboard. You can display
data for a single managed appliance, for a group of managed appliances, or for all
managed appliances.
To filter the dashboard data by managed appliance or appliance group:
1. To filter by an appliance group, open the Group drop-down menu and select the group.
To remove the filter, select All.
2. To filter by an individual appliance, open the Appliance drop-down menu and select
the appliance name. To remove the filter, select All.
Refreshing the Data Displayed in All Widgets
Follow these steps for a one-time refresh of the data displayed in all widgets of the current
dashboard. This operation does not affect the global auto-refresh interval.
To refresh the data displayed in all widgets of the current dashboard:
1. Access the dashboard that you want to refresh.
2. Click the dashboard-level More menu ( ) and choose Refresh.
© 2022 FireEye Security Holdings US LLC
67
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
Configuring the Time Period Covered by All Widgets
For many of the dashboard widgets, you can configure the time period for which the
widget displays data. Typical time period options are daily, weekly, and monthly. Follow
these steps to configure the time period for all widgets in the current dashboard.
The appliance retains this dashboard-wide setting for your user account until you change
it. You can override this setting for an individual widget in the dashboard.
To configure the time period covered by all widgets in the current dashboard:
1. Access the dashboard you want to edit.
2. Click the dashboard-level More menu ( ) and choose Set Time Period.
3. Choose the new refresh rate for the dashboard widgets: Day, Week, or Month.
4. Click Yes, Proceed.
Saving or Printing a Dashboard
Follow these steps to save the current dashboard to a PDF file. You can also print the
dashboard to a printer directly.
To print or save the current dashboard:
1. Click Dashboard and choose the dashboard you want to print or save.
2. Click the dashboard-level More menu ( ) and choose Print PDF.
3. To print a copy of the dashboard, select the printer settings and then click Print.
4. To save a copy of the dashboard, select Save as PDF, specify the file location, and then
click Save.
Refreshing the Data Displayed in a Single Widget
Follow these steps for a one-time refresh of the data displayed in a single widget of the
current dashboard. This operation does not affect the global auto-refresh interval.
To refresh the data displayed in a single widget in the current dashboard:
1. Click Dashboard and choose the dashboard that contains a widget you want to refresh.
2. Hover over the upper-right corner of the widget.
3. Click the Refresh icon (
68
).
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Scheduling Dashboard Reports
Configuring the Time Period Covered by a Single Widget
For many of the dashboard widgets, you can configure the time period for which the
widget displays data. Typical time period options are daily, weekly, and monthly. Follow
these steps to configure the time period for a single widget in the current dashboard.
The appliance retains this widget-specific setting for your user account until you change it
or unless you change the dashboard-wide time period.
To configure the time period covered by a single widget in the current dashboard:
1. Click Dashboard and choose the dashboard that contains the widget whose time
period you want to change.
2. Choose the time period for which data is to be displayed.
Viewing a Single Widget in Full Screen Mode
Follow these steps to expand a single widget and view it in full screen mode
To view a single widget in full screen mode:
1. Click Dashboard and choose the dashboard you want to view in full screen mode.
2. Hover over the upper-right corner of the widget.
3. Click the Full Screen icon (
).
Generating and Scheduling Dashboard
Reports
For each dashboard on the CM appliance Web UI, you can generate a single report, or
schedule reports to run periodically. The report contains data from all the widgets on the
dashboard. You can view generated reports on the Reports > Static Reports page, and view
scheduled reports on the Reports > Schedule Reports page. To delete or download the
report, click the Action icon in the Action column.
NOTE: Some widgets hold data for a maximum of one month. If you specify a time
frame longer than this, the report highlights that it contains only one month of data
for these widgets.
To generate a report from the dashboard:
© 2022 FireEye Security Holdings US LLC
69
Central Management System Administration Guide
CHAPTER 3: The Appliance Dashboard
1. Click the More Options menu and then click Generate Report.
2. Select the report format. You can choose CSV, JSON, or XML.
3. Select the time frame that the report covers and click Apply.
You can also generate a report from the Report > Static Reports page.
To schedule a report from the dashboard:
1. Click the More Options menu and then click Schedule Report.
2. In Scheduled, select how often you want to generate a report. You can choose
hourly, daily, weekly, or monthly.
3. Enter the time of day, day of the week, and day of the month where applicable.
4. Select the delivery method, the report format, and the time frame that the report
covers.
5. Click Schedule.
You can also schedule a report from the Report > Schedule Reports page.
70
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
PART II: Configuration
l
Accessing the Physical or Serial Console on page 73
l
Initial Configuration on page 77
l
Virtual Central Management Appliances on page 89
l
License Keys on page 91
l
The DTI Network on page 105
l
System Security on page 139
l
Date and Time Settings on page 157
l
System Email Settings on page 141
© 2022 FireEye Security Holdings US LLC
71
Central Management System Administration Guide
72
PART II: Configuration
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 4: Accessing the
Physical or Serial Console
Use one of the methods in this section to establish a connection with the physical or serial
console.
Physical Console Method
You can connect keyboard and video cables to the appliance and then log in to the CM
CLI. See your Hardware Administration Guide to view the port locations
To access the physical console:
l
Plug in a keyboard and a VGA monitor.
Serial Console Methods
If you are not using a terminal server, you need to be physically near the CM appliance to
use the serial port. The serial port is on the back of the appliance. See your Hardware
Administration Guide to view the port location.
The serial port uses the following settings:
l
Baud rate: 115200
l
Data bits: 8
l
Stop bits: 1
l
Parity: None
l
Flow control: XON/XOFF
© 2022 FireEye Security Holdings US LLC
73
Central Management System Administration Guide
CHAPTER 4: Accessing the Physical or Serial Console
NOTE: If the appliance stops responding on startup without displaying an error
message, the serial port or the connection may be faulty. If this occurs, do the
following:
1. Press and hold the power button on the front of the appliance for a few
seconds until the appliance powers off.
2. Unplug all power cables from the server and wait for about 5 minutes to
ensure shutdown is complete.
3. Connect a different serial cable.
4. Plug in the power cables.
5. If the server does not automatically restart, press the power button.
You can access the serial port as described in the following topics:
l
PC or Mac below
l
Linux below
l
Terminal Server on the facing page
PC or Mac
Because laptops do not usually have a serial port, you need a USB-to-serial cable to
connect the laptop to the DB-9 serial port of the CM appliance. Trellix uses Prolific
Technology Inc. adapters.
IMPORTANT! A USB-to-serial cable is not provided with the appliance.
To access the serial console from a PC or Mac laptop:
1. Connect the USB-to-serial cable to the USB port of the laptop.
2. Connect one end of the null modem cable that is provided with the appliance to the
USB-to-serial cable.
3. Connect the other end of the null modem cable to the serial port of the appliance.
4. Use a serial application (such as PuTTY) to establish a connection. Specify the COM
port assigned to the USB-to-serial cable.
Linux
You can use a serial cable or a USB-to-serial cable to connect the Linux machine to the
serial port of the CM appliance. Trellix uses Prolific Technology Inc. adapters.
74
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
IMPORTANT! A USB-to-serial cable is not provided with the appliance.
To access the serial console from a Linux machine:
1. Connect the cable to the serial port of the appliance and to the Linux machine.
2. From a command prompt, establish a connection. If you are using a USB-to-serial
cable, specify the COM port assigned to it.
Terminal Server
To access the serial console from a terminal server:
1. Set the terminal server to a baud rate of 115200.
2. Plug one end of a serial cable into the DB-9 serial port on the CM appliance and
plug the other end into the terminal server.
3. In a Telnet application (such as PuTTY), enter the host name or terminal server IP
address, the terminal server port number that the appliance is using, and the
appliance port number.
© 2022 FireEye Security Holdings US LLC
75
Central Management System Administration Guide
76
CHAPTER 4: Accessing the Physical or Serial Console
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
This section covers the following information:
l
Initial Configuration Overview on the next page
l
Initial Configuration Prerequisites on the next page
l
Use one of the following methods to configure initial settings:
o
Configuring Initial Settings Using a Keyboard and Monitor on page 79
o
Configuring Initial Settings Using the Serial Console Port on page 80
o
Configuring Initial Settings Using the LCD Panel on page 84
For information about responding to the configuration wizard prompts, refer to
Configuration Wizard Steps on page 82.
l
Configuring the IPMI Interface on page 85
© 2022 FireEye Security Holdings US LLC
77
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
Initial Configuration Overview
The management interface is the port through which the CM appliance is managed and
administered. It is also the port through which an appliance is managed by the Central
Management appliance. With the single-port address type, the management interface is
also the port through which a managed appliance requests and downloads software
updates from the DTI network.
Initial settings need to be configured to set up the management interface, and to allow
access to the network, change the default administrator password, and so on. The
following initial configuration methods are available:
Use one of the following methods to log in to the CM CLI and configure initial settings:
l
l
l
Keyboard and monitor—Connect a USB keyboard and VGA monitor directly to the
USB 3.0 ports and a video port that are on the rear panel of the appliance. This is
the easiest way to configure the initial settings, provided that you are physically
near the appliance.
Serial port—Connect a Windows laptop, a Mac laptop, a Linux system, or a
terminal server to the appliance serial port. The serial port is on the rear panel.
LCD panel—Use the navigation buttons and menus on the liquid crystal display
(LCD) panel to select initial settings. The LCD panel is on the front of most
appliance models.
Be sure to cable and configure the IPMI interface so that you can access the appliance
should it become unresponsive to network or serial port access.
NOTE: You must access the appliance through the serial port if you want to
monitor appliance boot activities. You can enter CLI commands through direct
keyboard and monitor connection only before the boot loader begins loading the
kernel, for example, to post output, and after the boot is completed.
Initial Configuration Prerequisites
Before you configure the appliance:
78
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Initial Settings Using a Keyboard and Monitor
l
Read the Release Notes for the current release.
l
Collect the following information from your network administrator:
o
Static IP address, subnet mask, and default gateway address for the appliance
management interface. (You do not need this information if Dynamic Host
Configuration Protocol (DHCP) will be used on the management interface.)
o
IP address for each Domain Name System (DNS) server (if DNS name
resolution will be used).
o
IP address for each Network Time Protocol (NTP) server (if
NTP synchronization will be used).
o
Telnet or SSH client on the remote system (if the appliance will be managed
remotely).
IMPORTANT: Endpoint Security Server needs to have both an IPv4 and
IPv6 address in order to communicate with the Trellix DTI server, which is
required for license validation, Agent installer package downloads, Server
package downloads, and IOC content.
l
If you plan to configure initial settings using the serial console port and a Windows
or Mac laptop, obtain a USB-to-serial cable.
Configuring Initial Settings Using a
Keyboard and Monitor
You can connect keyboard and video cables to the appliance and then log in to the CM CLI
to perform the initial configuration. See your Hardware Administration Guide to view the
port locations.
To configure initial settings using a keyboard and monitor:
1. Plug in a keyboard and a VGA monitor.
2. When prompted, enter the default username (admin) and password (admin) for the
permanent "admin" user.
3. You are asked to accept the End User License Agreement (EULA). Enter y to accept
the terms of the agreement.
4. Enter y when you are prompted to use the Configuration Wizard for initial
configuration. Then respond to the prompts as described in Configuration Wizard
Steps on page 82.
5. After you answer the questions, the wizard summarizes your answers. To change
an answer, enter the step number. Press Enter to save changes.
© 2022 FireEye Security Holdings US LLC
79
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
Configuring Initial Settings Using the
Serial Console Port
If you are not using a terminal server, you need to be physically near the CM appliance to
use the serial port. The serial port is on the back of the appliance. See your Hardware
Administration Guide to view the port location.
The serial port uses the following settings:
l
Baud rate: 115200
l
Data bits: 8
l
Stop bits: 1
l
Parity: None
l
Flow control: XON/XOFF
NOTE: If the appliance stops responding on startup without displaying an error
message, the serial port or the connection may be faulty. If this occurs, do the
following:
1. Press and hold the power button on the front of the appliance for a few
seconds until the appliance powers off.
2. Unplug all power cables from the server and wait for about 5 minutes to
ensure shutdown is complete.
3. Connect a different serial cable.
4. Plug in the power cables.
5. If the server does not automatically restart, press the power button.
Configure initial settings as described in the following topics:
l
Using a Windows or Mac Laptop below
l
Using a Linux System on the facing page
l
Using a Terminal Server on the facing page
Using a Windows or Mac Laptop
Use the procedure in this section to configure initial settings from a Windows or Mac
laptop.
80
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Initial Settings Using the Serial Console Port
To configure initial settings from a Windows or Mac laptop:
1. Establish a connection with the serial console as described in PC or Mac on page 74.
2. When prompted, enter the default username (admin) and password (admin) for the
administrator.
3. You are asked to accept the End User License Agreement (EULA). Enter y to accept
the terms of the agreement.
4. Enter y when you are prompted to use the Configuration Wizard for initial
configuration. Then respond to the prompts as described in Configuration Wizard
Steps on the next page.
5. After you answer the questions, the wizard summarizes your answers. To change
an answer, enter the step number. Press Enter to save changes.
Using a Linux System
Use the procedure in this section to configure initial settings from a Linux system.
To configure initial settings from a Linux system:
1. Establish a connection with the serial console as described in Linux on page 74.
2. When prompted, enter the default username (admin) and password (admin) for the
administrator.
3. You are asked to accept the End User License Agreement (EULA). Enter y to accept
the terms of the agreement.
4. Enter y when you are prompted to use the Configuration Wizard for initial
configuration. Then respond to the prompts as described in Configuration Wizard
Steps on the next page.
5. After you answer the questions, the wizard summarizes your answers. To change
an answer, enter the step number. Press Enter to save changes.
Using a Terminal Server
Use the procedure in this section to configure initial settings from a terminal server.
To configure initial settings from a terminal server:
1. Establish a connection with the serial console as described in Terminal Server on
page 75.
2. When prompted, enter the default username (admin) and password (admin) for the
administrator.
3. You are asked to accept the End User License Agreement (EULA). Enter y to accept
the terms of the agreement.
© 2022 FireEye Security Holdings US LLC
81
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
4. Enter y when you are prompted to use the Configuration Wizard for initial
configuration. Then respond to the prompts as described in Configuration Wizard
Steps below.
5. After you answer the questions, the wizard summarizes your answers. To change
an answer, enter the step number. Press Enter to save changes.
Configuration Wizard Steps
The configuration wizard is typically used to perform the initial configuration of the
system. See Initial Configuration on page 77 for information about running the wizard
before the management interface is configured. After the management interface is
configured, an administrator can use the configuration jump-start CLI command to run
the wizard.
The following table describes the questions the configuration wizard prompts you to
answer as it moves through the wizard steps. As noted in the table, the wizard skips some
steps based on your answers to previous steps.
NOTE: To exit the configuration wizard, press CTRL+C. To restart the configuration
wizard, use the configuration jump-start command.
Step
82
Response
Activation code?
(Virtual KVM
deployments only)
Enter the activation code you obtained from Trellix.
Hostname?
Enter the hostname for the appliance.
Admin password?
Enter a new administrator password. The new password must
be 8–32 characters. If you do not change the password, the
administrator will be unable to log in to the appliance.
Confirm admin
password?
Re-enter the new administrator password.
Enable remote access
for ‘admin’ user?
Enter yes to enable the administrator to log in to the appliance
remotely. Enter no to disable remote access.
Use DHCP on ether1
interface?
Enter yes to use Dynamic Host Configuration Protocol (DHCP)
to configure the appliance IP address and other network
parameters. Enter no to manually configure your IP address and
network settings. (If you enter yes, the zeroconf and static
IP addressing steps are skipped.)
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuration Wizard Steps
Step
Response
Use zeroconf on
ether1 interface?
Enter yes to use zero-configuration (zeroconf) networking. Enter
no to specify a static IP address and network mask. (If you
specify yes, the next step is skipped.) NOTE: Do not use
zeroconf on the primary interface.
Primary IP address
and masklen?
Enter the IP address for the management interface in A.B.C.D
format and enter the network mask, for example: 1.1.1.2/12.
Default gateway?
Enter the gateway IP address for the management interface.
Primary DNS server?
Enter the IP address of the DNS server.
Domain name?
Enter the domain for the management interface; for example:
it.acme.com.
Enable fenet service?
Enter yes to enable access to the DTI network. (If you enter no,
the next three steps are skipped.)
Enable fenet license
update service?
Enter yes to enable the licensing service to automatically
download your licenses from the DTI network and install them.
(If licenses are downloaded and installed successfully, the
wizard skips the step that prompts for the product license key
and the step that prompts for the security-content updates key.)
Sync appliance time
with fenet?
Enter yes to synchronize the appliance time with the DTI server
time. If you enabled the licensing service, synchronization
prevents a feature from being temporarily unlicensed due to a
time gap. The wizard makes three attempts to perform this step
before it gives up and moves to the next step.
Update licenses from
fenet?
Enter yes to download and install your licenses. The wizard
makes three attempts to perform this step before giving up and
moving on to the next step.
Enable NTP?
Enter yes to enable automatic time synchronization with one or
more Network Time Protocol (NTP) servers. Enter no to
manually set the time and date on the appliance. (This step is
skipped if you entered yes in the "Sync appliance time with
fenet?" step.) If you enter no, specify the time and date in
Greenwich Mean Time (GMT).
Set time
(<hh>:<mm>:<ss>)?
Enter the system time for the appliance. (This step and the next
step are skipped if you entered yes in the "Sync appliance time
with fenet?" or "Enable NTP?" step.)
© 2022 FireEye Security Holdings US LLC
83
Central Management System Administration Guide
Step
CHAPTER 5: Initial Configuration
Response
Set date
Enter the date corresponding to the system time for the
(<yyyy>/<mm>/<dd>)? appliance.
Enable IPv6?
Enter yes to enable IPv6 protocol, which changes network
IP routing from IPv4 to IPv6.
Enable IPv6
autoconfig (SLAAC)
on ether1 interface?
Enter yes to enable IPv6 autoconfig on the ether1 (management
interface) port. (This step is skipped if you entered no in the
"Enable IPv6?" step.)
Enable DHCPv6 on
ether1 interface?
Enter yes to use DHCPv6 to configure IPv6 hosts with IP
addresses. (This step is skipped if you entered no in the "Enable
DHCP?" or "Enable IPV6?" step.)
Product license key?
Enter the product license key you obtained from Trellix, or press
Enter to install a 15-day evaluation license. (This step and the
next step are skipped if you entered yes in the "Enable fenet
license update service?" step and if licenses were successfully
installed as a result.)
Security-content
updates key?
Enter the security-content license key you obtained from Trellix,
or press Enter to skip this step and install the license later.
Configure CMS HA?
Enter yes to configure the Central Management appliance in a
high availability (HA) environment. (For the remaining
HA configuration steps, see the Central
Management High Availibility Guide.)
(Physical models and
selected virtual models
only)
Configuring Initial Settings Using the
LCD Panel
An LCD panel is available on the front of some appliance models.
To configure initial settings from the LCD panel:
1. Press the center button to access the Network menu and respond to the prompts:
a. Hostname—Specify the hostname for the system.
b. DHCP enabled—Enter yes to use dynamic host configuration protocol
(DHCP). Enter no to manually configure your IP address and network
settings. If you entered yes, proceed to the IPv6 enabled step.
84
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring the IPMI Interface
c. Static IP address—Enter the IP address for the Ethernet 1 (management
interface) port.
d. Netmask—Enter the network mask.
e. Default gateway—Enter the gateway IP address for the management
interface.
f. Primary DNS—Enter the primary DNS server IP address.
g. Domain name—Enter the domain name for the management interface; for
example, it.acme.com.
h. IPv6 enabled—Enter yes to enable IPv6 protocol, which changes network
IP routing from IPv4 to IPv6. If you enter no, proceed to the Admin net login
step.
i. SLAAC enabled—Enter yes to enable IPv6 autoconfig on the ether1
(management interface) port. Enter no to disable IPv6 autoconfig on the
ether1 (management) interface port.
j. Admin net login—Enter yes to enable the administrator to log in to the
system remotely. Enter no to disable remote access.
2. Press the left or right arrow button until you reach the LCD menu. At the Password
prompt, enter a password used to access the LCD panel. (This is not the password
used to access the appliance Web UI or CLI.)
3. Press the left or right arrow button until you reach the Config Options menu. At the
Reset admin password prompt:
a. Press the center button to reset the password used by the permanent admin
user to log in to the appliance Web UI or CLI. (This is not the password used
to access the LCD panel.)
b. A randomly generated password is displayed. After you memorize it, press
the center or exit button to dismiss the display.
After the initial configuration, you can change to a password of your choice using
the appliance Web UI or CLI.
Configuring the IPMI Interface
Use the commands in this section to configure the IPMI interface. For information about
using the IPMI interface after it is configured, see The CM Appliance IPMI Interface on
page 44.
© 2022 FireEye Security Holdings US LLC
85
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
Prerequisites
l
One end of an Ethernet cable is plugged in to the IPMI port, and the other end of the
cable is plugged in to an administrative computer or terminal server
Viewing the IPMI Configuration
This procedure describes how to use the CLI to view the IPMI configuration.
To view the IPMI configuration:
1. Go to CLI enable mode:
hostname > enable
2. Display the configuration. For example:
hostname (config) # show ipmi interface
IPMI LAN Settings
---------------------------------------Admin Shut Down
: no
Shut Down
: no
IP Address Source
: Static Address
IP Address
: 192.168.42.27
Subnet Mask
: 0.0.0.0
Default Gateway IP
: 0.0.0.0
Configuring the IPMI Port
This procedure describes how to use CLI commands to configure the IPMI interface.
To configure the IPMI port:
1. If you want to configure a static IP address for the IPMI interface, do the following:
a. Log in to the appliance CLI.
b. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
c. If DHCP was previously configured for IPMI, change to the static method:
hostname (config) # ipmi lan ipsrc static
d. Configure the IP address for the IPMI interface:
hostname (config) # ipmi lan ipaddr <ipAddress>
e. Configure the netmask for the IPMI interface:
hostname (config) # ipmi lan netmask <netMask>
f. Configure the default gateway for the IPMI interface:
hostname (config) # ipmi lan defgw <ipAddress>
86
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring IPv6 Addresses for the IPMI Interface
2. If you want to configure DHCP:
a. Make sure that DHCP is enabled on your network:
hostname (config) # show ip dhcp
b. Enable DHCP:
hostname (config) # ipmi lan ipsrc dhcp
3. The default username for logging in to the IPMI Web UI is ADMIN. Configure the
password. The password must be a minimum of five characters, and a maximum of
20 characters.
hostname (config) # ipmi user set password <password>
4. Save your changes.
hostname (config) # write memory
To revert to the default configuration:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Revert to the default configuration:
hostname (config) # ipmi lan ipsrc static
3. Save your changes.
hostname (config) # write memory
NOTE: It is important to use the latest IPMI firmware available for your system. For
details, see IPMI and BIOS Firmware Updates on page 213.
Configuring IPv6 Addresses for the
IPMI Interface
IMPORTANT: You can configure IPv6 addresses for the IPMI interface only for CM
7500 and CM 9500 appliances.
Use the instructions in this section to configure an IPv6 Address for the IPMI interface
using the CLI. For information about using the IPMI interface, see The CM Appliance
IPMI Interface on page 44.
© 2022 FireEye Security Holdings US LLC
87
Central Management System Administration Guide
CHAPTER 5: Initial Configuration
Prerequisites
l
l
One end of an Ethernet cable is plugged in to the IPMI port, and the other end of the
cable is plugged in to an administrative computer or terminal server
Upgrade IPMI firmware version to 2.37. For details, see Updating IPMI and BIOS
Firmware on page 214.
To configure an IPv6 address for the IPMI interface using the CLI:
1. Log in to the appliance CLI.
2. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
3. Configure the static IPv6 address for the IPMI interface:
hostname (config) # ipmi lan6 ipaddr <valid IPv6 Address> prefix <1128>
4. To enable DHCP on your network:
hostname (config) # ipmi lan6 dhcp enable
5. Save your changes:
hostname (config) # write memory
6. Display the configuration. For example:
hostname (config) # show ipmi interface
IPMI LAN Settings
---------------------------------------Admin Shut Down
: no
Shut Down
: (n/a)
Set in Progress
: Set in Progress
IP Address Source
: DHCP Address
IPMI LAN6 Settings
---------------------------------------Static ipv6 Address
: 2015:9:19:ffff::da7/64
Dhcp ipv6 Address
: 2015:9:19:ffff::da7/64
88
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 6: Virtual Central
Management Appliances
A virtual Central Management appliance is a virtual instance of a physical Central
Management appliance. It manages a virtual appliance the same way it manages a
physical appliance, but requires no hardware. The same virtual Central Management
appliance can manage both physical and virtual appliances.
For information about deploying and working with virtual appliances, see the FireEye
Device Deployment Guide on the Trellix documentation portal at https://docs.fireeye.com/.
© 2022 FireEye Security Holdings US LLC
89
Central Management System Administration Guide
90
CHAPTER 6: Virtual Central Management Appliances
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About Trellix License Keys
CHAPTER 7: License Keys
This section covers the following information:
l
About Trellix License Keys below
l
Types of Licenses on page 93
l
Overriding One-Way Sharing License on page 93
l
Automatic License Updates on page 95
l
Manual License Installation on page 98
l
Viewing License Notifications Using the Web UI on page 102
About Trellix License Keys
License keys are required for system operation. The CM appliance requires these license
keys:
License Key
Description
FIREEYE_
Required to register your system and use the product features.
APPLIANCE
© 2022 FireEye Security Holdings US LLC
91
Central Management System Administration Guide
CHAPTER 7: License Keys
License Key
Description
CONTENT_
UPDATES
Allows your system to access the Dynamic Threat Intelligence (DTI)
network, which provides the latest intelligence on advanced cyber attacks
and malware callback destinations.
This enables Trellix products to proactively recognize new threats and
block attacks.
The two-way sharing license provides your appliance with malware
intelligence from the DTI network and shares data about malware
analyzed by your appliance.
The one-way sharing license provides your appliance with malware
intelligence, but no information is submitted to the DTI cloud.
l
You can use the analysis one-way-override enable command
to override the one-way sharing CONTENT_UPDATES license on
your appliance and send requests to unity.fireeye.com.
IMPORTANT: See About Support and Content License Sharing
Combinations on page 109.
NOTE: When you use a one-way license, locally generated intel is shared
across all appliances attached to the Central Management appliance.
FIREEYE_
SUPPORT
Allows your system to receive software image updates and the latest
guest images and depending on your sharing option, upload telemetry
and statistics to the DTI cloud.
The two-way sharing license allows the appliance to upload telemetry
and statistics to the DTI cloud for Trellix to monitor. The one-way sharing
license does not upload telemetry and statistics to the DTI cloud.
IMPORTANT: See About Support and Content License Sharing
Combinations on page 109.
NOTE: Click here for information about proactive support for issues
Trellix observes in uploaded telemetry and statistics.
The following licenses are optional:
NOTE: The functionality provided by optional licenses is disabled if the FIREEYE_
APPLIANCE license is invalid.
License Key
ATI
92
Description
Allows your appliance to use Advanced
Threat Intelligence features.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Types of Licenses
License Key
Description
MD_ACCESS
Allows Trellix products to connect to the
Managed Defense VPN. Without this
license, Managed Defense cannot manage
the server.
DA_HANCOM
Allows your appliance to perform dynamic
analysis of Hancom Office files.
If licenses have expired or will expire within 30 days, warnings are displayed on the
Appliance License Settings page. For details, see Viewing License Notifications Using the
Web UI on page 102.
If licenses have expired or will expire within 30 days, warnings are displayed on the
Central Management License Settings page. For details, see Viewing License Notifications
Using the Web UI on page 102.
Types of Licenses
Licenses on the Central Management appliance can be purchased in two ways.
Subscription-Based Appliance License
This appliance license has an expiry date. When the license expires, the appliance stops
inspecting as well as the passing of traffic. The user can only access the license screens
and cannot use the appliance.
Perpetual Appliance License
This appliance license does not expire. The customer owns the appliance and has
unlimited access to all the features. The appliance will continue to inspect with the latest
updated OS and SC.
Overriding One-Way Sharing License
A one-way sharing license on the appliance provides the CM appliance with malware
intelligence, but no information is submitted to AV-Suite and FAUDE. When you override
the setting for one-way license sharing, the appliance is allowed to submit information
such as an MD5 checksum to the AV-Suite and FAUDE for further malware analysis.
© 2022 FireEye Security Holdings US LLC
93
Central Management System Administration Guide
CHAPTER 7: License Keys
Prerequisites
l
Admin or Operator access to the appliance
l
A one-way or two-way sharing CONTENT_UPDATES license
l
Verify that AV-Suite integration is enabled and that AV-Suite version 6 is
configured. Use the show static-analysis config command.
Override One-Way Sharing License Using the CLI
Follow these steps to override the one-way sharing license setting and share information
with AV-Suite and FAUDE from the CM appliance.
To override the one-way sharing license:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Override the one-way sharing license on the appliance.
hostname (config) # analysis one-way-override enable
3. Verify that the one-way sharing license was overridden.
hostname # show analysis one-way-override
one_way license override
:Enabled
3. Save your changes:
hostname (config) # write memory
To return the one-way sharing license to its default setting:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Return the one-way sharing license to its default setting.
hostname (config) # no analysis one-way-override enable
3. Verify that the one-way sharing license has returned to its default setting.
hostname # show analysis one-way-override
one_way license override
:Disabled
4. Save your changes:
hostname (config) # write memory
94
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Automatic License Updates
Automatic License Updates
The license update feature enables the CM appliance with basic network connectivity to
automatically download licenses from the DTI network and install them. This feature
provides the following benefits:
l
l
l
Minimal initial configuration—The license update feature is enabled with the
configuration jump-start wizard during the initial system configuration. This means
the feature can be fully functional after the jump-start wizard is completed.
Simplified license management—There is no need to contact Trellix for license keys
when new features are added or when licenses are renewed, because the new
licenses are automatically downloaded and installed.
Scalability—Organizations, such as those with a large number of appliances, can
benefit from all appliances being updated automatically, instead of entering license
keys manually on each appliance, one at a time.
You can enable automatic license updates on the CM appliance using the configuration
wizard or the CLI.
How It Works
The license update feature, if enabled, downloads and applies licenses to which the
customer is contractually entitled. If an active license for a feature is already installed and
the licensing service downloads an active license for the feature, the installed license is
replaced by the downloaded license only if the downloaded license offers new
functionality, a later expiry date, or was part of a more recent customer order. This process
is automatic; however, you can also explicitly update licenses.
The license update feature will not:
l
l
Install a downloaded license that would cause a feature to become temporarily
unlicensed.
Remove a feature license if there is no newly ordered replacement for it.
If you experience issues with a license retrieved from an automatic update, you can use the
command no fenet license update enable to disable the automatic update process and
you can use the command license install <cr> to manually install your older license
key or keys.
You can synchronize the system time to the DTI server time to prevent a feature from being
temporarily unlicensed due to time differences. This is a one-time synchronization, but it
can be repeated.
When an appliance is managed by the Central Management appliance, the Central
Management appliance acts as a proxy between the managed appliance and the licensing
service. The license update feature must still be enabled on the managed appliance. In
© 2022 FireEye Security Holdings US LLC
95
Central Management System Administration Guide
CHAPTER 7: License Keys
such an integrated environment, the Central Management appliance acts as the DTI server
for the managed appliances, so the licensing service uses the Central Management DTI
network credentials instead of the appliance's credentials.
Enabling Automatic License Updates
This section describes two ways to enable automatic license updates on the CM appliance.
Configuration Wizard Method
The configuration wizard is typically used to initially configure a new system. The wizard
steps, which include the following license activation steps, allow a customer to have a
functioning system with only minimal configuration.
l
Enable fenet service?
l
Enable fenet license update service?
l
Sync appliance time with fenet?
l
Update licenses from fenet?
For details about the wizard steps, see Configuration Wizard Steps on page 82.
CLI Method
The following topic describes how to use CLI commands to enable and work with the
license update feature:
l
Enabling Automatic License Updates Using the CLI below
Prerequisites
l
l
l
l
An established connection between the appliance and the Internet.
Operator or Admin access to enable the license update feature and download and
install licenses.
DTI network access to allow the appliance to get updates directly from the
DTI network.
(Optional) Admin access to synchronize the system clock with the DTI server clock.
Enabling Automatic License Updates Using the CLI
When the license update feature is enabled, license updates are automatic. You can also
explicitly update licenses.
96
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Automatic License Updates
To verify and enable automatic license updates:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Verify the license update feature status:
hostname (config) # show fenet license
fenet License Update Service
Licensing service: Administratively enabled
Last time licensing service was contacted: 2014/08/11 10:50:04
Last time licensing service was contacted successfully: 2014/08/11
10:50:04
Last time keys from licensing service were applied: 2014/08/07 17:50:03
3. If the license update feature service is disabled, enable it:
hostname (config) # fenet license update enable
4. Save your changes:
hostname (config) # write memory
NOTE: See Synchronizing the System Clock to DTI Server Time Using the CLI on
page 170 for an option that prevents potential licensing issues if there is a time gap
between the two clocks.
To explicitly update licenses:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Update licenses:
hostname (config) # fenet license update
3. Save your changes:
hostname (config) # write memory
To disable automatic license updates:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable the feature:
hostname (config) # no fenet license update enable
3. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
97
Central Management System Administration Guide
CHAPTER 7: License Keys
Manual License Installation
If the license update feature is not enabled, you need to install license keys manually.
Licenses need to be installed when an evaluation license expires or when a license expires
or no longer meets your needs. In addition, replacement licenses need to be installed after a
Return Material Authorization (RMA).
You can obtain your license keys from the Assets tab in the Trellix Customer Support
Portal or by sending an email that includes the MAC address of your appliance to key_
request@fireeye.com.
There are two ways to manually install licenses, described in the following topics:
l
Installing Licenses Using the Web UI below
l
Installing Licenses Using the CLI on page 100
Installing Licenses Using the Web UI
Use the CM License Settings page to install licenses on the Central Management
appliance.
98
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Manual License Installation
NOTE: Clicking the Enable VPN link in the Description column for an MD_
ACCESS license allows you to connect the appliance to Managed Defense (formerly
called FireEye as a Service) over the Internet using a secure SSL VPN connection.
For details, see the Managed Defense Quick Start Guide.
Prerequisites
l
Admin or Operator access.
l
The appliance does not already have the type of license key you are installing.
To install license keys using the Web UI:
1. Click the Settings tab.
2. Click CM Licenses on the sidebar.
3. Click Add License. The Add License dialog box opens.
4. Paste the license key you obtained from Trellix in the License Key box.
5. Click Add.
The page refreshes to show the license key in the table. If the key is valid, the Valid
column shows a check mark and additional information is displayed about the
license.
Removing Licenses Using the Web UI
Use the CMS License Settings page to remove Central Management licenses.
© 2022 FireEye Security Holdings US LLC
99
Central Management System Administration Guide
CHAPTER 7: License Keys
Prerequisites
l
Admin or Operator access
To remove license keys:
1. Click the Settings tab.
2. Click CMS Licenses on the sidebar.
3. Click the icon in the Delete column in the row for the license you want to remove.
4. Click Yes in the confirmation message that appears.
Installing Licenses Using the CLI
Use the CLI commands in this topic to install licenses on the CM appliance.
Prerequisites
l
Admin or Operator access
To install licenses:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Install each license:
hostname (config) # license install <key1> <key2> <key3>
NOTE: You can enter the license keys sequentially separated by spaces as
shown above, or enter license install and then press Enter to be prompted
to enter the license keys one at a time.
100
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Manual License Installation
3. Verify the licenses:
hostname (config) # show licenses
License 1: LK2-FIREEYE_APPLIANCE-0000-0000-0000-0000-0000-0000-00000000-0000
Feature:
FIREEYE_APPLIANCE
Description:
FireEye Appliance
Valid:
yes
Start date:
2016/11/21 (ok)
Tied to Appl ID:
000000000000 (ok)
Product:
eMPS (ok)
Type:
PROD (ok)
Agreement:
EULA (ok)
Active:
yes
...
License 2: LK2-CONTENT_UPDATES-0000-0000-0000-0000-0000-0000-0000-00000000
Feature:
CONTENT_UPDATES
Description:
Content updates
Valid:
yes
Start date:
2016/11/21 (ok)
End date:
2017/11/21 (ok)
Tied to Appl ID:
000000000000 (ok)
Sharing:
all (ok)
Active:
yes
License 3: LK2-FIREEYE_SUPPORT-0000-0000-0000-0000-0000-0000-0000-00000000
Feature:
FIREEYE_SUPPORT
Description:
FireEye Support
Valid:
yes
Start date:
2016/11/21 (ok)
End date:
2017/11/21 (ok)
Tied to Appl ID:
000000000000 (ok)
Sharing:
all (ok)
Active:
yes
...
4. Save your changes:
hostname (config) # write memory
Removing Licenses Using the CLI
Use the CLI commands in this topic to remove licenses.
Prerequisites
l
Admin or Operator access
To remove licenses:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
101
Central Management System Administration Guide
CHAPTER 7: License Keys
2. List the installed licenses:
hostname (config) # show licenses
License 1: LK2-FIREEYE_APPLIANCE-0000-0000-0000-0000-0000-0000-0000
Feature:
FIREEYE_APPLIANCE
Description:
FireEye Appliance
Valid:
yes
Start date:
2016/11/01 (ok)
Tied to appl ID:
000000000000 (ok)
Product:
MPS (ok)
Type:
PROD (ok)
Agreement:
EULA (ok)
Op Mode:
inline (ok)
Active:
yes
...
License 2: LK2-CONTENT_UPDATES-0000-0000-0000-0000-0000-0000-0000
Feature:
CONTENT_UPDATES
Description:
Content updates
Valid:
yes
Start date:
2016/11/01 (ok)
End date:
2017/11/01 (ok)
Tied to appl ID:
000000000000 (ok)
Sharing:
all (ok)
Active:
yes
License 3: LK2-FIREEYE_SUPPORT-0000-0000-0000-0000-0000-0000-0000
Feature:
FIREEYE_SUPPORT
Description:
FireEye Support
Valid:
yes
Start date:
2016/11/01 (ok)
End date:
2017/11/01 (ok)
Tied to appl ID:
000000000000 (ok)
Sharing:
all (ok)
Active:
yes
3. Specify the license ID to remove an individual license. For example, 3 is the license
ID for the Support license shown in the previous example.
hostname (config) # license delete 3
4. Save your changes.
hostname (config) # write memory
NOTE: The show licenses command output in this procedure shows the basic
licenses installed on a Network Security appliance. The output is similar for CM
appliances.
Viewing License Notifications Using the
Web UI
Functionality associated with a license stops when a license expires. For example, when
the FIREEYE_APPLIANCE license expires, the appliance will block access to all pages
except the CMS License Settings page, and CLI commands (except those that install
102
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing License Notifications Using the Web UI
licenses) are disabled or their execution fails. For example, the report generate
command will not create a report.
To prevent a gap in functionality, the CMS License Settings page displays notifications
about expired license and licenses that will expire within 30 days. For example:
NOTE: See Automatic License Updates on page 95 for information about enabling
the appliance to automatically download licenses from the DTI network when it is
time to renew them.
© 2022 FireEye Security Holdings US LLC
103
Central Management System Administration Guide
104
CHAPTER 7: License Keys
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About the DTI Network
CHAPTER 8: The DTI Network
This section covers the following information:
l
About the DTI Network below
l
About DTI Network Communication on page 108
l
About Support and Content License Sharing Combinations on page 109
l
Changing the Active Setting for a DTI Service on page 109
l
Using an HTTP Proxy for DTI Service Requests on page 116
l
Understanding the DTI Cache on page 117
l
Validating DTI Access on page 129
l
Configuring DTI Credentials on page 132
l
Automatic Validation of Security Content on page 133
l
Sharing Appliance Telemetry and Statistics on page 135
About the DTI Network
The Trellix Dynamic Threat Intelligence (DTI) network (cloud) provides subscriber
platforms with the latest intelligence on advanced cyber attacks and malware callback
destinations. This enables Trellix products to proactively recognize new threats and block
attacks. The DTI cloud is also used to enable automatic software updates. Finally, a
connection to the DTI cloud is required to use the license update feature.
Threat Intelligence
The Trellix DTI cloud interconnects Trellix platforms deployed within customer networks,
technology partner networks, and service provider networks around the world. The Trellix
DTI cloud serves as a global distribution hub to efficiently share automatically generated
threat intelligence such as new malware profiles, vulnerability exploits, and obfuscation
tactics, as well as new threat findings from the Trellix APT Discovery Center and verified
third-party security feeds. By leveraging the Trellix DTI cloud, the Trellix Threat Prevention
© 2022 FireEye Security Holdings US LLC
105
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Platform is more efficient at detecting unknown zero-day, highly targeted attacks used in
cybercrime, cyber espionage, and cyber reconnaissance as well as known malware.
NOTE: A subscription to the Trellix DTI cloud service is required before you
can use the features described in this section.
When the DTI cloud receives threat intelligence from customers and partners from around
the world, this information is analyzed and distributed to all customers with a DTI cloud
subscription. The information includes:
l
New malware profiles
l
Vulnerability exploits
l
Obfuscation tactics
l
New threat findings from the Trellix Labs and verified third-party security feeds
Each customer controls what information is shared with and received from the DTI cloud.
Automatic License Updates
The license update feature enables appliances to automatically download the appropriate
licenses from the DTI cloud and install them. This feature provides the following benefits:
106
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
About the DTI Network
Minimal initial configuration—The license update feature is enabled with the
configuration jump-start wizard during the initial configuration. This means the
feature can be fully functional after the jump-start wizard is completed.
Simplified license management—There is never a need to contact Trellix for license
keys when new features are added or when licenses are renewed, because new
licenses are automatically downloaded and installed.
Scalability—Organizations, such as those with a large number of appliances, can
benefit from having all of them being updated automatically, instead of entering
license keys manually on each appliance, one at a time.
For more information on automatic license activation, see Automatic License Updates on
page 95.
System Health Monitoring and Software Updates
When connected to the DTI cloud, the CM appliance regularly provides system and
diagnostic information to the DTI cloud. This information is then analyzed to ensure that
the appliance is operating as expected.
The system and diagnostics checks include the following:
l
System Image Version
l
Guest Image Profiles
l
System Processes
l
Hardware State
l
Network State
If problems are found, the customer is alerted. If a new system image or guest image profile
is available, administrators can choose to download it and then update the appliance.
NOTE: No customer-specific proprietary information is included this system and
diagnostic information exchange.
© 2022 FireEye Security Holdings US LLC
107
Central Management System Administration Guide
CHAPTER 8: The DTI Network
About DTI Network Communication
To communicate with the DTI network, the CM appliance needs the following information:
l
DTI server address
l
DTI network username
l
DTI network user password
This information is pre-configured on new physical appliances and on virtual appliances.
For older appliances, the information was supplied in the box containing your appliance
or otherwise provided by Trellix. Communication with the DTI network is enabled during
the initial appliance configuration if default values are accepted, as described in Initial
Configuration Overview on page 78.
The appliance sends requests to the DTI network for the services shown in the following
table.
108
DTI Service
Description
Download
source
The source for software updates (system images, guest images, and security
content).
Upload
destination
The destination for appliance telemetry and statistics (anonymized data).
MIL
The destination for Malware Intelligence Lab (MIL) malware detection and
callback intelligence.
FAUDE
The destination for Advanced URL Detection Engine (FAUDE) malware
detection and callback intelligence.
AV-Suite
The destination to store verdicts for both malicious (blacklist) and
nonmalicious (whitelist) objects in the AV-Suite cloud-based detection
service.
Enrollment
The Central Management appliance that manages the MVX cluster to
which sensors and hybrid appliances send submissions for inspection and
analysis. This service is used by appliances that submit to or are part of an
MVX cluster.
Helix
The destination for health statistics from Helix-enabled appliances.
Virtual
The destination for virtual appliance services, such as license token
renewals and system entropy information. This service is used by virtual
appliances.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
About Support and Content License Sharing Combinations
About Support and Content License
Sharing Combinations
Trellix offers sharing options for your Support and Content Updates licenses. The following
table shows the content that is uploaded to the DTI cloud with each license sharing
combination.
The Support license sharing option determines whether telemetry and statistics are
uploaded. The Content Updates license sharing option determines whether security content
and AV-Suite and FAUDE requests are uploaded.
NOTE: For a description of the uploaded content types, see About DTI Network
Communication on the previous page. For a description of the licenses, see About
Trellix License Keys on page 91.
Support
License
Content License
Uploaded Content
Two-Way
Two-Way
Telemetry and statistics, security content, FAUDE and
AV-Suite requests
Two-Way
One-Way
Telemetry and statistics
Two-Way
One-Way with
Override
One-Way
One-Way
One-Way
One-Way with
Override
One-Way
Two-Way
Telemetry and statistics, FAUDE and AV-Suite
requests
Nothing is uploaded.
FAUDE and AV-Suite requests
Telemetry and statistics, security content, FAUDE and
AV-Suite requests
Changing the Active Setting for a DTI
Service
Appliances send requests for DTI services to the following servers:
l
Dynamic Threat Intelligence (DTI)—The Trellix DTI server. The DTI server
addresses follow:
© 2022 FireEye Security Holdings US LLC
109
Central Management System Administration Guide
l
l
l
CHAPTER 8: The DTI Network
l
staticcloud.fireeye.com (Download source and virtual service)
l
up-staticcloud.fireeye.com (Upload destination)
l
mil-staticcloud.fireeye.com (MIL service)
l
unity.fireeye.com (FAUDE and AV-Suite services)
l
Helix full URL (Helix service)
Content Delivery Network (CDN)—A content delivery network server. The server
address is cloud.fireeye.com or download.fireeye.com.
The Central Management appliance (CMS)—Available only to managed appliances.
The address is the Central Management address.
A custom DTI server, if configured—A custom DTI server used only for managed
appliances in a Network Address Translation (NAT) deployment in which the
appliance uses the non-default dual-port address type to communicate with the
Central Management appliance, and an accessible address needs to be configured
for the Central Management appliance. The address is the accessible Central
Management address. For details, see the System Administration Guide or
Administration Guide for the managed appliance.
Each appliance has an active setting and available options for each DTI service. By default,
CMS is the active setting for all DTI services on managed appliances. This is the default
global setting, which means all appliances that are managed by the Central Management
appliance use this setting. You can change the global setting on the Central Management
appliance, and you can override the global setting for individual managed appliances.
You can also change the active download source setting for standalone appliances and the
Central Management appliance.
Reasons for changing the active setting for a DTI service include:
l
l
l
l
110
More effective detection and remediation. Trellix recommends a direct connection
to unity.fireeye.com to prevent FAUDE and AV-Suite service timeouts and
errors.
Faster download speed. A CDN server is typically geographically closer to
standalone appliances than the Trellix DTI server. The DTI or CDN server could be
closer to managed appliances than the Central Management appliance.
Decentralization —You can limit the amount of traffic passing through the Central
Management appliance when requests for one or more DTI services go directly to
the DTI network.
Security. Your security policies could require you to download the software updates
directly from the Trellix DTI server.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Changing the Active Setting for a DTI Service
HTTP proxy. You can use an HTTP proxy as an intermediary between an appliance
and the DTI network. In this scenario, managed appliances using the single-port
address type must use DTI. Managed appliances using the dual-port address type
can use either CMS or DTI. For details, see Using an HTTP Proxy for DTI Service
Requests on page 116.
Network address translation. When the Central Management appliance is behind a
NAT gateway, an accessible IP address that the managed appliances can reach
could need to be configured as a custom DTI source. For details, see the System
Administration Guide or Administration Guide for the managed appliance.
Prerequisites
l
Admin access.
l
Appliances are in "online" mode and connected to the DTI network.
Changing the Active Source for a Standalone Appliance
Using the Web UI
Use the DTI Network Settings page to change the active DTI source setting for a
standalone appliance.
To change the active source setting:
1. Click the Settings tab.
2. Click DTI Network in the sidebar.
3. In the Content Source list, select the DTI source the appliance will use for software
updates.
4. Click Apply Settings.
© 2022 FireEye Security Holdings US LLC
111
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Changing the Active Source for a Managed Appliance
Using the Web UI
Use the DTI Network Settings page to change the active DTI source setting on a managed
appliance.
To change the active source setting:
1. Select Settings > DTI Network.
2. Clear the Obtain Settings from CM checkbox, if it is selected.
3. In the Content Source list, select the new DTI source.
4. Click Apply Settings.
Changing the Active Source for a Central Management
Appliance Using the Web UI
Use the DTI Network Settings page to change the active DTI source setting for a Central
Management appliance.
112
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Changing the Active Setting for a DTI Service
To change the active source setting:
1. Select Settings > CM Settings.
2. Click DTI Network in the sidebar.
3. In the Source list in the CM Local DTI Settings section, select the DTI the Central
Management appliance will use for software updates.
4. Click Save Local DTI Settings.
Changing the Active Source for a Central Management
Appliance Using the CLI
Use the commands in this section to change the active DTI source for a Central
Management appliance.
To change the active source setting:
1. Log into the standalone appliance.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. View the current active and available DTI sources:
hostname (config) # show fenet dti configuration
4. Change the active download source:
hostname (config) # fenet dti source default {CDN | DTI}
5. Verify your change:
hostname (config) # show fenet dti configuration
6. Save your change:
hostname (config) # write memory
Example
In this example, the active download source on a Central Management appliance is
changed from DTI to CDN.
hostname (config) # show fenet dti configuration
DTI CLIENT CONFIGURATIONS:
ACTIVE SETTINGS:
Mode
Download source
...
:
:
online
DTI (DTIUser@staticcloud.fireeye.com)
AVAILABLE OPTIONS:
--------------------------------------------------------------
© 2022 FireEye Security Holdings US LLC
113
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Download
User
Address
-------------------------------------------------------------CDN
DTIUser
cloud.fireeye.com
DTI
DTIUser
staticcloud.fireeye.com
...
-------------------------------------------------------------hostname (config) # fenet dti source default CDN
hostname (config) # show fenet dti configuration
DTI CLIENT CONFIGURATIONS:
ACTIVE SETTINGS:
Mode
Download source
...
:
:
online
CDN (DTIUser@cloud.fireeye.com)
Changing the Global Active Source for Managed
Appliances Using the Web UI
Use the DTI Network Settings page to change the DTI source from which the appliances
managed by a Central Management appliance download software updates.
To change the global source setting:
1. Select Settings > CM Settings.
2. Click DTI Network in the sidebar.
3. In the Source list in the Appliance DTI Settings section, select the DTI source from
which managed appliances download software updates.
4. Click Save Appliance DTI Settings.
Changing Global Active DTI Settings for Managed
Appliances Using the CLI
Use the commands in this section to change global active DTI settings for the appliances
that are managed by a Central Management appliance.
114
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Changing the Active Setting for a DTI Service
To change global active DTI settings:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the current active and available DTI sources.
hostname (config) # show fenet dti configuration
3. To change the active global source setting:
a. Specify the active setting:
hostname (config) # fenet dti source managed {DTI | CDN | CMS}
b. Apply the setting to all managed appliances:
hostname (config) # fenet dti source managed-sync
4. To change the active global upload destination setting:
a. Specify the active setting:
hostname (config) # fenet dti upload destination managed
{DTI | CMS}
b. Apply the setting to all managed appliances:
hostname (config) # fenet dti upload destination managed-sync
5. To change the active global setting for the mil, faude, avsuite, helix, or
virtual service:
a. Specify the active setting:
hostname (config) # fenet dti <service> service managed
{DTI | CMS}
b. Apply the setting to all managed appliances:
hostname (config) # fenet dti <service> service managed-sync
6. Verify your changes:
hostname (config) # show fenet dti configuration
7. Save your changes:
hostname (config) # write memory
Examples
In this example, the active setting for the download source is changed to DTI for the
appliances that are managed by this Central Management appliance.
hostname (config) # show fenet dti configuration
DTI CLIENT CONFIGURATIONS:
ACTIVE SETTINGS:
Mode
:
Download source
:
Upload destination :
...
© 2022 FireEye Security Holdings US LLC
online
CDN (DTIUser@cloud.fireeye.com)
DTI (DTIUser@up-staticcloud.fireeye.com)
115
Central Management System Administration Guide
CHAPTER 8: The DTI Network
ACTIVE SETTINGS FOR MANAGED APPLIANCES:
Download source
: CMS
Upload destination : CMS
...
AVAILABLE OPTIONS:
-------------------------------------------------------------Download
User
Address
-------------------------------------------------------------CDN
DTIUser
cloud.fireeye.com
CMS
DTIUser
10.2.3.4
DTI
DTIUser
staticcloud.fireeye.com
-------------------------------------------------------------...
hostname (config) # fenet dti source managed DTI
hostname (config) # fenet dti source managed-sync
hostname (config) # show fenet dti configuration
DTI CLIENT CONFIGURATIONS:
ACTIVE SETTINGS:
Mode
:
Download source
:
Upload destination :
...
online
CDN (DTIUser@cloud.fireeye.com)
DTI (DTIUser@up-staticcloud.fireeye.com)
ACTIVE SETTINGS FOR MANAGED APPLIANCES:
Download source
: DTI
Upload destination : CMS
...
Using an HTTP Proxy for DTI Service
Requests
An HTTP proxy server can act as an intermediary between an appliance and the
DTI network. The following table describes the default behavior, and the behavior after an
HTTP proxy is configured on the appliance and enabled for DTI service requests.
Appliance
Standalone
Appliance
116
Default
Behavior
The appliance
connects
directly to the
DTI network.
HTTP Proxy Behavior
The appliance connects to the DTI network through the
HTTP proxy.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Appliance
Understanding the DTI Cache
Default
Behavior
HTTP Proxy Behavior
Central
The Central
Management Management
Appliance
appliance
connects
directly to the
DTI network.
The Central Management appliance connects to the DTI
network through the HTTP proxy.
Managed
Appliance
Single-port communication with the Central
Management appliance (the default, in which both
management and DTI network traffic use SSH port
22)—The appliance connects to the DTI network
through the HTTP proxy.
The appliance
communicates
with the
DTI network
through the
Central
Management
appliance.
Dual-port communication with the Central Management
appliance (in which management traffic uses SSH port
22 and DTI network traffic uses HTTP port 443)—The
appliance either connects directly to the DTI network
through the HTTP proxy, or through the managing
Central Management appliance to the HTTP proxy.
IMPORTANT: If an HTTP proxy server is configured and enabled on a managed
appliance that uses single-port communication with the Central Management
appliance, the managed appliance will automatically fail over to the proxy server
for all DTI services if the Central Management appliance becomes unavailable.
For information about configuring an HTTP proxy server on the Central Management
appliance, see Configuring HTTP Proxy Server Settings on page 186. For information about
configuring managed appliances to use an HTTP proxy server for DTI services, see the
System Administration Guide or Administration Guide for the managed appliance.
Understanding the DTI Cache
When the Central Management appliance is the default DTI source for managed
appliances, it downloads software updates from the DTI network on behalf of the
appliances. The software updates are temporarily stored in a DTI cache on the Central
Management appliance.
When the Central Management appliance receives an update request from a managed
appliance or makes an update request on behalf of the appliance, the Central Management
appliance first determines whether the requested software is already in the cache and
whether it is the latest version. If the requested software is not in the cache, or if the
© 2022 FireEye Security Holdings US LLC
117
Central Management System Administration Guide
CHAPTER 8: The DTI Network
software is out-of-date, the Central Management appliance downloads the latest software
from the DTI network. After the software is in the cache, it is available to update the
appliances, as described in Updating Managed Appliances on page 495.
You can explicitly download system images and guest images from the DTI network and
store them in the cache, even if no appliance requested it. This saves bandwidth and
shortens the maintenance window for appliance updates. It also allows you to be more
flexible about scheduling appliance updates, because the software is already downloaded
and ready to push to the appliances. This can be especially useful for guest images, which
can take hours to download. For details, see Downloading Software Updates to the DTI
Cache on the facing page.
To save space on the hard disk, the Central Management appliance continuously removes
out-of-date security content, and removes out-of-date system images and guest images as
they are replaced. You can also manually remove security content, guest images, and
system images from the cache.
The Central Management appliance provides the following information about the cache
contents.
l
Size. The size of the guest image, system image, or security content, in bytes.
l
Type. The type of content:
l
SysImage—Appliance system image.
l
GI—Guest image.
l
l
l
l
l
GI-Delta—A file containing the changes between a particular version of the
guest images and the latest version.
GI-Metadata—A list of the names and versions of the guest images that are
available for the managed appliances.
SC-Full—Security content (stored for three hours).
SC-Delta—A file containing the changes between a particular version of the
security content and the latest version. Security content is updated every hour
(by default), and stale files are automatically removed from the cache.
State. Fresh or Stale. If a system image or guest image has been in the cache longer
than 90 days, or if security content has been in the cache longer than three hours for
SC-Full or one hour for SC-Delta, it is marked stale. Otherwise, it is marked fresh.
NOTE: If a system image or guest image is the latest available version, but is
older than 90 days, it is still marked stale.
l
118
File. The name of the system image, guest image, delta, metadata, or security content
file. For example, image-emps_7.7.0.img, win7-sp1.15.0826.img, sc-stable_
114.150.img.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
l
Understanding the DTI Cache
Last Modification Time. The date and time the file finished downloading from the
DTI network to the cache.
Max-Age. The amount of time the content is in the cache before it is marked stale.
System images and guest images become stale after 7776000 seconds (90 days).
Security content becomes stale after 10800 seconds (3 hours).
Etag. An internal identifier.
Active Download ID. An internal identifier that is displayed when you view the
status of the download.
For details about viewing the cache contents, removing software from the cache and other
cache management tasks, see Viewing the Cache Configuration on page 126.
NOTE: This information pertains to a Central Management appliance running in
online mode, in which the cache is always running. The cache is disabled on a
Central Management appliance running in offline mode. For information about how
the Central Management appliance handles software updates for managed
appliances when it is in offline mode, see the DTI Offline Portal User's Guide.
NOTE: The cache is disabled for cloud Central Management models CM 2500V and
CM 4500V. Appliances managed by these models download software updates
directly from the DTI network.
Downloading Software Updates to the DTI Cache
The following sections describe how to download software updates to the DTI cache in
advance, before an appliance requests them.
l
Downloading System Images to the DTI Cache Using the CLI on the next page
l
Downloading Guest Images to the DTI Cache Using the CLI on page 122
Cached guest images that were downloaded on behalf of a particular appliance type can
potentially be used for other appliances. Consider the following examples.
l
l
l
A Central Management administrator initiates a download of guest images for a
managed Network Security 7.9.0 appliance. The latest guest images in the
DTI network are version 3.
The system checks which guest images version is installed on the Network Security
appliance, and determines it is version 2.
The DTI network has a delta file containing the changes between guest images
version 2 and 3, so only the delta file is downloaded to the Central Management
cache.
© 2022 FireEye Security Holdings US LLC
119
Central Management System Administration Guide
l
l
CHAPTER 8: The DTI Network
A managed Email Security — Server Edition appliance (EX-01) running release 7.8.0
requests a guest images update. Guest images version 2 is installed on the Email
Security — Server Edition appliance, so the delta file in the cache can be used to
update the appliance. Nothing needs to be downloaded from the DTI network in
this case.
A managed Email Security — Server Edition appliance (EX-02) running release 7.7.0
requests a guest images update. Guest images version 1 is installed on the
appliance. The delta file in the cache does not contain the differences between
version 1 and 2 of the guest images, so a full update is needed. The complete guest
images version 3 is not in the cache, so the Central Management appliance must
download it from the DTI network before it can update the EX-02 appliance.
NOTE: You cannot manually download security content to the DTI cache. Security
content is updated frequently, so there is no benefit to downloading it before a
maintenance window. The newest security content is automatically downloaded to
the cache when the new security content is released.
NOTE: You can schedule the DTI cache storage operations using the job
CLI commands. For details, see the CLI Command Reference.
Prerequisites
l
l
l
l
Operator or Admin access
The type of appliance for which you will download content is connected to the
Central Management appliance.
Minimum appliance release for downloading system images: Network Security
7.5.0, Email Security — Server Edition 7.6.0, Malware Analysis 7.7.0, File Protect
7.7.0, and Endpoint Security 3.0.0.
Minimum appliance release for downloading guest images: Network Security 7.7.0
Downloading System Images to the DTI Cache Using the CLI
Use the commands in this section to download system images from the DTI network and
store them in the cache on the Central Management appliance. You can download the
latest system image for all managed appliances or for a specific type of managed
appliance. You can also download a specific version of a system image.
NOTE: You can perform only one download operation at a time.
120
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Understanding the DTI Cache
To download the latest system image for all appliances:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the system image:
hostname (config) # fenet dti cache populate image product all
3. Confirm that the operation succeeded:
hostname (config) # show fenet dti cache populate images status
To download the latest system image for a specific appliance type:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the system image:
hostname (config) # fenet dti cache populate image product <product>
where <product> is the product identifier, such as wMPS. Use the fenet dti
cache populate image product ? command to see a list of the product identifiers.
3. Confirm that the operation succeeded:
hostname (config) # show fenet dti cache populate images status
To download a specific version of a system image:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the system image:
hostname (config) # fenet dti cache populate image product <product>
version <version>
where :
l
<product> is the product identifier, such as wMPS. Use the fenet dti
cache populate image product ? command to see a list of the product
identifiers.
l
<version> is the product version. Use the fenet dti cache populate
image product <product> version ? command to see a list of the
available versions.
3. Confirm that the operation succeeded:
hostname (config) # show fenet dti cache populate images status
© 2022 FireEye Security Holdings US LLC
121
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Examples
The following example downloads the latest system image for the Network Security
appliance.
hostname (config) # fenet dti cache populate image product wMPS
Operation started in the background.
Run 'show fenet dti cache populate images status' to check on status.
hostname (config) # show fenet dti cache populate images status
Active Download ID: v54n
Start Time:
Elapsed Time:
2015/10/08 00:57:36.139
12 sec
==============================================================
Download Tasks
==============================================================
Downloading the 7.7.0 image for wMPS
Progress: 59.00 %
Status:
running
hostname (config) # show fenet dti cache populate images status
Active Download ID: v54n
Start Time:
Elapsed Time:
2015/10/08 00:57:36:139
20 sec
==============================================================
Download Tasks
==============================================================
Downloading the 7.7.0 image for wMPS
Progress: 100 %
Status:
success
The following example downloads the Email Security — Server Edition 7.6.1 system image.
hostname (config) # fenet dti cache populate image product eMPS 7.6.1
Operation started in the background.
Run 'show fenet dti cache populate images status' to check on status.
hostname (config) # show fenet dti cache populate images status
Active Download ID: pzz2
Start Time:
End Time:
Elapsed Time:
2015/10/07 14:37:51.220
2015/10/07 14:38:02.520
11 sec
==============================================================
Download Tasks
==============================================================
Downloading the 7.6.1 image for eMPS
Progress: 100.00 %
Status:
success
Downloading Guest Images to the DTI Cache Using the CLI
Use the commands in this section to download guest images from the DTI network and
store them in the cache on the Central Management appliance. You can download guest
images for all managed appliances, or guest images for a specific appliance.
122
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Understanding the DTI Cache
NOTE: You can perform only one guest images download operation at a time.
To download guest images for all managed appliances:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the guest images:
hostname (config) # fenet dti cache populate guest-images all
3. Confirm that the operation succeeded:
hostname (config) # show fenet dti cache populate guest-images status
To download guest images for a specific appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the guest images:
hostname (config) # fenet dti cache populate guest-images appliance
<applianceName>
where <applianceName> is the hostname of the appliance. Use the fenet dti
cache populate guest-images appliance ? command to list the hostnames.
3. Confirm that the operation succeeded:
hostname (config) # show fenet dti cache populate guest-images status
Examples
The following example downloads guest images for the NX-01 appliance and shows the
download progress.
hostname (config) # fenet dti cache populate guest-images appliance NX-01
Operation started in the background.
Run 'show fenet dti cache populate guest-images status' to check on status.
hostname (config) # show fenet dti cache populate guest-images status
Active Download ID: grgf
Start Time:
Elapsed Time:
2015/10/07 20:24:17.701
13 sec
============================================================================
Download Tasks
============================================================================
Downloading Guest-Image Profile (Full-Image) winxp-sp3 for NX-01
Progress: 4.97%
Status:
running
Downloading Guest Image-Profile (Full-Image) win7-sp1 for NX-01
Progress: -
© 2022 FireEye Security Holdings US LLC
123
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Status: not started
Downloading Guest-Image Profile (Full-Image) win7x64-sp1 for NX-01
Progress: Status: not started
hostname (config) # show fenet dti cache populate guest-images status
Active Download ID: grgf
Start Time:
Elapsed Time:
2015/10/07 20:24:17:701
218 sec
===========================================================================
Download Tasks
===========================================================================
Downloading Guest-Image Profile (Full-Image) winxp-sp3 for NX-01
Progress: 100.00%
Status:
success
Downloading Guest-Image Profile (Full-Image) win7-sp1 for NX-01
Progress: 14.62%
Status:
running
Downloading Guest-Image Profile (Full-Image) win7x64-sp1 for NX-01
Progress: Status: not started
Managing the DTI Cache
DTI cache management tasks include:
l
l
l
l
Viewing detailed information about the contents of the cache. For details, see
Viewing the DTI Cache Using the CLI below.
Viewing the cache configuration. For details, see Viewing the Cache Configuration
on page 126.
Manually removing images, if needed. For details, see Removing Images from the
Cache on page 127.
Disabling the automatic removal of stale security content. For details, see Disabling
Automatic Removal of Stale Security Content on page 128.
Prerequisites
l
Operator or Admin access
Viewing the DTI Cache Using the CLI
Use the commands in this section to view the contents of the DTI cache. You can view a
basic list of the files in the cache, or include details such as the state, age, and version of
the files.
124
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Understanding the DTI Cache
To list the cache contents:
1. Go to CLI enable mode:
hostname > enable
2. View the cache contents:
hostname # show fenet dti proxy cached-content
To view the state of each file in the cache:
1. Go to CLI enable mode:
hostname > enable
2. View the cache contents and state information:
hostname # show fenet dti proxy cached-content show-stale
To view age details for each file in the cache:
1. Go to CLI enable mode:
hostname > enable
2. View the cache contents and age details:
hostname # show fenet dti proxy cached-content freshness-info
To view the version of each file in the cache:
1. Go to CLI enable mode:
hostname > enable
2. View the cache contents and file versions:
hostname # show fenet dti proxy cached-content version
Examples
The following example shows the cache contents.
hostname # show fenet dti proxy cached-content
Size Type
File
=================================================
931798 SC-Full
sc-stable_114.150.img
294514420 SC-Full
sc-stable_409.198.img
12357897831 GI
win7-sp1.15.0826.img
931626 SC-Full
sc-stable_114.149.img
6314243531 GI
winxp-sp3.15.0826.img
586688050 SysImage
image-hx_3.0.0.img
294476781 SC-Full
sc-stable_409.194.img
602473341 SysImage
image-fmps_7.7.0.img
12783320704 GI
win7x64-sp1.15.0826.img
627703972 SysImage
image-emps_7.7.0.img
The following example includes state information.
hostname # show fenet dti proxy cached-content show-stale
Size
Type
State
© 2022 FireEye Security Holdings US LLC
File
125
Central Management System Administration Guide
CHAPTER 8: The DTI Network
==========================================================
931798 SC-Full
Fresh
sc-stable_114.150.img
294514420 SC-Full
Fresh
sc-stable_409.198.img
12357897831 GI
Fresh
win7-sp1.15.0826.img
931626 SC-Full
Fresh
sc-stable_114.149.img
294156637 SC-Full
Stale
sc-stable_409.186.img
6314243531 GI
Fresh
winxp-sp3.15.0826.img
586688050 SysImage
Fresh
image-hx_3.0.0.img
294415556 SC-Full
Stale
sc-stable_409.190.img
294476781 SC-Full
Fresh
sc-stable_409.194.img
602473341 SysImage
Fresh
image-fmps_7.7.0.img
12783320704 GI
Fresh
win7x64-sp1.15.0826.img
627703972 SysImage
Fresh
image-emps_7.7.0.img
The following example includes age information. (The values in the Etag and File
columns shown in this example have been shortened.)
hostname # show fenet dti proxy cached-content freshness-info
Size Type
Etag
Last Modification Time Max-Age State File
=============================================================================
93179 SC-Full "6xxx" Wed Oct 7 21:53:15 2015 10800
Fresh sc-xxx.img
29451442 SC-Full "6xxx" Wed Oct 7 22:22:28 2015 10800
Fresh sc-xxx.img
12357897831 GI
"4xxx" Wed Oct 7 20:31:20 2015 7776000 Fresh win7xx.img
931626 SC-Full "6xxx" Wed Oct 7 20:57:15 2015 10800
Fresh sc-xxx.img
6314243531 GI
"4xxx" Wed Oct 7 20:27:22 2015 7776000 Fresh winxp.img
586688050 SysImage "6xxx" Wed Oct 7 20:27:55 2015 7776000 Fresh image-n.img
294476781 SC-Full "6xxx" Wed Oct 7 20:22:20 2015 10800
Fresh sc-xxx.img
602473341 SysImage "6xxx" Wed Oct 7 20:24:25 2015 7760000 Fresh image-n.img
12783320704 GI
"4xxx" Wed Oct 7 20:34:52 2015 7776000 Fresh win7xx.img
627703972 SysImage "6xxx" Wed Oct 7 20:21:02 2015 7776000 Fresh image-n.img
The following example includes version information.
hostname # show fenet dti proxy cached-content version
Size Type
File Details
=============================================
931798 SC-Full
stable: 114.150
294514420 SC-Full
stable: 409.198
12357897831 GI
win7-sp1: 15.0826
931626 SC-Full
stable: 114:149
6314243531 GI
winxp-sp3: 15.0826
586688050 SysImage
hx: 3.0.0
294476781 SC-Full
stable: 409.194
602473341 SysImage
fmps: 7.7.0
12783320704 GI
win7x64-sp1: 15.0826
627703972 SysImage
emps: 7.7.0
Viewing the Cache Configuration
IMPORTANT: Trellix recommends that you do not change the cache configuration
settings.
126
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Understanding the DTI Cache
To view the cache configuration:
1. Go to CLI enable mode:
hostname > enable
2. View the cache configuration:
hostname # show fenet dti proxy configuration
To view full cache configuration information:
1. Go to CLI enable mode:
hostname > enable
2. View the full cache configuration:
hostname # show fenet dti proxy configuration all
Example
The following example shows the full cache configuration:
hostname # show fenet dti proxy configuration all
Fenet Cache Proxy State:
running
Fenet Cache Proxy Configurations:
Listening Port:
8443
Cache Size:
130000 MB
Maximum Cache-able Object Size: 26843545600 bytes
Additional Configurations:
CDN Server:
download.fireeye.com
Auto-Purge Cached Security-Content Deltas: yes
Terminate Connection on SSL error:
yes
Debug Options:
ALL,1
URL Query String Logging:
no
Removing Images from the Cache
Use the commands in this section to remove images from the DTI cache.
To remove a single image:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the image:
hostname (config) # fenet dti proxy cache purge file <fileName>
where <fileName> is a value listed in the show fenet dti proxy cached-content
command output.
3. Verify your change:
hostname (config) # show fenet dti proxy cached-content
© 2022 FireEye Security Holdings US LLC
127
Central Management System Administration Guide
CHAPTER 8: The DTI Network
To remove all images of a specific type:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the images:
hostname (config) # fenet dti proxy cache purge file-type <fileType>
where <fileType> can be SysImage, GI, GI-Delta, GI-Metadata, SC-Full, or SCDelta. See Understanding the DTI Cache on page 117 for a description of the file
types.
3. Verify your change:
hostname (config) # show fenet dti proxy cached-content
To remove all images in the cache:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the images:
hostname (config) # fenet dti proxy cache purge
3. Verify your change:
hostname (config) # show fenet dti proxy cached-content
Examples
The following example removes all guest image delta files from the cache.
hostname (config) # fenet dti proxy cache purge file-type GI-Delta
The following example removes the File Protect 7.7.0 system image from the cache.
hostname (config) # fenet dti proxy cache purge file image-fmps_7.7.0.img
The following example removes all images from the cache, and then verifies the change.
hostname (config) # fenet dti proxy cache purge
Operation started in the background.
Run 'show fenet dti proxy cached-content' to check on progress.
hostname (config) # show fenet dti proxy cached-content
The cache is empty.
Disabling Automatic Removal of Stale Security Content
Security content is updated every hour, so stale files are automatically removed from the
cache by default. Use the commands in this section to stop stale files from being removed
automatically.
128
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Validating DTI Access
To disable the automatic removal of stale security content:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable the automatic removal feature:
hostname (config) # no fenet dti proxy cache purge auto enable
3. Verify your change:
hostname (config) # show fenet dti proxy configuration all
The value of the Auto-Purge Cached Security-Content Deltas line should be
no.
4. Save your change:
hostname (config) # write memory
NOTE: Use the fenet dti proxy cache purge auto enable command to reenable the feature.
Example
The following example disables automatic removal of stale security content delta files.
hostname (config) # no fenet dti proxy cache purge auto enable
hostname (config) # show fenet dti proxy configuration all
Fenet Cache Proxy State:
running
Fenet Cache Proxy Configurations:
Listening Port:
8443
Cache Size:
130000 MB
Maximum Cache-able Object Size: 26843545600 bytes
Additional Configurations:
CDN Server:
download.fireeye.com
Auto-Purge Cached Security-Content Deltas: no
Terminate Connection on SSL error:
yes
Debug Options:
ALL,1
URL Query String Logging:
no
Validating DTI Access
Before using the features associated with the DTI network, you must establish
communication between the appliance and the DTI network. Use the following procedures
to verify this communication.
© 2022 FireEye Security Holdings US LLC
129
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Prerequisites
l
Operator or Admin access
l
Access to the DTI network
Validating DTI Access Using the Web UI
Use the FireEye CMS System Information page to validate DTI cloud communication.
To validate DTI access:
1. Click the About tab.
2. Click Health Check on the upper left side.
3. Locate the DTI Cloud section.
4. Verify that the DTI Client field is Enabled.
Validating DTI Access Using the CLI
Use the commands in this topic to verify DTI communication.
To validate DTI access:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
130
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Validating DTI Access
2. Check the status of the DTI service. (This example is from a managed appliance.)
hostname (config) # show fenet status
Dynamic Threat Intelligence Service:
Update source
Enabled
Download
Upload
Mil
: <online>
: yes
: DTIUser@10.11.121.13 : singleport
: DTIUser@10.11.121.13 : singleport
: DTIUser@10.11.121.13 : singleport
HTTP Proxy:
Address
Username
User-agent
:
:
:
Request Session:
Timeout
Retries
Speed Time
Max Time
Rate Limit
: 30
: 0
: 60
: 14400
:
Speed Limit
: 1
Dynamic Threat Intelligence Lockdown:
Enabled
Locked
Lock After
: no
: no
: 5 failed attempts
UPDATES
Security contents:
05:43:00
Stats contents
:
18:55:00
Enabled
------yes
yes
Notify
-----no
Scheduled
-------------every
Last Updated At
--------------2016/07/20
none
2016/07/20
3. Confirm the following information:
l
Update source is online.
l
DTI service is enabled.
l
DTI service username is the name provided with DTI subscription license.
l
DTI service address is cloud.fireeye.com.
© 2022 FireEye Security Holdings US LLC
131
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Configuring DTI Credentials
Virtual appliances have appliance-specific DTI credentials that are generated from the
appliance's activation code and that cannot be changed. Physical appliances have factoryconfigured DTI credentials that should not be changed.
You should never change DTI credentials, except when you need to configure a custom
DTI source in a Network Address Translation (NAT) deployment in which both of the
following are true:
l
l
The Central Management appliance is behind a NAT gateway.
The managed appliance uses the non-default dual-port address type for
communication with the Central Management appliance.
Prerequisites
l
Admin access
Configuring DTI Credentials Using the CLI
Use the commands in this topic to configure DTI credentials (username and password).
To configure DTI credentials:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the user and password:
hostname (config) # fenet dti source type <name> username <user>
password <password>
The variables have the following values:
l
<name>—The name of the custom DTI source.
l
<user> and <password>—The new credentials.
3. Verify your changes:
hostname (config) # show fenet dti configuration
4. Save your changes.
hostname (config) # write memory
132
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Automatic Validation of Security Content
Automatic Validation of Security Content
To prevent the installation of incompatible security content, security content packages are
validated automatically when they are downloaded from the Trellix Dynamic Threat
Intelligence (DTI) cloud or from the Trellix DTI Offline Update Portal. This feature is
supported for the following appliances:
l
Central Management release 8.1.0 and later.
l
Network Security release 8.0.0 and later.
l
Email Security — Server Edition release 8.1.4 and later.
About Automatic Validation of Security Content
When a security content package is downloaded, the appliance queries the package to
obtain its attributes. Some of the attributes are compared to attributes of the installed
security content and to values configured on the target appliance. The criteria that
determine whether a downloaded package is compatible are listed in Conditions That
Indicate a Compatible Security Content Package below.
If the package passes all applicable compatibility checks, the new security content is
installed on the target appliance.
If the package fails a compatibility check, the appliance does the following:
l
Sends an error code in log messages.
l
Displays an error message at the CLI or the Web UI.
l
Performs no further checking on the downloaded package.
l
Discards the downloaded package without installing
l
Requires that the next security content update uses a full update package and not a
delta update package.
Conditions That Indicate a Compatible Security Content
Package
Downloaded security content packages are automatically evaluated against the following
conditions in the order listed:
1. If the appliance is connected to the Internet: Was the package downloaded from the
correct update channel of the DTI download server?
2. If the appliance is not connected to the Internet: Was the package downloaded from the
correct content channel of the DTI Offline Portal?
© 2022 FireEye Security Holdings US LLC
133
Central Management System Administration Guide
CHAPTER 8: The DTI Network
3. Is the package version number compatible with the target appliance release?
4. Does the package acceptance level match the level configured on the target
appliance?
5. If the downloaded package is a delta package: Is the version of the content delta package
compatible with the version of the security content installed on the target appliance?
6. Is the version of the downloaded package the same as or newer than the version of
the installed content?
Error Codes for Incompatible Security Content Packages
The appliance writes a log message when a downloaded security content package is
determined to be incompatible with the target appliance settings or the security content
installed on the appliance. The following paragraphs describe the error codes for these
events.
81 ― Incompatible DTI download server update channel
The package was built for an update channel other than stable (such as beta), but the
appliance is not configured to use the same update channel.
82 ― Incompatible DTI Offline Portal content channel
The package was built for and downloaded from a content channel other than the one
configured on the target appliance. Examples of DTI Offline Portal content channels are
SCNET-5.0, SCNET-4.0, SCNET-3.0, SCNET-2.0, and SCEP-1.0.
83 ― Package version is incompatible with the appliance release
The package acceptance level configured on the appliance must be compatible with the
appliance software release. By default, the package acceptance level configured on the
appliance is stable. Other package acceptance levels are beta and long_beta.
134
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Sharing Appliance Telemetry and Statistics
84 ― Package acceptance level does not match the target
appliance configuration
The package acceptance level (such as beta or long_beta) does not match the acceptance
level configured on the appliance.
85 ― Delta content package version is incompatible with the
installed security content
The package is a delta (incremental) content package, and its version number is
incompatible with the security content version installed on the target appliance.
86 ― Package version is newer than the installed security
content version
The package version is newer than the installed security content version, and this is not a
content rollback operation.
Sharing Appliance Telemetry and
Statistics
The CM appliance can share anonymous data with the DTI cloud. No customer-specific
proprietary information is exchanged.
This section covers the following information:
l
l
l
About Sharing Appliance Telemetry and Statistics With the DTI Cloud on the next
page
Uploading Appliance Telemetry and Statistics Automatically Using the CLI on
page 137
Uploading Appliance Telemetry and Statistics Manually Using the CLI on page 138
Prerequisites
l
Admin access
© 2022 FireEye Security Holdings US LLC
135
Central Management System Administration Guide
CHAPTER 8: The DTI Network
About Sharing Appliance Telemetry and Statistics With
the DTI Cloud
Trellix appliances automatically push anonymous data to and pull security information
from the Dynamic Threat Intelligence (DTI) cloud.
NOTE: All Trellix devices upload information using a secure (HTTPS) connection to
cloud.fireeye.com. By default, managed appliances communicate with the DTI
cloud through the managing Central Management appliance.
No customer-specific or proprietary information is exchanged. Two types of data are
shared: real-time system statistics and threat intelligence information.
For information about the licenses required to share this data, see About Support and
Content License Sharing Combinations on page 109.
Real-Time Statistics
The following real-time statistics are anonymized and uploaded to the DTI cloud:
l
l
l
l
License information―Status of the FireEye licenses on the device.
Appliance health―Environmental information relating to all components such as
fans and hard disk drive with System Activity Report data.
Traffic Measurements―Traffic throughput statistics and capacity monitoring.
Statistics of critical sub-systems capacity―Interface status, packet counts, number of
flows, broken or asymmetric flows, binaries, packet loss, protocol-based stats,
memory usage, and Kernel-level information.
Threat Intelligence Information
The following threat intelligence information is shared with the DTI cloud:
l
l
l
l
136
Timestamp―The timestamp can be used as a reference for other events and can
provide additional information about the attack and the methods used.
URL―List of malicious URLs contacted during traffic analysis in the Virtual
execution (VX) engine.
MD5―An MD5 hash is generated for information such as IP addresses or MAC
addresses. The MD5 hash enables Trellix to maintain the data for analysis without
the data being traceable or recognizable in its original form. The information is
important for correlation of multiple threats on a common host.
File types―File types used in the course of an attack. Trellix determines the entry
point, the payload, and the methods used.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Sharing Appliance Telemetry and Statistics
Information That Is Not Uploaded to the DTI Cloud
The following information is NOT uploaded to the DTI cloud:
l
No customer-specific information
l
No proprietary information
l
No packet captures
Benefits of Sharing Data With the DTI Cloud
Uploading data to the DTI cloud provides the following benefits:
l
l
l
l
Participating Trellix appliances share malware intelligence in real time.
The Trellix Customer Support team can provide you with proactive operational
monitoring and support. This monitoring and support includes the identification of
targeted attacks.
The Trellix Research Labs team processes the collection of shared data to extract the malicious
content. Updated security content, some of which is developed using anonymous
customer data, is included in the security content delivered to the DTI cloud for
distribution to licensed Trellix appliances and compute nodes.
The Trellix DTI cloud itself employs technology to detect zero-day callbacks.
NOTE: You are not required to upload data in order to receive any benefits of the
DTI cloud. A managed appliance can download and install updated security
content, even if it does not upload data.
Uploading Appliance Telemetry and Statistics
Automatically Using the CLI
Use the CLI commands in this topic to upload CM appliance telemetry and statistics to the
DTI cloud automatically every three hours. No customer-specific or proprietary information
is exchanged.
To configure automatic system information updates:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Set the schedule to upload aggregation information to the DTI cloud automatically
every three hours:
fenet stats-content upload auto default
© 2022 FireEye Security Holdings US LLC
137
Central Management System Administration Guide
CHAPTER 8: The DTI Network
Uploading Appliance Telemetry and Statistics Manually
Using the CLI
Use the CLI commands in this topic to push aggregated system statistics from the CM
appliance to the DTI cloud.
To manually push statistics to the DTI cloud:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Upload the statistics:
hostname (config) # fenet stats-content upload now
138
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
AAA
CHAPTER 9: System Security
This section lists methods you can use to secure your Trellix appliances. For detailed
information about implementing the methods, see the Trellix System Security Guide.
AAA
Authentication, authorization and accounting (AAA) methods control users' access to
network resources, and monitor users' activities.
AAA information in the System Security Guide includes:
l
Authentication—Configuring authentication methods and order, local
authentication (user accounts, password complexity, and password policies), remote
authentication, Common Access Card (CAC) authentication, Secure Shell
(SSH) authentication, and Single Sign-On (SSO) authentication.
l
Authorization—Defining roles for local user accounts.
l
Accounting—Managing audit logs.
l
FireEye Cloud IAM—Using Identity Access Management (IAM), a Web service that
provides user authentication and authorization.
The guide also provides reference information about Trellix appliance roles and
capabilities and Trellix Cloud IAM entitlements.
Certificates
Trellix appliances use X.509 (TLS/SSL) certificates to allow secure connections between the
appliance and the Web browser running the Web UI, and to verify remote servers for
various client applications. They also use the certificates to encrypt the emails they forward
to a downstream MTA on the Email Security — Server Edition appliance, and secure the
connection to a WebDAV server on the File Protect appliance.
Certificate information in the System Security Guide includes:
© 2022 FireEye Security Holdings US LLC
139
Central Management System Administration Guide
140
CHAPTER 9: System Security
l
Regenerating the system self-signed server certificate
l
Managing HTTPS and MTA server certificates
l
Configuring Web server and SharePoint CA certificate chains
l
Adding supplemental CA client certificates
l
Importing and downloading public and private keys, and exporting public keys
l
Defining common attributes of X.509 certificates
l
Obtaining a CA certificate from a trusted public Certificate Authority (CA)
l
Specifying the minimum version requirement for Transport Layer Security (TLS)
l
Improving certificate security
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 10: System Email
Settings
The appliance can send email notifications about system health events, such as low disk
space or a power supply failure, or a split brain condition in a High Availability (HA)
deployment. It can also send scheduled reports containing malware analysis data, and
email notifications triggered by malware alerts.
Health Check Notifications
The system email server can send notifications about system events and Central
Management HA events to configured recipients. You configure the email server and
recipients for these events on the Email Settings page of the Web UI or by using the email
notify CLI commands. You can also:
l
l
l
Specify whether each recipient should receive notifications for "fail" events,
"info" events, or both "fail" and "info" events.
Specify whether each recipient should receive detailed or summarized notifications.
Enable or disable specific events from triggering notifications (except for Central
Management HA events).
For details, see:
l
Configuring the Mail Server on the next page
l
Configuring Email Recipients on page 147
l
Configuring System Events on page 151
Scheduled Reports
Scheduled reports use the same email server and recipient list as the system events. If you
use the CLI, you configure them using the report email commands instead of the email
notify commands, as described in Configuring the Mail Server for Scheduled Reports
Using the CLI on page 146. You configure the report data and schedule on the Reports >
© 2022 FireEye Security Holdings US LLC
141
Central Management System Administration Guide
CHAPTER 10: System Email Settings
Schedule page of the Web UI or by using the report schedule CLI commands. See
Scheduling Reports for Managed Appliances Using the Web UI on page 481 for details.
Malware Alert Notifications
You configure email settings for malware alert notifications on the Notification Settings
page of the Web UI or by using the fenotify email CLI commands. See the
"Notifications" section of the User Guide for details.See Event Notifications on page 285 for
details.
Configuring the Mail Server
Health check event notifications and scheduled reports can use the same mail server. If
you use the CLI to configure the server, you must use two separate sets of CLI commands.
The mail server settings are described in the following table.
System Mail Server Settings
Web
UI Field
142
Health
Report
Check
CLI
CLI
Parameter
Parameter
Description
Enable
email
—
—
Enables the email delivery of health check
notifications and scheduled reports.
Mail hub
mailhub
server
The hostname or IP address of the mail server.
Port
mailhubport
port
The SMTP port used to send the emails. The
default is 25.
Domain
domain
domain
The domain name from which emails will appear
to come. The default is the active domain for the
appliance.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Web
UI Field
Return
Addr
Configuring the Mail Server
Health
Report
Check
CLI
CLI
Parameter
Parameter
returnaddr
returnaddr
Description
Health check parameter: The username or fully
qualified return address from which emails are
sent. If the string contains the @ character, it is
considered fully qualified. Otherwise, it is
considered a username, and by default takes the
form <username>@<hostname>.<domain>. The
default username is do-not-reply.
Report parameter: The fully qualified return address
from which emails are sent.
Incl.
hostname
returnhost
—
Whether the appliance hostname is included in the
return address. If it is excluded, the return address
takes the form <username>@<domain>.
This setting is ignored if the provided return
address is fully qualified.
Prerequisites
l
Operator or Admin access
Configuring the Mail Server Using the Web UI
Use the Email Settings page to configure settings for the mail server.
© 2022 FireEye Security Holdings US LLC
143
Central Management System Administration Guide
CHAPTER 10: System Email Settings
To configure the mail server:
1. Click the Settings tab.
2. Click Email on the sidebar.
3. Specify settings as described in System Mail Server Settings on page 142.
4. Click Update to save your changes.
Configuring the Mail Server for Health Check
Notifications Using the CLI
Use the CLI commands in this topic to configure the mail server that sends health check
notifications. See System Mail Server Settings on page 142 for a description of each
parameter.
NOTE: See Configuring Email Recipients Using the CLI on page 149 for
information about configuring the notification recipients. See Configuring System
Event Notifications Using the CLI on page 152 for information about configuring the
events that trigger notifications.
To configure the mail server for system notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the hostname or IP address of the mail server:
hostname (config) # email mailhub {<hostname> | <IPv4 or IPv6 address>}
3. Specify the SMTP port used by the mail server to send notifications:
hostname (config) # email mailhub-port <port>
4. Specify the domain name from which emails will appear to come:
hostname (config) # email domain <domainName>
5. Specify the username or fully qualified return address from which emails are sent:
hostname (config) # email return-addr {<username> | <returnAddress>}
6. (Optional) Include the hostname of the mail server in the return address:
hostname (config) # email return-host
7. Verify your changes:
hostname (config) # show email
8. Save your changes:
hostname (config) # write memory
144
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring the Mail Server
NOTE: To remove a configuration or restore a default setting, append no to the
command. For example, to exclude the hostname in the return address, use the no
email return-host command, and to restore the default domain name, use the no
email domain command.
Examples
In this example, the return address is not fully qualified, so the hostname ("hostname") and
domain are appended to it.
hostname (config) # email mailhub 10.1.0.0
hostname (config) # email domain mail.acme.com
hostname (config) # email return-addr admin
hostname (config) # show email
Mail hub:
10.1.0.0
Mail hub port:
25
Domain override:
mail.acme.com
Return address:
admin
Include hostname in return address: yes
Current reply address: admin@hostname.mail.acme.com
...
In this example, the return address is fully qualified, so the hostname and domain are not
included.
hostname (config) # email mailhub 10.1.0.0
hostname (config) # email domain mail.acme.com
hostname (config) # email return-addr notify@acme.com
hostname (config) # show email
Mail hub:
10.2.0.0
Mail hub port:
25
Domain override:
mail.acme.com
Return address:
notify@acme.com
Include hostname in return address: yes
Current reply address: notify@acme.com
...
In this example, all settings are restored to their default values.
hostname (config) # show email
Mail hub:
10.3.0.0
Mail hub port:
26
Domain override:
mailhost.acme.com
Return address:
admin
Include hostname in return address: no
Current reply address: admin@hostname.mailhost.acme.com
...
hostname (config) # no email mailhub
hostname (config) # no email mailhub-port
hostname (config) # no email return-addr
hostname (config) # email return-host
hostname (config) # show email
Mail hub:
Mail hub port:
25
Domain override:
© 2022 FireEye Security Holdings US LLC
145
Central Management System Administration Guide
CHAPTER 10: System Email Settings
Return address:
do-not-reply
Include hostname in return address: yes
Current reply address: do-not-reply@hostname.acme.com
...
Configuring the Mail Server for Scheduled Reports Using
the CLI
Use the CLI commands in this topic to configure the mail server that sends scheduled
reports. See System Mail Server Settings on page 142 for a description of each parameter.
IMPORTANT! If you use the CLI to configure the mail server, the changes will not
appear on the Email Settings page in the Web UI.
NOTE: See Adding and Removing Scheduled Report Recipients on page 150 for
information about configuring the report recipients using the CLI.
To configure the mail server for scheduled reports:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the hostname or IP address of the mail server:
hostname (config) report email smtp server {<hostname> | <ipAddress>}
3. Specify the SMTP port used by the mail server to send reports:
hostname (config) # report email smtp port <port>
4. Specify the domain name from which emails will appear to come:
hostname (config) # report email smtp domain <domainName>
5. Specify the fully qualified return address from which emails are sent:
hostname (config) # report email smtp return-addr <returnAddress>
6. Verify your changes:
hostname (config) # show report email
7. Save the configuration:
hostname (config) # write memory
NOTE: To remove a configuration or restore the default setting, append no to the
command. For example, to restore the default return address, use the no report
email return-addr command, and to remove the configured domain name, use
the no report email smtp domain command.
146
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Email Recipients
Examples
In this example, the email server is configured to send scheduled reports.
hostname (config) # report email server 10.4.0.0
hostname (config) # report email smtp domain mailer.acme.com
hostname (config) # report email smtp return-addr reports@acme.com
hostname (config) # show report email
Report email configurations:
SMTP server: 10.4.0.0
SMTP server port: 25
SMTP Domain: mailer.acme.com
SMTP Return addr: reports@acme.com
...
In this example, all configuration settings are restored to their default values.
hostname (config) # show report email
Report email configurations:
SMTP server: 10.4.0.0
SMTP server port: 26
SMTP Domain: acme.com
SMTP Return addr: admin@acme.com
...
hostname (config) # no email report smtp server
hostname (config) # no email report smtp port
hostname (config) # no email report smtp domain
hostname (config) # no email report smtp return-addr
hostname (config) # show report email
Report email configurations:
SMTP server:
SMTP server port: 25
SMTP Domain:
SMTP Return addr: do-not-reply
...
Configuring Email Recipients
The same users can receive both system event notifications and scheduled reports. If you
use the CLI to configure them, you must use two separate sets of CLI commands.
Each new recipient will receive detailed notifications for all enabled system health check
events. You can customize the notifications for individual users, and configure which
specific events trigger notifications. (See Configuring System Events on page 151 for
details.)
© 2022 FireEye Security Holdings US LLC
147
Central Management System Administration Guide
CHAPTER 10: System Email Settings
IMPORTANT! If you use the CLI to configure a scheduled report recipient, the
change will not be reflected in the Web UI. For example:
l
l
You add analyst@acme.com using the report email recipient
analyst@acme.com CLI command. That recipient will be listed in the show
report email command output, but will not be added to the recipient list on
the Email Settings page in the Web UI.
The recipient list on the Email Settings page includes admin@acme.com, but
the Report checkbox is not selected. You then add that recipient using the
report email recipient admin@acme.com CLI command. The Report
checkbox will still not be selected on the Email Settings page.
IMPORTANT! If you use the Web UI to add an email recipient, the recipient will be
enabled to receive both system event notifications and scheduled reports. However,
if you use the email notify recipient CLI command to add this recipient, the
recipient will receive only system event notifications, not scheduled reports (the
Report check box will be cleared on the Email Settings page).
Prerequisites
l
Operator or Admin access
Configuring Email Recipients Using the Web UI
Use the Email Settings page to add or remove the email recipients for system event
notifications and for scheduled reports.
1. Click the Settings tab.
2. Click Email in the sidebar.
3. Locate the Email Recipients section.
4. Click Add Email Recipient.
5. Enter the email address of the user in the Add Email Recipient box and then click
Add Recipient.
148
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Email Recipients
6. (Optional) Clear the Info, Fail, Detail, and Scan checkboxes as needed to customize
the notifications the user will receive. (See Configuring System Event Notifications
Using the Web UI on page 151 for details.)
To add a scheduled report recipient:
1. Click Add Email Recipient.
2. Enter the email address of the user in the Add Email Recipient box and then click
Add Recipient.
3. Make sure the Report checkbox remains selected.
4. (Optional) Clear the Info, Fail, Detail, and Scan checkboxes to prevent the user from
receiving system event notifications as well as scheduled reports.
To remove an email recipient:
1. Click the icon in the Delete column.
2. When prompted, click OK to confirm the action.
Configuring Email Recipients Using the CLI
Use the commands in this section to add or remove email recipients for system event
notifications and scheduled reports.
IMPORTANT! If you use the CLI to add or remove a scheduled report recipient, the
changes will not appear on the Email Settings page in the Web UI.
Adding and Removing System Event Notification Recipients
To add system event notification recipients:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To add a recipient:
hostname (config) # email notify recipient <emailAddress>
3. To remove a recipient:
hostname (config) # no email notify recipient <emailAddress>
4. Verify your changes:
hostname (config) # show email
5. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
149
Central Management System Administration Guide
CHAPTER 10: System Email Settings
Adding and Removing Scheduled Report Recipients
To configure scheduled report recipients:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To add a recipient:
hostname (config) # report email recipient <emailAddress>
3. To remove a recipient:
hostname (config) # no report email recipient <emailAddress>
4. Verify your changes:
hostname (config) # show report email
5. Save your changes:
hostname (config) # write memory
Examples
This example adds analyst@acme.com as a system event notification recipient and
removes user3@acme.com.
hostname (config) # show email
...
Email notification recipients:
admin@acme.com (all events, in detail)
exec@acme.com (failure events only, in detail)
user3@acme.com (all events, summarized)
...
hostname (config) # email notify recipient analyst@acme.com
hostname (config) # no email notify recipient user3@acme.com
hostname (config) # show email
...
Email notification recipients:
admin@acme.com (all events, in detail)
analyst@acme.com (all events, in detail)
exec@acme.com (failure events only, in detail)
This example adds analyst@acme.com as a scheduled report recipient, and removes
admin@acme.com.
hostname (config) # show report email
Report email configurations:
...
Email recipients:
admin@acme.com
exec@acme.com
hostname (config) # report email recipient analyst@acme.com
hostname (config) # no report email recipient admin@acme.com
hostname (config) # show report email
Report email configurations:
...
150
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring System Events
Email recipients:
analyst@acme.com
exec@acme.com
Configuring System Events
By default, configured users receive detailed notifications about all enabled system events.
Informational events are logged when there is a change in the system. Failure events are
logged when there is a failure in the system.
You can use the CLI to change which events are enabled. For example, you could disable
informational events, such as system log file rotations, from triggering notifications.
For each recipient, you can specify whether failure notifications, informational
notifications, or both are sent. For example, a user might want to know that a disk failed,
but not that an excessive temperature condition returned to normal.
You can also specify whether a user receives summarized or detailed notifications.
Prerequisites
l
Operator or Admin access
Configuring System Event Notifications Using the Web UI
Use the Email Settings page to configure the severity of system email event notifications to
be sent to each configured recipient.
To enable or disable specific system notifications, you must use the CLI. See Configuring
System Event Notifications Using the CLI on the next page.
To configure severity of system event notifications to be sent to recipients:
1. Click the Settings tab.
2. Click Email in the sidebar.
3. Locate the Email Recipients section.
© 2022 FireEye Security Holdings US LLC
151
Central Management System Administration Guide
CHAPTER 10: System Email Settings
4. Select or clear the Info and Fail checkboxes to specify the severity of events for
which the user receives notifications.
5. Select or clear the Detail checkbox to specify whether the user receives detailed or
summarized notifications.
6. Select or clear the Scan checkbox to specify whether or not the user receives an
email once a configured scan has completed.
7. Click Update to save your changes.
Configuring System Event Notifications Using the CLI
Use the commands in this topic to customize system event notifications for each user and
to configure which events trigger notifications.
IMPORTANT: You cannot view most Central Managementhigh availability (HA)
events as described in this topic, and cannot configure which of those events trigger
notifications. For a list of the HA events and their severity, see the Central
Management High Availability Guide.
Viewing System Events
You can view all system events, or the system events that are currently enabled to trigger
notifications, ordered by their severity.
To view all system events:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the events:
hostname (config) # email notify event ?
To view enabled system events and their severity:
l
View the events by severity:
hostname > show email events
Configuring System Event Notifications for Each User
To configure system event notifications for each user:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
152
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring System Events
2. View the current configuration:
hostname (config) # show email
3. Specify the severity of events for which each user should receive notifications.
l
To receive "info" events:
hostname (config) # email notify recipient <emailAddress> class
info
l
To stop receiving "info" events:
hostname (config) # no email notify recipient <emailAddress> class
info
l
To receive "failure" events:
hostname (config) # email notify recipient <emailAddress> class
failure
l
To stop receiving "failure" events:
hostname (config) # no email notify recipient <emailAddress> class
failure
4. Specify the notification format.
l
To receive detailed notifications:
hostname (config) # email notify recipient <emailAddress> detail
l
To receive summarized notifications:
hostname (config) # no email notify recipient <emailAddress>
detail
Configuring Which Events Trigger Notifications
To configure which events trigger notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the current configuration as described in Viewing System Events on the
previous page.
3. To enable an event:
hostname (config) # email notify event <event>
4. To disable an event:
hostname (config) # no email notify event <event>
5. Verify your changes:
hostname (config) # show email events
© 2022 FireEye Security Holdings US LLC
153
Central Management System Administration Guide
CHAPTER 10: System Email Settings
6. Save your changes:
hostname (config) # write memory
Examples
This example stops admin@acme.com from receiving "info" notifications and changes the
message format to a summary.
hostname (config) # show email
...
Email notification recipients:
admin@acme.com (all events, in detail)
operator@acme.com (failure events only, in detail)
user3@acme.com (all events, in detail)
...
hostname (config) # no email notify recipient admin@acme.com info
hostname (config) # no email notify recipient admin@acme.com detail
hostname (config) # show email
...
Email notification recipients:
admin@acme.com (failure events only, summarized)
operator@acme.com (failure events only, in detail)
user3@acme.com (all events, in detail)
This example disables log file rotations from triggering event notifications:
hostname (config) # no email notify event syslog-rotation
This example disables DOP (depth of processing) overloads from triggering event
notifications:
hostname (config) # no email notify event avc-overload
The avc-overload event is an "info" level event that is generated for DOP overloads. DOP
overloads occur when there is CPU contention for an MVX engine. If an overload occurs
often, it can affect email and file analysis and potentially result in false negatives. If an
appliance consistently has less than 30% DOP, it is overloaded. This may not be an issue if
an overload happens for only a few minutes a week, but if there are overloads for several
hours of every work day, the MVX engine should be allotted more CPU time.
Configuring Auto Support for System
Event Notifications
You can configure the appliance to send emails to autosupport@fireeye.com when
specific system events occur.
This includes configuring settings to ensure the emails are sent securely. You can specify
one of the following security types:
154
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
Configuring Auto Support for System Event Notifications
none—Do not use TLS to secure the autosupport emails.
tls—Use TLS over the default server port to secure autosupport emails. Do not send
the emails if TLS fails.
tls-none—Use TLS over the default server port to secure autosupport email. The
email is sent in plain text if TLS fails.
Prerequisites
l
Operator or Admin access
Configuring Auto Support for System Event Notifications
Using the CLI
Use the commands in this section to configure autosupport for system event notifications.
(See Viewing System Events on page 152 for information about viewing a full list of
events.)
To configure autosupport:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable autosupport email notifications (disabled by default):
hostname (config) # email autosupport enable
3. Display the current configuration for generating autosupport emails for system
events:
hostname (config) # show email
4. Specify each event for which autosupport email notifications should be sent:
hostname (config) # email autosupport event <event>
5. Configure the supplemental Certificate Authority (CA) certificates that are used to
verify the server certificates.
l
To use only the built-in list:
hostname (config) # email autosupport ssl ca-list none
l
To use the default supplemental CA certificate list:
hostname (config) # email autosupport ssl ca-list default-ca-list
6. Configure a security type to use for autosupport email.
l
No TLS:
hostname (config) # email autosupport ssl mode none
© 2022 FireEye Security Holdings US LLC
155
Central Management System Administration Guide
l
CHAPTER 10: System Email Settings
TLS:
hostname (config) # email autosupport ssl mode TLS
l
TLS none:
hostname (config) # email autosupport ssl mode tls-none
7. Verify the server certificates:
hostname (config) # email autosupport cert-verify
8. Save your changes:
hostname (config) # write memory
156
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Manual Time Configuration
CHAPTER 11: Date and Time
Settings
You can set the CM appliance date and time manually, or configure one or more Network
Time Protocol (NTP) servers that synchronize the time automatically. You can also perform
a one-time synchronization of the system clock to the DTI server clock.
This section covers the following information:
l
Manual Time Configuration below
l
NTP Server Configuration on page 159
l
Time Zone Configuration on page 168
l
Synchronizing the System Clock to DTI Server Time Using the CLI on page 170
NOTE: The date and time are stored as Coordinated Universal Time (UTC) in the
database. The Z character in syslog output indicates that the time displayed is in the
UTC time zone; for example, Oct 19 2016 16:10:10 Z. By default, the display time
zone is UTC.
Manual Time Configuration
You can manually set the date and time on your CM appliance.
l
Setting the Date and Time Using the Web UI below
l
Setting the Date and Time Using the CLI on the next page
Setting the Date and Time Using the Web UI
Use the top section of the Date and Time Settings page to set the date and time for your
CM appliance.
© 2022 FireEye Security Holdings US LLC
157
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
IMPORTANT! NTP synchronization is set by default and must be disabled before
you can manually configure the date and time. For instructions about disabling
NTP, see NTP Server Configuration on the facing page.
Prerequisites
l
Admin access
To set the date and time:
1. Click the Settings tab.
2. Click Date and Time on the sidebar.
3. Select the date and time from the drop-down lists.
4. Click Update Time.
5. Set the time zone as described in Time Zone Configuration on page 168.
Setting the Date and Time Using the CLI
Use the CLI commands in this topic to set the time zone on your CM appliance.
IMPORTANT! NTP synchronization is set by default and must be disabled before
you can manually configure the date and time. For information about disabling
NTP, see NTP Server Configuration on the facing page.
Prerequisites
l
Admin access
To set the date and time:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
158
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
NTP Server Configuration
2. (Optional) Use the clock set <HH>:<MM> <YYYY>/<MM>/<DD> command to specify
the time and date. For example, the following command sets the time and date to
2:00 p.m. on July 21, 2014:
hostname (config) # clock set 14:00 2014/07/21
3. Use the clock timezone <timezone> command to specify the time zone. For
example, both of the following commands set the time zone to Pacific Standard
Time:
hostname (config) # clock timezone UTC-offset UTC+8
hostname (config) # clock timezone America North United_States Pacific
NOTE: The time zone is for display purposes and should match other
security device settings.
4. To restore the default time zone:
hostname (config) # no clock timezone
5. View the configured time and date settings:
hostname (config) # show clock
6. Save your changes.
hostname (config) # write memory
Examples
l
Time and date using the North America Central Daylight time zone:
hostname > show clock
Time:
16:39:35
Date:
2014/06/25
Time zone:
America North United_States Central
(US/Central)
UFC offset: -0500 (UTC minus 5 hours)
l
Time and date settings using the default time zone:
hostname > show clock
Time:
21:40:37
Date:
2014/06/25
Time zone:
UTC
(Etc/UTC)
UTC offset:
same as UTC
NTP Server Configuration
Instead of manually setting the system date and time, you can specify one or more
Network Time Protocol (NTP) servers and peers to synchronize the time automatically. By
default, NTP version 4 is used, but you can specify version 3 instead. You can perform a
© 2022 FireEye Security Holdings US LLC
159
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
one-time action that synchronizes the system clock with a specific NTP server. NTP is
enabled by default. The appliance is pre-configured with four NTP servers your appliance
can use if it can reach them.
The appliance can authenticate that the time it obtains from an NTP server is from a
known and trusted source. The system clock is updated only if a key ID in the incoming
NTP packet matches a key ID configured on the appliance, and if that key ID is mapped to
the same MD5 or SHA1 hash value stored on both the NTP server and the appliance. If the
key ID/value pair on NTP server and appliance do not match, the clock is not updated.
NTP authentication is enabled by default, but the NTP server must already have the key
ID/value pair, and the same key ID/value pair must be configured on the appliance and
then associated with the NTP server. A total of 16 keys can be configured on a single
appliance.
l
Configuring NTP Servers Using the Web UI below
l
Configuring NTP Servers Using the CLI on the facing page
l
Configuring NTP Authentication Using the CLI on page 164
Prerequisites
l
l
l
l
Admin access to configure NTP
Monitor, Operator, or Admin access to view NTP configuration and status
information
Connectivity to at least one NTP server
For NTP authentication: Authentication key ID/value pairs on the NTP servers for
which authentication will be configured
Configuring NTP Servers Using the Web UI
Use the Enable NTP section of the Date and Time Settings page to configure NTP servers.
160
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
NTP Server Configuration
To configure NTP servers:
1. Click the Settings tab.
2. Click Date and Time on the sidebar.
3. Click Add NTP Server.
4. Enter the IP address or hostname of the NTP server that you want to use in the Add
NTP Server box.
5. Click Add.
6. Repeat the previous three steps to add additional servers.
7. To synchronize the system time once with a selected NTP server, click Update next
to the server entry.
The time is updated, and the needed adjustment is displayed in a message on the
page.
8. To delete an NTP server, select the checkbox next to the server and then click
Remove NTP Server.
9. Click Yes to confirm the action.
Configuring NTP Servers Using the CLI
Use the commands in this topic to configure NTP servers.
NOTE: See Configuring NTP Authentication Using the CLI on page 164 for
information about ensuring that the system clocks are only updated if the time is
obtained from a trusted source.
To enable and configure NTP servers:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable NTP synchronization:
hostname (config) # ntp enable
3. Specify the primary NTP server:
hostname (config) # ntp server <server>
where <server> is the IPv4 or IPv6 address, or hostname of the NTP server.
4. Repeat the previous step for the secondary NTP server and any additional
NTP servers.
© 2022 FireEye Security Holdings US LLC
161
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
To change the NTP version:
1. Specify the version:
hostname (config) # ntp
2. To change the version on an NTP server:
hostname (config) ntp server <server> version <version>
where <server> is the IPv4 or IPv6 address, or hostname of the NTP server, and
<version> is either 3 or 4
3. To change the version on an NTP peer:
hostname (config) ntp peer <peer> version <version>
where <peer> is the IPv4 or IPv6 address, or hostname of the NTP peer, and
<version> is either 3 or 4.
4. Save your changes:
hostname (config) # write memory
To disable NTP:
1. Disable NTP synchronization:
hostname (config) # ntp disable
or
hostname (config) # no ntp enable
2. Save your changes:
hostname (config) # write memory
To synchronize the system time with a specific NTP server one time:
1. Synchronize the system time:
hostname (config) # ntpdate <server>
where <server> is the IPv4 or IPv6 address, or hostname of the NTP server to
synchronize with.
2. Save your changes:
hostname (config) # write memory
To view the current NTP runtime state and configuration:
1. Go to CLI standard mode.
2. View the information:
hostname > show ntp
162
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
NTP Server Configuration
To view the configured NTP servers and their settings:
1. Go to CLI standard mode.
2. View the information:
hostname > show ntp configured
Examples
The following example configures two NTP servers and an NTP peer.
hostname (config) # ntp server 0.acme.pool.ntp.org
hostname (config) # ntp server 1.acme.pool.ntp.org
hostname (config) # ntp peer 5.acme.pool.ntp.org
hostname (config) # show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
NTP peer 5.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
NTP server 0.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
NTP server 1.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
The following example disables NTP synchronization on the system.
hostname (config) # no ntp enable
hostname (config) # show ntp configured
NTP enabled: no
NTP Authentication enabled: yes
No NTP peers configured.
NTP server 0.acme.pool.ntp.org
Enabled: yes
...
hostname (config) # show ntp
NTP is administratively disabled.
NTP Authentication is administratively enabled.
Clock is unsynchronized.
No NTP associations present.
The following example temporarily disables NTP on the "3.acme.pool.ntp.org" server.
hostname (config) # ntp server 3.acme.pool.ntp.org disable
hostname (config) # show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
No NTP peers configured.
NTP server 0.acme.pool.ntp.org
Enabled: yes
...
NTP server 3.acme.pool.ntp.org
Enabled: no
...
The following example removes the "2.acme.pool.ntp.org" NTP server.
© 2022 FireEye Security Holdings US LLC
163
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
hostname (config) # no ntp server 2.acme.pool.ntp.org
The following example synchronizes the system clock with the NTP server.
hostname (config) # ntpdate 0.acme.pool.ntp.org
adjust time server 192.168.120.23 offset -0.023716 sec
The following example changes the NTP version on the "3.acme.pool.ntp.org" server to
version 3.
hostname (config) # ntp server 3.acme.pool.ntp.org version 3
hostname (config) # show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
No NTP peers configured.
...
NTP server 3.acme.pool.ntp.org
Enabled: yes
NTP version: 3
Key: none
The following example shows the current NTP runtime state and configuration.
hostname > show ntp
NTP is administratively enabled.
NTP Authentication is administratively enabled.
Clock is synchronized. Reference: 10.255.34.6 Offset: 1.713 ms.
Active servers and peers:
Poll
Last
Conf
Offset
Ref
Interv Resp
Address
Type Status
Stratum (msec)
Clock
(sec)
(sec)
===========================================================================
192.168.1.1 n/a
candidat (+)
2
-0.233
10.2.3.4
64
60
10.2.3.4
n/a
outlyer (-)
2
12.069
192.168.2.2
64
50
172.16.4.5
n/a
candidat (+)
2
-0.958
10.5.6.7
64
50
10.255.34.6 n/a
sys.peer (*)
2
1.713
172.16.3.4
64
45
The following example shows the configured NTP servers and their settings:
hostname > show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
No NTP peers configured.
NTP server 0.acme.pool.ntp.org
Enabled: yes
NTP version: 4
NTP server 1.acme.pool.ntp.org
Enabled: yes
NTP version: 4
NTP server 2.acme.pool.ntp.org
Enabled: yes
NTP version: 4
NTP server 3.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Configuring NTP Authentication Using the CLI
This topic describes how to configure NTP authentication using the CLI.
164
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
NTP Server Configuration
Enabling NTP Authentication and Configuring Keys
Perform the tasks in this section in the order shown to configure NTP authentication.
Obtain the authentication keys from the NTP server:
1. On the NTP server, map a key ID from 1–16 to an MD5 or SHA1 hash value.
2. Repeat the previous step for additional key ID/value pairs.
3. Copy and paste the key ID/value pairs so they can be configured on the appliance
later in this procedure.
Enable NTP and NTP authentication:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the current status.
hostname (config) # show ntp configured
3. If NTP enabled: no appears in the command output, enable NTP.
hostname (config) # ntp enable
4. If NTP Authentication enabled: no appears is the command output, enable NTP
authentication.
hostname (config) # ntp authentication enable
Define the authentication keys:
1. Use the following command to configure the key ID and hash value you obtained
from the NTP server:
hostname (config) # ntp authentication key <number> hash <type> <value>
where:
l
<number> is an integer from 1–16
l
<type> is md5 or sha1
l
<value> is the hash value
2. Repeat the previous step for each key you want to define.
3. View the configured keys.
hostname (config) # show ntp authentication configured
4. Save your changes.
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
165
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
Assign the keys to the NTP servers:
1. To assign a key to an NTP server, use the ntp server <server> authentication
key <number> command, where <server> is the IP address or hostname of the
NTP server, and <number> is the integer that you assigned to the key in the
previous task
The following example assigns hash key 1 to the NTP server 0.acme.pool.ntp.org:
hostname (config) # ntp server 0.acme.pool.ntp.org authentication key 1
2. Repeat the previous step for each key you want to define.
3. View the assigned keys:
hostname (config) # show ntp configured
4. Verify that the keys are valid:
hostname (config) # show ntp authentication
5. Save your changes:
hostname (config) # write memory
Disabling NTP Authentication and Removing Keys
You cannot delete an authentication key from the system if it is mapped to an NTP server.
If a key is mapped to an NTP server, you must disable NTP authentication on that server
before you delete the key.
To disable NTP authentication on the system:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable NTP authentication:
hostname (config) # no ntp authentication
3. Save your changes:
hostname (config) # write memory
To disable NTP authentication on a specific server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
166
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
NTP Server Configuration
2. To disable NTP authentication with a specified NTP server, use the no ntp
server <server> authentication command, where <server> is the hostname or
IP address of the NTP server.
The following example disables NTP authentication with the NTP server with
hostname 1.acme.pool.ntp.org:
hostname (config) # no ntp server 1.acme.pool.ntp.org authentication
3. Save your changes:
hostname (config) # write memory
To delete an NTP authentication key:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To delete a key, use the no ntp authentication key <number> command, where
<number> is the key ID.
hostname (config) # no ntp authentication key 1
3. Save your changes:
hostname (config) # write memory
Examples
The following example shows the current configuration.
hostname (config) # show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
No NTP peers configured.
NTP server 0.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
NTP server 1.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
NTP server 2.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
The following example defines two authentication keys and assigns each one to an
NTP server.
hostname (config) # ntp authentication key 1 hash md5
153ffa51cc765fb257e384e8e6aec8fe
hostname (config) # ntp server 0.acme.pool.ntp.org key 1
hostname (config) # ntp authentication key 2 hash sha1
27a048b642be47d50a9c38427495945429597d91
© 2022 FireEye Security Holdings US LLC
167
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
hostname (config) # ntp server 1.acme.pool.ntp.org key 2
hostname (config) # show ntp configured
NTP enabled: yes
NTP Authentication enabled: yes
No NTP peers configured.
NTP server 0.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: 1
NTP server 1.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: 2
NTP server 2.acme.pool.ntp.org
Enabled: yes
NTP version: 4
Key: none
hostname (config) # show ntp authentication configured
NTP enabled: yes
NTP Authentication enabled: yes
NTP Key Number 1
Type: md5
Key: 153ffa51cc765fb257e384e8e6aec8fe
NTP Key Number 2
Type: sha1
Key: 27a048b642be47d50a9c38427495945429597d91
hostname (config) # show ntp authentication
NTP is administratively enabled.
NTP authentication is administratively enabled.
Active servers and peers:
Address
auth
keyid
=====================================
172.16.2.3
ok
1
10.30.4.3
ok
2
192.168.10.12
none
none
The following example disables NTP authentication on the 1.acme.pool.ntp.org server and
then deletes the key it was using from the system.
hostname (config) # no ntp server 1.acme.pool.ntp.org authentication
hostname (config) # no ntp authentication key 2
Time Zone Configuration
You must set the time zone on your CM appliance whether you configure the date and
time manually or synchronize with an NTP server.
168
l
Setting the Date and Time Using the Web UI on page 157
l
Setting the Date and Time Using the CLI on page 158
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Time Zone Configuration
Setting the Time Zone Using the Web UI
Use the bottom section of the Date and Time Settings page to set the time zone for your
appliance.
Prerequisites
l
Admin access
To set the time zone:
1. Click the Settings tab.
2. Click Date and Time on the sidebar.
3. Select the time zone from the drop-down list.
4. Select options from other drop-down lists, if present.
5. Click Set Time Zone.
Setting the Time Zone Using the CLI
Use the CLI commands in this topic to set the time zone on your CM appliance.
Prerequisites
l
Admin access
To set the time zone:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To specify the time zone, use the clock timezone <timezone> command.
For example, both of the following commands set the time zone to Pacific Standard
Time:
hostname (config) # clock timezone UTC-offset UTC+8
© 2022 FireEye Security Holdings US LLC
169
Central Management System Administration Guide
CHAPTER 11: Date and Time Settings
hostname (config) # clock timezone America North United_States Pacific
NOTE: The time zone is for display purposes and should match other
security device settings.
3. Restore the default time zone:
hostname (config) # no clock timezone
4. View the configured time and date settings:
hostname (config) # show clock
5. Save your changes:
hostname (config) # write memory
Examples
Time and Date Using the North America Central Daylight Timezone
hostname # show clock
Time:
16:39:35
Date:
2014/06/25
Time zone:
America North United_States Central
(US/Central)
UFC offset: -0500 (UTC minus 5 hours)
Time and Date Settings Using the Default Timezone
hostname # show clock
Time:
21:40:37
Date:
2014/06/25
Time zone:
UTC
(Etc/UTC)
UTC offset:
same as UTC
Synchronizing the System Clock to
DTI Server Time Using the CLI
The system time should match the DTI server time as closely as possible. This is necessary
for features such as the license update service, in which licenses are downloaded from the
DTI server and installed on the CM appliance.
IMPORTANT! To prevent time gaps that could affect the validity of your licenses,
Trellix recommends that you perform this synchronization before you enable the
feature.
The fenet time sync CLI command retrieves the time (in UTC) from the DTI server and
then synchronizes the system clock to it. This command is especially useful if you do not
use NTP servers to synchronize your system clock.
170
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Synchronizing the System Clock to DTI Server Time Using the CLI
IMPORTANT! This action synchronizes the system clock to the DTI server a single
time. It does not change the system time zone.
Prerequisites
l
Admin access
To synchronize the system clock to the DTI server clock:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Synchronize the clocks:
hostname (config) # fenet time sync
3. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
171
Central Management System Administration Guide
172
CHAPTER 11: Date and Time Settings
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
PART III: Administration
l
Network Administration on page 175
l
Upgrading the FireEye Software on page 197
l
Log Management on page 217
l
Database Backup and Restore on page 233
l
System Health and Performance on page 253
l
SNMP Data on page 269
l
Login Banners and Messages on page 277
l
Event Notifications on page 285
l
Disk Space Management on page 335
© 2022 FireEye Security Holdings US LLC
173
Central Management System Administration Guide
174
PART III: Administration
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Basic Network Configuration
CHAPTER 12: Network
Administration
This section covers the following information:
l
Basic Network Configuration below
l
IP Filtering on page 181
l
Configuring HTTP Proxy Server Settings on page 186
l
Defining Another Management Interface on page 188
For additional information about configuring interfaces, see the CLI Command Reference. For
information about connecting to, configuring, and troubleshooting Managed Defense, see
the Managed Defense Quick Start Guide.
IMPORTANT: You must use the same link settings on both ends of a network
connection. For example, you cannot change the interface speed on one end to "auto"
if the other end has a manual speed configured.
Basic Network Configuration
The following sections describe basic management interface and global network
configuration settings.
Management Interface Settings
The following list describes the management interface configuration settings.
l
IP Version—The appliance has dual-stack support for Internet Protocol version 4
(IPv4) and version 6 (IPv6) on the management interface.
© 2022 FireEye Security Holdings US LLC
175
Central Management System Administration Guide
l
l
l
l
l
l
l
CHAPTER 12: Network Administration
DHCP—Dynamic Host Configuration Protocol (DHCP) dynamically distributes
network configuration parameters. If DHCP is disabled on the management
interface, you must manually configure the IP address, subnet mask, and default
gateway or next-hop device.
IP Address—The IPv4 or IPv6 address of the management interface. Both types of
addresses can be configured. The IPv4 address is enabled by default. You must
explicitly enable the IPv6 address.
Subnet Mask—The network portion of the IP address. For example, 255.255.255.0
indicates that the first 24 bits of an IPv4 address are used for the network portion of
the address.
Default Gateway—For an IPv4 address, the IPv4 address of the default router. For
an IPv6 address, the IPv6 address of the default router or next-hop device.
Autoconf Enabled—When Stateless Address Autoconfiguration (SLAAC) is enabled,
an IPv6 address is automatically assigned for the interface. The address is based on
an IPv6 prefix learned from router advertisements, combined with an interface
identifier based on the MAC address of the interface.
Autoconf Route—When this feature is enabled, the system learns a default route
from the automatically assigned IPv6 address.
Autoconf Privacy—When this feature is enabled, the system generates random host
identifiers (known as privacy extensions) to construct the IPv6 address. This
provides more security when communicating with remote hosts.
Global Network Settings
The following list describes global network configuration settings.
l
l
l
176
DNS Servers—Domain Name System (DNS) servers translate domain names to IP
addresses for routing. At least one DNS server is required. You can optionally
configure a secondary DNS server that is used when the primary server is
unavailable or cannot resolve a domain name. You can view a list of DNS servers
that will be traversed for DNS resolution, in order, from top to bottom. Only active
DNS servers are listed. If neither DNS server can resolve the domain name, an error
is displayed.
Domain Names—The domain names the DNS servers resolve to IP addresses. You
can view a list of domain names in order, from top to bottom.
Hostname—The hostname of the appliance (for example, dc-01). You can include
the domain (for example, dc-01.acme.com).
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Basic Network Configuration
IPv6—You can enable or disable IPv6 routing on the system, on the management
interface, or both. IPv6 must be enabled on the Network Security appliances that are
members of a Network Security High Availability (HA) pair. It is enabled
automatically by the Central Management appliance that manages the HA pair.
VPN—You can enable or disable virtual private networking (VPN) on the system.
When VPN is enabled, the appliance can connect to Managed Defense over the
Internet using a secure SSL VPN connection. VPN requires a valid MD_ACCESS
license on the appliance. VPN requires IPv6 routing, so IPv6 must be enabled on the
system before you can enable VPN. For more information, see the Managed Defense
Quick Start Guide.
Prerequisites
l
Operator or Admin access
Configuring Basic Network Settings Using the Web UI
Use the Network Settings page to configure basic network settings for the CM appliance.
For a description of the information and settings on this page, see Basic Network
Configuration on page 175.
Viewing Management Interface Detail Settings
Use the Interface Details section to view the configuration of the management interface.
This is a read-only section. The management interface is configured during the initial
configuration, and can be modified later using the CLI. For details, see Initial Configuration
on page 77 or the CLI Command Reference.
To view the management interface configuration:
1. Log in to the managing Central Management Web UI.
2. Click the Settings tab.
3. Select Network on the sidebar.
4. Locate the Interface Details section at the top of the page.
© 2022 FireEye Security Holdings US LLC
177
Central Management System Administration Guide
CHAPTER 12: Network Administration
Configuring DNS Servers
Use the Configure DNS Server Addresses section to configure DNS server addresses.
To configure DNS servers:
1. Click the Settings tab.
2. Select Network on the sidebar.
3. In the Configure DNS Server Addresses section, enter the IP address of the primary
DNS server.
4. (Optional) Enter the IP address of a secondary DNS server.
5. Click Apply.
The order in which the DNS servers are traversed is displayed in the DNS Resolution
order list. An error message is displayed if no server is active.
Configuring Domain Names
Use the Configure Domain Names section to add or remove domain names.
To add domain names:
1. Click the Settings tab.
2. Select Network on the sidebar.
3. In the Configure Domain Names section, click Add Domain Name.
4. Enter a domain name, click Add.
178
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Basic Network Configuration
5. Repeat the previous steps to configure additional domain names.
The order in which the domain names are traversed is displayed in the Domain Names
Resolution order list.
To remove domain names:
1. Locate the domain name you want to delete.
2. Click the Delete (trash can) icon in the Delete column for each domain name you
want to remove.
3. Click YES.
The domain name is deleted from the configuration.
4. Close the message.
Enabling IPv6
Use the Configure IPv6 section to enable or disable IPv6 routing. You can also use this
section to enable or disable IPv6 on the SMTP interface.
To enable IPv6 routing:
1. Click the Settings tab.
2. Select Network on the sidebar.
3. Enable IPv6:
l
l
To enable IPv6 routing on the system, select the Global IPv6 checkbox, and
then click Apply.
To enable IPv6 on the management interface, select the Management
Interface IPv6 checkbox, and then click Apply.
To disable IPv6 routing:
1. Click the Settings tab.
© 2022 FireEye Security Holdings US LLC
179
Central Management System Administration Guide
CHAPTER 12: Network Administration
2. Select Network on the sidebar.
3. Disable IPv6:
l
l
To disable IPv6 routing on the system, clear the Global IPv6 checkbox, and
then click Apply.
To disable IPv6 on the management interface, clear the Management
Interface IPv6 checkbox, and then click Apply.
Enabling VPN
The VPN Settings section appears at the bottom of the page if a valid MD_ACCESS license
is installed. You can enable VPN only when IPv6 is enabled on the system. For details, see
the Managed Defense Quick Start Guide.
Configuring Basic Network Settings Using the CLI
Use the commands in this topic to configure the network settings manually.
To configure basic network settings:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To disable DHCP for the interface:
hostname (config) # no interface ether1 dhcp
NOTE: If you use DHCP and there is no network connection for the
management interface, do the following:
a. Restore the network connection.
b. Disable DHCP.
c. Enable DHCP.
3. Set the interface IP address and network mask. For example:
hostname (config) # interface ether1 ip address 1.1.1.1 255.240.0.0
4. Specify the default gateway. For example:
hostname (config) # ip default-gateway 1.1.1.2 ether1
5. Specify a DNS server. For example:
hostname (config) # ip name-server 10.10.20.5
6. Save your changes.
hostname (config) # write memory
180
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
IP Filtering
IP Filtering
IP filtering allows you to manage rules for filtering IP packets entering and leaving the
appliance through its management interfaces. IP filtering supports IPv4 and IPv6, by
separate but largely identical sets of CLI commands. For more information, see the CLI
Command Reference.
IP filtering is disabled by default for both IPv4 and IPv6. However, some appliances may
have IP filtering enabled by existing components on the system which will still be visible
in the show ip filter command output.
NOTE: Enabling IPv6 filtering has no effect unless IPv6 is enabled.
Interfaces Supported by IP Filtering Rules
When you use IP filtering, interfaces can be grouped into three sets:
1. Management interfaces: ether*. IP filtering rules apply to these interfaces. Some
appliances such as the Network Security appliance, have one management interface,
ether1. On the Central Management platform and Endpoint Security appliance, there
are multiple management interfaces, named ether1, ether2, and so on.
If an interface is not specified for a rule, the default is "ether+," which in IP filtering
matches any interface beginning with "ether".
2. Data ports: pether* . These interfaces cannot have IP filtering rules.
3. Other interfaces: lo, tun0 (if a VPN is enabled). These interfaces may have IP
filtering rules installed automatically by the system. You cannot configure the rules
for these interfaces.
Viewing IP Filtering Rules
When you view a list of IP filtering rules using the show ip filter or show ipv6
filter command, rules added for management interfaces as described above and rules
added automatically by the system are listed together, in the order in which they are
applied.
If you are on the VPN, you should use the show ipv6 filter command, which displays
detailed information about the firewall rules. The show ipv6 filter configured
command, described below, does not include this information.
Rules that are manually configured are shown with numbers in the left column, which
correspond to the rule numbers visible in show ip filter configured and show ipv6
filter configured command output. Rules that are added automatically by the system
do not have numbers.
© 2022 FireEye Security Holdings US LLC
181
Central Management System Administration Guide
CHAPTER 12: Network Administration
The default filter configuration for the INPUT and OUTPUT chains is an ACCEPT rule
with a DROP policy for all traffic on all interfaces whose names begin with "ether". The
default configuration for the FORWARD is simply a DROP policy with no rules since CM
appliances do not forward packets. Enabling IP filtering has no effect on your network's
function until you create new IP filter rules.
When IP filtering is enabled, one additional rule is added automatically by the system after
all configured rules. This rule is to ACCEPT all inbound and outbound traffic on the
loopback 'lo' interface. The system requires the loopback interface to work for internal
purposes.
NOTE: When you enable Managed Defense, IP filters are automatically enabled. See
the Managed Defense Quick Start Guide for details.
CAUTION: This feature will affect integration with third-party services. Exercise
caution and common sense when adding IP filtering rules. If rules are set
improperly, it may cause problems such as dropping all traffic. For example,
adding DROP rules on the OUTPUT chain for ether1 or ether+ could interfere with
remote syslog; or adding DROP rules on the INPUT chain could interfere with
external access to system services such as SNMP.
Prerequisites
l
Operator or Admin access to configure IP filtering
l
Monitor, Operator, or Admin access to view IP filtering
Enabling IP Filtering Using the CLI
Use the commands in this section to enable IP filtering.
NOTES:
l
l
The default rules do not place any restrictions on incoming and outgoing
packets on ether* interfaces. You may add rules using the CLI. Use caution to
not block access to needed network services.
IP filtering is automatically enabled when you connect to Managed Defense,
described in the Managed Defense Quick Start Guide.
To view the active rules:
1. Go to CLI enable mode:
hostname > enable
182
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
IP Filtering
2. View the rules:
hostname # show ip filter
hostname # show ipv6 filter
To enable IP filtering:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable IP filtering:
hostname (config) # ip filter enable
hostname (config) # ipv6 filter enable
3. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
183
Central Management System Administration Guide
CHAPTER 12: Network Administration
Creating IPS Custom Variables Using the
Web UI
IPS custom variables are used in custom IPS rules, which are uploaded via the Web UI or
the API. This feature is supported on the following appliances:
l
Central Management release 9.1.3 and later.
l
Network Security release 9.1.3 and later.
The IPS policy synchronization capability supports custom variables. IPS custom rules
configured with IPS custom variables will synchronize successfully across all the managed
appliances.
Prerequisites
l
Operator or admin access
To create an IPS custom variable using the Web UI:
1. Log in to the Central Management Web UI.
2. Navigate to the IPS Custom Rules page.
184
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Creating IPS Custom Variables Using the Web UI
3. Click Add.
4. Enter the Name of the variable.
A variable name can only have alphanumeric characters, hyphen, and underscore
symbols. You can edit a variable even after creating it.
5. Select the Type from the dropdown list: IP Address or Port Address. The type
cannot be modified later.
6. Enter one of the following:
l
A valid IPv4 or IPv6 address.
l
A port number between 1 and 65535.
To add multiple addresses, enter a list of port numbers or IP addresses separated by
commas. Port range can also be specified as 1:46. Use a $ prefix to refer to another
variable name. You can assign up to 500 values to a single variable.
7. Click Save to save new variable.
Click Delete or Delete All buttons to delete one variable or multiple variables at once.
If your appliance is managed by a Central Management appliance, enable the Write To
Group option in the Central Management Web UI to push the changes to a selected group
of appliances managed by the Central Management appliance.
© 2022 FireEye Security Holdings US LLC
185
Central Management System Administration Guide
CHAPTER 12: Network Administration
Configuring HTTP Proxy Server Settings
Configuring an HTTP proxy server on your appliance involves the following tasks:
l
l
Configuring the hostname or IP address of the proxy server.
Configuring the port for client communication, if you do not want to accept the
default port (port 8080).
l
(Optional) Enabling basic authentication on the proxy server.
l
(Optional) Specifying a user-agent string that is included in HTTP requests.
l
Enabling the proxy server.
Prerequisites
l
Admin access.
l
The HTTP proxy server is deployed in your network.
Configuring HTTP Proxy Server Settings Using the CLI
Use the commands in this section to configure and enable an HTTP proxy server on an
appliance.
To configure and enable an HTTP proxy server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Configure the proxy server hostname or IP address, and the port (if you do not want
to use the default, port 8080):
hostname (config) # fenet proxy host <hostname or IP address>[:<port>]
3. Optional: Specify the credentials for basic authentication:
l
Specify the user:
hostname (config) # fenet proxy auth basic user <username>
l
Specify the password:
hostname (config) # fenet proxy auth basic password <password>
4. Optional: Specify a user-agent string:
hostname (config) # fenet proxy user-agent <string>
5. Enable the proxy server:
hostname (config) # fenet proxy enable
186
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring HTTP Proxy Server Settings
6. Verify your changes:
hostname (config) # show fenet
7. Save your changes:
hostname (config) # write memory
NOTE: The show fenet status command also displays HTTP proxy settings, but
does not show whether the proxy server is enabled or disabled. The show fenet
command output includes or excludes "disabled" to indicate the status.
Example
The following example configures an HTTP proxy server with basic authentication
credentials.
hostname (config) # fenet proxy host 192.168.2.3
hostname (config) # fenet proxy auth basic user bsmith
hostname (config) # fenet proxy auth basic password abcd6789
hostname (config) # fenet proxy enable
hostname (config) # show fenet
DTI CLIENT CONFIGURATION:
...
Http proxy
: bsmith@192.168.2.3:8080 (user agent:)
...
hostname (config) # show fenet status
...
HTTP Proxy:
Address
Username
User-agent
...
: 192.168.2.3:8080
: bsmith
:
Disabling HTTP Proxy Server Settings Using the CLI
Use the commands in this section to disable an HTTP proxy server or to remove its
configuration settings.
To disable an HTTP proxy server or remove its configuration settings:
l
To disable an HTTP server:
hostname (config) # no fenet proxy enable
l
To remove the HTTP proxy server:
hostname (config) # no fenet proxy
l
To remove the basic authentication user:
hostname (config) # no fenet proxy auth basic user
© 2022 FireEye Security Holdings US LLC
187
Central Management System Administration Guide
l
CHAPTER 12: Network Administration
To remove the basic authentication password:
hostname (config) # no fenet proxy auth basic password
l
To remove the user-agent string:
hostname (config) # no fenet proxy user-agent
Example
The following example disables an HTTP proxy server.
hostname (config) # no fenet proxy enable
hostname (config) # show fenet
DTI CLIENT CONFIGURATION:
...
Http proxy
: bsmith@192.168.2.3:8080 (user agent:) Disabled
...
Defining Another Management Interface
The management interface is used for remote access to the Web UI and CLI, and for other
management traffic (such as NTP, SNMP, and syslog). The default management interface
is ether1. You can define a different interface (such as ether2) for remote access to the Web
UI and CLI. Reasons for doing so include:
l
l
A private IP address is defined for ether1, so remote users cannot reach it. You
could use ether1 for the connection between a Central Management appliance and
its managed appliances, and define an accessible IP address for the ether2 interface.
You want to use one network for Web UI and CLI traffic, and another network for
other management traffic.
By default, listen interface constraints are enabled on the appliance. This means only
interfaces that meet the following criteria can accept HTTP/HTTPS requests (for Web UI
access) and SSH connections (for CLI access).
l
l
The interface must be in the listen interface list. By default, only ether1 is in this list.
The interface must meet the eligibility requirements listed in Prerequisites on the
facing page.
The system prevents remote users from being locked out of the system when the criteria are
not met by at least one interface. If no interface meets the criteria, listen interface
constraints are not enforced, and all viable interfaces are open and can accept
HTTP/HTTPS requests and SSH connections.
Examples
188
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Defining Another Management Interface
The appliance uses the default configuration (listen interface constraints are enabled
and ether1 is in the listen interface list). You configure a static IPv4 or IPv6 address
for the ether1 and ether2 interfaces and bring them up. Remote users do not have
access to the system over ether2, because it was not added to the listen interface list.
You then shut down the ether1 interface, and ether2 (the only viable interface)
immediately becomes accessible, because the listen interface constraints are no
longer enforced.
You add ether2 to the listen interface list, but both ether1 and ether2 use DHCP to
obtain IPv4 addresses or DHCPv6 to obtain IPv6 addresses. Because neither
interface meets the IPv4 or IPv6 static IP address requirement listed in Prerequisites
below, the listen interface constraints are no longer enforced. All viable interfaces,
including ether1 and ether2, become accessible.
Prerequisites
l
Operator or Admin access.
l
The appropriate management port is connected to the network switch or router.
l
Eligibility requirements:
l
l
l
The interface exists and is running.
DHCP and zeroconf are disabled on the interface (for IPv4), or IPv6 is
enabled on both the interface and the system (for IPv6).
The interface has an IPv4 or IPv6 address:
l
l
IPv4: At least one static nonzero IPv4 address is available to be
assigned to the interface.
IPv6: A static IPv6 address is available to assign to the interface, or the
address can be obtained dynamically through Stateless Address
Autoconfiguration (SLAAC) or DHCPv6.
Defining Another Management Interface Using the CLI
Use the commands in this section on an appliance that enforces listen interface constraints
to define a management interface other than ether1, and add it to the listen interface list so
it can accept HTTP/HTTPS requests and SSH connections.
To define another management interface:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
189
Central Management System Administration Guide
CHAPTER 12: Network Administration
2. Assign an IP address to the other interface:
hostname (config) # interface <interfaceName> ip address <ipAddress>
<mask>
where:
l
<ipAddress> is the IPv4 or IPv6 address of the interface.
l
<mask> is the IPv4 mask length prefixed by a slash (for example, /24) or an
IPv4 netmask (for example, 255.255.255.0), or the IPv6 mask length
prefixed by a slash (for example, /48).
3. (For IP routing) Set the static route for the interface:
hostname (config) # ip route <networkPrefix> <mask> <gatewayIP>
<interfaceName>
where:
l
<networkPrefix> is the IPv4 or IPv6 network prefix specifying the network.
l
<mask> is the IPv4 mask length prefixed by a slash (for example, /24) or a
netmask (for example, 255.255.255.0), or the IPv6 mask length preceded by
a slash (for example, /48).
l
<gatewayIP> is the IPv4 or IPv6 address of the gateway or next-hop device.
l
<interfaceName> is the name of the management interface.
4. (For Web UI access): Add the interface to the listen interface list for HTTP/HTTPS
requests:
hostname (config) # web server listen interface <interfaceName>
5. (For CLI access): Add the interface to the listen interface list for SSH connections:
hostname (config) # ssh server listen interface <interfaceName>
6. Verify your changes:
hostname (config) # show web
hostname (config) # show ssh server
7. Save your changes:
hostname (config) # write memory
NOTE: This procedure assigns a static IPv4 or IPv6 address to the interface. SLAAC
or DHCPv6 can instead automatically assign the IPv6 address.
Example
The following example configures ether2 as the management interface on the acme-1
appliance. It then adds ether2 the listen interface list.
acme-1 (config) # interface ether2 ip address 10.1.2.3 /24
acme-1 (config) # web server listen interface ether2
190
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
DTI Traffic and Management Traffic
acme-1 (config) # ssh server listen interface ether2
acme-1 (config) # show web
Web User Interface server:
Web interface enabled:
yes
HTTP enabled:
yes
HTTP port:
80
HTTP redirect to HTTPS:
yes
HTTPS enabled:
yes
HTTPS port:
443
HTTPS protocols:
TLSv1
HTTPS minimum protocol version: TLSv1
HTTPS cipher list:
compatible
HTTPS certificate name:
system-self-signed
HTTPS CA chain name:
Listen enabled: yes
Listen Interfaces:
Interface: ether1
Interface: ether2
Interface: lo
...
acme-1 (config) # show ssh server
SSH server configuration:
SSH server enabled:
yes
Minimum protocol version:
2
TCP forwarding enabled:
yes
X11 forwarding enabled:
no
Audit log file transfers: yes
Cipher list:
compatible
Minimum key length:
1024 bits
Client Alive Interval:
0
Client Alive Count Max
3
SSH server ports:
22
Interface listen enabled:
Listen Interfaces:
Interface: ether1
Interface: ether2
...
yes
IMPORTANT: Listen interface constraints are enabled on the system by default.
However, if the Listen enabled line in the show web command output is no, use
the web server listen enable command to enable constraints for HTTP/HTTPS
requests. If the Interface listen enabled line in the show ssh server
command output is no, use the ssh server listen enable command to enable
constraints for SSH connections.
DTI Traffic and Management Traffic
By default, both management and DTI traffic use the ether1 network interface, which needs
Internet access for DTI network downloads and uploads. For security, you might want to
isolate the management traffic by streaming it from an out-of-band network interface with
no Internet access.
© 2022 FireEye Security Holdings US LLC
191
Central Management System Administration Guide
CHAPTER 12: Network Administration
To split the DTI traffic from the ether1 interface, you need a dedicated network interface on
the Central Management appliance that is connected to the Internet, as shown in the
following illustration. The default gateway of the managed appliance must be reconfigured
to this interface. If the managed appliance and the Central Management appliance are in
different subnets, a static route must be configured to stream the management traffic from
the ether1 interface.
IMPORTANT! After traffic is split, accessing the management interface through the
Web UI or the CLI must be done from clients in the same subnet as the management
interface.
192
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
DTI Traffic and Management Traffic
Prerequisites
l
l
Admin access
Dedicated port for Internet access. For example, in a standard Central Management
deployment, the ether2, ether3, and ether4 ports are unused and can be used for this
purpose. (On some appliances, ports are labeled pether). For details, see the Central
ManagementHardware Administration Guide for your Central Management model.
Splitting DTI and Management Traffic Using the CLI
Use the commands in this section to split DTI and management traffic. The following
topologies are supported:
l
l
Central Management Appliance and Managed Appliance in Same Subnet below
Central Management Appliance and Managed Appliance in Different Subnets on
the next page
Central Management Appliance and Managed Appliance in
Same Subnet
To configure split traffic when the devices are in the same subnet:
1. Go to CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
2. Enable the interface that should have Internet access for DTI traffic:
cm-hostname (config) # no interface <interface> shutdown
where <interface> is the name of the interface (for example, ether4).
3. Configure the interface for DTI traffic:
cm-hostname (config) # interface <interface> ip address
<ipAddress> <mask>
where <interface> is the interface name, <ipAddress> is the interface IP address,
and <mask> is the network mask. The network mask can be specified in a dotted
decimal format (such as 255.255.255.0) or in a mask length format (such as /24).
4. Remove the existing default gateway route:
cm-hostname (config) # no ip default-gateway
5. Configure the default gateway to the interface for DTI traffic:
cm-hostname (config) # ip default-gateway <ipAddress> <interface>
where <ipAddress> is the IP address and <interface> is the name of the interface
for DTI traffic.
© 2022 FireEye Security Holdings US LLC
193
Central Management System Administration Guide
CHAPTER 12: Network Administration
6. Verify the default gateway configuration:
cm-hostname (config) # show ip default-gateway
7. Verify the IP route:
cm-hostname (config) # show ip route
8. Save your changes:
cm-hostname (config) # write memory
Example
In this example, the current settings are shown, DTI traffic is configured to go through the
ether4 interface, and the configuration is verified.
cm-hostname (config) # show ip default-gateway
Active default gateways:
172.16.1.1 (interface: ether1)
cm-hostname (config) # show ip route
Destination
Mask
Gateway
default
0.0.0.0
172.16.1.1
172.16.0.0
255.240.0.0
0.0.0.0
Interface
ether1
ether1
Source
static
interface
cm-hostname (config) # no interface ether4 shutdown
cm-hostname (config) # interface ether4 ip address 10.13.66.12 255.255.255.0
cm-hostname (config) # no ip default-gateway
cm-hostname (config) # ip default-gateway 10.13.66.1 ether4
cm-hostname (config) # show ip default-gateway
Active default gateways:
10.13.66.1 (interface: ether4)
cm-hostname (config) # show ip route
Destination
Mask
Gateway
default
0.0.0.0
10.13.66.1
10.13.66.1
255.255.255.0
0.0.0.0
172.16.0.0
255.240.0.0
0.0.0.0
Interface
ether4
ether4
ether1
Source
static
interface
interface
Central Management Appliance and Managed Appliance in
Different Subnets
When the Central Management appliance and the managed appliance are in different
subnets, there is an additional step to configure a static route for the managed appliance to
connect to the Central Management appliance.
To configure split traffic when the devices are in different subnets:
1. Go to CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
2. Enable the interface that should have Internet access for DTI traffic:
cm-hostname (config) # no interface <interface> shutdown
where <interface> is the name of the interface (for example, ether4).
194
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
DTI Traffic and Management Traffic
3. Configure the IP address and netmask of the interface for DTI traffic:
cm-hostname (config) # interface <interface> ip address
<ipAddress> <mask>
where <interface> is the name of the interface, <ipAddress> is the IP address of
that interface, and <mask> is the network mask. The network mask can be specified
in a dotted decimal format (such as 255.255.255.0) or in a mask length format (such
as /24).
4. Remove the static default gateway:
cm-hostname (config) # no ip default-gateway
5. Reconfigure the default gateway to the interface for DTI traffic:
cm-hostname (config) # ip default-gateway <ipAddress> <mask>
where <ipAddress> is the IP address and <interface> is the name of the interface
for DTI traffic.
6. Add a static route for the Central Management platform to send management traffic
to the managed appliance over the ether1 interface:
cm-hostname (config) # ip route <ipAddress> <mask> ether1
where <ipAddress> is an IP address in the same subnet as the managed appliance
and <mask> is the network mask.
7. Verify the default gateway configuration:
cm-hostname (config) # show ip default-gateway
8. Verify the IP route:
cm-hostname (config) # show ip route
9. Save your changes:
cm-hostname (config) # write memory
Example
In this example, the current settings are shown, DTI traffic is configured to go through the
ether4 interface, a new static route is configured for management traffic, and then the
configuration is verified.
cm-hostname (config) # show ip default-gateway
Active default gateways:
172.16.1.1 (interface: ether1)
cm-hostname (config) # show ip route
Destination
Mask
Gateway
default
0.0.0.0
172.16.1.1
172.16.0.0
255.240.0.0
0.0.0.0
Interface
ether1
ether1
Source
static
interface
cm-hostname (config) # no interface ether4 shutdown
cm-hostname (config) # interface ether4 ip address 10.13.66.12 255.255.255.0
cm-hostname (config) # no ip default-gateway
cm-hostname (config) # ip default-gateway 10.13.66.1 ether4
cm-hostname (config) # ip route 172.17.74.0 255.255.255.0 ether1
© 2022 FireEye Security Holdings US LLC
195
Central Management System Administration Guide
cm-hostname (config) # show ip default-gateway
Active default gateways:
10.13.66.1 (interface: ether4)
cm-hostname (config) # show ip route
Destination
Mask
Gateway
default
0.0.0.0
10.13.66.1
10.13.66.1
255.255.255.0
0.0.0.0
172.16.0.0
255.240.0.0
0.0.0.0
172.17.74.0
255.255.255.0
0.0.0.0
196
CHAPTER 12: Network Administration
Interface
ether4
ether4
ether1
ether1
Source
static
interface
interface
static
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Before You Begin the Upgrade
CHAPTER 13: Upgrading the
FireEye Software
The CM appliance automatically checks for new system images and guest images
versions. Updates are made on an ongoing basis and are easy to download and install.
For an appliance that is managed by the Central Management appliance, software updates
should be performed entirely from the Central Management Web UI. For more information,
see the Central Management Administration Guide.
This section describes how to update the Central Management system image. For
information about updating managed appliances from the Central Management appliance,
see Updating Managed Appliances on page 495.
NOTES:
l
l
l
Refer to the FireEye DTI Offline Update Portal Guide for upgrade instructions if
your server is offline and cannot download updates from the DTI network.
Upgrade times vary, based on the operating environment at your site and the
size of the server database.
Do not reboot your server during an upgrade, unless prompted to do so.
Before You Begin the Upgrade
Review the items in this section before you begin your upgrade.
l
l
User Role—You must have admin access to upgrade the CM appliance.
Back Up the Appliance—Before performing the upgrade, back up your appliance.
See Database Backup and Restore on page 233 for more information.
© 2022 FireEye Security Holdings US LLC
197
Central Management System Administration Guide
l
CHAPTER 13: Upgrading the FireEye Software
Licenses—Before performing upgrades, confirm that the following licenses are
installed and valid:
l
CONTENT_UPDATES license (needed for security content updates)
l
FIREEYE_SUPPORT license (needed for software updates)
NOTE: See License Keys on page 91 for more information. If you need to
obtain the licenses, send an email to key_request@fireeye.com.
l
l
l
End-User License Agreement (EULA)—The upgrade could require acceptance of the
End User License Agreement (EULA). If it is required, the appliance will not
function until the EULA is accepted. To review the EULA before the upgrade,
download a copy from the Trellix Customer Support Portal at
http://csportal.fireeye.com.
Minimum Version to Upgrade—Refer to the Release Notes to determine whether you
can upgrade directly from the current release to the new release.
IPMI and BIOS Versions—The latest IPMI and BIOS firmware should be running.
See IPMI and BIOS Firmware Updates on page 213.
NOTE: The CM 4500 model requires IPMI 3.11 and BIOS 1.9.
l
l
Download Time—Downloading the operating system software requires about 45
minutes when upgrading from the CLI. Downloading the guest images typically
requires 2 ½ to 9 hours from the CLI, depending on connection speed and whether
the full set of guest images is downloaded. A complete set can require 24 hours or
more.
Network Proxy Configuration—If you have an intelligent proxy appliance that is
required for access to the Internet, ensure that it does not perform secure sockets
layer (SSL) terminations with certificate replacement. An example of such a proxy is
the Blue Coat ProxySG appliance. If the proxy does perform SSL terminations, then
you must whitelist the Trellix Dynamic Threat Intelligence (DTI) network server
(staticcloud.fireeye.com), or the Content Distribution Network (CDN) server
(cloud.fireeye.com or download.fireeye.com) in the proxy configuration.
For integration with third-party products, such as ArcSight, Juniper STRM, Blue
Coat ProxySG, or Q1 Lab QRadar, contact Trellix Technical Support. Refer to the
vendor documentation for proxy configuration information.
Upgrading the Appliance Using the Web
UI
Use the Upgrade page to upgrade the CM appliance. To open the Upgrade page, click the
About tab and then click Upgrade.
198
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Upgrading the Appliance Using the Web UI
The following is an example of the Upgrade page for a standalone appliance.
The following is an example of the Upgrade page for an appliance that is managed by the
Central Management appliance.
The following is an example of the Update page for a Central Management appliance.
Task List for Upgrades
Perform the following steps (detailed in the sections that follow) to upgrade the CM
appliance.
NOTE: If your appliance is offline and cannot download updates from the DTI
network, perform Select an Upgrade Source below and then refer to the Trellix DTI
Offline Update Portal User Guide for additional instructions.
1. Select an Upgrade Source below.
2. Check for Available Update Software on the next page.
3. Download the Software on the next page.
4. Install the Software Update on page 201.
5. Upgrading the Appliance Using the Web UI on the previous page.
6. Validate the Software Updates on page 201.
Select an Upgrade Source
The upgrade source is the location from which the software updates will be downloaded.
© 2022 FireEye Security Holdings US LLC
199
Central Management System Administration Guide
CHAPTER 13: Upgrading the FireEye Software
Online Option
l
DTI—The software is downloaded from the Dynamic Threat Intelligence
(DTI) server or a Content Delivery Network (CDN) server. The server address is
displayed at the top right of the page. See Changing the Active Setting for a DTI
Service on page 109 for details about these options.
Offline Options
The following options can be used if your appliance cannot download updates from a
DTI source server. For details and upgrade instructions, see the Trellix DTI Offline Update
Portal User Guide.
l
l
Local—Upload a local file that was obtained from the Trellix DTI Update Portal for
offline appliances. Click Local to specify a path to the locally stored update software,
and then click Save.
URL—Upload a local file that was obtained from Trellix via the DTI Update Portal
for offline appliances and hosted on a local site identified by a URL. Click URL to
specify a URL to the update software, and then click Save.
NOTE: For offline guest image updates, downloads are more efficient if Source is
set to URL, not Local.
If neither offline option is feasible, contact FireEye Technical Support.
Check for Available Update Software
Click the action icon (
) in the Action column, and then click Check for a resource row
to determine if update software is available.
The status is displayed in the expanded Status area.
NOTE: If the Check option does not appear in the Action column, then the software
is already available for download or an update has recently taken place. The Check
option also does not appear during software downloads.
Download the Software
If a software update is available for a software image, guest image, or security content
update, the Download option in the Action column is displayed.If a software update is
available, the Download option in the Action column is displayed.
Click the action icon (
) in the Action column, and then click Download to begin the
software download.
The download status is displayed in the expanded Status area.
200
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Upgrading the Appliance Using the CLI
Install the Software Update
Installation status is displayed in the expanded Status area. After you download a
software update, click the action icon (
) in the Action column, and then click Install to
install it.
Installation status is displayed in the expanded Status area. If prompted, read the End
User License Agreement (EULA), and then accept it if you agree to its terms. If you do not
accept it, the appliance will not function.
NOTE: If an upgrade process is interrupted or fails, the appliance software
automatically falls back to the currently installed image.
When installation of the software image is complete, click the action icon (
) in the
Action column, and then click Reboot to complete the update process.
NOTE: You must access the appliance through the serial port if you want to
monitor appliance boot activities. You can enter CLI commands through direct
keyboard and monitor connection only before the boot loader begins loading the
kernel, for example, to post output, and after the boot is completed.
Validate the Software Updates
After software updates are installed, verify the installations:
l
l
l
Click the Settings tab, and then click Guest Images on the sidebar to verify and
view the installed guest images version.
Click the About tab. The current software image version information is displayed on
the FireEye CMS System Information page.
Click the Settings tab, and then click Appliance Licenses on the sidebar to verify
and view installed licenses. Click the Settings tab, and then click CMS Licenses on
the sidebar to verify and view installed licenses. Valid and active licenses display
the attribute “True.” If the licenses are not valid and active, the updates are not
functional.
Upgrading the Appliance Using the CLI
Use the commands in the following sections to upgrade the CM appliance.
Task List for Upgrades
Perform the following steps (detailed in the sections that follow) to upgrade the appliance.
© 2022 FireEye Security Holdings US LLC
201
Central Management System Administration Guide
CHAPTER 13: Upgrading the FireEye Software
1. Download and Install the Appliance Software Image below.
2. Restart the Appliance and Accept the EULA on the facing page.
3. Download Guest Images on the facing page.
4. Install Downloaded Guest Image Profiles on page 205.
5. Download and Install Guest Images in a Single Command on page 206.
6. Verify the Upgrade on page 206.
IMPORTANT: Be sure to download the software image and guest image files from
the configured DTI source server before beginning any installations.
Download and Install the Appliance Software Image
To download and install the software image:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Check for downloads:
hostname (config) # fenet image check
hostname (config) # show fenet image status
3. Download the software image:
hostname (config) # fenet image fetch
4. View the download progress:
hostname (config) # show fenet image status
Progress of latest action taken:
action fetch initiated
Tue Nov 22 13:04:44 2016
applying fetch for image
lms
fetching checksum of the requested image
done
fetching requested image 7.9.0
initiated
fetching requested image 7.9.0
done
action fetch completed
Tue Nov 22 13:06:03 2016
fetch-done: OS image downloaded successfully: image-lms_7.9.0.img
If you have already downloaded the latest software, you may see an error:
"Latest image already downloaded and ready to install (error)." To check
which images are downloaded, use the following command:
hostname (config) # show fenet image list
202
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Upgrading the Appliance Using the CLI
5. Install the downloaded software image:
hostname (config) # image install image-lms_7.9.0.img
hostname (config) # image boot next
NOTE: If an upgrade process is interrupted or fails, the appliance software
automatically falls back to the currently installed image.
6. Save your changes:
hostname (config) # write memory
Restart the Appliance and Accept the EULA
To restart the appliance and accept the EULA:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Restart the appliance:
hostname (config) # reload
3. After restarting the appliance, the system could display the Trellix End User License
Agreement (EULA). Read the EULA. Click Yes if you agree to its terms, and then
click Submit. If you do not accept the EULA, the appliance will not function.
After accepting the EULA, the login page is displayed. Wait a few minutes before
logging in because database records are undergoing an update in preparation for the
upgrade.
NOTE: You must access the appliance through the serial port if you want to
monitor appliance boot activities. You can enter CLI commands through
direct keyboard and monitor connection only before the boot loader begins
loading the kernel, for example, to post output, and after the boot is
completed.
Download Guest Images
Default guest images are automatically downloaded and installed from the DTI
source server. To download and install a guest image bundle or profile, you must
first use the guest-images configure command to select the guest image.
This procedure describes how to install default and non-default guest images.
© 2022 FireEye Security Holdings US LLC
203
Central Management System Administration Guide
CHAPTER 13: Upgrading the FireEye Software
To download guest images:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the guest images configured for the appliance:
hostname (config) # show guest-images config
3. Download the guest images, but do not install them yet. Downloading guest images
will take some time, so allow the download to run in the background.
hostname (config) # guest-images download
Wait for the appliance to fully download the guest images before beginning any
installations.
NOTE: You can perform automatic downloads of available guest images.
For details, see the fenet guest-images auto download and fenet
guest-images auto update commands in the CLI Command Reference.
4. Confirm the guest image downloads are completed:
hostname (config) # show guest-images download
To cancel a download in progress:
hostname (config) # guest-images download cancel
To resume a download that has been interrupted for any reason:
hostname (config) # guest-images download resume
5. To download non-default guest images by specifying the server manifest:
Perform this step if you do not need all available guest images.
a. Download the server manifest:
hostname (config) # guest-images download manifest [version
<version-id>
b. Display available guest image bundles:
hostname (config) # show guest-images available bundles
c. Note the bundle ID of the bundle of guest images that you want from the list
displayed (only one bundle can be selected).
d. Select the guest image bundle to be installed, where bundle_id is obtained
from the previous step:
hostname (config) # guest-images configure bundle <bundle-id>
e. Verify that the bundle is properly selected:
hostname (config) # show guest-images config
204
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Upgrading the Appliance Using the CLI
6. To update guest images with one or more profiles (mutually exclusive with default
and bundle sets):
a. Download the server manifest:
hostname (config) # guest-images download manifest [version <version-
id>]
b. Display available guest image profiles:
hostname (config) # show guest-images available profiles
c. Note the profile ID of the needed profile(s) from the list displayed.
d. Select the guest image profile to be installed:
hostname (config) # guest-images configure profile <profileID>
where <profileID> is the profile you noted in the previous step.
e. Repeat the previous step for each additional profile needed.
f. Verify that all needed profiles are configured:
hostname (config) # show guest-images configuration
g. Download the guest images:
hostname (config) # guest-images download
h. Monitor the download progress:
hostname (config) # show guest-images download
NOTE: If you encounter a problem with a download, the output of
the show guest-images download command will describe the
issues, including notification about the specific file that was
involved in the failure. Network connectivity issues cause download
failures. Repeat the download using the guest images download
command. The system will restart the download at the point at
which it was interrupted or failed. If the problem persists, contact
Trellix Technical Support.
7. Save your changes:
hostname (config) # write memory
Install Downloaded Guest Image Profiles
To download default guest images:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. After the download is complete, install the guest images:
hostname (config) # guest-images install
© 2022 FireEye Security Holdings US LLC
205
Central Management System Administration Guide
CHAPTER 13: Upgrading the FireEye Software
3. Verify that guest images are properly installed:
hostname (config) # show guest-images
4. Save your changes:
hostname (config) # write memory
Download and Install Guest Images in a Single Command
To download and install default guest images:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download and install guest images:
hostname (config) # guest-images download-and-install
NOTE: When the appliance is managed by a Central Management appliance,
the guest image download process is automated. The managed appliance is
scheduled to check for guest image updates daily and then trigger the Central
Management appliance to download the requested guest image update for
hosting. The managed appliance will automatically download and install the
updates after the Central Management appliance completes the download.
3. View the download status of the guest images:
hostname (config) # show guest-images download
To cancel a download in progress:
hostname (config) # guest-images download cancel
To resume a download that has been interrupted for any reason:
hostname (config) # guest-images download-and-install resume
4. Verify that the guest images are properly installed:
hostname (config) # show guest-images
Verify the Upgrade
To verify the upgrade:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Display the version information for the current system image:
hostname (config) # show version
206
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Auto-Mounting on a USB Device
3. Display all guest images:
hostname (config) # show guest-images
Configuring Auto-Mounting on a USB
Device
You can configure auto-mounting on a USB device attached to the CM appliance. Only one
USB device can be mounted at a time. You can configure HTTP access to install system
images, guest images, from the USB device onto the appliance.
NOTE: You can configure auto-mounting on a USB device only using the CLI.
Prerequisites
l
Admin access
Enabling or Disabling Auto-Mounting on a USB Device
Using the CLI
Use the commands in this topic to enable or disable auto-mounting on a USB device
attached to the CM appliance. You must enable auto-mounting when the USB device is
attached. By default, auto-mounting is disabled. Auto-mounting will not mount the USB
device when it is already attached to the appliance.
Prerequisites
l
Admin access
To enable auto-mounting on a USB device:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable auto-mounting on a USB device attached to the appliance:
hostname (config) # media usb auto-mount enable
3. Plug the USB device in to the appliance immediately.
4. Verify the USB device auto-mount configuration.
hostname (config) # show media usb
© 2022 FireEye Security Holdings US LLC
207
Central Management System Administration Guide
CHAPTER 13: Upgrading the FireEye Software
USB auto-mount configuration:
Enabled:
yes
Local web access:
yes
Top-level directory: fireeye
To disable auto-mounting on the USB device:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable auto-mounting on the USB device:
hostname (config) # no media usb auto-mount enable
3. Verify the USB device auto-mount configuration.
hostname (config) # show media usb
USB auto-mount configuration:
Enabled:
no
Local web access:
yes
Top-level directory: fireeye
Configuring HTTP Access to Install Software Updates
Using the CLI
Use the commands in this topic to configure HTTP access to install software updates from
a USB device onto the appliance. By default, you can access only the contents locally in the
fireeye directory for the first partition from a specified URL.
NOTE: The Central Management appliance does not host guest images when it is
operating in "inline" mode.
Prerequisites
l
l
Admin access
Enable auto-mounting on the USB device to the attached appliance. For details
about how to enable auto-mounting, see Enabling or Disabling Auto-Mounting on a
USB Device Using the CLI on the previous page.
To configure HTTP access to install software updates from a USB device:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
208
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Auto-Mounting on a USB Device
2. Enable HTTP access on the loopback interface on the appliance:
hostname (config) # media usb web-access enable local
Local web access is enabled by default.
3. Specify the top-level directory as the location to extract software updates on a USB
device:
hostname (config) # media usb web-access top-dir fireeye
This directory will be used as the URL to extract the software on the USB device. For
example, if you specified the install directory as fireeye/gi-13.0701, the URL for
the installation is http://localhost/media/usb1/fireeye/gi-13.0701.
4. Verify that the USB device is mounted:
hostname (config) # show media usb
USB auto-mount configuration:
Enabled:
yes
Local web access:
yes
Top-level directory: fireeye
USB auto-mount status:
Device mounted:
yes
Access URL:
N/A
5. Download software updates using the specified URL as the location to install the
updates. See Installing Guest Images from a USB Device Using the CLI below for a
representative procedure.
Installing Guest Images from a USB Device Using the CLI
Use the commands in this topic to install guest images from a USB device onto the
appliance. By default, you can access only the contents locally in the fireeye directory for
the first partition from a specified URL.
NOTE: The Central Management appliance does not host guest images when it is
operating in "inline" mode.
Prerequisites
l
l
Admin access
Enable auto-mounting on the USB device to the attached appliance. For details
about how to enable auto-mounting, see Enabling or Disabling Auto-Mounting on a
USB Device Using the CLI on page 207.
© 2022 FireEye Security Holdings US LLC
209
Central Management System Administration Guide
l
l
CHAPTER 13: Upgrading the FireEye Software
Configure HTTP access. For details, see Configuring HTTP Access to Install Software
Updates Using the CLI on page 208.
Complete the steps in the following order to set up the files correctly to install guest
images from a USB device:
1. Download the guest images tar file from the Trellix network.
2. Extract the contents on the USB device.
3. Remove the version numbers. Copy the following file names:
l
server-manifest.VERSION to server-manifest
l
server-manifest.VERSION.md5 to server-manifest.md5
l
server-manifest.VERSION.v2 to server-manifest.v2
l
server-manifest.VERSION.v2.md5 to server-manifest.v2.md5
To download guest images from a USB device:
1. Download guest images using the specified URL as the location to install the guest
images:
hostname (config) # guest-images download url <URL>
where URL is the location that you specified as the top-level directory for the
installation.
Wait for the appliance to fully download the guest images before beginning any
installations.
2. Verify the download progress:
hostname (config) # show guest-images download
3. After the download is complete, install the guest images:
hostname (config) # guest-images install
4. Verify that guest images are properly installed:
hostname (config) # show guest-images
Mounting or Unmounting a USB Device Using the CLI
Use the commands in this topic to manually mount or unmount a USB device to the
attached appliance. Trellix recommends that you physically remove the USB device from
the port. Use the media usb mount command before you attach the drive, and use the
media usb eject command after you unplug it.
NOTE: The media usb eject command will have no effect if the USB device is not
mounted.
210
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Auto-Mounting on a USB Device
Prerequisites
l
Admin access
To mount a USB device:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Mount the USB device to the attached appliance:
hostname (config) # media usb mount
To unmount a USB device:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Unmount the USB device from the attached appliance:
hostname (config) # media usb eject
© 2022 FireEye Security Holdings US LLC
211
Central Management System Administration Guide
212
CHAPTER 13: Upgrading the FireEye Software
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 14: IPMI and BIOS
Firmware Updates
New Intelligent Platform Management Interface (IPMI) firmware and BIOS firmware is
packaged with the appliance software image, but are not automatically installed when you
upgrade to a new appliance release. It is important to update the firmware to ensure that
you are using the latest, most secure version. BIOS firmware updates are associated with
IPMI updates, and they should both be updated. IPMI firmware must be updated first.
By default, if the IPMI interface has been configured with an IP address, you are notified
when a newer version is available. The notice is displayed when you log in to the CLI and
when you view the IPMI card in the About > Summary page in the Web UI. If you prefer,
you can disable the notification from appearing again. For details, see Enabling and
Disabling IPMI Firmware Notifications Using the CLI on page 215.
You can use the show ipmi version include-firmware-update-notice command to
view the notice, even if your IPMI firmware is up-to-date.
Note the following:
l
l
l
l
The IPMI Web UI will be unavailable during the IPMI firmware update.
The IPMI firmware type is specific to the appliance model, so it is possible that not
all models will get an IPMI firmware update in the same CM software release.
IPMI and BIOS firmware pertain to hardware, so updates are required for physical
appliances only. The commands described in this section are not available in the
CLI of a virtual appliance.
Not all appliance models support IPMI and BIOS firmware updates.
IMPORTANT! Updating the IPMI firmware reverts all settings to factory defaults,
including the IPMI username and password, network configuration, and event logs.
Before starting the update, gather all information you will need to reconfigure IPMI.
Prerequisites
l
Admin access
© 2022 FireEye Security Holdings US LLC
213
Central Management System Administration Guide
CHAPTER 14: IPMI and BIOS Firmware Updates
Updating IPMI and BIOS Firmware
This procedure describes how to use CLI commands to update IPMI and BIOS firmware on
the CM appliance.
NOTE: The CM 4500 model requires an update to IPMI 3.11 and BIOS 1.9. You
must update the IPMI before you update the BIOS.
Updating IPMI Firmware
To update the IPMI firmware:
CAUTION: IPMI network and password settings revert to factory defaults after
this upgrade, and IPMI logs are deleted. Make a note of your settings and back up
your IPMI logs.
WARNING: Do not shut down or remove power from the appliance during the
update.
1. Go to CLI configuration mode.
hostname> enable
hostname# configure terminal
2. Check the version installed on the appliance:
hostname (config) # show ipmi
3. Begin the update:
hostname (config)# ipmi firmware update latest
4. Confirm the update:
hostname (config)# show ipmi
If the update fails, try the steps again.
If IPMI functions are not fully restored, perform a full power cycle (cold shutdown) on the
appliance:
1. Stop the reload process:
hostname (config)# reload halt
2. Disconnect all power cables for two minutes.
3. After two minutes, reconnect power cables and restart the appliance.
214
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling and Disabling IPMI Firmware Notifications Using the CLI
Updating BIOS Firmware
IMPORTANT: Make sure the IPMI firmware is updated before you perform this
procedure.
To update the BIOS firmware:
1. Go to CLI configuration mode.
hostname> enable
hostname# configure terminal
2. Check the installed version:
hostname (config) # show system bios
3. Begin the update:
hostname (config)# system bios firmware update latest
WARNING: Do not shut down or remove power from the appliance
during the update.
4. Confirm the update:
hostname (config)# show system bios
5. Stop the reload process:
hostname (config)# reload halt
6. Disconnect all power cables for two minutes.
7. After two minutes, reconnect power cables and restart the appliance.
Enabling and Disabling IPMI Firmware
Notifications Using the CLI
This procedure describes how to use CLI commands to disable and re-enable notifications
about out-of-date IPMI firmware on the CM appliance. This notification is enabled by
default.
To disable notifications about out-of-date firmware:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable notifications:
hostname (config) # no ipmi firmware update notice enable
© 2022 FireEye Security Holdings US LLC
215
Central Management System Administration Guide
CHAPTER 14: IPMI and BIOS Firmware Updates
3. Save your changes.
hostname (config) # write memory
To re-enable notifications about out-of-date firmware:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable notifications:
hostname (config) # ipmi firmware update notice enable
3. Save your changes.
hostname (config) # write memory
216
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Managing Logs Using the Web UI
CHAPTER 15: Log Management
This section covers the following information:
l
Managing Logs Using the Web UI below
l
Viewing the Current Log Configuration on page 220
l
Configuring a Syslog Server Using the CLI on page 221
l
l
l
Configuring the Minimum Severity of Messages Sent to Syslog Servers Using the
CLI on page 222
Configuring the Minimum Severity of Messages Stored on the Local Drive Using the
CLI on page 224
Excluding System Internal Audit Messages from the Audit Log File Using the CLI
on page 226
l
Configuring Log Rotation for Specific Types of Log Files on page 227
l
Viewing Log Rotation Configuration Using the CLI on page 227
l
Configuring the Timestamp Format Using the CLI on page 229
l
Uploading the Active Log File to a Network Location Using the CLI on page 231
For a full list and for details about command usage and parameters, see the CLI Command
Reference.
NOTE: You may need to download logs and provide them to Trellix Technical
Support for troubleshooting.
Managing Logs Using the Web UI
Use the About > Log Manager page to manage appliance logs. This page allows you to
customize log generation for various time periods.
© 2022 FireEye Security Holdings US LLC
217
Central Management System Administration Guide
CHAPTER 15: Log Management
NOTE: You may need to download logs and provide them to Trellix Technical
Support for troubleshooting. You may also be asked to upload the logs to Trellix.
To manage logs:
1. Click the About tab.
2. Click Log Manager.
3. Select which log categories to include by clicking Selected Logs or All logs and
outputs.
4. Select or clear checkboxes to specify the categories you want to include in the logs.
5. If a drop-down list is present, select the time period the log should cover. The
default is today. The other options are past week, past 2 weeks, and past month.
6. If you want to view the log files you download, clear the Password-protect
generated log archive checkbox in the Password area.
IMPORTANT: If this checkbox is selected, you will be unable to open the
files.
7. Click Create. The log is added to the Log Archives area.
8. To download a log, click the action icon (
) in the Action column and then click
Download.
The log archive is downloaded to your local file system. The archive name begins
with the hostname of the appliance.
9. To delete an archive, click the action icon (
) in the Action column and then
click Delete.
218
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Managing Logs Using the Web UI
10. If Trellix requests that you upload an archive, click the action icon (
) in the
Action column and then click Upload. The file is automatically uploaded to Trellix.
© 2022 FireEye Security Holdings US LLC
219
Central Management System Administration Guide
CHAPTER 15: Log Management
Viewing the Current Log Configuration
This topic describes how to use CLI commands to view the current log configuration on
the CM appliance. For a full list of logging commands and the usage and parameters, see
the CLI Command Reference.
Prerequisites
l
Admin access
To view the current log configuration:
1. Go to CLI enable mode:
hostname > enable
2. View the current logging configuration:
hostname # show logging
Local logging level:
Override for class mgmt-back:
Override for class mgmt-front:
220
notice
notice
notice
Remote syslog default level:
No remote syslog servers configured.
notice
Receive remote messages via UDP:
no
Receive remote messages via TCP:
no
Receive remote messages via TLS:
no
Log file rotation:
Log rotation size threshold:
Archived log files to keep:
256 megabytes
40
Log format:
Timestamp format:
Subsecond timestamp field:
rfc-3164
disabled
Secure channel logs:
yes
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring a Syslog Server Using the CLI
Configuring a Syslog Server Using the CLI
This topic describes how to use CLI commands to specify a syslog server for log messages
on the CM appliance. For a full list of logging commands and the usage and parameters,
see the CLI Command Reference.
Prerequisites
l
Admin access
To specify a syslog server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To specify a syslog server to which logging messages are sent, use the
logging <serverAddress> command, where <serverAddress> is the server IP
address. For example:
hostname (config) # logging 10.10.20.62
3. Verify your changes:
hostname (config) # show logging
Local logging level:
Override for class mgmt-back:
Override for class mgmt-front:
Remote syslog default level:
Remote syslog servers:
10.10.20.62
protocol:
port:
[ . . . ]
notice
notice
notice
notice
notice
udp
514
4. Save your changes.
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
221
Central Management System Administration Guide
CHAPTER 15: Log Management
Configuring the Minimum Severity of
Messages Sent to Syslog Servers Using
the CLI
This topic describes how to use CLI commands to specify the minimum severity level of
log messages sent to syslog servers. For a full list of logging commands and the usage and
parameters, see the CLI Command Reference.
Prerequisites
l
Admin access
To configure the minimum severity of log messages sent to syslog servers:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To specify the minimum severity level of messages sent to syslog servers, use the
logging trap <severity> command, where <severity> is one of the following:
l
none—Disables logging.
l
emerg—System failure.
l
alert—Immediate action required.
l
crit—Critical condition.
l
err—Error condition.
l
warning—Warning condition.
l
notice—Normal but significant condition.
l
info—Informational message.
l
debug—Debug-level message.
The following example specifies that all log messages of error level or higher
severity are sent to the syslog server:
hostname (config) # logging trap err
222
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring the Minimum Severity of Messages Sent to Syslog Servers Using the CLI
3. Verify your changes:
hostname (config) # show logging
Local logging level:
Override for class mgmt-back:
Override for class mgmt-front:
Remote syslog default level:
Remote syslog servers:
10.10.20.62err
protocol:
port:
[ . . . ]
notice
notice
notice
err
udp
514
4. Save your changes.
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
223
Central Management System Administration Guide
CHAPTER 15: Log Management
Configuring the Minimum Severity of
Messages Stored on the Local Drive
Using the CLI
This topic describes how to use CLI commands to specify the minimum severity level of
log messages stored on the local drive. For a full list of logging commands and the usage
and parameters, see the CLI Command Reference.
Prerequisites
l
Admin access
To configure the minimum severity of log messages stored on the local drive:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To specify the minimum severity level of messages stored on the local disk, use the
logging local <severity> command, where <severity> is one of the following:
l
none—Disables logging.
l
emerg—System failure.
l
alert—Immediate action required.
l
crit—Critical condition.
l
err—Error condition.
l
warning—Warning condition.
l
notice—Normal but significant condition.
l
info—Informational message.
l
debug—Debug-level message.
l
override—Override a log level.
The following example specifies that all log messages of "error" level or higher
severity are saved in the log files on the local disk:
hostname (config) # logging local err
224
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring the Minimum Severity of Messages Stored on the Local Drive Using the CLI
3. Verify your changes:
hostname (config) # show logging
Local logging level:
Override for class mgmt-back:
Override for class mgmt-front:
err
notice
notice
4. Save your changes.
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
225
Central Management System Administration Guide
CHAPTER 15: Log Management
Excluding System Internal Audit
Messages from the Audit Log File Using
the CLI
This topic describes how to filter out system internal audit messages from the audit log file
on the CM appliance. For a full list of logging commands and their usage and parameters,
see the CLI Command Reference.
Prerequisites
l
Admin access
To enable filtering out of internal audit messages:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable the filtering feature:
hostname (config) # logging files audit filter exclude-system-internal
enable
226
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Log Rotation for Specific Types of Log Files
Configuring Log Rotation for Specific
Types of Log Files
This topic describes how to enable and configure file-based log rotation for audit logs and
login history logs on the CM appliance. You can rotate these log files at a specified period
of time, when they reach a specified file size, or when they take up a specified percentage
of disk space. Configuring the criteria for individual file types overwrites the global
configuration. For a full list of logging commands and their usage and parameters, see the
CLI Command Reference.
Prerequisites
l
Admin access
To enable and configure file-based log rotation:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable the rotation feature for the specified file type:
hostname (config) # logging files rotation file-type {audit | loginhistory} criteria enable
3. Specify either the frequency or file size at which a new log is created:
hostname (config) # logging files rotation file-type {audit | loginhistory} criteria {frequency {daily | monthly | weekly | yearly} | size
<megabytes> | size-pct <percentage>}
Viewing Log Rotation Configuration
Using the CLI
This topic describes how to view file-based log rotation configuration for various types of
log files on the CM appliance. You can view the configuration details for the following file
types:
l
audit
l
eventd
l
events
© 2022 FireEye Security Holdings US LLC
227
Central Management System Administration Guide
l
fireeyedb
l
lms_production
l
login-history
l
perfmon
l
syslog
l
weblogs
l
all
CHAPTER 15: Log Management
For a full list of logging commands and their usage and parameters, see the CLI Command
Reference.
Prerequisites
l
Admin access
To view file-based log rotation configuration:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the file type and view the log rotation configuration:
hostname (config) # show logging-filewise <audit | eventd | events |
fireeyedb | lms_production | login-history | perfmon | syslog | weblogs
| all>
228
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring the Timestamp Format Using the CLI
Configuring the Timestamp Format Using
the CLI
This topic describes how to use CLI commands to specify the syslog timestamp format. For
a full list of logging commands and the usage and parameters, see the CLI Command
Reference.
Prerequisites
l
Admin access
To configure the timestamp format used in log messages:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enter the logging fields timestamp format <format> command, where
<format> is one of the following:
l
l
rfc-3164—Use the timestamp format specified in RFC-3164 (for example, May
13 15:12:01).
rfc-3339—Use the timestamp format specified in RFC-3339 (for example,
2017-05-15T15:22:33).
The following example specifies that all log messages use RFC-3339 format:
hostname (config) # logging fields timestamp format rfc-3339
© 2022 FireEye Security Holdings US LLC
229
Central Management System Administration Guide
CHAPTER 15: Log Management
3. Verify your changes:
hostname (config) # show logging
Local logging level:
err
Remote syslog default level:
notice
No remote syslog servers configured.
Receive remote messages via UDP:
no
Receive remote messages via TCP:
no
Receive remote messages via TLS:
no
Log file rotation:
Log rotation size threshold:
Archived log files to keep:
256 megabytes
40
Log format:
Timestamp format:
rfc-3339
Subsecond timestamp field:
Secure channel logs:
disabled
no
4. Save your changes.
hostname (config) # write memory
230
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Uploading the Active Log File to a Network Location Using the CLI
Uploading the Active Log File to a
Network Location Using the CLI
This topic describes how to use CLI commands to upload the active log file to a network
location. For a full list of logging commands and the usage and parameters, see the CLI
Command Reference.
Prerequisites
l
Admin access
To upload the active log file to a network location:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To upload the active log file to a specified network location using file transfer
protocol (FTP), trivial file transfer protocol (TFTP), secure copy (SCP) or SSH file
transfer protocol (SFTP), use the following command:
hostname (config) # logging files upload current <uploadURL>
The <uploadURL> parameter specifies the protocol and file location.
l
ftp://<domain>/<path>/<fileName>
l
tftp://<domain>/path>/<fileName>
l
scp://<username>[:<password>]@<hostname>/<path>/<fileName>
l
sftp://<domain>/<path>/<fileName>
NOTE: For the SCP protocol, you also specify the credentials. You can enter
the password in the command line, or you can enter it when you are
prompted at the CLI.
The following example uses SCP to upload the active log file to logs/FE_log.gz:
hostname (config) # logging files upload current
scp://it123@example.com/logs/FireEye_log.gz
Password (if required): ***********
3. Verify your changes:
hostname (config) # show log files
4. Save your changes.
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
231
Central Management System Administration Guide
232
CHAPTER 15: Log Management
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Database Backup and Restore Introduction
CHAPTER 16: Database Backup
and Restore
This section describes how to back up and restore the appliance database and how to
manage backup files on the appliance. It includes the following topics:
l
Database Backup and Restore Introduction below
l
Task List for Database Backup and Restore on the next page
l
Viewing the Last Backup and Restore Results on the next page
l
Estimating the Space Needed for the Backup File on page 236
l
Backing Up the Database on page 237
l
Scheduling Automatic Backups on page 242
l
Downloading Backup Files on page 245
l
Uploading Backup Files on page 246
l
Restoring the Database from a Backup File on page 247
l
Deleting Previous Backup Files on page 251
Database Backup and Restore
Introduction
You can back up, restore, upload, download, and delete the configuration database, which
stores Central Management configuration settings. You can restore a database from a
previous backup. Backup files can be deleted to free space for new backups.
NOTE: License keys and guest images (applicable to offline Central Management
appliances only) are not included in the backup. You must reinstall the license keys
and guest images separately. Network settings can be restored.
© 2022 FireEye Security Holdings US LLC
233
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
Task List for Database Backup and
Restore
Complete the steps for backing up and restoring the database in the following order:
1. Log in to the Web UI or CLI.
2. Verify the status of the last backup and restore operations. For details about how to
view the last backup and restore operations, see Viewing the Last Backup and
Restore Results below.
3. the config backup file. For details about how to estimate the space needed, see
Estimating the Space Needed for the Backup File on page 236.
4. Specify a config backup profile and a location for the backup file. Decide whether to
include public and private key encryption. Start the backup. For details about how
to specify a backup profile, include encryption, and start or cancel the backup, see
Backing Up the Database on page 237.
To schedule how often you want the backup job to automatically run, see
Scheduling Automatic Backups on page 242.
5. To restore the database, select the backup file. For details about how to restore the
database, see Restoring the Database from a Backup File on page 247.
6. Monitor the status of the backup or restore operation.
Viewing the Last Backup and Restore
Results
You can view the details for the last backup and restore operations. Details of the last
backup or restore operation include the following:
l
Status of the backup or restore (such as "running")
l
Destination of the backup file or source of the restore file
l
Start time of the backup or restore operation
l
End time of the backup or restore operation
l
Result of the backup or restore operation (such as "success")
After a backup or restore operation, the appliance marks the result as "success" or "failure."
When a backup or restore operation is in process, the appliance displays the status as
"running."
234
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing the Last Backup and Restore Results
Prerequisites
l
Admin access
Viewing the Last Backup and Restore Results Using the
Web UI
The Backup and Restore page displays the status details about the last backup and restore
operation. Example status details are shown in the following illustration.
Viewing the Last Backup and Restore Status Using the
CLI
Use the commands in this section to view the status for the last backup and restore
operations.
To view the details of the last backup operation:
1. Go to CLI enable mode.
hostname > enable
2. View the details of the last backup operation. For example:
hostname # show backup status
Backup status:
Last backup profile:
Last backup destination:
Last backup start time:
Last backup end time:
Last Backup result:
not-running
config
local
2016/12/08 18:32:58.112
2016/12/08 18:34:26.301
success
To view the details of the last restore operation:
1. Go to CLI enable mode.
hostname > enable
© 2022 FireEye Security Holdings US LLC
235
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
2. View the details of the last restore operation. For example:
hostname # show restore status
Restore status:
Last restore profile:
Last restore source:
Last restore start time:
Last restore end time:
Last restore result:
not-running
config
usb
2016/12/08 21:13:53.151
2016/12/08 21:13:53.151
success
Estimating the Space Needed for the
Backup File
The appliance estimates the size of the backup file and calculates the amount of space it
needs. The available space must be greater than the estimated space required to perform
the backup operation. The size depends on the profile you select (described in Database
Backup and Restore Introduction on page 233).
Details of the backup estimates for the configuration database include the following:
l
Size estimate of the database file based on the backup profile
l
Available space based on the backup profile
l
Whether the backup can be performed
Prerequisites
l
l
Admin access to run the estimate
Monitor, Operator, or Admin access to view the backup estimate using the CLI. (In
the Web UI, these roles can view only existing backup files, not the backup
estimate.)
Estimating the Space Needed for the Backup File Using
the Web UI
Use the Backup and Restore page to estimate the space needed for the backup file.
To estimate the space needed for the backup file:
1. Click the Settings tab.
2. Click CM Backup & Restore on the sidebar.
3. Select the configuration backup file you want to estimate. (See Database Backup and
Restore Introduction on page 233 for descriptions.)
236
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Backing Up the Database
4. Click Estimate in the Estimate Backup column.
Details of the backup estimates for the configuration database are displayed.
Estimating the Space Needed for the Backup File Using
the CLI
Use the commands in this section to estimate the space needed for the backup file.
To estimate the space needed for the backup file:
1. Go to CLI enable mode.
hostname > enable
2. View the estimate for the configuration database:
hostname # show backup estimate profile config
Example
The following example shows the estimated available space for a backup of the
configuration database:
hostname # show backup estimate profile config
-----------------------------------------------# Estimates for config backup
-----------------------------------------------Local space available
: 599097 MB
Space reserved for other purposes
: 356220 MB
Space available for backups
: 242877 MB
Estimated space required for backup : 8 MB
Can perform local or remote backup
: yes
USB space available
: 12808 MB
Can perform USB backup
: yes
Backing Up the Database
You can save the backup file three ways:
l
l
l
To a local destination on the appliance
To a remote server (this first creates a local backup and then transfers it to the
remote server)
To a USB device connected to your local machine
© 2022 FireEye Security Holdings US LLC
237
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
Use the media usb mount command to mount the USB device to the
attached appliance. If the USB device is mounted, use the media usb eject
command to unmount the USB device. For details about how to mount or
unmount a USB device, see Mounting or Unmounting a USB Device Using
the CLI on page 210.
The appliance must have sufficient space to save one backup. You cannot proceed with a
backup operation if there is not enough space on the requested backup destination. For
information about estimating the amount of space, see Estimating the Space Needed for the
Backup File on page 236.
NOTE: The appliance is fully functional while the backup operation is in process.
Prerequisites
l
Admin access
Backing Up the Database Using the Web UI
Use the Backup and Restore page to back up the database.
To back up the database:
1. Click the Settings tab.
2. Click CM Backup & Restore on the sidebar.
238
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Backing Up the Database
3. Select the backup location from the drop-down list.
l
Local—Saves the backup file to a local destination on the appliance.
IMPORTANT: When the number of backup files on your appliance
reaches the backup file limit set for your appliance, you need to delete
old backups to continue performing local backups.
l
l
USB—Saves the backup file to a USB device connected to your local machine.
Remote—Saves the backup file to a remote server. This first creates a local
backup and then transfers it to the remote server.
4. If you selected Remote Server, enter the location of the remote backup file in the
Remote URL or Server Location column:
scp://<username>:<password>@<hostname>/<directory>
where <username> and <password> are remote server admin credentials,
<hostname> is the remote server, and <directory> is the directory in which to save
the backup file.
5. Enter a custom prefix for the backup file name in the File Name Prefix column.
You can use the prefix to sort the list of the backup files.
6. (Optional) Clear the Encrypt checkbox to disable public and private key encryption
for the backup operation. Each backup file is signed by default using the public and
private key pairs. By default, encryption is always included in the backup.
NOTE: Encryption delays the backup operation. Backups are encrypted
only using static keys.
7. Click Backup in the Action column.
A progress bar indicates the status of the backup operation.
NOTE: To cancel a database backup that is in progress, click the red X in
the progress bar.
Backing Up the Database Using the CLI
Use the commands in this section to back up the configuration database.
To back up the database:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Specify the configuration database for backup:
hostname (config) # backup profile config
© 2022 FireEye Security Holdings US LLC
239
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
3. Specify the location for the backup file.
l
To save the configuration backup file to a local destination on the Central
Management appliance:
hostname (config) # backup profile config to local
l
To save the backup file on a remote server:
hostname (config) # backup profile config to <url>
where <url> specifies remote server admin credentials (<username> and
<password>), the remote server( <hostname>), and the directory in which to
save the backup file (<directory> )in the following format:
scp://<username>[:<password>]@<hostname>/<directory>
NOTE: If you do not specify the remote host administrator password
in the backup profile command (where the password would be
visible as clear text), the CLI prompts for the password and obfuscates
the keyboard input as you type it.
A remote backup first creates a local backup and then transfers it to
the remote server.
l
To save the backup file to a USB drive on your local machine:
hostname (config) # backup profile config to usb
4. Specify a custom prefix for the backup file name:
hostname (config) # backup profile config to <backupLocation> prefix
<prefix>
5. (Optional) Monitor the progress of the backup operation.
l
To disable progress tracking for the backup operation:
hostname (config) # backup profile config to <backupLocation>
progress no-track
l
To enable progress tracking for the backup operation:
hostname (config) # backup profile config to <backupLocation>
progress track
By default, progress tracking is enabled.
240
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Backing Up the Database
6. (Optional) Disable public and private key encryption for the backup operation.
hostname (config) # backup profile config to <backupLocation> noencryption
The following example backs up the configuration database to a local destination on
the Central Management appliance without encryption:
hostname (config) # backup profile config to local no-encryption
NOTE: Encryption is enabled by default. Encryption delays the backup
operation. Backups are encrypted only using static keys.
NOTE: To cancel a backup that is in progress, enter the backup cancel
command. When you cancel the backup operation that is in progress, the system
finishes the current step before canceling the entire operation.
Examples
NOTE: The following examples are from a Virtual Execution appliance, but they are
representative of CM appliances as well.
The following example backs up the configuration database to a local destination on the
Central Management appliance:
hostname (config) # backup profile config to local
Step 1 of 3: Performing Sanity checks
100.0% [#################################################################]
Step 2 of 3: Backing up config db
100.0% [#################################################################]
Step 3 of 3: Generating Backup package
100.0% [#################################################################]
The following example backs up the configuration database to a remote location:
hostname (config) # backup profile config to scp://admin123@bkpFeb/IE-CM4400
Password (if required): ********
Step 1 of 4: Performing Sanity checks
100.0% [#################################################################]
Step 2 of 4: Backing up config db
100.0% [#################################################################]
Step 3 of 4: Generating Backup package
100.0% [#################################################################]
Step 4 of 4: Transferring backup to remote loc
100.0% [#################################################################]
© 2022 FireEye Security Holdings US LLC
241
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
Limiting the Number of Backup Files on
Your Appliance
For Local Backups, you can specify a limit to the number of backup files that can be stored
on your appliance. When the number of backup files on your appliance reaches the
specified limit, you need to delete old backups to continue performing local backups.
NOTE: By default, the maximum number of backup files that can be stored on
your appliance is 25.
To set the limit to the number of backup files that can be stored on your appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. (Optional) To view the details of local backup files such as count and file names:
hostname (config) # show backup available local list
3. Specify the maximum number of backup files that can be stored on your appliance.
hostname (config) # backup limit <max-number-of-backups-allowed>
After the backup count on the appliance reaches the limit, you need to delete the old
backups to make space for the new backups. For information on deleting backup
files, see Deleting Previous Backup Files Using the CLI on page 252
4. (Optional) To reset the custom backup limit to the default value:
hostname (config) # backup reset maxcount
Scheduling Automatic Backups
You can configure and enable automatic backup jobs. You can specify how often you want
the backup job to run automatically.
NOTE: You can schedule automatic backup jobs only using the CLI.
242
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Scheduling Automatic Backups
Prerequisites
l
Admin access
l
Sufficient storage for automatic backups
IMPORTANT! Additional space is required when you schedule automatic
backups to run frequently. You must monitor the generated backups and
delete the unnecessary backups.
Scheduling Automatic Backups Using the CLI
Use the commands in this section to schedule automatic backups for the database.
To configure the scheduled backup job:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Create the job by specifying the job ID.
hostname (config) # job <jobID>
3. Schedule the backup job for the configuration database:
hostname (config) # job <jobID> command <sequenceNumber> "backup
profile config"
4. Use the backup profile command to specify the location for the backup file.
hostname (config) # job <jobID> command <sequenceNumber> "backup
profile config to <backupLocation>"
l
To schedule the backup job to a local destination on the Central Management
platform:
hostname (config) # job <jobID> command <sequenceNumber> "backup
profile config to local"
l
To schedule the backup job on a remote server:
hostname (config) # job <jobID> command <sequenceNumber> "backup
profile config to <url>"
where <url> is the specified remote location using the following format:
scp://<username>:<password>@<hostname>/<remotePath>
l
To schedule the backup job to a USB drive on your local machine:
hostname (config) # job <jobID> command <sequenceNumber> "backup
profile config to usb"
5. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
243
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
To schedule automatic backups for the database:
1. Specify how often you want the backup job to run automatically.
l
To schedule daily, enter the end date, start date, or time:
hostname (config) # job <jobID> schedule daily end date
<yyyy/mm/dd>
hostname (config) # job <jobID> schedule daily start date
<yyyy/mm/dd>
hostname (config) # job <jobID> schedule daily time <hh:mm:ss>
The parameter values are as follows:
o
<yyyy/mm/dd> specifies the end or start date for the backup job.
o
<hh:mm:ss> specifies the time to start the backup job based on a 24-
hour clock.
l
To schedule monthly, enter:
hostname (config) # job <jobID> schedule monthly day-of-month
<day>
where <day> is the day of the month the backup should occur.
l
To schedule once, enter:
hostname (config) # job <jobID> schedule once time <hh:mm:ss> date
<yyyy/mm/dd>
The parameter values are as follows:
o
<hh:mm:ss> specifies the time to start the backup job based on a 24-
hour clock.
o
l
<yyyy/mm/dd> specifies the date to start the backup job.
To schedule a backup that runs periodically on a schedule you define, enter
the end and start date or time interval:
hostname (config) # job <jobID> schedule periodic end
date <yyyy/mm/dd> time <hh:mm:ss>
hostname (config) # job <jobID> schedule periodic start
date <yyyy/mm/dd> time <hh:mm:ss>
hostname (config) # job <jobID> schedule periodic interval
<timeInterval>
The parameter values are as follows:
o
<yyyy/mm/dd> specifies the end or start date for the backup job.
o
<hh:mm:ss> specifies the end or start time for the backup job based on
a 24-hour clock.
o
244
<timeInterval> is specified in the format of "2h3m4s."
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Downloading Backup Files
l
To schedule weekly:
hostname (config) # job <jobID> schedule <frequency> weekly dayof-week <day>
The <day> parameter is the day of the week the backup job is scheduled to
occur. Valid values are sun (Sunday), mon (Monday), tue (Tuesday), wed
(Wednesday), thu (Thursday), fri (Friday), and sat (Saturday).
l
To specify a type of schedule, enter:
hostname (config) # job <jobID> schedule <type>
where <type> is the type of schedule for the backup job. Valid values are:
Value
Description
once
The backup runs only once
daily
The backup runs daily
weekly
The backup runs weekly
monthly
The backup runs monthly
periodic
The backup runs automatically on a schedule you define
2. Enable the configuration for the scheduled backup job.
hostname (config) # job <jobID> enable
3. Save your changes:
hostname (config) # write memory
4. Verify the status for the scheduled backup job. For example:
hostname (config) # show job
Job 333:
Status:
pending
Enabled:
yes
Continue on failure: no
Schedule type:
Time and date:
daily
2016/08/16 00:00:00 +0000
Last exec time:
N/A
Next exec time:
Sun 2016/08/17 00:00:00 +0000
Commands:
Command 1: backup profile config to local
Downloading Backup Files
You can download backup files from the appliance to your local machine.
NOTE: A backup file is downloaded only using the Web UI.
© 2022 FireEye Security Holdings US LLC
245
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
Prerequisites
l
Admin access
Downloading Backup Files Using the Web UI
Use the Backup and Restore page to download a backup file from the appliance to your
local machine.
To download a database backup file:
1. Click the Settings tab.
2. Click CM Backup & Restore on the sidebar.
3. In the Restore Available Backups section, locate the backup FEBKP file in the
Backup name (Profile) column.
4. Click the green arrow in the Download column to download the backup.
Uploading Backup Files
You can upload backup files from your local machine to the appliance. One backup file is
used to restore the database for multiple appliances. The uploaded backup files are stored
in the same location where you saved the local backup files.
NOTE: You can use the Web UI to upload a backup file or you can secure copy
(SCP) the backup file directly to the /data/fe-backups directory on the appliance.
Prerequisites
l
Admin access
Uploading Backup Files Using the Web UI
Use the Backup and Restore page to upload a backup file from your local machine to the
appliance.
246
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Restoring the Database from a Backup File
To upload a backup file from your local machine:
1. Click the Settings tab.
2. Click CMS Backup & Restore on the sidebar.
3. In the Upload Backup File area, click Choose File, and then navigate to the backup
file you want to upload.
4. Click Submit to upload the backup file from your local machine.
An error occurs if an invalid backup file is uploaded.
Restoring the Database from a Backup
File
You can restore the backup from three locations:
l
l
l
From your local appliance.
From a remote server. Do not restore the current network settings while the
appliance is performing a restore operation from a remote server.
From a USB device connected to your local machine.
Usage Guidelines
Follow these usage guidelines when you are restoring the database from a backup file:
l
l
l
l
l
The appliance will not be fully operational during the restore operation. For
example, the alert detection process will stop during the restore operation.
You cannot cancel the restore operation while it is in process.
If the restore process fails, the Central Management platform will automatically
revert back to the original configuration.
The config backup profile can be restored from a software upgrade. You cannot
restore the backup from a software downgrade.
You cannot restore a backup from another product family.
© 2022 FireEye Security Holdings US LLC
247
Central Management System Administration Guide
l
CHAPTER 16: Database Backup and Restore
You cannot restore a backup from a release earlier than Central Management 7.5.0.
You can restore a backup from Central Management 7.5.0 on a Central Management
platform running release 7.6.0.
Prerequisites
l
l
l
l
Admin access
Verify that you have a backup FEBKP file of the current database before you begin
the restore operation.
Locate the previous backup you want to restore.
Verify the details for the appliance, backup profile, version, hostname, and date
stamp. These details are validated while the restore operation is in process.
Restoring the Database from a Backup File Using the
Web UI
Use the Backup and Restore page to restore the database from a backup file.
NOTE: This illustration is from an Email Security — Server Edition appliance, but it
is representative of CM appliances as well.
To restore the database from a backup file:
1. Click the Settings tab.
2. Click CM Backup & Restore on the sidebar.
3. Locate the backup FEBKP file you want to restore in the Backup Name (Profile)
column.
You have the option to restore everything using a full profile or restore portions
using one of the other profiles.
248
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Restoring the Database from a Backup File
4. If you selected Remote Server, scroll down to enter the location of the remote backup
file in the Remote URL or SCP box:
{scp|sftp}://<username>:<password>@<hostname>/<filePath>
where <username> and <password> are remote server Administrator credentials,
<hostname> is the remote host, and <filepath> is the full path of the backup file.
Then select the profile you want to restore from the drop-down list.
5. (Optional) Clear the Exclude Network Settings checkbox to include the network
settings from the backup file. By default, the network settings are not included in the
restore operation.
CAUTION! Do not restore the current network settings while the
appliance is performing a restore operation from a remote server.
6. Click Restore to restore the backup.
7. In the confirmation dialog box, click Yes.
NOTE: The appliance will not be fully operational during the restore
operation. You cannot cancel the restore operation while it is in process.
You must reinstall the license keys separately.
Restoring the Database from a Backup File Using the CLI
Use the commands in this section to restore the database from a backup file.
To restore the database from a backup file:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Locate the backup FEBKP file you want to restore.
l
To display a list of the backup files on the USB drive:
hostname (config) # show backup available on-usb
l
To display a list of the backup files:
hostname (config) # show backup available local
3. Specify the configuration database profile:
hostname (config) # restore profile config
4. Specify the location of the backup file.
l
To restore the backup from the local destination on the Central Management
appliance:
hostname (config) # restore profile config from local
© 2022 FireEye Security Holdings US LLC
249
Central Management System Administration Guide
l
CHAPTER 16: Database Backup and Restore
To restore the backup from a remote server:
hostname (config) # restore profile config from <url>
where <url> specifies remote server Administrator credentials (<username>
and <password>), the remote server (<hostname>), and the full path of the
backup file( <filepath>) in the following format:
{scp|sftp}://<username>[:<password>]@<hostname>/<filepath>
NOTE: If you do not specify the remote host administrator password
in the restore profile command (where the password would be
visible as clear text), the CLI prompts for the password and obfuscates
the keyboard input as you type it.
l
To restore the backup from a USB drive on your local machine:
hostname (config) # restore profile config from usb
5. Enter the name of the backup file.
hostname (config) # restore profile config
from <backupLocation> backup <name>
6. (Optional) Restore the network settings from the relevant backup:
hostname (config) # restore profile config from <backupLocation>
backup <name> include-network-config
CAUTION! Do not restore the current network settings while the CM
appliance is performing a restore operation from a remote server.
7. (Optional) Monitor the progress of the restore operation. Progress tracking is enabled
by default.
l
To disable progress tracking for the restore operation:
hostname (config) # restore profile config from <backupLocation>
backup <name> progress no-track
l
To enable progress tracking for the restore operation:
hostname (config) # restore profile config from <backupLocation>
backup <name> progress track
You can cancel progress tracking by using Ctrl+C. The restore operation still
happens in the background. Use the show restore status command to
find the status of the restore operation.
Example
The following example shows how to restore a configuration database backup from local
on an appliance.
hostname (config) # restore profile config from local backup vx-Config-7.9.0vx-2-20160802-239500.febkp
250
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Deleting Previous Backup Files
Password (if required): ********
Step 1 of 4: Performing Sanity checks
100.0% [##################################################################]
Step 2 of 4: Extracting backup package
100.0% [##################################################################]
Step 3 of 4: Restoring config db
100.0% [##################################################################]
Step 4 of 4: Restart system services
100.0% [##################################################################]
NOTE: This example is from a Virtual Execution appliance, but it is representative
of CM appliances as well.
Deleting Previous Backup Files
You can delete previous backup files to free space for new backup files.
Prerequisites
l
Admin access
Deleting Previous Backup Files Using the Web UI
Use the Backup and Restore page to delete a backup file.
NOTE: This illustration is from an Email Security — Server Edition appliance, but it
is representative of CM appliances as well.
To delete a backup:
1. Click the Settings tab.
2. Click CMS Backup & Restore on the sidebar.
© 2022 FireEye Security Holdings US LLC
251
Central Management System Administration Guide
CHAPTER 16: Database Backup and Restore
3. In the Restore Available Backups area, locate the backup FEBKP file you want to
delete in the Backup Name (Profile) column.
4. Click the icon in the Delete column.
5. Click Yes to confirm the action.
Deleting Previous Backup Files Using the CLI
Use the commands in this section to delete previous backup files.
IMPORTANT! If you delete a backup file from a USB drive by using the backup
delete from usb command, the deletion might take a few minutes.
To delete a backup file:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Specify the location of the backup file.
l
To delete a file from the appliance, enter:
hostname (config) # backup delete from local
l
To delete a file from a USB drive on your local machine, enter:
hostname (config) # backup delete from usb
NOTE: To delete a remote backup file, you must log in to the remote
server and delete the file manually.
3. Specify the name of the backup file to delete from the backup location.
hostname (config) # backup delete from <backupLocation> name
<backupName>
where <backupName> is the backup FEBKP file you want to delete.
Example
The following example shows how to delete a database backup that resides locally on an
appliance.
hostname (config) # backup delete from local name wMPS-Config-7.9.0-IE-NX90020160807-220207.febkp
NOTE: This example is from a Network Security appliance, but it is representative
of CM appliances as well.
252
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Viewing System Health and Performance Check Results
CHAPTER 17: System Health and
Performance
The Central Management platform provides health and status information about itself and
its managed appliances.
l
Checking Status and Health of Managed Appliances on page 485
For information about checking the status of an MVX cluster, see the Trellix Network
Security Deployment Guide for MVX Smart Grid.
Prerequisites
l
Monitor, Operator, Analyst, or Admin access
Viewing System Health and Performance
Check Results
You can view overall status information about system health and appliance performance
check results.
Prerequisites
l
Admin, Operator, Monitor, or Analyst access
© 2022 FireEye Security Holdings US LLC
253
Central Management System Administration Guide
CHAPTER 17: System Health and Performance
Viewing System Health and Performance Check Results
Using the Web UI
Use the About > Summary page to view overall status information about the appliance
components. The Summary page panels display a summary view of appliance health,
appliance performance, and status.
This example is from a SmartVision Edition sensor (which is a Network Security
appliance with a SmartVision Edition FIREEYE_APPLIANCE license), but it is
representative of CM appliances as well.
The color of a display panel indicates the status of each appliance component:
Color
Gray
Description
A gray panel indicates the appliance component is in good condition.
Yellow A yellow panel indicates the appliance component is in warning condition.
Red
A red panel indicates the appliance component is in critical condition.
The following table describes each display panel on the Summary page.
Panel
Software
Version
254
Description
Compares the software version running on the system to the available
software on the DTI network. A red panel indicates that your appliance is
not running the current software version. To upgrade the software image,
click Upgrade. The Web UI displays the About > Upgrade page, where
you can upgrade to the latest software image.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing System Health and Performance Check Results
Panel
Description
Licenses
Displays the number of installed licenses that are valid and active. A red
panel indicates that licenses have expired. A yellow panel indicates that
licenses will expire within 30 days.
DTI
Displays whether the appliance can receive security content updates
from and upload analysis statistics to the DTI network. A red panel
indicates that services are not reachable.
Backups
Displays the status of the last backup operation. A red panel indicates
that the last backup operation failed or data has never been backed up on
the appliance. To back up the database, click Create Backup. The Web UI
displays the Settings > Appliance Backup & Restore page, where you
can back up the database.
Global
Cache
Displays whether the global cache is enabled on the system.
RAID
Displays the overall status of RAID. An error message appears if a RAID
error has occurred. A yellow panel indicates that a non-RAID disk was
detected.
Power
Supply
Displays the overall status of the power supply. A red panel indicates
that the power supply is in critical condition.
System
Temperature
Displays the current temperature and unit of measurement on the
system. A red panel indicates that the temperature is below or exceeded a
system-defined threshold.
Paging
Displays whether the system has started the paging activity. A yellow
panel indicates that the paging activity is in progress.
IPMI
Compares the IPMI firmware version running on the system to the
available version on the DTI network. A red panel indicates that a newer
version exists.
IP
Displays IPv4, IPv6, or both.
Network
Deployment
Displays the status of network information that might indicate appliance
deployment problems. A red panel indicates that a network deployment
problem was found.
Filesystem
Displays the status of the number of partitions that have free space. A
yellow panel indicates that the amount of free space in one of the
partitions dropped below 10 percent.
© 2022 FireEye Security Holdings US LLC
255
Central Management System Administration Guide
Panel
CHAPTER 17: System Health and Performance
Description
USB
Displays whether a USB device is connected to the appliance.
Timezone
Displays the time zone for your appliance. The Timezone panel also
displays the number of seconds since the appliance was synchronized
with the DTI server.
CMS
Displays the status of whether an appliance is managed by the Central
Management Management appliance.
To display system health and performance check results:
1. Click the About tab.
2. Click Summary.
256
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
Checking System Health and Status
You can use the Web UI or CLI to view health and status information.
Prerequisites
l
Monitor, Operator, Analyst, or Admin access
Checking System Health Using the Web UI
Use the Health Check page to check appliance health and status.
This illustration is from a Network Security appliance, but is representative of CM
appliances as well.
© 2022 FireEye Security Holdings US LLC
257
Central Management System Administration Guide
CHAPTER 17: System Health and Performance
To view health and status:
1. Click the About tab.
2. Click Health Check.
The results of the last check are displayed.
3. Review the system information.
4. To update the results, click Refresh Health Check.
The following sections contain descriptions of the information in each area of the page.
Version Information
The About > Health Check > Version Information section provides an up-to-date view of
the software running on your appliance and compares that with the available software on
the Trellix DTI network.
NOTE: Information about the IPMI version is not displayed for a user that is
assigned an Analyst role.
Information
258
Description
Software
Version
Compares the software version running on the system to the available
software on the DTI network. If a newer version exists, administrators are
prompted to upgrade the software.
Installed
Version
Displays the current software version running on the system.
Available
Version
Displays the current software version available on the DTI network.
Content
Version
When the Central Management appliance is in "online" mode, it sends the
request for security content updates to the DTI network on behalf of its
managed appliances. The security content is downloaded to the managed
appliances; it is not hosted on the Central Management appliance. When
the Central Management appliance is in "offline" or "local" mode, the
Central Management appliance downloads and hosts the security content
for the appliances to download.
IPMI
Version
Compares the IPMI firmware version running on the system to the
available version on the DTI network. If a newer version exists,
administrators are prompted to upgrade the firmware.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
Information
Description
Installed
Version
Displays the current IPMI firmware version.
Available
Version
Displays the latest available IPMI firmware version.
Guest Images Information
The About > Health Check > Guest Images Information section provides an up-to-date
view of the guest images installed on your appliance.
System Info
The System Info status section provides an up-to-date status of your appliance hardware
and alerts administrators when problems are found.
Information
Description
Processing
Load
Provides analysis of the overall load the system is carrying. If it is nearing
capacity, the administrator is alerted.
© 2022 FireEye Security Holdings US LLC
259
Central Management System Administration Guide
Information
CHAPTER 17: System Health and Performance
Description
Average
Load
The average processing load handled by the system.
Elapsed
The current uptime of the system in days, hours, minutes, and seconds.
Detection
Engine
Displays the status of the detection engine. If the Detection Engine is not
running, the administrator is alerted.
VM
Analyzing
The number of virtual machines currently analyzing suspect content.
VM
Allowed
The maximum number of VMs that can run concurrently to analyze
suspect content.
Services Health
The About > Health Check > Services Health section provides an up-to-date status of your
appliance’s system services and analysis engine services when problems are found.
Information
Description
Service
Name
Displays the name of the system service or analysis engine service.
Status
Displays the health state of the system service or analysis engine service.
Services can be healthy, disabled, degraded, or in the failed state.
Recovery
Steps
Displays instructions for how to resolve the problem.
Hardware
The About > Health Check > Hardware section provides status on the appliance’s
hardware components.
Information about the disk, RAID, and chassis are not displayed for a user that is
assigned an Analyst role.
260
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
Information
Description
Disk
Displays whether the hard disk is online. If a problem is found, the
administrator is alerted.
Device State
Displays the current state of the hard disk.
Device Support
Displays the type of device available on the system.
Self Assessment
Indicates whether the disk passed its internal self-tests.
User Capacity
Shows the disk capacity on the disk.
Chassis
Displays status of the hardware chassis. If a problem is found, the
administrator is alerted.
Lock
Provides the state of the chassis lock.
Boot Up State
Provides the boot up status.
Power Supply
State
Provides the state of the power supply.
RAID
Provides the status of RAID.
Dynamic Threat Intelligence DTI Cloud
The About > Health Check > DTI Cloud section displays the status of the connection
between the appliance and the DTI network.
This example is from a Network Security appliance, but is representative of other FireEye
appliances as well.
Information
Description
DTI Client
Shows whether the DTI client is running on the system.
Username
Displays the current user of the system.
Support
Updates
Displays the status of the support license.
Security
Content
Displays whether security content sharing is enabled on the system.
Sharing
Displays the type of content update license purchased.
© 2022 FireEye Security Holdings US LLC
261
Central Management System Administration Guide
Information
CHAPTER 17: System Health and Performance
Description
Content
Updates
Displays the status of the content update license.
Download
Compares the source for software updates (system images, guest
images, and security content) to the available download source on the
DTI network and displays the status.
Upload
Compares the destination that is used for software uploads to the
available upload destination on the DTI network and displays the
status.
Last
Shows the last time software updates were downloaded and
Communication uploaded.
Time
Features
The About > Health Check > Features section displays the status of the features on the CM
appliance.
This example is from a Network Security appliance, but is representative of CM
appliances as well.
Information
262
Description
ATI
Shows whether the Advanced Threat Intelligence (ATI) feature is
enabled. When you enable the ATI feature, information about MVXverfied events is provided on the Network Security appliances.
Riskware
Shows whether the riskware detection feature is enabled. When you
enable the riskware detection feature, you can distinguish between
malicious files and riskware on the Network Security appliance.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
Interfaces
The About > Health Check > Interfaces section displays information about each available
Ethernet port on the CM appliance.
The About > Health Check > Interfaces section is not displayed for a user that is
assigned an Analyst role.
Information
Description
Interface
Whether the Ethernet port is up or down.
Auto
Negotiation
Whether auto negotiation is enabled.
Duplex
The type of duplex communication used by the Ethernet port.
Link Detected
Whether the Ethernet port is currently linked to another port.
Link
Transceiver
The location of the link transceiver used to generate Ethernet traffic.
Link Speed
The maximum data speed available on the Ethernet port.
MAC Address
The MAC address of the Ethernet port.
RX Packet
The number of packets received by the Ethernet port during the life of
this connection.
TX Packet
The number of packets transmitted by the Ethernet port during the life
of this connection.
TX Packets
Dropped
The number of packets that were dropped through Ethernet traffic.
Checking System Health Using the CLI
Use the CLI commands in this topic to view health and status information about CM
appliance components. This topic describes selected commands that return system,
hardware status, DTI network, and interface information. For a full list of commands and
details about their usage and parameters, see the CLI Command Reference.
l
Monitor, Operator, or Admin access
l
Admin access for the show ipmi command
© 2022 FireEye Security Holdings US LLC
263
Central Management System Administration Guide
CHAPTER 17: System Health and Performance
NOTE: The examples in this section are from a Network Security appliance, but
they are representative of CM appliances as well.
To check appliance health:
1. Go to CLI enable mode:
hostname > enable
2. Display detailed information about the system and the software running on it.
hostname # show version
Product name:
Web MPS [licensed]
Product model:
FireEyeNX9450
Product edition:
Classic
Bandwidth:
2000 Mb
Product release:
wMPS (wMPS) 7.7.0.433916
Build ID:
#433916
Build date:
2015-12-29 17:21:57
Build arch:
x86_64
Built by:
root@vta114
Version summary:
wmps wMPS (wMPS) 7.7.0.433916
#433916 2015-12-29 17:21:57 x86_64 build@vta108:FireEye (xxx)
Content Version:
385.314
Appliance ID:
XXXXXXXXXXXX
Product model:
FireEyeNX9450
Host ID:
XXXXXXXXXXX
System serial num: XXXXXXXXXX
System UUID:
XXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXXX
Uptime:
3d 6h 34m 34.205s
CPU load averages: 0.36 / 0.40 / .38
Number of CPUs:
32
System memory:
9210 MB used / 119984 MB free / 129194 MB total
Swap:
0 MB used / 65536 MB free / 65536 MB total
264
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
3. Display the IPMI configuration:
hostname # show ipmi
IPMI LAN Settings
---------------------------------------Admin Shut Down
: no
Shut Down
: no
IP Address Source
: Static Address
IP Address
: 192.168.42.27
Subnet Mask
: 0
Default Gateway IP
: 0
IPMI Firmware Installed
------------------------------Firmware Version:
2.67
Device:
1
IPMI Version:
2.0
IPMI Firmware Available For Update
----------------------------------New Firmware Version:
2.67
New Firmware Filename:
FireEye_V267.bin
Firmware Update Notice:
Firmware is up to date for this release
IPMI Firmware Availability Notice is enabled
4. Display overall system status:
hostname * show system health
Overall system feature status: Good
5. Display current status of system and available services:
hostname # show show health all
Health Status:
Last Updated at: : 2019-11-06T20:31:00
Service:
: System CPU/Memory/Disk IO Health
Health Status:
: Healthy
Details:
: Healthy
Service:
: Global Cache
Health Status:
: Healthy
Details:
: Healthy
.
.
.
© 2022 FireEye Security Holdings US LLC
265
Central Management System Administration Guide
CHAPTER 17: System Health and Performance
6. Display information about the Dynamic Threat Intelligence (DTI) network:
hostname # show fenet status
Dynamic Threat Intelligence Service:
Update source
Enabled
Download
Upload
Mil
: <online>
: yes
: DTIUser@cloud.fireeye.com
: DTIUser@up-cloud.fireeye.com
: DTIUser@mil-cloud.fireeye.com
HTTP Proxy:
Address
Username
User-agent
:
:
:
Request Session:
Timeout
Retries
Speed Time
Max Time
Rate Limit
: 30
: 3
: 60
: 14400
:
Speed Limit
: 1
Dynamic Threat Intelligence Lockdown:
Enabled
Locked
Lock After
: no
: no
: 5 failed attempts
UPDATES
Enabled
------Security contents: yes
Stats contents:
yes
266
Notify
-----no
Scheduled
--------every
none
Last Updated At
------------------2016/07/18 19:28:00
2016/07/18 15:55:00
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking System Health and Status
7. Display status and traffic statistics for all interfaces:
hostname # show interfaces
Interface ether1 status:
Comment:
Admin up:
yes
Link up:
yes
DHCP running:
no
IP address:
172.00.00.00
Netmask:
255.000.0.0
IPV6 enabled:
no
Speed:
1000Mb/s (auto)
Duplex:
full (auto)
Interface type:
ethernet
Interface ifindex: 12
Interface source:
physical
MTU:
1500
HW address:
00:25:90:D0:A3:76
RX bytes:
3114981133
RX packets:
31934013
RX mcast packets: 31564
RX discards:
296
RX errors:
1
RX overruns:
0
RX frame:
0
TX bytes:
227921679
TX packets:
367951
TX discards:
0
TX errors:
0
TX overruns:
0
TX carrier:
0
TX collisions: 0
TX queue len:
1000
Interface ether2 status:
Comment:
Admin up:
yes
Link up:
no
DHCP running:
no
IP address:
Netmask:
IPV6 enabled:
no
Speed:
UNKNOWN
Duplex:
UNKNOWN
Interface type:
ethernet
MTU:
1500
HW address:
00:25:90:D0:A3:77
RX bytes:
RX packets:
RX mcast packets:
RX discards:
RX errors:
RX overruns:
RX frame:
0
0
0
0
0
0
0
TX bytes:
TX packets:
TX discards:
TX errors:
TX overruns:
TX carrier:
TX collisions:
TX queue len:
0
0
0
0
0
0
0
0
Interface pether2 status:
Comment:
Admin up:
yes
Link up:
no
DHCP running:
no
IP address:
Netmask:
IPV6 enabled:
no
Speed:
UNKNOWN
Duplex:
UNKNOWN
Interface type:
ethernet
Interface ifindex: 9
© 2022 FireEye Security Holdings US LLC
267
Central Management System Administration Guide
CHAPTER 17: System Health and Performance
Interface source:
Bridge group:
MTU:
HW address:
physical
ether2
1500
00:25:90:D0:A3:77
RX bytes:
RX packets:
RX mcast packets:
RX discards:
RX errors:
RX overruns:
RX frame:
0
0
0
0
0
0
0
TX bytes:
TX packets:
TX discards:
TX errors:
TX overruns:
TX carrier:
TX collisions:
TX queue len:
0
0
0
0
0
0
0
1000
Interface pether3 status:
Comment:
Admin up:
yes
Link up:
yes
DHCP running:
no
IP address:
127.0.0.10
Netmask:
255.255.255.0
IPV6 enabled:
no
Speed:
1000 MB/s (auto)
Duplex:
full (auto)
Interface type:
ethernet
Interface ifindex: 6
Interface source:
physical
MTU:
1500
HW address:
00:25:90:D0:A3:67
RX bytes:
RX packets:
RX mcast packets:
RX discards:
RX errors:
RX overruns:
RX frame:
268
31628620500
46795
367056
212322
0
0
0
TX bytes:
TX packets:
TX discards:
TX errors:
TX overruns:
TX carrier:
TX collisions:
TX queue len:
0
0
0
0
0
0
0
1000
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Retrieving SNMP Data
CHAPTER 18: SNMP Data
Trellix appliances send Simple Network Management Protocol (SNMP) data to convey
abnormal conditions to administrative computers that monitor and control them. The
administrative computers are called SNMP managers.
SNMP data includes the following:
l
l
Information that is retrieved (pulled) by the SNMP manager. This information is
sent in response to requests the SNMP manager sends to the appliance. See
Retrieving SNMP Data below.
Events (known as traps) that are sent (pushed) by the appliance to the
SNMP manager. Traps typically report alarm conditions such as a disk failure or
excessive temperature. They are unsolicited; that is, they are not sent in response to
requests from the SNMP manager. See Sending Traps on page 273.
Retrieving SNMP Data
This section describes how to retrieve SNMP information from the CM appliance.
A Management Information Base (MIB) is a text file written in a specific format in which
all of the manageable features of a device are arranged in a tree. Each branch of the tree
contains a number and a name, and the complete path from the top of the tree down to the
point of interest forms the Object Identifier, or OID. The OID is a string of values separated
by periods, such as .1.3.6.1.2.1.1.3.0.
You can send requests for data on an object using the OID, but it can be simpler to use the
symbolic name for the object instead. A MIB allows SNMP tools to translate the symbolic
names into OIDs before sending the requests to the managed device. Symbolic names for
objects in the Trellix MIB include feSerialNumber.0, feHardwareModel.0,
feProductLicenseActive0, feFanIsHealthy.1, and so on.
The Trellix MIB, named FE-FIREEYE-MIB, needs to be downloaded from the CM appliance
to the SNMP manager so it can be loaded into an SNMP browser or other tool. A typical
SNMP browser can retrieve the values the appliance supports, and then display them in a
hierarchy so you can navigate to the value you need to include in the request.
© 2022 FireEye Security Holdings US LLC
269
Central Management System Administration Guide
CHAPTER 18: SNMP Data
This section contains the following topics:
l
Providing Access to SNMP Data below
l
Downloading the MIB below
l
Sending Requests for SNMP Information on page 272
Providing Access to SNMP Data
To allow access to SNMP v3 data, configure a username and password.
Prerequisites
l
Operator or Admin access
To enable access to SNMP data:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Verify that SNMP is enabled:
hostname (config) # show snmp
If the output shows SNMP enabled: no, enter the snmp-server enable command.
3. SNMP v3: Specify the SNMP user and password:
hostname (config) # snmp-server user <username> v3 enable
hostname (config) # snmp-server user <username> v3 auth sha <password>
4. Save your changes:
hostname (config) # write memory
Downloading the MIB
You can download the MIB from the Web UI or from the command prompt.
Prerequisites
l
Analyst, Operator, or Admin access
Downloading the MIB Using the Web UI
Use the Notification Settings page to download the MIB.
270
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Retrieving SNMP Data
To download the MIB:
1. Click the Settings tab.
2. Click Notifications on the sidebar.
3. Click the SNMP tab.
4. In the Define protocol settings section, click Download.
Downloading the MIB Using the Command Prompt
This section describes how to download the FE-FIREEYE-MIB to SNMP managers that run
on Microsoft Windows, Linux, and Apple devices. The MIB file is retrieved using a
program that connects using port 22, which is normally used for protocols such as SSH,
SCP, and PSCP. Because file-level access is denied by policy, the direct path to the MIB file
needs to be specified.
To download the FireEye MIB to Windows devices:
1. Download the pscp.exe tool (available from PuTTY download page).
2. Navigate to a command prompt window.
3. Change to the directory in which you downloaded the pscp.exe tool:
cd Downloads
4. Copy the MIB file from the appliance:
pscp.exe -r -scp
admin@<appliance><applianceIPAddress>:/usr/share/snmp/mibs \Temp\mibs\
5. When prompted for the password, enter admin.
The files are copied to the \Temp\mibs directory on the Windows device.
6. Change to the mibs directory:
cd C:\Temp\mib
© 2022 FireEye Security Holdings US LLC
271
Central Management System Administration Guide
CHAPTER 18: SNMP Data
7. Load the MIB into an SNMP browser or tool, or open the MIB file:
vi FE-FIREEYE-MIB.txt
To download the FireEye MIB to Linux devices:
1. Copy the MIB file from the appliance using the OpenSSH client:
scp -r admin@<appliance><applianceIPAddress>:/usr/share/snmp/mibs
/usr/<userDirectoryName>
2. When prompted for the password, type admin.
The files are copied to the mibs directory that resides in the
/usr/<userDirectoryName> directory.
3. Change to the mibs directory:
cd mibs
4. Load the MIB into an SNMP browser or tool, or open the MIB file:
vi FE-FIREEYE-MIB.txt
To download the FireEye MIB to Apple devices:
1. Navigate to the terminal emulator.
2. Copy the MIB files from the appliance:
scp -r admin@<applianceIPAddress>:/usr/share/snmp/mibs ~/
3. When prompted for the password, type admin.
The files are copied to the mibs directory that resides in the user directory.
4. Load the MIB into an SNMP browser or tool, or open the MIB file:
vi FE-FIREEYE-MIB.txt
Sending Requests for SNMP Information
This topic describes two ways to retrieve SNMP information.
l
l
The snmpget command retrieves the value of a specific object.
The snmpwalk command walks through the object hierarchy, automatically
retrieving the values of objects for the subtree or node that you specified.
Examples of basic commands that retrieve SNMP data follow. The commands are entered
from the SNMP manager application. The IP address in the commands is the appliance
IP address.
SNMP v3 commands:
snmpmgr # snmpget -m +FE-FIREEYE-MIB -v 3 -u myname -a MD5 -A mypassword -l
authNoPriv 172.0.0.0 feTemperatureValue.0
snmpmgr # snmpwalk -m +FE-FIREEYE-MIB -v 3 -u myname -a MD5 -A mypassword -l
authNoPriv 172.0.0.0 enterprises.25597
272
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Sending Traps
SNMP v2c commands:
snmpmgr # snmpget -m +FE-FIREEYE-MIB -v 2c -c public 172.0.0.0
feSupportLicenseActive.0
snmpmgr # snmpwalk -m +FE-FIREEYE-MIB -v 2c -c public 172.0.0.0 fireeye
snmpmgr # snmpwalk -v 2c -c public 172.0.0.0 enterprises.25597
To retrieve license expiration dates formatted in a table, use a command similar to the
following (different commands are required by different SNMP manager applications):
snmpmgr # snmptable -c public -Of -v 2c localhost feLicenseFeatureTable
Check the number of days in the rightmost column. If the value is less than 30, contact
your system administrator.
Sending Traps
This section describes how to configure basic SNMP support on the CM appliance, enable
and configure traps, and set up trap logging. For detailed information about SNMP
commands and options for more advanced configurations, see the CLI Command Reference.
Enabling and Configuring Traps
Various events can trigger the appliance to send traps to the SNMP manager. Most of the
events are enabled by default. This topic describes how to enable the appliance to send
traps, configure the IP address of the SNMP manager that receives the traps, and disable
and enable individual events.
Prerequisites
l
Operator or Admin access
To enable traps and events:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. SNMP is enabled by default. Verify that it is enabled:
hostname (config) # show snmp
If the output shows SNMP enabled: no, enter the snmp-server enable command.
3. Enable the appliance to send notifications to the SNMP manager:
hostname (config) # snmp-server enable notify
© 2022 FireEye Security Holdings US LLC
273
Central Management System Administration Guide
CHAPTER 18: SNMP Data
4. Specify the IPv4 or IPv6 address of the SNMP manager:
hostname (config) # snmp-server host <IPv4 or IPv6 address> traps
public
5. Save your changes
hostname (config) # write memory
To view the events that can be enabled or are currently enabled:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View a list of all events that can be enabled:
hostname (config) # snmp-server notify event ?
3. View the events that are currently enabled:
hostname (config) # show snmp events
To disable or enable specific events:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Disable an event:
hostname (config) # no snmp-server notify event <event>
For example, the following command stops a trap from being sent when the
temperature of the appliance is normal:
hostname (config) # no snmp-server notify event normal-temperature
3. Enable an event:
hostname (config) # snmp-server notify event <event>
For example, the following command enables the appliance to send a trap when
there is a change in an interface link:
hostname (config) # snmp-server notify event if-link-change
1. Save your changes:
4.
hostname (config) # write memory
Logging Trap Messages
The snmptrapd service receives and logs trap messages.
274
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Sending Traps
To set up trap logging:
1. Log into the SNMP manager application.
2. Enable the snmptrapd service:
snmptrapd
3. Specify the log location:
/var/log/snmptrapd.log
© 2022 FireEye Security Holdings US LLC
275
Central Management System Administration Guide
276
CHAPTER 18: SNMP Data
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About Login Banners and Messages
CHAPTER 19: Login Banners and
Messages
This section covers the following information:
l
About Login Banners and Messages below
l
Customizing Login Banners and Messages Using the Web UI on the next page
l
Customizing Login Banners and Messages Using the CLI on page 279
About Login Banners and Messages
You can customize or remove the messages that appear when users log in to the CM
appliance. You can configure the following messages:
l
Remote Banner—Shown on the Web UI login page and SSH login page.
l
Local Banner—Shown after the username is entered in the CLI session.
l
Message of the Day—Shown after the user is authenticated and logged into the
appliance CLI.
The default local banner and message of the day are shown in the following illustration.
© 2022 FireEye Security Holdings US LLC
277
Central Management System Administration Guide
CHAPTER 19: Login Banners and Messages
Customizing Login Banners and
Messages Using the Web UI
Use the Login Banner page to configure the messages users see when they log in to the CM
appliance.
278
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Login Banners and Messages Using the CLI
Prerequisites
l
Operator or Admin access
To configure login messages:
1. Click the Settings tab.
2. Click Login Banner on the sidebar.
3. In the Remote Banner Text box, clear any existing text, and then enter the message
to be displayed in the Web UI and SSH login pages. You can enter up to 2000
characters.
IMPORTANT! If you change the banner text later with the banner login
CLI command, the new text will also appear in the Web UI login page and
SSH login page, overwriting the text you specify here.
4. In the Local Banner Text box, clear any existing text, and then enter the message to
be displayed in the CLI after the username is entered. You can enter up to 2000
characters.
5. In the Message of the Day Text box, clear any existing text, and then enter the
message to be displayed in the CLI after the user is authenticated. You can enter up
to 2000 characters.
6. Click Update.
The messages will appear the next time the user logs in.
Customizing Login Banners and
Messages Using the CLI
Use the CLI commands in this topic to configure the messages users see when they log in
to the appliance.
l
The login message is shown after the username is entered.
l
The local login message is shown in the CLI login after the username is entered.
l
The remote login message is shown in the SSH login page.
l
The message of the day is shown after the password is entered and the user is
authenticated.
NOTE: Messages can be longer than one line. To add a new line, type >. Each
message can contain up to 2000 characters.
© 2022 FireEye Security Holdings US LLC
279
Central Management System Administration Guide
CHAPTER 19: Login Banners and Messages
Prerequisites
l
Operator or Admin access
To customize the messages:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Display the current banner text:
hostname (config) # show banner
3. Perform the following tasks as needed.
l
To configure the same message for the local login message (that appears in the
CLI login) and the remote login message (that appears in the Web UI login page
and SSH login page), use the following command:
hostname (config) # banner login "<text>"
IMPORTANT! The login message you configure using the
banner login "<text>" command also overwrites the remote message
that is displayed on the Web UI login page and SSH login page. Use
the Customizing Login Banners and Messages Using the Web UI on
page 278 to specify a unique Web UI and SSH login message.
l
To change the local login message only, use the following command:
hostname (config) # banner login-local "<text>"
l
To change the remote login message only, use the following command:
hostname (config) # banner login-remote "<text>"
l
To change the message of the day, use the following command:
hostname (config) # banner motd "<text>"
l
To clear the local login message, the remote login message, or both:
hostname (config) # banner login ""
hostname (config) # banner login-local ""
hostname (config) # banner login-remote ""
l
To clear the message of the day:
hostname (config) # banner motd ""
l
To restore the default messages:
hostname (config) # no banner login
hostname (config) # no banner motd
4. Save your changes.
hostname (config) # write memory
280
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Login Banners and Messages Using the CLI
Examples
The following example changes the message of the day.
hostname (config) # banner motd “There are no maintenance activities
scheduled for this week.”
The following example changes the local and remote login messages:
hostname (config) # banner login "This FireEye appliance is the property of
Acme, Inc.
>
>Unauthorized access is prohibited and is punishable by law."
The following example shows the current messages.
hostname # show banner
Banners:
Message of the Day (MOTD): There are no maintenance activities scheduled
for this week.
Login: This FireEye appliance is the property of Acme, Inc.
Unauthorized access is prohibited and is punishable by law.
The following example shows the default messages:
hostname # show banner
Banners:
Message of the Day (MOTD): FireEye Command Line Interface
Local login: This system is for the use of authorized users only.
>
>Individuals using this computer system without authority, or in excess of
their authority, are subject to having all of their activities on this system
monitored and recorded by system personnel.
Network login: This system is for the use of authorized users only.
>
>Individuals using this computer system without authority, or in excess of
their authority, are subject to having all of their activities on this system
monitored and recorded by system personnel.
© 2022 FireEye Security Holdings US LLC
281
Central Management System Administration Guide
CHAPTER 19: Login Banners and Messages
282
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Viewing Supported Features Using the Web UI
CHAPTER 20: Supported Features
The Web UI Features page shows tiles for the features available for this appliance. Tiles for
enabled features are marked with a checkmark and are outlined in green. Features
introduced in the release of Central Management that you are viewing are labeled New.
Prerequisites
l
Admin, Operator, Monitor, or Analyst access
Viewing Supported Features Using the
Web UI
Use the Supported Features page to view the features available for an appliance.
To view the supported features:
1. Click the Features tab or click About > Supported Features.
2. To filter by category, select one of the following from the selection box on the top left
of the page:
l
Detection
l
Integration
l
Management
3. Click Enabled or Disabled to filter by enabled or disabled features.
4. Click New Features Only to view only new features.
5. Click i in a tile to view information about the feature, including the version in
which it was released, the category of security it provides, and any additional
requirements.
© 2022 FireEye Security Holdings US LLC
283
Central Management System Administration Guide
284
CHAPTER 20: Supported Features
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Configuring Event Notifications Using the Web UI
CHAPTER 21: Event Notifications
As described in Managing the Distribution of Alert Notifications on page 415, you can
configure alert notifications for the Central Management appliances, for managed
appliances, or both.
You can send a test-fire notification from the Central Management appliance or from
managed appliances. There are the following differences:
l
l
l
l
A test-fire notification sent from a managed appliance contains more information
than one sent from the Central Management appliance.
Notifications sent from the Central Management appliance do not appear in the
Central Management database or Web UI.
Notifications sent from a managed appliance do appear in the appliance database
and Web UI; if they are aggregated up to the Central Management appliance, they
also appear in the Central Management database and Web UI.
After notifications are aggregated up to the Central Management appliance, another
notification is sent from the Central Management appliance.
NOTE: This section describes how to configure event (alert) notifications. See System
Email Settings on page 141 for information about system email notifications.
Configuring Event Notifications Using
the Web UI
Prerequisites
l
The appliance must have an established connection to the Internet.
l
Operator or Admin access.
© 2022 FireEye Security Holdings US LLC
285
Central Management System Administration Guide
CHAPTER 21: Event Notifications
Configuring Event Notifications
Use the Notification Settings page to configure event notifications.
To configure event notifications:
1. Click the Settings tab.
2. Click the Notifications on the side bar. The Summary tab opens.
3. In the Global column of the matrix, select the event types for which you want
notifications.
Selections in this column ensure notifications are sent for these event types. This
selection does not affect the display of events in the Web UI.
4. In the Global row of the matrix, select the appropriate protocol for all events.
Alternatively, select the appropriate protocol for each event type, in the appropriate
event type row.
5. To configure a protocol, click the applicable column heading:
o
Configuring Email Notifications Using the Web UI on page 289
o
Configuring HTTP Notifications Using the Web UI on page 291
o
Configuring Rsyslog Notifications Using the Web UI on page 295
o
Configuring SNMP Notifications Using the Web UI on page 299
6. Click Send Test Message to send a test notification to verify your settings for all
enabled protocols. Recipients are specified in the Email Settings page; see
Configuring Email Recipients on page 147.
NOTE: Test-fire events generated for malware object event notifications
disappear from the Alerts tab within five minutes.
286
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
7. To turn off daily digest notifications for all enabled protocols, clear the Daily digest
at checkbox. To turn on daily digest notifications, select the checkbox.
NOTE: Trellix recommends using Per Event notifications instead of Daily
Digest notifications.
8. To change the time for the daily notification, specify the hour and minutes in the
drop-down list boxes.
9. To apply your notification settings, click Update Digest.
CSV Fields for Daily Digest Notifications
The following table describes the fields included in the daily digest notifications for all
protocols.
Field
Description
alertType
Type of alert.
alertid
Trellix internal alert ID (which is external for ArcSight).
product
Name of Trellix product.
release
Trellix software release.
fileHash
Checksum of the malware object from a managed Trellix appliance MVX
engine.
dvchost
Hostname of a Trellix appliance performing the detection and sending the
notification.
sname
Trellix-assigned signature name.
dvc
Device address of the detecting Trellix appliance MVX engine.
locations
Geographical location of the botnet CnC server, if known.
malware_
type
Type of malware.
sev
Severity level of the event. Range: 0 through 10. The highest event severity
level is 10.
occurred
Time that the malware event occurred as detected by a managed Trellix
appliance MVX engine.
mwurl
URL that triggered the malware event.
© 2022 FireEye Security Holdings US LLC
287
Central Management System Administration Guide
Field
CHAPTER 21: Event Notifications
Description
link
URL of the infection or alert that is local to the detecting appliance.
src
IP address of the infected host.
action
Type of action (notified or blocked) that was taken by the managed Trellix
appliance MVX engine.
objurl
Detailed information about the detected malware URL.
sid
Trellix internal alert signature ID that is assigned for malware detection.
stype
Trellix-assigned signature type that is used for malware detection.
profile
Guest image profile and version that is used for malware detection.
malwarenote
Notes about the malware.
application Name of the target application that is running on the MVX engine during
malware detection.
288
original_
name
Original file name of the malware.
header
Protocol header.
anomaly
Attributes of operating system (OS) changes made by the malware, data
theft, or miscellaneous anomaly.
osinfo
Information about the OS name and version.
cnchost
Hostname of the command and control (CnC) server, if known. This field
will display the IP address if the managed appliance cannot determine the
hostname.
channel
CnC channel.
cncport
Port number of the CnC listening server.
os
Application name of the target OS.
app
Name of the target application that is running on the MVX engine during
malware detection.
shost
Hostname of the infected machine as detected by a managed FireEye
appliance MVX engine, if available.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
Field
Description
spt
Source port number of the infected host as detected by a managed Trellix
appliance MVX engine.
smac
Source MAC address of the infected host.
dst
IP address of the destination when any communication to an external host
is observed within the MVX engine.
dmac
MAC address of the destination when any communication to an external
host is observed within the MVX engine.
dpt
Port number of the destination when any communication to an external
host is observed within the MVX engine.
Configuring Email Notifications Using the Web UI
Use the Notification Settings page to select who is sent email notifications when the
specified events are detected.
Prerequisites
l
The appliance must have an established connection to the Internet.
l
Operator or Admin access
Configuring SMTP Settings
Use the Define protocols section on the SMTP tab of the Notification Settings page to
configure SMTP settings.
© 2022 FireEye Security Holdings US LLC
289
Central Management System Administration Guide
CHAPTER 21: Event Notifications
To configure the SMTP server:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the SMTP tab.
4. Locate the Define protocol settings section.
5. Enter the domain that is used for email in the Domain field.
6. Enter the SMTP server that is used for mail delivery in the SMTP Server field.
7. Enter the SMTP server port that is used for mail delivery in the SMTP Server Port
field.
8. (Optional) Select the Return hostname checkbox to use the local domain name.
Clear this checkbox to use the value in the Return username box and the value in
the Domain box.
9. Enter the user who is specified as the “from” user in the Return username box.
10. Verify that the value in the Return address box is correct. If it is not, change the
values in the Domain box and Return username boxes.
11. Select XML, JSON, or Text as the default format and select which level of detail is
provided in the Default format drop-down list box:
o
Normal—This format contains detailed information and abstracts, such as
alert type, ID, source IP, malware name, hostname, and alert URL without
redundant information.
o
Concise—This format contains basic information, such as alert type, ID,
source IP, malware name, hostname, and alert URL.
o
Extended—This format contains detailed information and abstracts,
including data-theft information (if any) and static-analysis details. This
format provides all details about files and objects modified during analysis.
12. Select whether to send the notification as an inline message or an attachment in the
Default send as drop-down list box.
13. Select the delivery frequency in the Default delivery drop-down list box:
o
Per Event (Recommended)—Send a notification each time an event of this
type occurs.
o
Daily Digest—Send a daily notification of specified events detected in the
past 24 hours.
14. Click Apply Settings.
NOTE: If you do not click Apply Settings, your changes are lost.
290
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
Setting Up the SMTP Recipients
Use the View and add SMTP Recipients section of the Notification Settings page to add
and configure SMTP recipients for email notifications.
To add an SMTP recipient:
1. Select Notifications on the side bar.
2. Enter the email address to receive the notification in the Email Address box. For
example, name@company.com
3. Select the Enabled checkbox to enable the recipient to receive email notifications.
To update the SMTP recipient listing:
1. Select Notifications on the side bar.
2. Click the SMTP tab.
3. Click the recipient in the Name column.
4. Click the icon in the Edit column.
5. Make changes as needed.
6. Click Update Recipient.
Configuring HTTP Notifications Using the Web UI
Use the Notification Settings page to post HTTP notifications to one or more Web servers.
Prerequisites
l
The appliance must have an established connection to the Internet.
l
Operator or Admin access.
© 2022 FireEye Security Holdings US LLC
291
Central Management System Administration Guide
CHAPTER 21: Event Notifications
Configuring HTTP Settings
Use the Define protocol settings section on the HTTP tab of the Notification Settings page
to configure default settings for HTTP notifications.
To configure HTTP settings:
1. Click the Settings tab.
2. Select Notifications on the side bar.
3. Click the HTTP tab.
4. Select the delivery frequency in the Default delivery drop-down list box:
o
Daily Digest—Send a daily notification of specified events detected in the
past 24 hours in the selected format and level of details (default is Concise).
o
Per Event (recommended)—Send a notification each time an event of this
type occurs.
5. Select a service provider in the Default provider drop-down list box. The default
service provider is Generic.
NOTE: Trellix recommends using the Generic service provider.
6. Select XML, JSON, or Text as the default format and select which level of detail is
provided in the Default format drop-down list box:
o
l
l
Normal—This format contains detailed information and abstracts, such as
alert type, ID, source IP, malware name, hostname, and alert URL without
redundant information
Concise—This format contains basic information, such as alert type, ID,
source IP, malware name, hostname, and alert URL.
Extended—This format contains detailed information and abstracts,
including data-theft information (if any) and static-analysis details. This
format provides all details about files and objects modified during analysis.
7. To apply the HTTP settings, click Apply Settings.
NOTE: If you do not click Apply Settings, your changes are lost.
292
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
Setting Up HTTP Servers
Use the View and add HTTP Servers section on the HTTP tab of the Notification Settings
page to add and configure HTTP servers.
To add an HTTP server:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the HTTP tab and locate the View and add HTTP Servers section.
4. Click Add HTTP Server. The Add New HTTP Server dialog box opens.
5. Enter the name of the HTTP server that will post the notification (for example,
NX7400 or HX4500) in the Server name box
NOTE: Do not enter URLs and email addresses in the Server name box.
6. Select the Enabled checkbox to choose which servers will post HTTP notifications.
7. Enter the URL of the server to post the HTTP notification in the Server Url box.
8. Leave the User box blank. This option will be deprecated.
9. Select the Alerts Update Notification checkbox to choose which servers will post
HTTP notifications when ATI alert updates are detected.
10. (Optional) If authentication is required for the server, select the Auth checkbox. If
you checked the Auth checkbox, you must also enter a username and password.
l
Enter the user name for HTTP authentication in the Username box.
l
Enter the password for HTTP authentication in the Password box.
11. (Optional) If you want to use SSL for notifications, select the SSL Enable checkbox
and SSL Verify checkboxes.
© 2022 FireEye Security Holdings US LLC
293
Central Management System Administration Guide
CHAPTER 21: Event Notifications
12. Select the event type or All Events in the Events Notification drop-down list box to
post HTTP notifications when the specified events are detected.
NOTE: Selections on the Summary tab take precedence over your
selection here. For example, if you globally disable an event type on the
Summary tab, no alert notifications will be sent for that event type,
regardless of your selection in this drop-down list box.
13. Select the delivery frequency in the Delivery drop-down list box:
o
Per Event (recommended)—Send a notification each time an event of this
type occurs.
o
Default—Use the delivery frequency specified in the Default delivery box in
the HTTP Settings area.
o
Daily Digest—Send a daily notification of specified events detected in the
past 24 hours in the selected format and level of details (default is Concise).
14. Select a service provider in the Default provider drop-down list box. The default
service provider is Generic.
NOTE: Trellix recommends using the generic service provider.
15. Select XML, JSON, or Text as the notification format and select which level of detail
is provided in the Message Format drop-down list box. Select Default to use the
format specified in the Default format box in the HTTP Settings area.
o
Normal—This format contains detailed information and abstracts, such as
alert type, ID, source IP, malware name, hostname, and alert URL without
redundant information.
o
Concise—This format contains basic information, such as alert type, ID,
source IP, malware name, hostname, and alert URL.
o
Extended—This format contains detailed information and abstracts,
including data-theft information (if any) and static-analysis details. This
format provides all details about files and objects modified during analysis.
16. Click Add New HTTP Server.
To modify the HTTP server listing:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the HTTP tab and locate the View and add HTTP Servers section.
4. Click the server in the Name column in the View and add HTTP Servers section.
5. Click the icon in the Edit column.
6. Update the settings as needed.
7. Click Update HTTP Server.
294
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
To enable or disable an HTTP server:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the HTTP tab and locate the View and add HTTP Servers section.
4. Select the checkbox next to the server.
5. Click Enable or Disable.
6. Click Yes to confirm the action.
To remove an HTTP server:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the HTTP tab and locate the View and add HTTP Servers section.
4. Select the checkbox next to the server.
5. Click Remove.
6. Click Yes to confirm the action.
Configuring Rsyslog Notifications Using the Web UI
Use the Notification Settings page to send notifications to one or more remote syslog
servers.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access
Configuring Rsyslog Settings
Use the Define protocol settings section on the RSYSLOG tab of the Notification Settings
page to configure default settings for rsyslog notifications.
© 2022 FireEye Security Holdings US LLC
295
Central Management System Administration Guide
CHAPTER 21: Event Notifications
To configure rsyslog settings:
1. Click the Settings tab.
2. Select Notifications on the side bar.
3. Click the RSYSLOG tab.
4. Select Common Event Format (CEF), Log Event Enhanced Format (LEEF), CommaSeparated Values (CSV), XML, JSON, or Text as the default format and select
which level of detail (only for XML, JSON, or text) is provided in the Default format
drop-down list box:
o
Normal—This format contains detailed information and abstracts, such as
alert type, ID, source IP, malware name, hostname, and alert URL without
redundant information.
o
Concise—This format contains basic information, such as alert type, ID,
source IP, malware name, hostname, and alert URL.
o
Extended—This format contains detailed information and abstracts,
including data-theft information (if any) and static-analysis details. This
format provides all details about files and objects modified during analysis.
5. Per event is selected in the Default delivery drop-down list box. This sends a
notification each time an event of this type occurs.
6. Select the severity classification for the rsyslog notification in the Default send as
box:
o
Alert—Action must be taken immediately (severity 1).
o
Critical—Critical conditions (severity 2).
o
Debug—Debug-level messages (severity 7).
o
Emergency—Emergency: system is unusable (severity 0).
o
Error—Error conditions (severity 3).
o
Informational—Informational messages (severity 6).
o
Notice—Normal but significant conditions (severity 5).
o
Warning—Warning conditions (severity 4).
7. Click Apply Settings.
NOTE: If you do not click Apply Settings, your changes are lost.
Setting Up Rsyslog Servers
Use the View and add Rsyslog Servers section on the RSYSLOG tab of the Notification
Settings page to add and configure rsyslog servers.
296
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
To add an rsyslog server:
1. Click the Settings tab.
2. Click Notifications on the side bar.
3. Click the RSYSLOG tab.
4. Click Add Rsyslog Server. The Add New Rsyslog Server dialog box opens.
5. Enter the name of the rsyslog server to receive the notifications (for example,
NX7400) in the Server Name box.
6. Enter the IP address of the rsyslog server in the IP Address box.
7. Select the Enabled checkbox to choose which servers will receive rsyslog
notifications.
8. Select the delivery frequency in the Delivery drop-down list box:
o
Default—Use the delivery frequency specified in the Default delivery box in
the Rsyslog Settings area.
o
Per Event—Send a notification each time a malware object is detected.
9. Select the event type or All Events in the Notification drop-down list box to send
rsyslog notifications when the specified events are detected.
10. Select CEF, LEEF, CSV, XML, JSON, or Text as the default format and select which
level of detail (only for XML, JSON, or text) is provided in the Format drop-down
list box. Select Default to use the format specified in the Default format box in the
Rsyslog Settings section.
o
Normal—This format contains detailed information and abstracts, such as
alert type, ID, source IP, malware name, hostname, and alert URL without
redundant information.
o
Concise—This format contains basic information, such as alert type, ID,
source IP, malware name, hostname, and alert URL.
o
Extended—This format contains detailed information and abstracts,
including data-theft information (if any) and static-analysis details. This
format provides all details about files and objects modified during analysis.
© 2022 FireEye Security Holdings US LLC
297
Central Management System Administration Guide
CHAPTER 21: Event Notifications
11. Select the severity classification for the rsyslog notification in the Send as box:
o
Default—Use the value specified in the Default send as field in the Rsyslog
Settings area.
o
Alert—Action must be taken immediately (severity 1).
o
Critical—Critical conditions (severity 2).
o
Debug—Debug-level messages (severity 7).
o
Emergency—Emergency: system is unusable (severity 0).
o
Error—Error conditions (severity 3).
o
Informational—Informational messages (severity 6).
o
Notice—Normal but significant conditions (severity 5).
o
Warning—Warning conditions (severity 4).
12. Select UDP or TCP in the Protocol drop-down list box.
13. Click Add new Rsyslog Server.
To update the rsyslog servers:
1. Click the Settings tab.
2. Select Notifications on the side bar.
3. Click the RSYSLOG tab.
4. Click the server in the Name column of the View and add Rsyslog Servers section.
5. Click the icon in the Edit column.
6. Update settings as needed.
7. Click Update Rsyslog Server.
To enable or disable an rsyslog server:
1. Click the Settings tab.
2. Select Notifications on the side bar.
3. Click the RSYSLOG tab.
4. Select the checkbox for the server.
5. Click Enable or Disable.
6. Click Yes to confirm the action.
To remove an rsyslog server:
1. Click the Settings tab.
2. Select Notifications on the side bar.
3. Click the RSYSLOG tab.
298
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the Web UI
4. Select the checkbox for the server.
5. Click Remove.
6. Click Yes to confirm the action.
Configuring SNMP Notifications Using the Web UI
NOTE: The following topics pertain to malware alert events. For information about
SNMP notifications that pertain to system events such as low disk space, see SNMP
Data on page 269.
Use the Notification Settings page to send notifications to one or more Simple Network
Management Protocol (SNMP) servers.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access.
Configuring SNMP Settings
Use the Define protocols section on the SNMP tab of the Notification Settings page to
configure default SNMP settings.
To configure SNMP notifications:
1. Click Settings > CM Settings.
2. Click Notifications on the side bar.
3. Click the SNMP tab.
4. Locate the Define protocols settings section.
5. Per event is selected in the Default delivery drop-down list box. This sends a
notification each time an event of this type occurs.
© 2022 FireEye Security Holdings US LLC
299
Central Management System Administration Guide
CHAPTER 21: Event Notifications
6. Select the SNMP version (1 or 2c) to use for the notification in the Version dropdown list box.
7. If you need the MIB file, click Download.
8. Click Apply Settings.
NOTE: If you do not click Apply Settings, your changes are lost.
Setting Up SNMP Servers
Use the SNMP Trap Sink Listing section on the SNMP tab of the Notification Settings
page to add and configure SNMP servers.
To add an SNMP server:
1. Click Settings.
2. Click Notifications on the side bar.
3. Click the SNMP tab.
4. Click Add SNMP Trap Sink. The Add new SNMP trap sink dialog box opens.
5. Enter the name of the SNMP server to receive the notifications in the Trap sink
name box and click Add New SNMP Trap Sink.
6. Enter the IP address of the SNMP server in the IP Address box.
7. Enter the SNMP community string in the Community box.
8. Select the Enabled checkbox to enable the server to receive SNMP notifications.
9. Select the delivery frequency in the Delivery drop-down list box.
o
Default—Use the delivery frequency specified in the Default delivery box in
the SNMP Settings area.
o
Per Event (recommended)—Send a notification each time an event of this
type occurs.
10. Select the event type or All Events in the Notification drop-down list box to send
SNMP notifications when the specified events are detected.
300
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
11. Select the SNMP version (1 or 2c) to use for the notification in the Version dropdown list box. Select Default to use the version specified in the Define protocol
settings section.
12. Click Add New SNMP Trap Sink.
To update SNMP server settings:
1. Click Settings.
2. Click Notifications on the side bar.
3. Click the SNMP tab.
4. Click the server in the Name column.
5. Click the icon in the Edit column.
6. Update settings as needed.
7. Click Update SNMP Trap Sink.
Configuring Event Notifications Using
the CLI
Prerequisites
l
The appliance must have an established connection to the Internet.
l
Operator or Admin access.
Configuring Event Notifications
Use the CLI commands in this topic to configure event notifications.
To configure event notifications using the CLI:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Check which protocols are already enabled:
hostname (config) # show fenotify email
hostname (config) # show fenotify http
hostname (config) # show fenotify rsyslog
hostname (config) # show fenotify snmp
© 2022 FireEye Security Holdings US LLC
301
Central Management System Administration Guide
CHAPTER 21: Event Notifications
3. Configure the protocols that you want to use:
o
Configuring Email Notifications Using the CLI below
o
Configuring HTTP Notifications Using the CLI on page 311
o
Configuring Rsyslog Notifications Using the CLI on page 318
o
Configuring SNMP Notifications Using the CLI on page 325
4. Confirm that the protocols are configured correctly:
hostname (config) # show fenotify email
hostname (config) # show fenotify http
hostname (config) # show fenotify rsyslog
hostname (config) # show fenotify snmp
5. Enable the notifications. By default, notifications are enabled. This command only
affects notifications for enabled protocols. If a protocol has been disabled, you must
enable the protocol before enabling notifications.
hostname (config) # fenotify enable
6. Select the event type:
hostname (config) # fenotify alert domain-match
hostname (config) # fenotify alert infection-match
hostname (config) # fenotify alert ips-event
hostname (config) # fenotify alert malware-callback
hostname (config) # fenotify alert malware-object
hostname (config) # fenotify alert web-infection
7. Send a test email message to all enabled recipients:
hostname (config) # fenotify email send-test
NOTE: Test-fire events generated for event notifications disappear from the
Alerts tab within five minutes.
8. Save the configuration:
hostname (config) # write memory
Configuring Email Notifications Using the CLI
Use the CLI commands in this section to select who is notified by email when malware
objects are detected.
Prerequisites
302
l
The appliance must have an established connection to the Internet.
l
Operator or Admin access to the Central Management platform.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
NOTE: If email notifications are not being received, check that the
following items are specified:
l
l
l
l
Mail port used to send the email notifications (fenotify email
mailhub port <port-number>)
Mail relay address used to send the email notifications (fenotify
email mailhub address <ip_address>)
Email notification recipient (fenotify email recipient
<rname>)
Recipient address used to send the email notifications (fenotify
email recipient <rname> email-address <email_address>)
Configuring SMTP Settings
To configure the SMTP settings, perform the following subtasks:
l
Specify the SMTP server.
l
Set the default SMTP notification settings.
l
(Optional) Set authentication for SMTP notification settings.
l
(Optional) Set preferences for SMTP notifications.
To specify which SMTP server to use:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
3. Set the mail relay address used to send the email notifications:
hostname (config) # fenotify email mailhub address <ip_address>
4. Set the mail port used to send the email notifications:
hostname (config) # fenotify email mailhub port <port-number>
5. Save the configuration:
hostname (config) # write memory
To configure the default settings for SMTP notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
3. Set the domain from which emails appear to come:
hostname (config) # fenotify email domain <email-domain>
© 2022 FireEye Security Holdings US LLC
303
Central Management System Administration Guide
CHAPTER 21: Event Notifications
4. (Optional) To include the hostname in the return address for email notifications:
hostname (config) # fenotify email return host-name <host_name>
5. Set the user name in the return address for email notifications (the default is donot-reply):
hostname (config) # fenotify email return user-name <user_name>
304
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
6. Select one of the XML, JavaScript Object Notation (JSON), or Text options for the
default format of the notification:
The json_legacy-concise, json_legacy-extended, and json_legacy-normal
formats are deprecated.
o
To send notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email default format xml-concise
o
To send notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email default format xml-extended
o
To send notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email default format xml-normal
o
To send notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email default format json-concise
o
To send notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email default format json-extended
o
To send notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email default format json-normal
o
To send notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email default format text-concise
o
To send notifications in Text Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (Text Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email default format text-extended
© 2022 FireEye Security Holdings US LLC
305
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To send notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email default format text-normal
7. Specify how the notification is delivered by default:
o
To deliver the notification as an email attachment, enter:
hostname (config) # fenotify email default send-as attachment
o
To deliver the notification in the email body (the default), enter:
hostname (config) # fenotify email default send-as in-line
8. Specify the default delivery schedule for email notifications:
FireEye recommends using per-event notifications.
o
To receive information about all events detected in the past 24 hours, enter:
hostname (config) # fenotify email default delivery daily-digest
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify email default delivery daily-persource
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify email default delivery hourly-persource
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify email default delivery per-1min-persource
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify email default delivery per-5min-persource
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify email default delivery per-event
9. Save the configuration:
hostname (config) # write memory
To configure authentication for SMTP notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
3. Enable authentication for event mail notifications:
306
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
hostname (config) # fenotify email mailhub auth enable
4. Set the authentication method you want to use to send event mail notifications.
Available methods include PLAIN, LOGIN, or CRAM-MD5.
hostname (config) # fenotify email mailhub auth auth-method PLAIN
5. Set the username required to authenticate sending event email notifications:
hostname (config) # fenotify email mailhub auth username <username>
6. Set the password required to authenticate sending event email notifications:
hostname (config) # fenotify email mailhub auth password <password>
To configure preferences for SMTP notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
3. Enable From: line override for event mail notifications:
hostname (config) # fenotify email mailhub preferences from-lineoverride enable
4. Set the minimum SSL protocol version required to send event mail notifications
through SMTP. The following versions are supported:
l
ssl3: SSLv3 or higher is required.
l
tls1: TLSv1 or higher is required.
l
tls1.1: TLSv1.1 or higher is required.
l
tls1.2: TLSv1.2 or higher is required.
hostname (config) # fenotify email mailhub preferences ssl-min-version
<ssl-min-version>
5. (Optional) Set the TLS certificate authority file for event mail notifications going
through SMTP. You can choose filenames under the /etc/pki/tls/certs/
directory.
hostname (config) # fenotify email mailhub preferences tls-ca-file
<tls-ca-file>
The following example sets the TLS certificate authority file for event mail
notifications to ca-bundle.crt:
hostname (config) # fenotify email mailhub preferences tls-ca-file <cabundle.crt>
6. (Optional) Set the TLS certificate file for event email notifications going through
SMTP. You can choose filenames under the /etc/pki/tls/ directory.
hostname (config) # fenotify email mailhub preferences tls-cert-file
<tls-cert-file>
© 2022 FireEye Security Holdings US LLC
307
Central Management System Administration Guide
CHAPTER 21: Event Notifications
The following example sets the TLS certificate file for event mail notifications to
cert.pem:
hostname (config) # fenotify email mailhub preferences tls-cert-file
<cert.pem>
7. Enable TLS certificate verification for the SMTP relay used for event email
notifications:
hostname (config) # fenotify email mailhub preferences tls-cert-verify
enable
8. Enable the TLS security protocol for the SMTP relay used for event email
notifications:
hostname (config) # fenotify email mailhub preferences tls enable
9. Enable the STARTTLS security protocol for the SMTP relay used for event email
notifications:
hostname (config) # fenotify email mailhub preferences use-start_tls
enable
Setting Up the SMTP Recipients
To set up the SMTP recipients, perform the following subtasks:
l
Add the SMTP recipients.
l
Configure the SMTP recipient listing for email notifications,
To add an SMTP recipient:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
3. Add a recipient for email notifications:
hostname (config) # fenotify email recipient <rname>
4. Select a recipient to receive email notifications (one recipient per command):
hostname (config) # fenotify email recipient <rname> enable
5. Specify the email address for a recipient who will receive email notifications:
hostname (config) # fenotify email recipient <rname> email-address
<email_address>
6. Save the configuration:
hostname (config) # write memory
To configure the SMTP recipient listing for email notifications:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable email notifications:
hostname (config) # fenotify email enable
308
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
3. Select one of the XML, JavaScript Object Notation (JSON), or Text options for the
format of the notifications received by a specified recipient:
NOTE: The json_legacy-concise, json_legacy-extended, and json_legacynormal formats are deprecated.
o
To send notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email recipient <rname> prefer
message format xml-concise
o
To send notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email recipient <rname> prefer
message format xml-extended
o
To send notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email recipient <rname> prefer
message format xml-normal
o
To send notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email recipient <rname> prefer
message format json-concise
o
To send notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email recipient <rname> prefer
message format json-extended
o
To send notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email recipient <rname> prefer
message format json-normal
o
To send notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify email recipient rname prefer message
format text-concise
© 2022 FireEye Security Holdings US LLC
309
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To send notifications in Text Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (Text Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify email recipient rname prefer message
format text-extended
o
To send notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify email recipient rname prefer message
format text-normal
4. Specify how email notifications are delivered to the specified recipient:
o
To deliver the notification as an email attachment, enter:
hostname (config) # fenotify email recipient rname prefer message
send-as attachment
o
To deliver the notification in the email body (the default), enter:
hostname (config) # fenotify email recipient rname prefer message
send-as in-line
5. Select the event type:
hostname (config) # fenotify email alert domain-match
hostname (config) # fenotify email alert infection-match
hostname (config) # fenotify email alert ips-event
hostname (config) # fenotify email alert malware-callback
hostname (config) # fenotify email alert malware-object
hostname (config) # fenotify email alert web-infection
6. Enable email notifications for specified recipients when ATI alert updates are
detected:
hostname (config) # fenotify email recipient <rname> alerts-update
enable
310
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
7. Specify the delivery frequency for email notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive information about all events detected in the past 24 hours, enter:
hostname (config) # fenotify email delivery daily-digest
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify email delivery daily-per-source
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify email delivery hourly-per-source
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify email delivery per-1min-per-source
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify email delivery per-5min-per-source
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify email delivery per-event
8. Save the configuration:
hostname (config) # write memory
Configuring HTTP Notifications Using the CLI
Use the CLI commands in this section to post HTTP notifications to one or more Web
servers.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access
Configuring HTTP Settings
Use the CLI commands in this topic to set up the default configuration for HTTP
notifications.
To configure HTTP settings:
1. Go to CLI configuration mode:
hostname > enable
© 2022 FireEye Security Holdings US LLC
311
Central Management System Administration Guide
CHAPTER 21: Event Notifications
hostname # configure terminal
2. Enable HTTP notifications:
hostname (config) # fenotify http enable
3. Specify the default delivery schedule for HTTP notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive information about all events detected in the past 24 hours, enter:
hostname (config) # fenotify http default delivery daily-digest
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify http default delivery daily-persource
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify http default delivery hourly-persource
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify http default delivery per-1min-persource
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify http default delivery per-5min-persource
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify http default delivery per-event
4. Specify the default service provider. The default service provider is generic.
NOTE: Trellix recommends using the generic service provider.
o
To select Aruba as the provider, enter:
hostname (config) # fenotify http default provider aruba
o
To select the generic provider, enter:
hostname (config) # fenotify http default provider generic
312
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
5. Select one of the XML, JavaScript Object Notation (JSON), or Text options for the
default format of the notification where service_name is the name of the HTTP
server that posts the notification:
NOTE: The json_legacy-concise, json_legacy-extended, and json_legacynormal formats are deprecated.
o
To post notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-concise
o
To post notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-extended
o
To post notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-normal
o
To post notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-concise
o
To post notifications in Text Extended format containing detailed information
and abstracts including data-theft information (if any) and static-analysis
details (Text Extended provides all details about files and objects modified
during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-extended
o
To post notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-normal
o
To post notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-concise
© 2022 FireEye Security Holdings US LLC
313
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To post notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-extended
o
To post notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-normal
6. Save the configuration:
hostname (config) # write memory
Setting Up HTTP Servers
To set up HTTP servers, perform the following subtasks:
l
Add the HTTP servers
l
Configure the HTTP server listing
To add an HTTP server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable HTTP notifications:
hostname (config) # fenotify http enable
3. Specify the name of the HTTP server (for example, NX7400) to receive the
notification. URLs and email addresses are not allowed.
hostname (config) # fenotify http service <service-name>
4. Specify which servers will post HTTP notifications (one server per command):
hostname (config) # fenotify http service <service_name> enable
5. Specify the URL for each HTTP server to receive the notification:
hostname (config) # fenotify http service <service_name> server-url
<url>
6. Save the configuration:
hostname (config) # write memory
To configure the HTTP server listing:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable HTTP notifications:
hostname (config) # fenotify http enable
314
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
3. (Optional) If authentication is required for the server, enable authentication and then
specify the user name and password for HTTP authentication:
hostname (config) # fenotify http service <service_name> auth enable
hostname (config) # fenotify http service <service_name> auth username
<user_name>
hostname (config) # fenotify http service <service_name> auth password
<password>
4. Select the event type:
hostname (config) # fenotify http alert domain-match enable
hostname (config) # fenotify http alert infection-match enable
hostname (config) # fenotify http alert ips-event enable
hostname (config) # fenotify http alert malware-callback enable
hostname (config) # fenotify http alert malware-object enable
hostname (config) # fenotify http alert web-infection enable
5. Enable the specified servers to post HTTP notifications when ATI alert updates are
detected (one server per command):
hostname (config) # fenotify http service <service_name> alerts-update
enable
6. Specify the delivery frequency for HTTP notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive information about all events detected in the past 24 hours, enter:
hostname (config) # fenotify http service <service_name> prefer
message delivery daily-digest
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify http service service_name prefer
message delivery daily-per-source
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify http service <service_name> prefer
message delivery hourly-per-source
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify http service <service_name> prefer
message delivery per-1min-per-source
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify http service <service_name> prefer
message delivery per-5min-per-source
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify http service <service_name> prefer
message delivery per-event
7. (Optional) If you want to use SSL for notifications:
hostname (config) # fenotify http service <service_name> ssl enable
hostname (config) # fenotify http service <service_name> ssl verify
© 2022 FireEye Security Holdings US LLC
315
Central Management System Administration Guide
CHAPTER 21: Event Notifications
8. Specify the service provider. The default service provider is generic.
NOTE: Trellix recommends using the generic service provider.
o
To select the currently active service provider, enter:
hostname (config) # fenotify http service <service_name> provider
default
o
To select the generic provider, enter:
hostname (config) # fenotify http service <service_name> provider
generic
o
To select Aruba as the provider, enter:
hostname (config) # fenotify http service <service_name> provider
aruba
316
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
9. Select one of the XML, JavaScript Object Notation (JSON), or Text options for the
format of the HTTP notifications:
NOTE: The json_legacy-concise, json_legacy-extended, and json_legacynormal formats are deprecated.
o
To post notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-concise
o
To post notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-extended
o
To post notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format xml-normal
o
To post notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-concise
o
To post notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-extended
o
To post notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format json-normal
o
To post notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-concise
© 2022 FireEye Security Holdings US LLC
317
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To post notifications in Text Extended format containing detailed information
and abstracts including data-theft information (if any) and static-analysis
details (Text Extended provides all details about files and objects modified
during analysis.), enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-extended
o
To post notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify http service <service_name> provider
generic message format text-normal
10. Save the configuration:
hostname (config) # write memory
Configuring Rsyslog Notifications Using the CLI
Use the CLI commands in this section to send notifications to a remote syslog server.
NOTE: You must use the CLI to configure whether there should be line breaks
between notifications.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access.
Configuring Rsyslog Settings
Use the CLI commands in this topic to set up the default configuration for rsyslog
notifications.
To configure rsyslog settings:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable rsyslog notifications:
hostname (config) # fenotify rsyslog enable
318
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
3. Specify the default format for rsyslog notifications:
NOTE: The json_legacy-concise, json_legacy-extended, and json_legacynormal formats are deprecated.
o
To send notifications in the Common Export Format (CEF), enter:
hostname (config) # fenotify rsyslog default format cef
o
To send notifications in the comma-separated values (CSV) format, enter:
hostname (config) # fenotify rsyslog default format csv
o
To send notifications in the Log Extended Event Format (LEEF) (default),
enter:
hostname (config) # fenotify rsyslog default format leef
o
To send notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog default format xml-concise
o
To send notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog default format xml-extended
o
To send notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog default format xml-normal
o
To send notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog default format json-concise
o
To send notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog default format json-extended
o
To send notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog default format json-normal
o
To send notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog default format text-concise
© 2022 FireEye Security Holdings US LLC
319
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To send notifications in Text Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (Text Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog default format text-extended
o
To send notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog default format text-normal
4. Specify the default delivery schedule for email notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify rsyslog default delivery daily-persource
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify rsyslog default delivery hourly-persource
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify rsyslog default delivery per-1minper-source
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify rsyslog default delivery per-5minper-source
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify rsyslog default delivery per-event
5. Specify the default severity classification for the rsyslog notification:
NOTE: Trellix recommends setting the severity classification to alert.
o
To indicate that action must be taken immediately (severity 1), enter:
hostname (config) # fenotify rsyslog default send-as alert
o
To indicate that the notification contains critical conditions (severity 2), enter:
hostname (config) # fenotify rsyslog default send-as crit
o
To indicate that the notification contains debug-level messages (severity 7),
enter:
hostname (config) # fenotify rsyslog default send-as debug
o
To indicate an emergency (the system is unusable) (severity 0), enter:
hostname (config) # fenotify rsyslog default send-as emerg
320
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
o
To indicate that the notification contains error conditions (severity 3), enter:
hostname (config) # fenotify rsyslog default send-as error
o
To indicate that the notification contains informational messages (severity 6),
enter:
hostname (config) # fenotify rsyslog default send-as info
o
To indicate normal but significant conditions (severity 5), enter:
hostname (config) # fenotify rsyslog default send-as notice
o
To indicate that the notification contains warning conditions (severity 4),
enter:
hostname (config) # fenotify rsyslog default send-as warning
6. Save the configuration:
hostname (config) # write memory
Configuring Line Feedback for Rsyslog Notifications
Use the CLI commands in this topic to configure whether to send notifications to a remote
syslog server in a single line or with line breaks between each notification. The default is to
send rsyslog notifications in a single line.
To send rsyslog notifications in a single line:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Configure the single line option:
hostname (config) # fenotify preferences rsyslog-strip-lnfb enable
3. Save the configuration:
hostname (config) # write memory
4. Verify that rsyslog notifications will be sent in a single line:
hostname (config) # show fenotify preferences
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: yes
Rsyslog notification Stripping off line feedback: yes
To send rsyslog notifications with line breaks:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Configure the line break option:
hostname (config) # no fenotify preferences rsyslog-strip-lnfb enable
3. Save the configuration:
© 2022 FireEye Security Holdings US LLC
321
Central Management System Administration Guide
CHAPTER 21: Event Notifications
hostname (config) # write memory
4. Verify that rsyslog notifications will be sent with line breaks:
hostname (config) # show fenotify preferences
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: yes
Rsyslog notification Stripping off line feedback: no
Setting Up Rsyslog Servers
To set up rsyslog servers, perform the following subtasks:
l
Add the rsyslog servers
l
Configure the rsyslog servers
To add an rsyslog server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable rsyslog notifications:
hostname (config) # fenotify rsyslog enable
3. Specify the name of the rsyslog server to receive the notification:
hostname (config) # fenotify rsyslog trap-sink <sink_name>
4. Specify which servers will receive rsyslog notifications (one server per command):
hostname (config) # fenotify rsyslog trap-sink <sink_name> enable
5. Specify the IP address or DNS address of the rsyslog server to send event logs to:
hostname (config) # fenotify rsyslog trap-sink <sink_name> address <ip
address>
6. Save the configuration:
hostname (config) # write memory
To configure the rsyslog servers:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable rsyslog notifications:
hostname (config) # fenotify rsyslog enable
3. Specify the delivery frequency for rsyslog notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message delivery daily-per-source
322
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message delivery hourly-per-source
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message delivery per-1min-per-source
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message delivery per-5min-per-source
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message delivery per-event
4. Select the event type:
hostname (config) # fenotify rsyslog alert domain-match
hostname (config) # fenotify rsyslog alert infection-match
hostname (config) # fenotify rsyslog alert ips-event
hostname (config) # fenotify rsyslog alert malware-callback
hostname (config) # fenotify rsyslog alert malware-object
hostname (config) # fenotify rsyslog alert web-infection
5. Specify the format for rsyslog notifications:
NOTE: The json_legacy-concise, json_legacy-extended, and json_legacynormal formats are deprecated.
o
To send notifications in the Common Export Format (CEF), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format cef
o
To send notifications in the comma-separated values (CSV) format, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format csv
o
To send notifications in the Log Extended Event Format (LEEF) (default),
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format leef
o
To send notifications in XML Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format xml-concise
© 2022 FireEye Security Holdings US LLC
323
Central Management System Administration Guide
o
CHAPTER 21: Event Notifications
To send notifications in XML Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (XML Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format xml-extended
o
To send notifications in XML Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format xml-normal
o
To send notifications in JSON Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format json-concise
o
To send notifications in JSON Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (JSON Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format json-extended
o
To send notifications in JSON Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format json-normal
o
To send notifications in Text Concise format containing basic information
such as alert type, ID, source IP, malware name, hostname, and alert URL,
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format text-concise
o
To send notifications in Text Extended format containing detailed
information and abstracts including data-theft information (if any) and staticanalysis details (Text Extended provides all details about files and objects
modified during analysis.), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format text-extended
o
To send notifications in Text Normal format containing detailed information
and abstracts such as alert type, ID, source IP, malware name, hostname, and
alert URL without any redundant information, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message format text-normal
324
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
6. Specify the severity classification for the rsyslog notification:
NOTE: Trellix recommends setting the severity classification to alert.
o
To indicate that action must be taken immediately (severity 1), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as alert
o
To indicate that the notification contains critical conditions (severity 2), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as crit
o
To indicate that the notification contains debug-level messages (severity 7),
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as debug
o
To indicate an emergency (the system is unusable) (severity 0), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as emerg
o
To indicate that the notification contains error conditions (severity 3), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as error
o
To indicate that the notification contains informational messages (severity 6),
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as info
o
To indicate normal but significant conditions (severity 5), enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as notice
o
To indicate that the notification contains warning conditions (severity 4),
enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name> prefer
message send-as warning
7. Specify the protocol used to send rsyslog notifications (UDP is the default):
l
To select UDP, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name>
protocol UDP
l
To select TCP, enter:
hostname (config) # fenotify rsyslog trap-sink <sink_name>
protocol TCP
8. Save the configuration:
hostname (config) # write memory
Configuring SNMP Notifications Using the CLI
NOTE: The following topics pertain to malware alert event notifications. For
information about SNMP notifications that pertain to system events such as low
disk space, see SNMP Data on page 269.
© 2022 FireEye Security Holdings US LLC
325
Central Management System Administration Guide
CHAPTER 21: Event Notifications
Use the CLI commands in this section to send notifications to one or more Simple Network
Management Protocol (SNMP) servers.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access.
Configuring SNMP Settings
Use the CLI commands in this topic to set up the default configuration for SNMP
notifications.
To configure SNMP settings:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable SNMP notifications:
hostname (config) # fenotify snmp enable
3. Specify the default delivery schedule for SNMP notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify snmp default delivery daily-persource
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify snmp default delivery hourly-persource
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify snmp default delivery per-1min-persource
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify snmp default delivery per-5min-persource
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify snmp default delivery per-event
326
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
4. Specify the SNMP version used for notifications:
o
To use SNMP version 1, enter:
hostname (config) # fenotify snmp default version 1
o
To use SNMP version 2c, enter:
hostname (config) # fenotify snmp default version 2c
5. If you are going to download the MIB file, see the procedure that follows for
Microsoft Windows, Linux, or Mac devices. The MIB file is retrieved using a
program that connects using port 22, which is normally used for tools like SSH,
SCP, and PSCP. Because file-level access is denied by policy, the direct path to the
MIB file needs to be specified.
6. Save the configuration:
hostname (config) # write memory
To download the Trellix MIB for SNMP on Windows:
1. Download the pscp.exe tool (available from PuTTY download page).
2. Navigate to a command prompt window.
3. Change to the directory in which you downloaded the pscp.exe tool:
cd Downloads
4. Copy the MIB file from the Central Management appliance:
pscp.exe -r -scp admin@<CMSeriesIPaddress>:/usr/share/snmp/mibs
\Temp\mibs\
5. When prompted for the password, enter admin.
The file is copied to the \Temp\mibs directory that resides on your desktop.
6. Change to the “mibs” directory:
cd C:\Temp\mibs
7. Load the MIB file into an SNMP browser or tool or open the MIB file with the
following command:
FE-FIREEYE-MIB.txt
To download the FireEye MIB for SNMP on Linux:
1. Using the OpenSSH client, copy the MIB file from the Central Management
appliance:
scp -r admin@<CMSeriesIPaddress>:/usr/share/snmp/mibs
/usr/<userDirectoryName>/
2. When prompted for the password, enter admin.
The files are copied to the “mibs” directory that resides in the
/usr/<userDirectoryName> directory.
3. Change to the “mibs” directory:
cd mibs
4. Load the MIB file into an SNMP browser or tool or open the MIB file with the
following command:
vi FE-FIREEYE-MIB.txt
© 2022 FireEye Security Holdings US LLC
327
Central Management System Administration Guide
CHAPTER 21: Event Notifications
To download the FireEye MIB for SNMP on Mac OS X:
1. Navigate to the terminal emulator.
2. Copy the MIB file from the Central Management appliance:
scp -r admin@<CMSeriesIPaddress>:/usr/share/snmp/mibs ~/
3. When prompted for the password, enter admin.
The files are copied to the “mibs” directory that resides in the user directory.
4. Load the MIB file into an SNMP browser or tool or open the MIB file with the
following command:
vi ~/mibs/FE-FIREEYE-MIB.txt
Setting Up SNMP Servers
To set up the SNMP servers, perform the following subtasks:
l
Add the SNMP servers
l
Configure the SNMP servers
To add an SNMP server:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable SNMP notifications:
hostname (config) # fenotify snmp enable
3. Specify the name of the SNMP server (for example, NX7400) for SNMP notifications:
hostname (config) # fenotify snmp trap-sink <sink_name>
4. Specify which servers will receive SNMP notifications (one server per command):
hostname (config) # fenotify snmp trap-sink <sink_name> enable
5. Specify the IP address or DNS address of the SNMP server to receive the
notifications:
hostname (config) # fenotify snmp trap-sink <sink_name> address <ip
address>
6. Save the configuration:
hostname (config) # write memory
To configure the SNMP servers:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Enable SNMP notifications:
hostname (config) # fenotify snmp enable
3. Specify the SNMP community string:
hostname (config) # fenotify snmp trap-sink <sink_name> community
<community_name>
328
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Event Notifications Using the CLI
4. Specify the SNMP version used for notifications:
o
To use SNMP version 1, enter:
hostname (config) # fenotify snmp trap-sink <sink_name> version 1
o
To use SNMP version 2c, enter:
hostname (config) # fenotify snmp trap-sink <sink_name> version 2c
5. Specify the delivery frequency for SNMP notifications:
NOTE: Trellix recommends using per-event notifications.
o
To receive a daily notification for each entity that was the source of the event,
enter:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
message delivery daily-per-source
o
To receive an hourly notification for each entity that was the source of the
event, enter:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
message delivery hourly-per-source
o
To receive a notification every minute for each entity that was the source of
the event, enter:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
message delivery per-1min-per-source
o
To receive a notification every 5 minutes for each entity that was the source
of the event, enter:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
message delivery per-5min-per-source
o
To receive information about each event, sent when the event is triggered,
enter:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
message delivery per-event
6. Select the event type:
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification all-events
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification domain-match
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification infection-match
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification ips-event
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification malware-callback
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification malware-object
hostname (config) # fenotify snmp trap-sink <sink_name> prefer
notification web-infection
7. Save the configuration:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
329
Central Management System Administration Guide
CHAPTER 21: Event Notifications
Configuring the Proxy Server for
Notifications
You can enable or disable the proxy server for notifications. The proxy server is referred to
as the Trellix network proxy server. HTTP notifications are currently sent through the
Trellix network proxy server. This is the default setting. You can disable the proxy server
for outgoing HTTP notifications, such as email reports or Splunk notifications.
NOTE: Proxy server for notifications is configured only using the CLI.
Prerequisites
l
The Central Management appliance must have an established connection to the
Internet.
l
Operator or Admin access.
l
The proxy server must be explicitly disabled for outgoing HTTP notifications.
Configuring the Proxy Server for Notifications Using the
CLI
Use the CLI commands in this topic to configure the proxy server for notifications using
the CLI.
To enable the proxy server for notifications:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Enable the proxy server for notifications.
hostname (config) # fenotify preferences use-fenet-proxy enable
3. Verify that HTTP notifications are enabled for the proxy server.
hostname (config) # show fenotify preferences
Notification customized settings:
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: yes
To disable the proxy server for notifications:
1. Go to CLI configuration mode.
hostname > enable
330
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring ATI Alert Updates for Notifications
hostname # configure terminal
2. Disable the proxy server for notifications.
hostname (config) # no fenotify preferences use-fenet-proxy enable
3. Verify that HTTP notifications are disabled for the proxy server.
hostname (config) # show fenotify preferences
Notification customized settings:
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: no
Configuring ATI Alert Updates for
Notifications
You can enable or disable Advanced Threat Intelligence (ATI) alert updates for
notifications through HTTP and email protocols.
NOTE: Rsyslog and SNMP protocols are not supported.
You can configure Advanced Threat Intelligence (ATI) alert updates for notifications
through HTTP and email protocols. When you enable ATI alert updates for notifications,
notifications will be sent for events with threat intelligence on managed Network Security
appliances running Release 7.7.0 or later. When you disable ATI alert updates for
notifications, notifications will not be sent for events with threat intelligence on managed
appliances. When ATI alert updates are enabled, notifications will not be sent for alerts
with threat intelligence that were detected more than 90 days ago. If multiple alerts match
the same ATI event triggered on the appliance, notifications will be sent only for the first
three alerts per day. For detailed information about ATI, see the Network Security User Guide.
NOTE: ATI alert updates for notifications are configured only using the CLI. This
feature is disabled by default.
Prerequisites
l
l
The Central Management appliance must have an established connection to the
Internet.
Operator or Admin access to the Central Management appliance
© 2022 FireEye Security Holdings US LLC
331
Central Management System Administration Guide
CHAPTER 21: Event Notifications
Configuring ATI Alert Updates for Notifications Using the
CLI
Follow these steps to configure ATI alert updates for notifications using the CLI.
To enable ATI alert updates for notifications:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Enable ATI alert update settings for notifications.
hostname (config) # fenotify preferences alerts-update ati enable
3. Save your changes.
hostname (config) # write memory
4. Verify the status for the ATI alert update settings.
hostname (config) show fenotify preferences
Notification customized settings:
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: yes
Rsyslog notification Stripping off line feedback: yes
Notification timeout: 600 seconds
SSL cipher list: compatible
SSL minimum protocol version: tls1
Alert ATI Updates: yes
CEF Compliance: yes
To disable ATI alert updates for notifications:
1. Go to CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Disable ATI alert update settings for notifications.
hostname (config) # no fenotify preferences alerts-update ati enable
3. Save your changes.
hostname (config) # write memory
4. Verify the status for the ATI alert update settings.
hostname (config) # show fenotify preferences
Notification customized settings:
IPS delivery mode: instant
HTTP(s) notification using fenet proxy: yes
332
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring ATI Alert Updates for Notifications
Rsyslog notification Stripping off line feedback: yes
Notification timeout: 600 seconds
SSL cipher list: compatible
SSL minimum protocol version: tls1
Alert ATI Updates: no
CEF Compliance: yes
© 2022 FireEye Security Holdings US LLC
333
Central Management System Administration Guide
334
CHAPTER 21: Event Notifications
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
On-Demand Cleanup Using Profiles
CHAPTER 22: Disk Space
Management
Some appliance processes require a specific amount of disk space to complete. If disk space
is not available, the processes do not start. An error message describes the problem.
For example, you may need to delete files and artifacts to free disk space if there is not
enough room to do a database backup, to retrieve SNMP data, or to send system
notifications. It may also be necessary to free disk space before upgrading the appliance.
On-Demand Cleanup Using Profiles
You can analyze disk space used by system files, such as backups, dumps, reports, log
files, and some types of artifacts. Disk management profiles are defined for groups of
system file types, and you can delete data using these profiles to free disk space.
Some data, such as configuration data, cannot be deleted.
Following are the profiles you can use for disk management:
Profile
Description
backups
Backup files created during user-initiated backup and restore
procedures.
fedb-backups
Database backup files created during system image updates
logs
Log files
malicious-artifacts
Malicious artifact files generated on the appliance
nonmaliciousartifacts
Nonmalicious artifact files generated on the appliance
reports
Report files
© 2022 FireEye Security Holdings US LLC
335
Central Management System Administration Guide
Profile
CHAPTER 22: Disk Space Management
Description
snapshots
System snapshots
sysdumps
System dumps
tcpdumps
TCP capture files
temp-files
Temporary files
For more information, see:
l
Viewing a Summary of Disk Space Use Using the CLI below
l
Viewing Disk Space Use By Profile Using the CLI on the facing page
l
Deleting Data to Free Disk Space Using the CLI on the facing page
Viewing a Summary of Disk Space Use Using the CLI
You can view a summary of disk space use for the /config, /var, and /data file systems
and the associated profiles. You should run this command to analyze disk space use.
NOTE: You cannot delete files from the /config file system. Space information for
this file system is for information purposes only.
To view a summary of disk space use:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Show the current disk space use summary:
hostname (config) # show system cleanup summary
Statistics for /config filesystem:
Space Total
182 MB
Space Used
7 MB
Space Free
175 MB
Space Available
166 MB
Space Percent Free
96%
Inodes Percent Free 99%
Statistics for /var filesystem:
Space Total
20031 MB
Space Used
2682 MB
Space Free
17348 MB
Space Available
16324 MB
Space Percent Free
86%
Inodes Percent Free 99%
Statistics for /data filesystem:
Space Total
1068532 MB
Space Used
126189 MB
Space Free
942343 MB
Space Available
888058 MB
Space Percent Free
88%
Inodes Percent Free 99%
Statistics for /data/db filesystem:
Space Total
125863 MB
Space Used
958 MB
Space Free
124905 MB
Space Available
118489 MB
336
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Space Percent Free
Inodes Percent Free
On-Demand Cleanup Using Profiles
99%
99%
Profile Name
| Description
| Occupied Space | Cleanable Space | Filesystems
====================== | ================================|===============================================
backups
| Unified Backups
|
0 MB |
0 MB | /data
fedb-backups
| FEDB Backups
|
6446 MB |
6446 MB | /data
logs
| Application log files
|
427 MB |
411 MB | /var
malicious-artifacts
| Malicious Malware Artifacts
|
0 MB |
0 MB | /data
nonmalicious-artifacts | Non-malicious Malware Artifacts |
0 MB |
0 MB | /data
reports
| Reports
|
1 MB |
1 MB | /data
snapshots
| System snapshots
|
8 MB |
5 MB | /data
sysdumps
| System dumps
|
0 MB |
0 MB | /data
tcpdumps
| TCP capture files
|
0 MB |
0 MB | /var
temp-files
| Temporary files
|
0 MB |
0 MB | /var
Viewing Disk Space Use By Profile Using the CLI
You can view disk space use by profile. You should run this command to determine the
best data to delete for a specific profile.
To view a summary of disk space use by profile:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Show the current disk space use for a profile:
hostname (config) # show system cleanup profile [backups | fedb-backups
| logs | malicious-artifacts | nonmalicious-artifacts | reports
|snapshots | sysdumps | tcpdumps | temp-files]
For profile descriptions, see On-Demand Cleanup Using Profiles on page 335.
For example, the following shows the disk space use for the logs profile:
hostname (config) # show system cleanup profile logs
Older than | Size
============|=============
365 days
|
0 MB
180 days
|
25 MB
90 days
|
212 MB
30 days
|
342 MB
7 days
|
382 MB
1 day
|
405 MB
All
|
411 MB
Deleting Data to Free Disk Space Using the CLI
After you have analyzed the disk space use, you can delete data to free the disk space you
need.
To delete data to free disk space:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
337
Central Management System Administration Guide
CHAPTER 22: Disk Space Management
2. Delete data:
hostname (config) # system cleanup profile {backups | fedb-backups |
logs | malicious-artifacts | nonmalicious-artifacts | reports
|snapshots | sysdumps | tcpdumps | temp-files} {all | older-than <no.
of days>} [force]
where:
l
l
l
all deletes all data that can be deleted for this profile
older-than <no. of days> deletes data that is older than the specified number
of days
force deletes the data as requested without prompting for confirmation
If you do not use the force option, the command prompts for confirmation.
For example, the following deletes data that matches the logs profile. It deletes only
data that can be deleted that is older than 180 days.
hostname (config) # system cleanup profile logs older-than 180
This will remove cleanable files older than 180 days for the profile
'logs'. Do you want to continue? [y/n]: y
25 MB of disk space freed.
338
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 23: Boot Manager
Utilities
The Tools menu provides access to the boot manager utilities.
In the console, the Tools menu is sometimes called Boot Menu.
Reset admin Password
Resets the factory default "admin" password. This password, which is typically
"admin," is the password used to log into the physical or serial console. For security,
the "admin" user cannot use this password to remotely log into the Web UI or CLI of
the appliance, so the password must be changed in the console during the initial
configuration of the appliance. This option is suitable if the configured "admin"
password for remote access is lost or forgotten. The "admin" user can log into the
physical or serial console using the default password, and then change it so the
password can be used for remote access as well.
Wipe Appliance Media
Wipes the appliance media. The appliance will not be usable afterward. This option is
suitable if you intend to use an RMA to replace the appliance, and have already saved
customer data using the database backup feature. For more information, see Wiping
Persistent Media on page 348.
© 2022 FireEye Security Holdings US LLC
339
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
Manufacture Appliance
Manufactures the appliance to factory settings, including its original manufacturing
parameters (such as hostname and DTI credentials.) This option is suitable if you need
to do a more complete factory reset than is possible with the reset factory CLI
commands. After you manufacture using this utility, only the original system image
version and manufacture timestamps are preserved in the system log.
Wipe Appliance Media and Manufacture Appliance
Wipes the appliance media and manufactures the appliance to factory settings. This
option is suitable if you are returning the appliance to Trellix at the end of an
evaluation so it can be used for another evaluation. For more information, see Wiping
Persistent Media on page 348.
Return to Image Boot Menu
Returns to the image boot menu, where you can boot an installed image from a
particular boot location. This option is suitable if you install a new system image
version but decide to use a previous version instead, or if you accidentally booted from
the wrong boot location.
IMPORTANT: After you select this option, pay close attention to the console so you
do not miss a series of five periods (.) displayed one second apart. Before the
console moves past the fifth period, press any key twice to return to the boot menu.
Working with the Tools Menu
The following topics describe how to access and use the Tools menu.
l
System Requirements below
l
Setting the Tools Menu Password on page 342
l
Accessing the Tools Menu on page 344
l
Disabling the Tools Menu on page 346
l
Viewing Tools Menu Availability on page 347
System Requirements
Make sure the following requirements are met.
l
Model numbers and system image versions:
l
340
Malware Analysis Version 8.0.0 or later is running on one of the following
appliance models: AX 5500, AX 5550.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with the Tools Menu
l
l
l
l
l
l
l
l
l
Central Management Version 8.1.0 or later is running on one of the
following appliance models: CM 4500, CM 7500, CM 9500.
Email Security — Server Edition Version 8.0.0 or later is running on one of
the following appliance models: EX 3500, EX 5500, EX 8500.
File Protect Version 8.0.0 or later is running on the FX 6500 model.
Endpoint Security Version 4.0.0 or later is running on one of the following
appliance models: HX 4000, HX 4400, HX 4402.
Network Security Version 8.0.0 or later is running on one of the following
appliance models: NX 1500, NX 2500, NX 2550, NX 3500, NX 4500, NX 5500,
NX 7500, NX 10450, NX 10550.
Virtual Execution Version 8.0.0 or later is running on one of the following
appliance models: VX 5500, VX 12500.
You have access to the physical or serial console (see Accessing the Physical or
Serial Console on page 73).
The minimum system image version cited above is installed on both boot partitions
on the appliance. If the appliance was not originally manufactured with that system
image version, you must perform the Upgrade Steps below to meet this requirement.
You obtained the appliance-specific preset Tools menu password from Trellix
Technical Support, or you configured another password as described in Setting the
Tools Menu Password on the next page.
Limitations
l
l
The Manufacture Appliance and Wipe Appliance Media and Manufacture
Appliance options require that the appliance was originally manufactured with a
system image that supports the Tools menu.
All logging goes to the serial console. If you use the physical console to access the
Tools menu, you will be unable to monitor the progress on the VGA monitor.
Upgrade Steps
The minimum system image version must be installed on both boot partitions before you
can access the Tools menu. Perform the steps in this section if you are upgrading from an
earlier version.
NOTE: These steps are not required if your appliance was originally manufactured
with the minimum system image version. The minimum versions are listed in
System Requirements on the previous page.
© 2022 FireEye Security Holdings US LLC
341
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
To enable the Tools menu if you are upgrading from an earlier release:
1. Fetch and install a supported system image:
hostname (config) # fenet image check
hostname (config) # show fenet image status
hostname (config) # fenet image fetch
hostname (config) # show fenet image status
hostname (config) # image install <image>
This installs the system image in one of the boot partitions.
2. Verify the boot partition for the new system image:
hostname (config) # show images
For example, on a Network Security appliance:
hostname (config) # show images
Installed images:
Partition 1:
wmps wMPS (wMPS) 8.0.0 ...
Partition 2:
wmps wMPS (wMPS) 7.9.4 ...
Last boot partition: 2
Next boot partition: 2
3. If necessary, change the Next boot partition so the appliance boots from the
partition with the new system image when it reloads:
hostname (config) # image boot next
hostname (config) # write memory
4. Reload the appliance:
hostname (config) # reload
5. Install the new system image again to put it on the other boot partition:
hostname (config) # image install <image>
6. Change the next boot partition:
hostname (config) # image boot next
hostname (config) # write memory
7. Reload the appliance:
hostname (config) # reload
If you do not want to use the default Tools menu password, you can now configure one as
described in Setting the Tools Menu Password below. Users who know the password can
access the Tools menu on any subsequent appliance reload, as described in Accessing the
Tools Menu on page 344.
Setting the Tools Menu Password
The Tools menu requires a password. There are two options:
342
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Working with the Tools Menu
Default Password. A unique password that is derived from the appliance ID is
preset on the appliance and must be obtained from Trellix Technical Support.
Configured Password. You can instead set another password in plain text or as a
hashed string. A plain-text password is hashed before it is stored.
Prerequisites
l
Admin access
Setting the Tools Menu Password in Plain Text Using the CLI
Use the commands in this section to set the Tools menu password in plain text.
To set a plain-text password:
1. Log into the appliance CLI.
2. Go to CLI configuration mode:
hostname > enable
hostame # configure terminal
3. Set the password:
hostname (config) # boot bootmgr tools password <password>
4. Save your change:
hostname (config) # write memory
NOTE: Alternatively, you can use the boot bootmgr tools password 0 <password>
command to set the password in plain text, or use the boot bootmgr tools password
command and enter the plain-text password at the prompt.
Example
The following example sets "fyd4k8q2" as the password for the Tools menu.
hostname (config) # boot bootmgr tools password fyd4k8q2
Setting the Tools Menu Password with Encryption Using the
CLI
Use the commands in this section to set the Tools menu password with a hashed string.
© 2022 FireEye Security Holdings US LLC
343
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
To set an encrypted password:
1. Log into the appliance CLI.
2. Go to CLI configuration mode:
hostname > enable
hostame # configure terminal
3. Set the password:
hostname (config) # boot bootmgr tools password 7 <password>
4. Save your change:
hostname (config) # write memory
Example
The following example sets an encrypted password for the Tools menu.
hostname (config) # boot bootmgr tools password 7
$6$xuQN2G3r$ufK5k8dUDdpp0hPETrtjBIDZ3f3PhCxGYagp2k0gvgv/YrD88GNIkUsaKRVDMsPAy
QlcGuzhRXaBpCCVPeQd1
Restoring the Default Tools Menu Password Using the CLI
Use the commands in this section to restore the default Tools menu password. You must
obtain this password from Trellix Technical Support.
To restore the default Tools menu password:
1. Log into the appliance CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Restore the password:
hostname (config) # no boot bootmgr tools password
4. Save your change:
hostname (config) # write memory
Accessing the Tools Menu
Use the procedure in this section to access the Tools menu.
To access the Tools menu:
1. Connect to the physical or serial console as described in Accessing the Physical or
Serial Console on page 73.
344
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with the Tools Menu
NOTE: If you use the physical console to access the Tools menu, you will be
unable to monitor the progress on the VGA monitor.
2. Log into the console using admin credentials.
3. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
4. Reload the appliance:
hostname (config) # reload
5. Pay close attention to the console as it reloads so you do not miss the boot:
prompt.
6. When you see the boot: prompt, press Enter.
7. Pay close attention to the console so you do not miss a series of five periods (.)
displayed one second apart.
8. Before the console moves past the fifth period, press any key twice. An image boot
menu such as the following on a Network Security appliance is displayed.
Boot Menu
--------------------------------------------------------------0: wmps wMPS (wMPS) 8.0.0...
1: wmps wMPS (wMPS) 8.0.0...
2: Tools Menu
---------------------------------------------------------------
9. Press the down arrow on your keyboard to select the 2. Tools Menu option.
10. Press Enter.
11. When prompted, enter the Tools menu password provided by your administrator.
12. The Tools menu (labeled "Boot Menu") is displayed.
Boot Menu
--------------------------------------------------------------0: Reset admin Password
1: Wipe Appliance Media
2: Manufacture Appliance
3: Wipe Appliance Media and Manufacture Appliance
4: Return to Image Boot Menu
---------------------------------------------------------------
13. Select an option (described in Boot Manager Utilities on page 339).
NOTE: If you select option 4, pay attention to the console so you do not miss a
series of five periods displayed one second apart, and then press any key twice to
access the image boot menu.
Example
The following example from a Network Security appliance accesses the Tools menu.
© 2022 FireEye Security Holdings US LLC
345
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
nx-03 (config) # reload
Configuration changed: save changes?
Configuration changes saved.
Rebooting...
...
boot:
Booting from local disk...
PXE-MOF: Exiting Intel Boot Agent.
Booting default image in 3 seconds.
...
This terminal is not active or input for output while booting.
Booting default image in 1 seconds.
Boot Menu
--------------------------------------------------------------0: wmps wMPS (wMPS) 8.0.0...
1: wmps wMPS (wMPS) 8.0.0...
2: Tools Menu
--------------------------------------------------------------Use the ^ and v keys to select which entry is highlighted.
Press enter to boot the selected image or 'p' to enter a
password to unlock the next set of features.
Highlighted entry is 2:
Booting: 'Tools Menu'
Password: ********
.......
Boot Menu
--------------------------------------------------------------0: Reset admin Password
1: Wipe Appliance Media
2: Manufacture Appliance
3: Wipe Appliance Media and Manufacture Appliance
4: Return to Image Boot Menu
--------------------------------------------------------------Use the ^ and v keys to select which entry is highlighted.
Press enter to boot the selected image or 'p' to enter a
password to unlock the next set of features.
Highlighted entry is 0:
NOTE: The 'p' option cited in the console instructions is not available.
Disabling the Tools Menu
To prevent users from accessing the Tools menu, disable the Tools menu password.
346
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with the Tools Menu
Prerequisites
l
Admin access
Disabling the Tools Menu Using the CLI
Use the commands in this section to disable the Tools menu password, which prevents
users from accessing the Tools menu.
To disable the Tools menu:
1. Log into the appliance CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Disable the password:
hostname (config) # boot bootmgr tools disable password
4. Save your change:
hostname (config) # write memory
Viewing Tools Menu Availability
You can view whether the Tools menu is available on the appliance.
Prerequisites
l
Monitor, Operator, or Admin access
Viewing Tools Menu Availability Using the CLI
Use either of the following commands to view whether users can access the Tools menu.
l
show bootvar
l
show images
If a Tools menu password is set (either the default password or a configured password),
users can access the Tools menu. If the Tools menu password is disabled, users cannot
access the Tools menu.
Examples
The following example from a Network Security appliance shows that the Tools menu
password is set, so users can access the Tools menu.
© 2022 FireEye Security Holdings US LLC
347
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
nx-05 > show bootvar
Installed images:
Partition 1:
wmps wMPS (wMPS) 7.4.0 xxx
Partition 2:
wmps wMPS (wMPS) 8.0.0 xxx
Last boot partition: 1
Next boot partition: 1
Boot manager admin password:
undisclosed password set
Boot manager tools menu password: undisclosed password set
...
The following example shows that the Tools menu password is disabled, so users cannot
access the Tools menu.
nx-01 > show images
Installed images:
Partition 1:
wmps wMPS (wMPS) 7.4.0 ...
Partition 2:
wmps wMPS (wMPS) 8.0.0 ...
No image files are available to be installed.
No image install currently in progress.
Boot manager admin password:
Boot manager tools menu password:
undisclosed password set
password disabled
Wiping Persistent Media
You can securely erase (wipe) proprietary and confidential data from the persistent media
on an appliance before you return it to Trellix at the end of an evaluation or when you
need to use a Return of Materials Authorization (RMA) to replace the appliance. The
secure erase operation overwrites every addressable byte of the media device at least once,
and then verifies that the operation succeeded.
You use the Tools (also known as Boot) menu in the boot manager to perform these actions.
The boot manager requires serial or physical console access and a password. You can
either wipe the appliance media only or wipe the appliance media and manufacture the
appliance. These options are described in Boot Manager Utilities on page 339.
The media wipe operation could take from six to ten hours, depending on the disk size.
The status of the current operation is displayed in the console so you can monitor the
progress, which is refreshed periodically.
348
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Wiping Persistent Media
Prerequisites
l
Make sure the requirements for the Tools menu are met. See System Requirements
on page 340.
Wiping Persistent Media Using the Tools Menu
Use the procedure in this section to wipe persistent media from the appliance.
To wipe persistent media:
1. Go to the Tools (displayed as Boot) menu as described in Accessing the Tools Menu
on page 344.
Boot Menu
--------------------------------------------------------------0: Reset admin Password
1: Wipe Appliance Media
2: Manufacture Appliance
3: Wipe Appliance Media and Manufacture Appliance
4: Return to Image Boot Menu
---------------------------------------------------------------
2. To only wipe the media, use the ^ and v keys to select 1: Wipe Appliance Media.
CAUTION: This option will leave the appliance unusable.
3. To both wipe the media and then manufacture the appliance, select 3: Wipe
Appliance Media and Manufacture Appliance.
4. Press Enter.
Example
The following example from a Network Security appliance accesses the Tools menu, and
then wipes the appliance media and manufactures the appliance. For brevity, some
console output is omitted.
nx-03 (config) # reload
Configuration changed: save changes?
Configuration changes saved.
Rebooting...
...
boot:
Booting from local disk...
PXE-MOF: Exiting Intel Boot Agent.
Booting default image in 3 seconds.
...
This terminal is not active for input or output while booting.
Booting default image in 1 seconds.
Boot Menu
© 2022 FireEye Security Holdings US LLC
349
Central Management System Administration Guide
CHAPTER 23: Boot Manager Utilities
--------------------------------------------------------------0: wmps wMPS (wMPS) 8.0.0...
1: wmps wMPS (wMPS) 7.9.4...
2: Tools Menu
--------------------------------------------------------------Use the ^ and v keys to select which entry is highlighted.
Press enter to boot the selected image or 'p' to enter a
password to unlock the next set of features.
Highlighted entry is 2:
Booting: 'Tools Menu'
Password: ********
.......
Boot Menu
--------------------------------------------------------------0: Reset admin Password
1: Wipe Appliance Media
2: Manufacture Appliance
3: Wipe Appliance Media and Manufacture Appliance
4: Return to Image Boot Menu
--------------------------------------------------------------Use the ^ and v keys to select which entry is highlighted.
Press enter to boot the selected image or 'p' to enter a
password to unlock the next set of features.
Highlighted entry is 3:
Booting: 'Wipe Appliance Media and Manufacture Appliance'
...
Running /etc/init.d/rcS.d/S33diskwipe
- Preparing to run diskwipe...
*** WARNING: DO NOT POWER OFF! ***
== Detecting disks to wipe
== Wiping system disks
scrub: using NNSA NAP-14.1-C patterns
scrub: please verify that device size below is correct!
scrub: scrubbing /dev/sda 1919313510400 bytes (~1787GB)
scrub: random |.......|
..................
NOTE: The 'p' option cited in the console instructions is not available.
350
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
PART IV: Appliances
l
Adding and Removing Appliances on page 353
l
Viewing and Modifying Managed Appliance Information on page 365
l
Configuring Managed Appliances on page 375
l
Using Appliance Groups and Command Profiles on page 399
l
Monitoring Aggregated Alert Data on page 415
l
Working with Reports for Managed Appliances on page 437
l
Checking Status and Health of Managed Appliances on page 485
l
Updating Managed Appliances on page 495
l
Configuring Custom IOC Feeds on page 501
l
Filtering Alerts Using Tags and Rules on page 521
© 2022 FireEye Security Holdings US LLC
351
Central Management System Administration Guide
352
PART IV: Appliances
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 24: Adding and
Removing Appliances
Appliances can be added to a Central Management network for management in two ways:
initiated by the server or initiated by the client.
Server-Initiated Connection
A Central Management administrator can add an appliance directly from the Central
Management appliance. For details, see the following section:
l
Adding an Appliance Using the Central Management Appliance on the next page.
Client-Initiated Connection
An appliance administrator can send a management request to the Central Management
appliance, and a Central Management administrator can accept or reject the request. For
details, see the following section:
l
Accepting a Management Request on page 357
Client-initiated connections use CMC rendezvous functionality to set up the client record in
the Central Management appliance. The rendezvous process requires configuration on both
the Central Management appliance and the requesting appliance. You use the cmc
rendezvous server commands on the Central Management appliance and cmc rendezvous
client commands on the managed appliance.
Connection Removal
For details about removing a managed appliance, whether the connection was initiated by
the server or the client, see the following section:
l
Removing a Managed Appliance from the Central Management Network on page 363
© 2022 FireEye Security Holdings US LLC
353
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
Adding an Appliance Using the Central
Management Appliance
A Central Management administrator can add an appliance to the Central Management
appliance. This is called a server-initiated connection.
NOTE: For procedures to follow in a NAT deployment, see Adding an Appliance in a
NAT Deployment (Using the Central Management Appliance) on page 580.
Prerequisites
l
Admin access to the Central Management appliance
l
Unique hostname for each appliance being added
l
Remote user credentials. This is a managed appliance "admin" user that the Central
Management appliance uses to log in to the appliance to establish the connection. See
User Authentication on page 554 for details about configuring the remote user.
Adding an Appliance Using the Central Management Web
UI
Use the Add New Sensor dialog box to add an appliance to the Central Management
appliance.
When you add an appliance, "password" is the initial authentication type, so a username
and password must be provided for the remote user that logs in to the appliance to
establish the connection.
354
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Adding an Appliance Using the Central Management Appliance
After the appliance is added, you can change the authentication type as described in
Configuring User Authentication Using the Web UI on page 558.
IMPORTANT! You can use the Web UI to add appliances with publicly accessible IP
addresses only. For information about adding appliances with publicly inaccessible IP
addresses, see Adding an Appliance in a NAT Deployment (Using the Central
Management Appliance) on page 580.
To add an appliance:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Actions > Add Sensor. The Add New Sensor dialog box opens.
3. In the Sensor Name box, enter a unique name that identifies the appliance.
4. In the IP Address box, enter the appliance IP address.
5. In the Username and Password boxes, enter the credentials for the remote user. These
are the credentials for an existing user on the appliance you are adding.
6. (Optional) In the Comments box, enter explanatory information about the appliance.
7. (Required for compliance mode; optional for non-compliance mode) Enter the
appliance host key (beginning with the appliance IP address) in the Host Key box. For
details, see Importing a Host Key into the Global Host-Keys Database Using the
Web UI on page 564.
8. Click Add.
The appliance is added to the list on the page, and it becomes a member of the system
group for that appliance type. You can add the appliance to a different group or create
a new group for the appliance as described in Grouping Appliances on page 399.
NOTE: See Viewing Managed Appliance Information Using the Web UI on
page 367 for information about the status indicators and the actions you can take
from this page.
Adding an Appliance Using the Central Management CLI
Use the commands in this section to add an appliance to the Central Management
appliance.
NOTE: The procedure in this section includes the basic steps for adding an
appliance. Additional options are available. See Configuring Secure Shell (SSH)
Authentication on page 553 for information about public key and host
authentication. See the CLI Command Reference for a full list of the cmc...
commands and details about their parameters and usage.
© 2022 FireEye Security Holdings US LLC
355
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
To add an appliance:
1. Log in to the Central Management CLI.
2. Enable the CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
3. Specify the appliance IP address:
cm-hostname (config) # cmc appliance <applianceID> address <IPaddress>
where applianceID is the appliance record name and IPaddress is its IP address.
IMPORTANT: Specify the IP address, not the hostname. Otherwise, if the
hostname changes later, the connection will be broken and the appliance will
need to be added again.
4. (Optional) Specify the appliance port:
cm-hostname (config) # cmc appliance <applianceID> port <port>
The port defaults to 22 if it is not specified.
5. Configure authentication for the remote user (an existing user on the appliance you
are adding):
cm-hostname (config) # cmc appliance <applianceID> authtype <authtype>
cm-hostname (config) # cmc appliance <applianceID> auth <authtype>
username <username>
cm-hostname (config) # cmc appliance <applianceID> auth <authtype>
password <password> | identity <identity>
where authtype can be password, ssh-dsa2, or ssh-rsa2. (See Configuring User
Authentication Using the CLI on page 559 for details.)
6. (Optional) Add a comment describing the appliance:
cm-hostname (config) # cmc appliance <applianceID> comment <comment>
7. (Required for compliance mode; optional for non-compliance mode) Configure the
appliance host key (beginning with the appliance IP address). For details, see
Importing a Host Key into the Global Host-Keys Database Using the CLI on
page 566.
8. Save your changes:
cm-hostname (config) # write memory
Example
cm-hostname (config) # cmc appliance Acme-NX address 172.00.00.00
cm-hostname (config) # cmc appliance Acme-NX authtype password
cm-hostname (config) # cmc appliance Acme-NX password username admin3
cm-hostname (config) # cmc appliance Acme-NX password password 12345abcde
cm-hostname (config) # cmc appliance Acme-NX comment New York NX Series
356
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Accepting a Management Request
Accepting a Management Request
A Central Management administrator can view a list of appliances that requested to be
added for management, and accept or reject them. After a request is accepted, the appliance
is added to the Central Management appliance.
This section covers the following information:
l
Requirements for Accepting a Management Connection Request below
l
Preparing to Accept a Management Request Using the CLI on the next page
l
l
l
Preparing to Accept Requests for Management Connections that Support Shifting
Appliance IP Addresses Using the CLI on the next page
Accepting a Management Request Using the Central Management Web UI on
page 360
Accepting a Management Request Using the Central Management CLI on page 361
NOTE: For procedures to follow in a NAT deployment, see Accepting a
Management Request in a NAT Deployment on page 582.
Requirements for Accepting a Management Connection
Request
To accept a management request and successfully establish and maintain the connection,
the following must be in place on the Central Management appliance:
The Central Management appliance has the rendezvous process enabled
The rendezvous process is enabled by default.
The Central Management appliance has a permanent hostname
If the hostname is changed, the connection will be broken and cannot be reset. If this
happens, the appliance must be removed from the Central Management appliance and
then added again using the new hostname.
The Central Management and requesting appliances have the same service name
The rendezvous process has an identifier (known as service name) that is set to "cmc"
by default. The Central Management appliance and the requesting appliance must
have the same service name; if you change the service name on one, you must change
it on the other as well.
Use the cmc rendezvous service-name <hostname> command to change the service
name. Use the no cmc rendezvous service-name command to restore the default
value. For details, see the CLI Command Reference.
© 2022 FireEye Security Holdings US LLC
357
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
Preparing to Accept a Management Request Using the
CLI
Follow these steps to prepare the Central Management appliance to accept or reject a
request by an appliance to be added for management.
To prepare to accept a request to be managed:
1. Log in to the Central Management CLI.
2. Verify that the rendezvous process is enabled:
cm-hostname > enable
cm-hostname # show cmc rendezvous
3. If Server rendezvous enabled: no is shown, enable the rendezvous process and
save your changes:
cm-hostname # configure terminal
cm-hostname (config) # cmc rendezvous server enable
cm-hostname (config) # write memory
Preparing to Accept Requests for Management
Connections that Support Shifting Appliance IP
Addresses Using the CLI
Follow these steps to configure the Central Management appliance to accept client-initiated
rendezvous requests for management connections that support appliance IP address changes
and automatic reconnections to the Central Management appliance.
For this feature, you will configure the Central Management appliance to accept connection
requests using one of the following methods:
l
Explicitly accept pending connection requests—The Central Management appliance is
typically configured to explicitly accept connection requests. As a Central Management
appliance administrator, you can view the list of pending rendezvous clients and then
explicitly accept all of them at once or accept selected clients one at a time.
For detailed information about explicitly accepting pending connection requests, see
Accepting a Management Request Using the Central Management Web UI on page 360
or Accepting a Management Request Using the Central Management CLI on page 361.
l
358
Automatically accept any client-initiated connection request—If you will be adding
multiple new appliances with client-initiated connections, Trellix recommends that
you temporarily configure the Central Management appliance to automatically accept
any client-initiated connection request.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Accepting a Management Request
Client-initiated connections use CMC rendezvous functionality to set up the client record in
the CMC. The Central Management Console (CMC) provides basic management and control
capabilities for the rendezvous server (Central Management appliance) and its clients
(managed appliances).
NOTE: The rendezvous process requires configuration on both the Central
Management appliance and the requesting appliance. You use the cmc rendezvous
server commands on the Central Management appliance and cmc rendezvous
client commands on the managed appliance.
To enable the appliance to accept requests for management connections that support
shifting appliance IP addresses:
1. Log in to the Central Management appliance CLI.
2. Go to CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
3. Enable CMC rendezvous functionality with support for management connections with
shifting appliance IP addresses:
cm-hostname (config) # cmc rendezvous server enable
cm-hostname (config) # cmc rendezvous server allow-shifting-ips
If you need to stop accepting client-initiated connections that support shifting IP
addresses, use the no cmc rendezvous server allow-shifting-ips command.
4. (Optional) If you will be adding multiple new appliances with client-initiated
connections, Trellix recommends that you temporarily configure the Central
Management appliance to automatically accept any client-initiated connection request.
cm-hostname (config) # cmc rendezvous server auto-accept
If you need to stop automatically accepting any client-initiated connection request, use
the no cmc rendezvous server auto-accept command.
© 2022 FireEye Security Holdings US LLC
359
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
5. Check the rendezvous configuration and state:
cm-hostname (config) # show cmc rendezvous
CMC rendezvous service name: cmc
CMC server:
Server rendezvous enabled:
yes
Auto-accept enabled:
no
Allow changing IPs from clients:
yes
Enforce appliance id checks to clients: yes
No clients awaiting approval.
Default authentication configuration for new clients:
Authentication type: ssh-dsa2
password username: admin
password password: ********
ssh-dsa2 username: admin
ssh-dsa2 identity:
ssh-rsa2 username: admin
ssh-rsa2 identity:
6. Save your changes.
cm-hostname (config) # write memory
Accepting a Management Request Using the Central
Management Web UI
Use the Connection Requests dialog box to accept (or reject) a request to be managed.
If any requests from appliances are waiting for approval, a message is displayed in the
notification bell at the top right of the Central Management Web UI.
To accept a request to be managed from an appliance:
1. If the Central Management appliance has never accepted a request for management,
ensure that it meets the requirements described in Preparing to Accept a
360
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Accepting a Management Request
Management Request Using the CLI on page 358.
2. Log in to the Central Management Web UI.
3. Do one of the following to open the Connection Requests dialog box:
l
l
Click the button in the Dashboard message.
Click the Appliances tab. The Sensors tab should be selected. Click Actions >
Waiting Connection Requests.
The IP address and hostname of the requesting appliance are displayed.
4. To approve the request and add the appliance:
a. Select its checkbox and then click Accept.
b. When prompted, confirm your action.
The appliance is added to the list on the page, and it becomes a member of the
system group for that appliance type. The appliance hostname becomes the display
name shown in the Sensor column. You can add the appliance to a different group
or create a new group for the appliance as described in Grouping Appliances on
page 399.
5. To reject the request (for example, if you do not recognize the appliance):
a. Select its checkbox and then click Reject.
b. When prompted, confirm your action.
NOTE: For information about the status indicators and the actions available from this
page, see Viewing Managed Appliance Information Using the Web UI on page 367.
Accepting a Management Request Using the Central
Management CLI
Use the commands in this section to accept or reject a request by an appliance to be added
to the Central Management appliance for management.
To accept a request to be managed:
1. If the Central Management appliance has never accepted a request for management,
ensure that it meets the requirements described in Preparing to Accept a
Management Request Using the CLI on page 358.
2. Log in to the Central Management CLI.
3. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
361
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
4. View the list of requests:
cm-hostname (config) show cmc rendezvous
5. Accept one or more requests.
l
To accept a specific appliance:
cm-hostname (config) # cmc rendezvous server accept client
<hostname>
where <hostname> is the hostname of the requesting appliance.
l
To accept all appliances in the list:
cm-hostname (config) # cmc rendezvous server accept all
6. Save your changes.
hostname (config) # write memory
To reject a request to be managed:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the list of requests:
cm-hostname (config) # show cmc rendezvous
3. Reject one or more requests:
l
To reject a specific appliance:
cm-hostname (config) # no cmc rendezvous server accept client
<hostname>
where <hostname> is the hostname of the requesting appliance.
l
To reject all appliances in the list:
cm-hostname (config) # no cmc rendezvous server accept all
4. Save your changes.
hostname (config) # write memory
Example
In this example, the request from the nx-02 appliance is accepted and the request from the
nx-04 appliance is rejected.
hostname (config) # show cmc rendezvous
CMC rendezvous service name: cmc
CMC server:
Server rendezvous enabled: yes
Auto-accept enabled:
no
Clients waiting approval:
nx-02 (172.14.10.00)
362
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Removing a Managed Appliance from the Central Management Network
nx-04 (172.14.20.00)
...
hostname (config) # cmc rendezvous server accept client nx-02
hostname (config) # no cmc rendezvous server accept client nx-04
hostname (config) # write memory
Removing a Managed Appliance from the
Central Management Network
When you remove a managed appliance from the Central Management network, all
aggregated data (including alert information) associated with the appliance is also
removed. When you subsequently add back the appliance, the data is restored, but all
alerts generated by the appliance are assigned new IDs.
IMPORTANT! Because the alerts have new IDs when an appliance is added back
to the Central Management appliance, Endpoint Security links for alerts will break
if the alerts were generated by the appliance before it was removed from the Central
Management appliance.
Prerequisites
l
Admin access
Removing a Managed Appliance from the Central
Management Network Using the Web UI
Use the Sensors page to remove an appliance from the Central Management network.
NOTE: The Un-Enroll And Delete link is used to remove a Network Security sensor
from an MVX cluster and then remove it from the Central Management appliance.
For details, refer to the MVX Smart Grid Guide or the Cloud MVX Guide.
© 2022 FireEye Security Holdings US LLC
363
Central Management System Administration Guide
CHAPTER 24: Adding and Removing Appliances
To remove an appliance:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Select > Delete in the row for the appliance you to want to remove.
3. If the Network Security sensor is enrolled with the MVX cluster, click Un-Enroll And
Delete in the row for the sensor you want to remove.
4. When prompted, click OK to confirm your action.
NOTE: Removing an appliance can take a long time if the Central Management
appliance is busy aggregating data.
Removing a Managed Appliance from the Central
Management Network Using the CLI
Use the commands in this section to remove an appliance from the Central Management
network.
To remove an appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the appliance:
hostname (config) # no cmc appliance <applianceName>
3. Save your changes:
hostname (config) # write memory
NOTE: Removing an appliance can take a long time if the Central Management
appliance is busy aggregating data.
Example
This example removes the FX-03 appliance from management.
hostname (config) # no cmc appliance FX-03
364
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 25: Viewing and
Modifying Managed Appliance
Information
You can view information about managed appliances in the Central Management Web UI
or CLI. You might need to modify information about a managed appliance. Reasons for
doing so include:
l
The password for the remote user changes due to password change policies. (This is
the user that logs in to the appliance to establish the connection.)
l
You need to change the remote user authentication type to SSH-DSA2 or SSH-RSA2.
l
The appliance IP address changes.
l
You need to provide the global host-key for a managed appliance because global
host-key authentication is enforced.
The following table describes the managed appliance information.
Appliance Information
Field
Description
Sensor
The unique name that identifies the appliance.
Product
The appliance type (for example, AX, EX, FX, HX, NX,
NX - IPS, Network Security [SmartVision Edition]).
IP
The IP address of the appliance's management interface.
Sensor ID
The unique sensor ID of the appliance.
Model
Number
The model number of the appliance.
© 2022 FireEye Security Holdings US LLC
365
Central Management System Administration
Guide
366
CHAPTER 25: Viewing and Modifying Managed Appliance
Information
Field
Description
Cluster
Enrollment
The MVX cluster with which the sensor is enrolled and
the broker to which it is connected. For details about
cluster enrollment, refer to the MVX Smart Grid Guide or
the Cloud MVX Guide.
Connection
The status of the connection between the Central
Management appliance and the managed appliance.
Public Key
Used
The SSH-DSA2 or SSH-RSA2 key used to authenticate the
remote user the Central Management appliance uses to log
in to the appliance for management. This field is empty if
password authentication is being used.
Health
The status of the appliance health.
Last Contact
The last time the Central Management appliance contacted
the managed appliance to get its status and health check
data.
Last
Connected
The last time the Central Management appliance and the
managed appliance connected to each other, either initially
or after a broken connection was restored.
Last Broken
The last time the Central Management appliance and the
managed appliance lost their connection.
Member
Groups
The groups of which the appliance is a member, including
the reserved system group.
EULA
Whether the terms of the Trellix End User License
Agreement (EULA) were accepted when the appliance was
first configured.
Version
The version of the appliance's software image.
Security
Content
Version
The version of the security content installed on the
appliance.
Timestamp
(UTC)
The last time security content was generated for the
appliance.
Guest Image
Version
The guest images profiles installed on the appliance.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing Managed Appliance Information Using the Web UI
Field
Description
Enabled
(CLI only) Whether the appliance can be managed by the
Central Management appliance .
Version
compatible
Whether the Central Management appliance supports this
version of the appliance.
Prerequisites
l
Monitor, Operator, or Admin access
Viewing Managed Appliance Information
Using the Web UI
Use the Sensors page to view information about managed appliances.
For information about tasks you can perform from this page, see:
l
l
Configuring User Authentication Using the Web UI on page 558
Importing a Host Key into the Global Host-Keys Database Using the Web UI on
page 564
l
Creating and Managing Groups Using the Web UI on page 400
l
Adding Appliances to Groups Using the Web UI on page 404
l
Modifying Managed Appliance Information Using the Web UI on page 371
l
Checking Status and Health of Managed Appliances Using the Web UI on page 486
l
Removing a Managed Appliance from the Central Management Network Using the
Web UI on page 363
See Appliance Information on page 365 for a description of the fields on the page.
© 2022 FireEye Security Holdings US LLC
367
Central Management System Administration
Guide
CHAPTER 25: Viewing and Modifying Managed Appliance
Information
NOTE: The Create HA Pair link is used to create a Network Security high
availability (HA) pair. For details, see the Network Security High Availability Guide.
To view appliance information:
1. Click the Appliances tab. The Sensors tab should be selected.
2. By default, appliances in all groups are displayed. To filter by appliance group,
select a group in the Sensor Group list.
3. By default, ten appliances are displayed on each page. To show all appliances on
one page, click Show All. To return to the paginated view, click paginate.
4. To view detailed information about an appliance, click the appliance name in the
Sensor column.
368
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing Managed Appliance Information Using the Web UI
5. To determine how the connection between the Central Management appliance and
the managed appliance was initiated, rest your cursor over the icon in the
Connection column. If the Central Management appliance initiated the connection,
server-initiated is displayed. If the appliance initiated the connection, clientinitiated is displayed.
© 2022 FireEye Security Holdings US LLC
369
Central Management System Administration
Guide
CHAPTER 25: Viewing and Modifying Managed Appliance
Information
Viewing Managed Appliance Information
Using the CLI
Use the commands in this section to view information about managed appliances.
NOTE: See Appliance Information on page 365 for a description of the command
output.
To view appliance information:
1. Go to CLI enable mode:
hostname > enable
2. View basic appliance information:
hostname # show cmc appliances
3. View the groups to which the appliances belong:
hostname # show cmc groups
4. View detailed information about a specific appliance:
hostname # show cmc appliances <applianceName>
Example
This example shows basic information about the three appliances this Central
Management appliance manages.
hostname # show cmc appliances
Appliance FX-03:
Address:
172.16.109.163
Enabled:
yes
Connected:
yes (server-initiated)
Status check OK:
no
Version compatible:
yes
Appliance HX-05:
Address:
Enabled:
Connected:
370
10.2.201.20
yes
yes (server-initiated)
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Status check OK:
Version compatible:
Appliance NX-04:
Address:
Enabled:
Connected:
Status check OK:
Version compatible:
Modifying Managed Appliance Information Using the Web UI
yes
no
172.16.74.50
yes
yes (server-initiated)
yes
yes
NOTE: For an example of the show cmc groups command output, see Adding
Appliances to Groups Using the CLI on page 404. For an example of the show cmc
appliances <applianceName> command output, see Checking Status and Health of
Managed Appliances Using the CLI on page 488.
Modifying Managed Appliance
Information Using the Web UI
Use the Edit Sensor page to modify information about a managed appliance.
To modify appliance information:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Select > Edit in the row for the appliance you need to modify. The Edit Sensor
dialog box opens.
3. Edit the fields as needed and then click Update.
4. Verify that the updated information is displayed in the row for the appliance.
IMPORTANT! The Edit menu item is not available if the managed appliance
initiated the connection to the Central Management appliance, as described in
Accepting a Management Request on page 357 and the System Administration Guide
or Administration Guide for the appliance.
© 2022 FireEye Security Holdings US LLC
371
Central Management System Administration
Guide
CHAPTER 25: Viewing and Modifying Managed Appliance
Information
Modifying Managed Appliance
Information Using the CLI
Use the commands in this section to modify information about managed appliances.
CAUTION! Do not change an appliance's hostname if the appliance initiated the
connection to the Central Management appliance.
NOTE: This section does not include all appliance modification commands. For a
full list of commands, see the cmc appliance <applianceName> commands in the
CLI Command Reference.
To modify appliance information:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. To change the appliance IP address:
hostname (config) # cmc appliance <applianceName> address <ipAddress> |
<hostname>
3. To rename the appliance:
hostname (config) # cmc appliance <applianceName> rename <newName>
4. To add or modify a comment about the appliance:
hostname (config) # cmc appliance <applianceName> comment "<comment>"
where commentText must be enclosed in double quotation marks.
5. To change the remote user:
hostname (config) # cmc appliance <applianceName> auth password
username <username>
6. To change the password:
hostname (config) # cmc appliance <applianceName> auth password
password <password>
7. Verify your changes:
hostname (config) # show cmc appliance <applianceName>
8. Save your changes:
hostname (config) # write memory
372
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Modifying Managed Appliance Information Using the CLI
NOTE: This procedure shows how to change the credentials for password
authentication. For information about changing ssh-dsa2 and ssh-rsa2
authentication credentials, see Configuring User Authentication Using the CLI on
page 559. To configure a host key for global host-key authentication, see Importing a
Host Key into the Global Host-Keys Database Using the CLI on page 566.
Example
This example changes the NX-04 appliance name and comment.
hostname (config) # cmc appliance NX-04 rename NX-07
hostname (config) # cmc appliance NX-07 comment "Network Security appliance"
© 2022 FireEye Security Holdings US LLC
373
Central Management System Administration
Guide
374
CHAPTER 25: Viewing and Modifying Managed Appliance
Information
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 26: Configuring
Managed Appliances
When an appliance is under the management of the Central Management appliance,
appliance configuration tasks can be performed from either the Central Management
appliance or the managed appliances. However, Trellix recommends making configuration
changes centrally from the Central Management appliance instead of from the managed
appliances for the following reasons:
l
l
It is more efficient because the tasks can be performed from a single interface—the
Central Management Web UI or CLI.
Changes you make on individual appliances could inadvertently override global
settings for managed appliances. (By default, you cannot enter configuration mode
in the CLI of a managed appliance until you confirm that you understand that this
could happen.)
You can centrally configure settings for managed appliances using the Central
Management Web UI (primarily under the Appliance Settings tab) or by using the cmc
execute commands in the Central Management CLI.
Prerequisites
l
l
Admin access to use the cmc execute commands
Admin access to most Appliance Settings pages, such as User Accounts and
Appliance Licenses. Admin or Operator access to some Appliance Settings pages,
such as Network, Login Banner, and YARA Rules.
© 2022 FireEye Security Holdings US LLC
375
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Configuring Managed Appliances Using
the Web UI
Use the Appliance Settings pages to configure managed appliances. Only appliance setting
options specific to the appliances currently being managed by the Central Management
appliance are displayed on the sidebar under the Appliance Settings tab. For example, in
the following illustration, the Inline Operational Modes tab is only displayed for managed
Network Security appliances.
On the individual settings pages, only information specific to the appliances currently
being managed is displayed. For example, only license notifications specific to those
appliances are displayed in the Appliance Settings: Appliance Licenses page.
When a single appliance is selected on a common settings page, the Write to group control
is displayed at the top of the page. If the control is set to On when you apply a change, the
change is pushed to all appliances in the group selection. For example, in the following
illustration, after you click Add User, Jim will be added to all appliances being managed
by the Central Management appliance because All Groups is selected as the group. (If a
specific group were selected, he would be added to all of the appliances in that group.)
NOTE: If a change is related to a new feature, the change will only be applied to
those appliances running the minimum required version.
376
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Configuring Network Settings for Managed Appliances
Using the Web UI
Use the Appliance Settings: Network page to configure network settings on managed
appliances.
To configure network settings:
1. Click Settings and then select Appliance Settings.
2. Click Network in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
Setting the Appliance Date and Time Manually on
Managed Appliances Using the Web UI
Use the Appliance Settings: Date and Time page to set the date and time manually on
managed appliances.
To set the date and time:
1. Click Settings and then select Appliance Settings.
2. Click Date and Time in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
Managing Licenses for Managed Appliances Using the
Web UI
Use the Appliance Settings: Appliance Licenses page to manage licenses on managed
appliances.
To manage licenses:
1. Click Settings and then select Appliance Settings.
2. Click Appliance Licenses in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
© 2022 FireEye Security Holdings US LLC
377
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Configuring NTP Servers for Managed Appliances Using
the Web UI
Use the Appliance Settings: Date and Time page to configure NTP servers on managed
appliances.
To configure NTP servers:
1. Click Settings and then select Appliance Settings.
2. Click Date and Time in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
Configuring System Email Settings for Managed
Appliances Using the Web UI
Use the Appliance Settings: Email page to configure system email settings on managed
appliances.
To configure system email settings:
1. Click Settings and then select Appliance Settings.
2. Click Email in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
Configuring DTI Network Settings for Managed
Appliances Using the Web UI
Use the Appliance Settings: DTI Network page to configure DTI network settings on
managed appliances.
To configure DTI network settings:
1. Click Settings and then select Appliance Settings.
2. Click DTI Network in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
378
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Customizing Appliance Login Messages for Managed
Appliances Using the Web UI
Use the Appliance Settings: Login Banner page to customize the messages users see when
they log in to managed appliances.
To customize login messages:
1. Click Settings and then select Appliance Settings.
2. Click Login Banner in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Administration Guide or Administration
Guide for the managed appliance.
Configuring Guest Images for Managed Appliances Using
the Web UI
NOTE: Guest images will not be available on a Network Security or File Protect
sensor or sensor-enabled Network Security integrated appliance.
Use the Appliance Settings: Guest Images page to view guest images on managed
appliances.
To view guest images:
1. Click Settings and then select Appliance Settings.
2. Click Guest Images in the sidebar.
3. (Optional) Use the controls at the top of the page to filter the results.
4. Configure settings as described in the User Guide for the managed appliance.
Uploading Certificates to Managed Appliances Using the
Web UI
Use the Appliance Settings: Certificates/Keys page to upload certificates to managed
appliances.
To upload certificates:
1. Click Settings and then select Appliance Settings.
2. Click Certificates/Keys in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Security Guide.
© 2022 FireEye Security Holdings US LLC
379
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Managing Users on Managed Appliances Using the Web
UI
Use the Appliance Settings: User Accounts page to manage users on managed appliances.
To manage user accounts:
1. Click Settings and then select Appliance Settings.
2. Click User Accounts in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the System Security Guide.
Configuring Event Notifications for Managed Appliances
Using the Web UI
IMPORTANT! Do not configure notifications for managed appliances (and remove
any existing notifications) if you are using centralized alert management as
described in Centralized Notifications on page 415.
Use the Appliance Settings: Notifications page to configure event notifications on
managed appliances.
To configure event notifications:
1. Click Settings and then select Appliance Settings.
2. Click Notifications in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the User Guide for the managed appliance. For
IPS-enabled Network Security appliances, configure settings as described in the
IPS Feature Guide.
Configuring File Types for Managed Malware Analysis
Appliances to Analyze Using the Web UI
Use the Appliance Settings: Malware File Assoc. page to configure the file types managed
Malware Analysis appliances should analyze.
NOTE: You must explicitly enable the display of this page. To do so, use the cmc
execute appliance <applianceID> command "guest-images file-association
display on" command in the CLI configuration mode.
380
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
To configure file types for analysis:
1. Click Settings and then select Appliance Settings.
2. Click Malware File Association in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Malware Analysis User Guide.
Generating Reports for Managed Appliances Using the
Web UI
Use the Generate Report page to generate static reports for managed appliances.
To generate static reports:
1. In the Web UI, choose Reports > Static Reports.
2. Generate the static reports as described in the User Guide for the managed appliance.
For information about generating a SmartVision alerts report, see the
Network Security SmartVision Feature Guide.
For SmartVision appliances, generate the SmartVision Alert static report as
described in the Network Security SmartVision Feature Guide. A SmartVision appliance
can be any of the following:
o
SmartVision Edition sensor
o
SmartVision-enabled Network Security sensor
o
SmartVision-enabled Network Security integrated appliance
You can generate a SmartVision Alerts report from the Web UI only. A
SmartVision Alerts report cannot be customized.
For IPS-enabled Network Security appliances, generate the static reports as described
in the Network Security IPS Feature Guide.
Scheduling Reports for Managed Appliances Using the
Web UI
Use the Schedule Report page to schedule static or custom reports for managed
appliances.
You can schedule custom reports that have been generated for managed Email
Security — Server Edition, Network Security, and File Protect appliances if you select
the Make Schedulable checkbox in the Reports > Custom Reports page on the
Central Management appliance.
© 2022 FireEye Security Holdings US LLC
381
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
To schedule static reports:
1. In the Web UI, choose Reports > Schedule Reports.
2. Schedule the static reports as described in the User Guide for the managed appliance.
For IPS-enabled Network Security appliances, schedule the static reports as
described in the IPS Feature Guide.
NOTE: You can schedule a SmartVision Alerts report from the Web UI only.
A SmartVision Alerts report cannot be customized.
To schedule custom reports:
1. In the Central Management appliance Web UI, choose Reports > Schedule Reports.
2. In the Report Type drop-down menu under "Custom Reports", select the custom
report that has been generated for managed Email Security — Server Edition,
Network Security, and File Protect appliances.
3. In the Scheduled drop-down menu, set the time frequency:
l
hourly
l
daily
l
weekly
l
monthly
4. In the Time drop-down menu, set the time of day in hours and minutes (00:00).
5. If you selected a weekly report, specify the report day of the week in the WeekDay
field.
6. If you selected a monthly report, specify the report day of the month in the
MonthDay field.
7. In the Delivery drop-down menu, specify the delivery method. The default delivery
is email.
l
email—Deliver the custom report as a file attached to email.
l
file—Deliver the custom report as a file linked from the Web UI.
8. In the Time Frame drop-down menu, select the time period for this custom report:
l
past day—Report covers analysis generated during the past 24 hours.
l
past week—Report covers analysis generated during the past 7 days.
l
past month—Report covers analysis generated during the past 1 month.
l
past 3 months—Report covers analysis generated during the past 3 months.
9. Click Schedule Report. The scheduled report is added to the top of the scheduling
list.
382
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Enabling or Disabling Riskware Detection Custom Policy
Rules for Managed Appliances Using the Web UI
When riskware detection is enabled on a managed Network Security or Email Security —
Server Edition appliance, you can use the Appliance Settings > Riskware Policy page to
enable or disable a particular policy rule. When you enable at least one matched policy
rule on a managed Network Security or Email Security — Server Edition appliance, you
can have the managed appliance generate a riskware alert on a nonmalicious submission.
For managed Email Security — Server Edition appliances, you can also choose to block an
email from being delivered to the intended recipient.
For more information about this feature, see the Network Security Guide or Email Security —
Server Edition User Guide.
To enable or disable riskware detection custom policy rules:
1. Click the Settings and then select Appliance Settings.
2. Click Riskware Policy in the sidebar.
3. Configure settings as described in the Network Security Guide or Email Security —
Server Edition User Guide.
Configuring Inline Operational Modes for Managed
Network Security Appliances Using the Web UI
Use the Appliance Settings: Interfaces - Operational Modes page to configure inline
operational modes for managed Network Security appliances.
NOTE: SmartVision Edition sensors and SmartVision-enabled Network Security
sensors and integrated appliances are not supported in inline deployments. These
appliances must be deployed out-of-band using a TAP device. For more information,
see “SmartVision Appliance Placement and Operational Mode” in the Network
Security SmartVision Feature Guide.
To configure operational modes:
1. Click Settings and then select Appliance Settings.
2. Click Inline Operational Modes in the sidebar.
3. (Optional) Use controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
© 2022 FireEye Security Holdings US LLC
383
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Configuring Alert Policy Exceptions for Managed
Network Security Appliances Using the Web UI
Use the Settings > Alert Policy Exceptions page to configure policy exceptions that
customize inline operations on managed Network Security appliances.
To configure policy exceptions:
1. Click Settings and then select Appliance Settings in the sidebar.
2. Click Alert Policy Exceptions in the sidebar.
3. (Optional) Use controls at the top of the page to define the scope of the changes.
4. Configure settings as described "Alert Policy Exceptions" in the Network Security
User Guide.
Configuring Whitelists for Managed Network Security
Appliances Using the Web UI
Use the Appliance Settings: Whitelists page to configure whitelists for inline operation on
managed Network Security appliances.
To configure inline whitelists:
1. Click Settings and then select Appliance Settings.
2. Click Whitelists in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
Defining Filters for Managed Network Security
Appliances Using the Web UI
Use the Filters page to define filters for events on managed Network Security appliances.
To define filters:
1. Click Alerts and then select NX.
2. Click Filters.
3. Configure settings as described in the Network Security User Guide.
384
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Uploading YARA Rules to Managed Appliances Using the
Web UI
IMPORTANT! YARA rules are not supported on a Network Security or File Protect
sensor or sensor-enabled Network Security integrated appliance.
Use the Appliance Settings: YARA Rules page to upload YARA rules for malware
analysis to managed Network Security appliances running Release 7.7.0 or later, managed
Email Security — Server Edition appliances running release 7.9.0 or later, managed Virtual
Execution appliances, and managed File Protect appliances running Release 8.0.0 or later.
To upload YARA rules:
1. Click Settings and then select Appliance Settings.
2. Click YARA Rules in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
IMPORTANT! If the scope includes appliances that are not running the
minimum supported release, a message informs you that the changes were
not applied to those appliances.
4. Configure and upload YARA rules as described in the Network Security User Guide,
the Email Security — Server Edition User Guide, Virtual Execution Administration Guide,
or File Protect User Guide.
Uploading Custom Rules to Managed Network Security
Appliances Using the Web UI
Use the Appliance Settings: Custom Rules page to upload custom rules for malware
analysis to managed Network Security appliances.
IMPORTANT: This page is displayed only when the custom rules feature is
enabled using the Network Security CLI. To enable the feature, enter the fenet
security-content custom rule enable command in the CLI configuration mode.
To upload custom rules:
1. Click Settings and then select Appliance Settings.
2. Click Custom Rules in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
IMPORTANT! If the scope includes appliances that are not running the
minimum supported release, a message informs you that the changes were
not applied to those appliances.
4. Upload custom rules as described in the Network Security User Guide.
© 2022 FireEye Security Holdings US LLC
385
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Configuring Forensic Analysis Integration on Managed
Network Security Appliances Using the Web UI
Use the Appliance Settings: Forensics page to integrate with packet analyzer applications
that perform full packet capture and analysis for specific target and source IP addresses.
Integrations with Solera Networks, RSA NetWitness, and PX Technology are supported.
This page is displayed only when the integrations are enabled using CLI commands from
both the Network Security CLI and theCentral Management CLI.
l
Solera Networks—Use the forensic analysis enable command.
l
RSA NetWitness—Use the netwitness analysis enable command.
l
PX Technology—Use the npulse analysis enable command.
To configure forensic analysis integration:
1. Click Settings and then select Appliance Settings.
2. Click Forensics in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure the integration as described in the Network Security User Guide.
Configuring IPS Settings for Managed Network Security
Appliances Using the Web UI
Use the IPS tab on managed IPS-enabled Network Security appliances to view IPS events,
enable and disable IPS-related features, manage policies and monitoring interfaces, and
define custom IPS rules.
To configure IPS settings:
1. Click the IPS tab at the top of the page.
2. Configure settings as described in the IPS Feature Guide.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
386
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Configuring IPS Policy Synchronization for Managed
Network Security Appliances Using the Web UI
To configure IPS policy synchronization among managed Network Security appliances, use
the Configure tab in the IPS Policy Sync page. Use the Configuration tab to specify two or
more managed Network Security appliances: the appliance whose IPS policy is to be used as
the source of the policy synchronization job and one or more appliances that are to be
updated.
The sync job fetches the IPS policies from the master IPS policy and caches them on the
Central Management appliance. The cached policies are used to update the recipient
appliances.
To configure IPS policy synchronization:
1. Choose IPS > IPS Policy Sync. The Configure tab is displayed by default.
2. Click Select/Change Master Policy, select the managed appliance, and click Save.
3. Select one or more managed appliances to receive the cached IPS policies.
4. Click Sync at the top right side of the list, then click Sync in the confirmation dialog box.
5. To see the progress of the synchronization, click the Sync Jobs tab.
l
l
The name of the source appliance you selected in step 2 appears in the
Master Policy column of the tab.
The names of the recipient appliances you selected in step 2 appear in the
Destination Appliances column of the tab.
Checking the Status of IPS Policy Synchronization for
Managed Network Security Appliances Using the Web UI
Use the Sync Jobs tab in IPS Policy Sync page to check the status of IPS policy synchronization
among managed Network Security appliances.
To check the status of IPS policy synchronization:
1. Choose IPS > IPS Policy Sync. The Configure tab is displayed by default.
2. Click the Sync Jobs tab.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
© 2022 FireEye Security Holdings US LLC
387
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
4. (Optional) Specify any of the following filtering criteria, then click Apply at the bottom of
the filtering panel.
Date Range
Modify the time range using any of the following methods:
l
Edit the time and date range specified in the text box.
l
Select a predefined time range, from Past Hour to Past 1 Year.
l
Select Custom, specify a time and date range.
Master Policy
Enter the name of the master policy you want to view.
Destination Appliances
Enter the name of a managed Network Security appliance.
Last Updated Time
Select the last update time.
Sync Status
Select the status of the IPS policy synchronization jobs you want to view:
l
Failed
l
In Progress
l
Partial Complete
l
Queued
l
Success
5. To view details about a synchronization job displayed in the list, click the down arrow
to expand the entry.
Configuring SSL Interception for Managed Network
Security Appliances Using the Web UI
Use the Appliance Settings: SSL Intercept page to configure SSL interception.
SSL/TLS protocols provide a secure communication between clients and servers. SSL/TLS
traffic (also referred to as HTTPS) can be a security risk that can hide malicious traffic and
user activity. Without SSL interception, the Network Security appliance cannot inspect
encrypted traffic for indicators of malicious activity.
The SSL interception feature enables decryption and inspection of HTTPS traffic. The SSL
interception feature allows the Network Security appliance to act as a proxy to intercept
and to decrypt HTTPS traffic. The Network Security appliance uses certificates to establish
a trusted third-party (man in the middle, or MitM) connection between the client and
server.
388
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
To configure SSL interception:
1. Click Settings and then select Appliance Settings.
2. Click SSL Intercept in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
Configuring the Helix Integration for Managed Network
Security Appliances Using the Web UI
Use the Appliance Settings: Evidence Collector page to enable the integration between
Helix and the managed Network Security appliance to allow the Evidence Collector
module on the managed Network Security appliance to send the network event logs to
Helix for further analysis.
To configure the Helix Integration:
1. Click Settings and then select Appliance Settings.
2. Click Evidence Collector in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
Configuring the ICAP Integration for Managed Network
Security Appliances Using the Web UI
Use the Appliance Settings: ICAP page to configure the Internet Content Adaptation
Protocol (ICAP) integration so that the managed Network Security appliance can act as an
ICAP server to perform signature and callback detection and malware analysis on ICAPencapsulated data from a proxy server running an ICAP client.
To configure the ICAP Integration:
1. Click Settings and then select Appliance Settings.
2. Click ICAP in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
© 2022 FireEye Security Holdings US LLC
389
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
Configuring Port Mirroring for Managed Network
Security Appliances Using the Web UI
Use the Appliance Settings: Port Mirroring page to configure port mirroring on the
managed Network Security appliance. Two types of port mirroring are supported—port
mirroring for all traffic types (including SSL encrypted traffic) and SSL decryption
mirroring. You can configure and enable each feature separately.
To configure port mirroring:
1. Click Settings and then select Appliance Settings.
2. Click Port Mirroring in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Network Security User Guide.
Allowing Increased Detection for Managed Appliances
Using the Web UI
Use the Appliance Settings: Increased Detection page to select options for sending
additional information to Trellix for analysis to increase detection rates. These options,
which Trellix recommends, are disabled by default. The settings are applied globally to
managed appliances running Release 7.8.0 or later.
NOTE: See your Trellix sales representative for more information.
To allow increased detection:
1. Click Settings and then select Appliance Settings.
2. Click Increased Detection.
3. Select the Suspicious metadata checkbox to send metadata your appliance flags as
"likely suspicious" to Trellix for analysis. This may result in more false positives,
but will also increase detection rates for actual malware. If you do not select this
option, then only metadata flagged as "malicious" will be sent to Trellix.
390
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
4. Select the Suspicious file checkbox to send files that your appliance flags as "likely
malicious" to Trellix for analysis. This may result in more false positives being sent
to Trellix for analysis, but will also increase detection rates for actual malware.
5. Click Apply.
NOTE: Alternatively, you can click a link on the Central Management Dashboard to
open a dialog box with the same options. After you select the options, the link is no
longer displayed.
Enabling Advanced URL Defense on Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Appliance Settings: Advanced URL Defense page to globally enable or disable the
Advanced URL Defense feature on all qualified managed Email Security — Server Edition
appliances that are connected or will be connected to this Central Management appliance.
This feature sends URLs in emails to Trellix for analysis to increase detection rates. An
Email Security — Server Edition appliance is qualified if it has a two-way sharing
CONTENT_UPDATES license and is running Release 7.8.0 or later. (For more information
about this feature, see the Email Security — Server Edition User Guide. )
IMPORTANT! This feature is disabled by default, even on Email Security — Server
Edition appliances that had the feature enabled before upgrading to Release 7.8.0.
NOTE: If you enable or disable this feature on a standalone Email Security — Server
Edition appliance, and then add that appliance to the Central Management
appliance, the global Central Management setting will override the standalone
Email Security — Server Edition setting.
To enable Advanced URL Defense:
1. Click Settings and then select Appliance Settings.
2. Click Advanced URL Defense in the sidebar.
3. Select the Enable Advanced URL Defense checkbox.
4. Click Apply to All.
© 2022 FireEye Security Holdings US LLC
391
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
NOTE: Alternatively, you can click a link on the Central Management Dashboard to
navigate to this page. After you enable the feature, the link is no longer displayed.
Configuring Email MTA Settings for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Appliance Settings: Email MTA page to configure an MTA (Mail Transfer Agent)
so email can pass through and be analyzed by managed Email Security — Server Edition
appliances.
To configure email MTA settings:
1. Click Settings and then select Appliance Settings.
2. Click Email MTA in the sidebar.
3. (Optional) Use the section at the top of the page to define the scope of the changes.
4. Configure settings as described in the Email Security — Server Edition User Guide.
Configuring Email Policy Using the Web UI
Use the Appliance Settings: Email Policy page to configure analysis and post-analysis
policies for managed Email Security — Server Edition appliances. To configure quarantine
settings for the managing Central Management appliance, use the CM Settings: Email
Quarantine Policy page.
To configure email policy:
1. Do one of the following:
l
Click Settings and then select Appliance Settings.
l
Click Settings and then select CM Settings.
2. Click Email Policy (for managed appliance settings) or Email Quarantine Policy (for
CM settings) in the sidebar.
3. (Optional) Use section at the top of the page to define the scope of the changes.
4. Configure settings as described in the Email Security — Server Edition User Guide.
Configuring Impersonation Rules Using the Web UI
Use the Appliance Settings: Impersonation page to configure impersonation rules on
managed appliances.
392
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
To configure impersonation rules:
1. Click Settings and then select Appliance Settings.
2. Click Impersonation in the sidebar.
3. Click Add.
4. Specify all valid names and email addresses for an individual, separating multiple
entries with commas.
5. Click Add.
Configuring Rules on an Allowed List for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Appliance Settings: Allowed List page to configured rules on an allowed list,
which allows you to control which messages can be bypassed based on the matched email
entries.
IMPORTANT! Trellix recommends that you apply the same configuration changes
on all managed appliances. If you edit a rule that is not common to all appliances
and then apply the rule to the appliance group, the edited rule will be applied to all
appliances in that group, including those appliances that did not have the rule.
To configure rules:
1. Click Settings and then select Appliance Settings.
2. Click Allowed List in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Email Security — Server Edition User Guide.
Configuring Rules on a Blocked List for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Appliance Settings: Blocked List page to configured rules on a blocked list, which
allows you to control which messages must be considered as malicious based on the
matched email entries.
IMPORTANT! Trellix recommends that you apply the same configuration changes
on all managed appliances. If you edit a rule that is not common to all appliances
and then apply the rule to the appliance group, the edited rule will be applied to all
appliances in that group, including those appliances that did not have the rule.
© 2022 FireEye Security Holdings US LLC
393
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
To configure rules:
1. Click Settings and then select Appliance Settings.
2. Click Blocked List in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Email Security — Server Edition User Guide.
Configuring Attachment Decryption Settings for
Managed Email Security — Server Edition Appliances
Using the Web UI
Use the Appliance Settings: Attachment decryption page to configure a list of password
candidates, list of keyword candidates, and a list of ignored word candidates the Email
Security — Server Edition appliance can use to decrypt password-encrypted malware
objects.
To configure attachment decryption settings:
1. Click Settings and then select Appliance Settings.
2. Click Attachment decryption in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Email Security — Server Edition User Guide.
Configuring Retroactive Remediation for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Appliance Settings: Remediation page to configure settings for retroactive
remediation of retroactively detected malware on the Email Security — Server Edition
appliance.
To configure retroactive remediation settings:
1. Click Settings.
2. Click Remediation.
3. Enable remediation and configure settings as described in the Email Security —
Server Edition User Guide.
394
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the Web UI
Configuring Malware Analysis Settings for Managed
Malware Analysis Appliances Using the Web UI
Use the Appliance Settings: Malware Analysis page to configure malware analysis
settings on managed Malware Analysis appliances.
To configure malware analysis settings:
1. Click Settings and then select Appliance Settings.
2. Click Malware Analysis in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Malware Analysis User Guide.
Configuring File Types for Managed Malware Analysis
Appliances to Analyze Using the Web UI
Use the Appliance Settings: Malware File Assoc. page to configure the file types managed
Malware Analysis appliances should analyze.
NOTE: You must explicitly enable the display of this page. To do so, use the cmc
execute appliance <applianceID> command "guest-images file-association
display on" command in the CLI configuration mode.
To configure file types for analysis:
1. Click Settings and then select Appliance Settings.
2. Click Malware File Association in the sidebar.
3. (Optional) Use the controls at the top of the page to define the scope of the changes.
4. Configure settings as described in the Malware Analysis User Guide.
Configuring Malware Repository Settings for Managed
Malware Analysis Appliances Using the Web UI
Use the Appliance Settings: Malware Repository page to configure the malware repository
network share and the repository paths for guest images on managed Malware Analysis
appliances.
To configure malware repository settings:
1. Click Settings and then select Appliance Settings.
2. Click Malware Repository in the sidebar.
3. (Optional) Use controls at the top of the page to define the scope of the changes.
© 2022 FireEye Security Holdings US LLC
395
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
4. Configure settings as described in the Malware Analysis User Guide.
Configuring and Managing Scans for Managed File
Protect Appliances Using the Web UI
Use the CMS Scans page to configure and manage scans on managed File Protect
appliances.
To configure and manage scans:
1. Click Alerts and then select FX.
2. Click Configured & Recent Scans.
3. (Optional) Use controls at the top of the page to define the scope of the changes and
filter the results.
4. Configure and manage scans as described in the File Protect User Guide.
Configuring and Managing Storage for Managed File
Protect Appliances Using the Web UI
Use the CMS Storage page to configure and manage file shares on managed File Protects
appliances.
To configure and manage storage:
1. Click Alerts and then select FX.
2. Click Storage.
3. (Optional) Use the appliance list to specify the scope of the changes and filter the
results.
4. Configure and manage storage as described in the File Protect User Guide.
Configuring Managed Appliances Using
the CLI
Use the commands in this section to configure managed appliances by executing
individual commands on behalf of them. The commands are executed once; they are not
stored.
NOTE: For comprehensive information about the configuration commands, see the
System Administration Guide, Administration Guide, or User Guide for your appliance.
396
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Managed Appliances Using the CLI
NOTE: If you omit the command parameter from these commands, you will be
prompted for it, and the characters you enter will be masked for confidentiality.
NOTE: This topic describes how to execute a single command. You can also define
a profile of commands that run in sequence unattended. See Working with
Command Profiles on page 406.
To execute a command on an appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Execute the command:
hostname (config) # cmc execute appliance <applianceName> command
"<command>"
where command must be enclosed in double quotation marks.
3. Save your changes:
hostname (config) # cmc execute appliance <applianceName> command
"write memory"
To execute a command on a group of appliances:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Execute the command:
hostname (config) # cmc execute group <groupName> command "<command>"
where command must be enclosed in double quotation marks.
3. Save your changes:
hostname (config) # cmc execute group <groupName> command "write
memory"
IMPORTANT! You can cancel the execution of outstanding commands, as
described in Canceling Outstanding Commands on the next page.
Example
This example executes the aaa authentication password local no-userid and show
aaa authentication password commands on behalf of the NX-04 appliance.
hostname (config) # cmc execute appliance NX-04 command "aaa authentication
password local no-userid"
============ Appliance NX-04 ============
Execution was successful.
Execution output:
(none)
© 2022 FireEye Security Holdings US LLC
397
Central Management System Administration Guide
CHAPTER 26: Configuring Managed Appliances
hostname (config) # cmc execute appliance NX-04 command "show aaa
authentication password"
============ Appliance NX-04 ============
Execution was successful.
Execution output:
Local password requirements:
Minimum length: 5
Maximum length: 32
Maximum character repeats: no limit
Minimum lower case characters: 0
Minimum upper case characters: 0
Minimum special characters: 0
Minimum numeric characters: 0
Recent passwords to check against:
Allowed password to match userid: no
...
Canceling Outstanding Commands
Use the commands in this section to cancel commands that were issued but have not yet
been executed.
NOTE: You can cancel both commands issued using the cmc execute command,
and commands in a profile.
To cancel all outstanding commands on an appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Cancel the commands:
hostname (config) # cmc cancel appliance <applianceName> all
To cancel all outstanding commands on a group of appliances:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Cancel the commands:
hostname (config) # cmc cancel group <groupName> all
Example
This command cancels all outstanding commands on the EX-03 appliance.
hostname (config) # cmc cancel appliance EX-03 all
398
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Grouping Appliances
CHAPTER 27: Using Appliance
Groups and Command Profiles
You can use appliance groups and command profiles to manage the appliances in your
network more efficiently. For details, see:
l
Grouping Appliances below
l
Working with Command Profiles on page 406
Grouping Appliances
Appliance groups allow you to push configuration changes to multiple appliances at the
same time, and to limit the displayed event data to specific appliances.
IMPORTANT! Each appliance type has a reserved system group; appliances
cannot be removed from their respective system groups. For example, all Network
Security appliances are permanent members of the sysgroup.Web_MPS group, all
Email Security — Server Edition appliances are permanent members of the
sysgroup.Email_MPS, all Malware Analysis group appliances are permanent
members of the sysgroup.MAS group, and so on. All managed appliances are
members of the All group.
You cannot add or delete appliances from reserved groups. You can create custom
groups to which you can add or delete appliances as desired.
You can create additional custom groups as needed. A group can have any number of
appliances, and an appliance can be a member of any number of groups. Reasons for
creating groups include:
l
Dividing appliances of the same type into smaller groups. For example, you could
group your Network Security appliances by region.
© 2022 FireEye Security Holdings US LLC
399
Central Management System Administration Guide
l
CHAPTER 27: Using Appliance Groups and Command Profiles
Combining different appliance types into the same group. For example, you could
put all of your Network Security appliances and Email Security — Server Edition
appliances into the same group so you can push the same user accounts or
password security policies to all of them.
Group Information
The settings for groups are shown in the following table.
Field
Description
Name
The group name.
Comment
An optional comment about the group.
Created
(UTC)
The date and time the group was created.
Action
Links to edit or delete a group. These links are not provided for the
reserved system groups.
Sensors
The number of appliances that are members of the group.
For more information, see:
l
Creating and Managing Groups Using the Web UI below
l
Creating and Managing Groups Using the CLI on page 402
l
Adding Appliances to Groups Using the Web UI on page 404
l
Adding Appliances to Groups Using the CLI on page 404
l
Removing Appliances from Groups Using the Web UI on page 405
l
Removing Appliances from Groups Using the CLI on page 406
Prerequisites
l
Operator or Admin access
Creating and Managing Groups Using the Web UI
Use the Create New Group dialog box to create groups, and the Groups dialog box to
manage groups.
400
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Grouping Appliances
To add a new group:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Actions > New Group.
3. Enter the name of the group and an optional comment.
4. Click Create Group. The Groups dialog box opens.
5. Verify that the new group was added.
To edit an existing group:
1. Click Show All Groups to open the Groups dialog box.
2. Locate the group in the list.
© 2022 FireEye Security Holdings US LLC
401
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
3. Click Select > Edit.
4. Edit the name and comment as needed.
5. Click Edit Group.
To delete a group:
1. Click Show All Groups to open the Groups dialog box.
2. Locate the group in the list.
3. Click Select > Delete.
4. When prompted, click OK to confirm that you want to delete the group.
Creating and Managing Groups Using the CLI
Use the commands in this section to create and manage appliance groups.
To add a new group:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Add a new group:
hostname (config) # cmc group <groupName>
3. (Optional) Add a comment about the group:
hostname (config) # cmc group <groupName> comment "<comment>"
where commentText must be enclosed in double quotation marks.
4. Verify your changes:
hostname (config) # show cmc groups
5. Save your changes:
hostname (config) # write memory
To rename a group:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Rename the group:
hostname (config) # cmc group <groupName> rename <newGroupName>
3. Verify your change:
hostname (config) # show cmc groups <newGroupName>
402
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Grouping Appliances
4. Save your change:
hostname (config) # write memory
To delete a comment:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Delete the comment:
hostname (config) # no cmc group <groupName> comment
3. Verify your change:
hostname (config) # show cmc groups <groupName>
4. Save your change:
hostname (config) # write memory
To delete a group:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Delete the group:
hostname (config) # no cmc group groupName
3. Verify your change:
hostname (config) # show cmc groups
4. Save your change:
hostname (config) # write memory
Example
This example creates a "Milan" appliance group, deletes the "Sydney" group, renames the
"Milan" group to "Venice," and adds a comment to the group.
hostname (config) # cmc group Milan
hostname (config) # show cmc groups
Group Milan
Comment:
No members.
Group Sydney
Comment:
Appliances:
NX-01
Group sysgroup.Email_MPS
Comment:
System Group: eMPS
Appliances:
EX-02
.
.
.
© 2022 FireEye Security Holdings US LLC
403
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
hostname (config) # no cmc group Sydney
hostname (config) # show cmc groups Sydney
% Unknown group.
hostname (config) # cmc group Milan rename Venice
hostname (config) # cmc group Venice comment "Italian region appliances"
hostname (config) # show cmc groups Venice
Group Venice
Comment: Italian region appliances
No members.
Adding Appliances to Groups Using the Web UI
Use the Appliance/Sensor display to add appliances to groups.
Tip: Select the group in the Sensor Group to see a full list of the appliances
currently in a particular group.
To add an appliance to a custom group:
1. Click Appliances > Sensors.
2. Click Show All Groups. The Groups dialog appears.
3. Click the Select button for the desired group.
4. Click Add/Remove Sensors. The Add/Remove Sensors dialog appears.
5. Click the checkbox for the sensor to be added.
6. Click the Add/Remove Selected Sensors button to add the sensor.
Adding Appliances to Groups Using the CLI
Use the commands in this section to add appliances to groups.
To add an appliance to a group:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
404
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Grouping Appliances
2. Add an appliance to a group:
hostname (config) # cmc group <groupName> appliance <applianceName>
3. Verify that the appliance was added:
hostname (config) # show cmc group <groupName>
4. Save your change:
hostname (config) # write memory
Example
This example add the FX-06 appliance to the Acme group.
hostname (config) # cmc group Acme appliance FX-06
hostname (config) # show cmc groups Acme
Group Acme
Comment:
Acme division appliances
Appliances;
FX-06
Removing Appliances from Groups Using the Web UI
Use the Add/Remove Sensors from <Group> dialog box to remove appliances from
groups.
Tip: Select the group in the Sensor Group list to see a full list of the appliances
currently in the group.
To remove appliances from a group:
1. Click Appliances > Sensors.
2. Select the group in the Sensor Group dropdown..
3. Click Select in the Action column for the sensor to be removed.
4. Click Delete. A confirmation prompt appears.
5. Click OK.
6. Repeat the Select> Delete > OK sequence for each sensor to be removed from the
group.
© 2022 FireEye Security Holdings US LLC
405
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
Removing Appliances from Groups Using the CLI
Use the commands in this section to remove appliances from groups.
To remove an appliance from a group:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove an appliance from a group:
hostname (config) # no cmc group <groupName> appliance <applianceName>
3. Verify that the appliance was removed:
hostname (config) # show cmc group <groupName>
4. Save your change:hostname (config) # write memory
Example
This example removes the EX-03 appliance from the London group.
hostname (config) # cmc group London appliance EX-03
show cmc groups London
Group Acme
Comment:
UK region appliances
Appliances;
AX-05
Working with Command Profiles
A profile is a set of CLI commands that can be applied to an appliance or appliance group.
Each command is assigned a sequence number. When the profile is applied, the
commands are executed in the order defined by that sequence, starting with the command
with the smallest number. The benefits of using profiles include:
l
l
Automation—Multiple configuration settings can be applied at the same time with
little user intervention.
Reuse—A profile consisting of common configuration commands can be used on
different appliances and appliance types.
You can use the following methods to add commands to profiles:
406
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Working with Command Profiles
Manually, where you define each command and its sequence number one at a time.
Extracting commands from a running configuration. The show configuration
running command displays commands that can be used to recreate the current
running configuration. You can extract these commands from an appliance and put
them into an empty profile. The commands will automatically be executed in the
correct order. Commands that configure local, appliance-specific settings (such as
routing, licensing, and time zone settings) will be omitted from the target profile.
IMPORTANT! Some commands in the running configuration may be
incompatible with a different product type or appliance model. Review the
commands to determine if they are compatible before you apply a profile
using this method.
l
Duplicating a profile.
There are two options you can use when applying a profile.
Profile Options
Option
Description
no-save
Prevents the configuration set by the commands in the profile from being
saved to memory after the profile is applied. Otherwise, the write memory
command is run in the background after the profile is applied.
failcontinue
Allows command execution to continue, even if one or more commands in
the profile fail. Otherwise, none of the remaining commands in the profile
are executed after a single command fails.
Prerequisites
l
Admin access
Creating and Managing Profiles Using the CLI
Use the commands in this section to create and manage command profiles.
To create a profile:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Create the profile:
hostname (config) # cmc profile <profileName>
© 2022 FireEye Security Holdings US LLC
407
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
3. (Optional) Add a comment about the profile:
hostname (config) # cmc profile <profileName> comment "<comment>"
where comment must be enclosed in double quotation marks.
4. Verify your change:
hostname (config) # show cmc profiles
5. Save your changes:
hostname (config) # write memory
To rename a profile:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Rename the profile:
hostname (config) # cmc profile <profileName> rename <newProfileName>
3. Verify your change:
hostname (config) # show cmc profiles <newProfileName>
4. Save your change:
hostname (config) # write memory
To remove a comment:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the comment:
hostname (config) # no cmc profile <profileName> comment
3. Verify your change:
hostname (config) # show cmc profiles <profileName>
4. Save your change:
hostname (config) # write memory
To delete a profile:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Delete the profile:
hostname (config) # no cmc profile <profileName>
408
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with Command Profiles
3. Verify that the profile was deleted:
hostname (config) # show cmc profiles
4. Save your change:
hostname (config) # write memory
Example
This example creates an "acctmgt" profile with a comment and deletes the "PswdPolicy"
profile.
hostname (config) # cmc profile acctmgt
hostname (config) # cmc profile acctmgt comment "Adds operator user account."
hostname (config) # no cmc profile PswdPolicy
hostname (config) # show cmc profiles
Profile acctmgt
Comment: Adds operator user account.
Commands:
No commands.
...
Adding Commands to Profiles Using the CLI
Use the commands in this section to add commands to a profile.
To add individual commands to a profile:
1. Enable the CLI configuration mode.
hostname > enable
hostname # configure terminal
2. Add a command and specify its sequence:
hostname (config) # cmc profile <profileName> command <sequenceNumber>
"<command>"
where:
l
profileName is the name of an existing or new profile. (If the profile does not
exist, it will be created.)
l
sequenceNumber is an integer that controls the order in which the commands
within the profile will be executed. The command with the smallest sequence
number is executed first.
l
command is the CLI command. It must be enclosed in double quotation marks.
3. Repeat the previous step for each command you want to include.
4. Verify your changes:
hostname (config) # show cmc profiles <profileName>
5. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
409
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
To extract commands from a running configuration and add them to a profile:
IMPORTANT: Some commands in the running configuration may be incompatible
with a different product type or appliance model. Review the commands to
determine if they are compatible before you apply a profile using this command.
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the empty profile and the appliance from which to extract the commands:
hostname (config) # cmc profile <profileName> extract-from-appliance
<applianceName>
where profileName is the name of an empty profile, and applianceName is the
name of the appliance from which the commands from the running configuration
will be extracted.
3. Verify your change:
hostname (config) # show cmc profiles <profileName>
4. Save your change:
hostname (config) # write memory
To copy a profile:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the names of the source profile and the target (new) profile:
hostname (config) # cmc profile <sourceProfileName> copy
<targetProfileName>
where sourceProfileName is the original profile and targetProfileName is the
new profile.
3. Verify your change:
hostname (config) # show cmc profiles
4. Save your change:
hostname (config) # write memory
Examples
Manually Adding Commands
This example populates the "acctmgt" profile with commands that will add an Operator3
user account to the appliances to which it is applied.
410
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with Command Profiles
hostname (config) # cmc profile acctmgt command 1 "username Operator3 role
operator"
hostname (config) # cmc profile acctmgt command 2 "username Operator3
password evtk*643U"
hostname (config) # show cmc profiles acctmgt
Profile acctmgt
Comment:
Commands:
1. username Operator3 role operator
2. username Operator 3 password evtk*643U
Adding Commands Extracted from the Configuration of
Another Appliance
This example extracts commands from the EX-03 appliance running configuration,
populates the "general" profile with them, and applies them to the EX-05 appliance. The
output indicates that the no fenet check-certificate command could not be executed.
hostname (config) # cmc profile extract extract-from appliance EX-03
hostname (config) # cmc profile general apply appliance EX-05
====================Appliance EX-05==========================
Execution was successful.
Execution output:
%Disabling certificate checking is not allowed.
Saving configuration file...Done!
Removing Commands from Profiles Using the CLI
Use the commands in this section to remove commands from a profile.
To remove a single command:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the command:
hostname (config) # no cmc profile <profileName> command
<sequenceNumber>
where sequenceNumber is the number assigned to the command.
3. Verify your changes:
hostname (config) # show cmc profiles <profileName>
4. Save your changes:hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
411
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
To remove all commands:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove all commands:
hostname (config) # no cmc profile <profileName> command
3. Verify your change:
hostname (config) # show cmc profiles <profileName>
4. Save your change:
hostname (config) # write memory
Applying Profiles Using the CLI
Use the commands in this section to apply profiles to a specific appliance or to an
appliance group. For a description of the optional parameters, see Profile Options on
page 407.
IMPORTANT! Unless you use the no-save parameter, the configuration changes
set by the commands in the profile are written to memory.
IMPORTANT! You can cancel the execution of outstanding commands in a profile,
as described in Canceling Outstanding Commands on page 398.
To apply a profile to a specific appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Apply the profile:
l
To apply the profile normally:
hostname (config) # cmc profile <profileName> apply appliance
<applianceName>
l
To prevent the configuration changes from being written to memory after the
profile is applied:
hostname (config) # cmc profile <profileName> apply appliance
<applianceName> no-save
l
To continue executing commands after one command fails:
hostname (config) # cmc profile <profileName> apply appliance
<applianceName> fail-continue
3. View the command output to determine whether the profile was applied
successfully.
412
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Working with Command Profiles
4. Save your changes:
hostname (config) # write memory
To apply a profile to a group of appliances:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Apply the profile:
l
To apply the profile normally:
hostname (config) # cmc profile <profileName> apply group
<groupName>
l
To prevent the configuration changes from being written to memory after the
profile is applied:
hostname (config) # cmc profile <profileName> apply group
<groupName> no-save
l
To continue executing commands on the appliances in the group after one
command fails:
hostname (config) # cmc profile <profileName> apply group
<groupName> fail-continue
3. View the command output to determine whether the profile was applied
successfully.
4. Save your changes:
hostname (config) # write memory
Examples
Successful Profile Application
This example applies the "acctmgt" profile to the NX-04 appliance, which succeeds.
hostname (config) # cmc profile acctmgt apply appliance NX-04
=================Appliance NX-04=============================
Execution was successful.
Execution output:
Saving configuration file...Done!
Failed Profile Application
This example attempts to apply the "DateTimeJpn" profile to the Tokyo group, but fails
because manual time and date settings are not permitted when NTP is enabled.
© 2022 FireEye Security Holdings US LLC
413
Central Management System Administration Guide
CHAPTER 27: Using Appliance Groups and Command Profiles
hostname (config) # cmc profile DateTimeJpn apply group Tokyo
=================Appliance FX-03 =============================
Error code 6 (CLI command execution failure)
Error output:
%NTP enabled, clock adjustment not allowed
Execution output:
(none)
414
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Managing the Distribution of Alert Notifications
CHAPTER 28: Monitoring
Aggregated Alert Data
The Central Management appliance aggregates events from all managed appliances. You
can use appliance groups to limit the displayed event data to specific appliances. (For
information about groups, see Grouping Appliances on page 399.)
You can centrally view detection and analysis results for managed appliances using the
Dashboard and the Alerts sub-menus in the Central Management Web UI or by using the
cmc execute commands in the Central Management CLI.
Managing the Distribution of Alert
Notifications
You can send alert notifications from the Central Management appliance, from managed
appliances, or from both the Central Management appliance and managed appliances to
different servers. The following options are available:
Centralized Notifications—All notifications come from the Central Management
appliance.
Mixed Notifications—Notifications come from both the Central Management appliance
and managed appliances.
Decentralized Notifications—Notifications come from managed appliances only.
Centralized Notifications
Use centralized notifications if you want all your alert notifications to come from the
Central Management appliance. The advantage of using centralized notifications is that
you only have to configure settings once, and the alerts are tracked in the same place. A
disadvantage is that you have fewer delivery options. For example, for email notifications
configured on the Network Security appliance, the delivery options are "Daily digest," "Per
event," "Daily per source," "Hourly per source," "1 min per source," and "5 mins per
© 2022 FireEye Security Holdings US LLC
415
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
source." On the Central Management appliance the only options are "Daily digest" and
"Per event."
After Central Management notifications are enabled, all notification alerts are sent to the
notification servers you configure for the Central Management appliance. Centralized
notifications start immediately after you configure a protocol and add notification server
details, and they stop if you remove the notification servers or the protocols. The Central
Management appliance sends notifications in the order they are received.
Perform the following tasks to set up centralized notifications:
1. Remove the notification settings for each managed appliance, as described in the
User Guide for the managed appliance.
2. Enable notification settings for the Central Management appliance, as described in
Event Notifications on page 285.
Mixed Notifications
Use mixed notifications when you want to send centralized notifications to one notification
server, and individual appliance notifications to other servers. One advantage of mixed
notifications is that you can track notifications from individual appliances separately on a
separate notifications server, while still aggregating notifications from all managed
appliances on the Central Management appliance. Another advantage is the additional
delivery options on the individual appliances, as described in Centralized Notifications on
the previous page.
NOTE: If you disconnect an appliance from the Central Management appliance,
notifications will be sent to the server configured for that appliance, if one is
configured.
416
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Managing the Distribution of Alert Notifications
Perform the following tasks to set up mixed notifications:
1. Enable notification settings for the Central Management appliance, as described in
Event Notifications on page 285.
2. Enable notification settings for each managed appliance you want to track
separately, as described in the User Guide for the managed appliance.
Decentralized Notifications
Use decentralized notifications if you want notifications to be sent only from individual
managed appliances, and not from the Central Management appliance. This was the
notification delivery method in previous versions of the Central Management appliance
(Release 6.4.1 and earlier), so no configuration changes are needed for backward
compatibility.
Perform the following tasks to set up decentralized notifications:
© 2022 FireEye Security Holdings US LLC
417
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
1. Remove all notification settings for the Central Management appliance, as described
in Event Notifications on page 285.
2. Enable notification settings for each managed appliance, as described in the User
Guide for the managed appliance.
Monitoring Appliances Using the Web UI
Alert and analysis results are specific to appliance types. You can filter some results based
on appliance group or a specific appliance, as shown in the following illustration. Data is
displayed only if you select a group or appliance to which the page applies. For example,
no data would be displayed if you select a Network Security appliance on the Email Alerts
page, because that page applies only to the Email Security — Server Edition appliance.
Viewing Alerts and Events for Managed Network Security
Appliances Using the Web UI
Use the Alerts page to view information about Network Security alerts and events.
To view alerts and events:
1. On the Alerts tab, click NX > Alerts.
2. (Optional) Use the controls at the top of the page to filter the results.
3. View the results as described in the Network Security User Guide. For IPS-enabled
Network Security appliances, see the IPS Feature Guide.
NOTE: See Managing Suppressed Alerts on Managed Network Security Appliances
Using the Web UI on the facing page.
418
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Monitoring Appliances Using the Web UI
Managing Suppressed Alerts on Managed Network
Security Appliances Using the Web UI
Use the Appliance Settings: Suppressed Alerts page to view and manage suppressed
alerts on managed Network Security appliances.
When an alert is suppressed, the suppression total is pushed to all managed Network
Security appliances. The maximum number of suppressed alerts is 15 for all managed
appliances combined. For example, suppose the Central Management appliance manages
a Network Security appliance that already has the maximum number of suppressed alerts.
If you add another Network Security appliance with suppressed MD5s or URLs to the
Central Management appliance, a notice at the top of the page advises you to suppress or
resolve alerts until the number is brought down to 15. After you suppress or resolve these
extra alerts, the suppressed alerts on the Network Security appliances become out-of-sync.
A warning with a link to synchronize them is displayed at the top of the Appliance
Settings: Suppressed Alerts page.
NOTE: For detailed information about the alert suppression feature, see the Network
Security User Guide. .
To view and manage suppressed alerts:
1. Click Settings and then select Appliance Settings.
2. Click Suppressed Alerts in the sidebar.
3. Manage the suppressed alerts as described in the Network Security User Guide.
To reduce an excess of aggregated suppressed alerts:
1. Open the Appliance Settings: Suppressed Alerts page.
A notice at the top of the page advises that too many alerts are suppressed.
2. Select the checkboxes for the MD5s and URLs with the least impact, and then click
Unsuppress or Resolve.
CAUTION: Do not resolve alerts until the FireEye Security Content team
determines that they are false positives and updates its security content.
Apply the latest security content update to your appliance, and then
resolve the alerts.
3. Refresh the page. The MD5s and URLs you selected are removed from the page, and
a warning at the top of the page informs you about an out-of-sync condition on the
managed appliances.
4. Click the SYNC link in the warning to synchronize alert suppression.
© 2022 FireEye Security Holdings US LLC
419
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
Monitoring Malware and Callback Activity for Managed
Network Security Appliances Using the Web UI
Use the Hosts and Callback Activity pages to view information about malware and CnC
callback server activity on managed Network Security appliances.
To view malware and callback activity:
1. Click Alerts and then select NX.
2. Click Alerts.
3. Click the Hosts or Callback Activity link.
4. (Optional) Use the controls at the top of the page to filter the results.
5. View the results as described in the Network Security User Guide.
Viewing Malware Summaries for Managed Network
Security Appliances Using the Web UI
Use the Summaries page to view summary information about malware detected by
managed Network Security appliances.
To view malware summaries:
1. Click Alerts and then select NX.
2. Click Summaries.
3. Select one of the following tabs at the top of the page:
l
Malware—Displays the information in a table.
l
Charts—Displays the information in bar charts.
l
Treemaps—Displays the information in a treemap.
4. (Optional) Use the controls at the top of the page to filter the results.
5. View the results as described in the Network Security User Guide.
Viewing Riskware for Managed Appliances Using the
Web UI
In the Riskware Alerts page of a managed Network Security or the Riskware Emails page
of a managed Email Security — Server Edition appliance, you can identify the matched
alerts that are detected as nonmalicious for a riskware event. On the Dashboard What's
Happening panel, you can track the number of Web and email riskware alerts.
For more information about riskware, see the Network Security Guide or Email Security —
Server Edition User Guide.
420
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Monitoring Appliances Using the Web UI
To view riskware alerts:
1. (Network Security) Select Alerts > NX > Riskware or on the Dashboard What's
Happening panel, click the Web Riskware Alerts link.
2. (Email Security — Server Edition) Select Alerts > Email > Riskware or on the
Dashboard What's Happening panel, click the Email Riskware Alerts link.
3. (Optional) Use the controls at the top of the page to filter the results.
Viewing SmartVision Alerts on SmartVision Appliances
Using the Web UI
Use the Trellix Network SmartVision page to view SmartVision alerts and associated
forensic data on a SmartVision appliance. A SmartVision appliance can be any of the
following
l
SmartVision Edition sensor
l
SmartVision-enabled Network Security sensor
l
SmartVision-enabled Network Security integrated appliance
To view SmartVision alerts:
1. Select Alerts > NX > SmartVision.
2. (Optional) Use the page controls at the top of the page to define the number of alerts
per page and to select a page of alerts in the list.
3. (Optional) Click the funnel icon to expand the Filter panel at the left edge of the
page. Use filter options to define the match criteria for alerts that are displayed.
4. View and investigate SmartVision alerts as described in the Network Security
SmartVision Feature Guide.
Configuring AD Logger for Enhanced SmartVision Alerts
On managed SmartVision appliances or sensors, you can view SmartVision alert details
that are enhanced with user details obtained from Microsoft Active Directory. To enable
enhanced SmartVision alerts, use the Trellix Central Management appliance Web UI or CLI
to configure the Active Directory (AD) Logger feature.
For details, see How to Configure Central Management Active Directory Integration for
SmartVision Alerts in the Trellix Community Knowledge Base. You must sign in with your
Trellix account credentials in the Username and Password fields.
© 2022 FireEye Security Holdings US LLC
421
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
Viewing the Campaigns for Managed Email Security —
Server Edition Appliances Using the Web UI
In the eAlerts > Campaigns page of a managed Email Security — Server Edition appliance,
you can track the total number of infected emails that are part of a campaign. A red status
indicates that the campaign is not verified. A blue status indicates that the campaign is
verified.
You can generate and download the list of campaigns as an Email Campaign List report
in XML format, PDF format, CSV format, or JSON format from the appliance to your local
desktop.
To view the campaigns:
1. Click eAlerts > Campaigns.
2. (Optional) Use the page controls at the top of the page to define the number of
campaigns per page and to select a page of campaigns in the list.
3. (Optional) Click the funnel icon to expand the Filter panel at the left edge of the
page. Use filter options to define the match criteria for campaigns that are displayed.
4. View the analysis results that have been identified as a campaign as described in
the Email Security — Server Edition User Guide.
Managing Quarantined Emails for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Email Quarantine page to view and manage quarantined emails on managed
Email Security — Server Edition appliances.
To manage quarantined emails:
1. Click Alerts and then select Email.
2. Click eQuarantine.
3. (Optional) Use the controls at the top of the page to filter the results.
4. Manage the quarantine as described in the Email Security — Server Edition User
Guide.
Viewing Email Analysis Results for Managed Email
Security — Server Edition Appliances Using the Web UI
Use the Email Alerts page to view information about infected emails observed by managed
Email Security — Server Edition appliances.
422
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Monitoring Appliances Using the Web UI
To view email analysis results:
1. Click Alerts and then select Email.
2. Click eAlerts.
3. (Optional) Use the controls at the top of the page to filter the results.
4. View the information as described in the Email Security — Server Edition User Guide.
Viewing and Exporting the Results of Processed Emails on
a Managed Email Security — Server Edition Appliance
Using the Web UI
Use the Processed Emails page to view the list of malicious and nonmalicious emails that
have been processed by the Email Security — Server Edition appliance based on the type of
fields (Message ID, Sender, Recipient, Subject Line, URL, and Attachment).
The Processed Emails page also displays the status and state of the scanned emails with
an associated verdict based on the results of the scan. You can display up to 100 emails
per page. You can also export a filtered list of processed emails from the appliance.
To view and export the status of processed emails:
1. Click the Search Emails tab and then click Processed Emails.
2. (Optional) Use the controls at the top of the page to filter the results.
3. View and export the status of processed emails as described in the Email Security —
Server Edition User Guide.
Viewing the Messages in the Email Queue on a Managed
Email Security — Server Edition Appliance Using the Web
UI
Use the Queued Emails page to view the list of messages that are queued for dynamic
analysis. You can filter the specific search criteria based on the sender, recipient, or queue
type. You can monitor your emails while they are being processed and held in the email
queue.
To view the messages in the email queue:
1. Click the Search Emails tab and then click Queued Emails.
2. (Optional) Use the controls at the top of the page to define the scope of the changes.
3. View messages in the email queue as described in the Email Security — Server
Edition User Guide.
© 2022 FireEye Security Holdings US LLC
423
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
Viewing URL Click Reports for Managed Email Security
Appliances Using the Web UI
Use the Dashboard page to view the total number of missed and blocked URL click events.
In this example, the following URL click events were reported for the week:
l
l
2 URLs were reported missed and 5 click timestamps were reported for these URLs.
5 URLs were reported blocked and 18 click timestamps were reported for these
URLs.
To view the URL click event details:
1. Click URL Click Missed or URL Click Blocked.
The eAlerts > Alerts page is displayed. This example is displayed after URL Click
Missed is selected.
This example, displays the URL click badges for the alerts.
2. Click on an alert to display a summary of the alert details along with a table
itemizing the URL clicks, the URL click time stamp, and the missed or blocked URL
click status.
424
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Monitoring Appliances Using the Web UI
For detailed information about the URL click reporting feature, see the Email Security
— Server Edition User Guide
Viewing Malware Analysis Results for Managed Malware
Analysis Appliances Using the Web UI
Use the Analysis page to view information about the malware analysis jobs run on
managed Malware Analysis appliances.
To view malware analysis results:
1. Click Alerts and then select AX.
2. Click Analysis.
3. (Optional) Use the controls at the top of the page to filter the results.
4. View results as described in the Malware Analysis User Guide.
Managing File Quarantines for Managed File Protect
Appliances Using the Web UI
Use the CM: Quarantined Files page to view and manage quarantined files on managed
File Protect appliance.
To manage quarantined files:
1. Click Alerts and then select FX.
2. Click Quarantined Files.
3. (Optional) Use the controls at the top of the page to filter the results.
4. Manage the quarantine as described in the File Protect User Guide.
© 2022 FireEye Security Holdings US LLC
425
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
Managing File Alerts for Managed File Protect Appliances
Using the Web UI
Use the CM: File Alerts page to view and drill into details about malicious files on
managed File Protect appliance.
To manage quarantined files:
1. Click Alerts and then select FX.
2. Click Alerts.
3. (Optional) Use the controls at the top of the page to filter the results.
4. Manage the alerts as described in the File Protect User Guide.
Monitoring Appliances Using the CLI
Use the commands in this section to view detection and analysis results on managed
appliances by executing individual commands on behalf of them. The commands are
executed once; they are not stored.
NOTE: For comprehensive information about the detection and analysis commands,
see the User Guide for your appliance.
NOTE: If you omit the command parameter from these commands, you will be
prompted for it, and the characters you enter will be masked for confidentiality.
NOTE: This topic describes how to execute a single command. You can also define
a profile of commands that run in sequence unattended. See Working with
Command Profiles on page 406.
To execute a command on a managed appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Execute the command:
hostname (config) # cmc execute appliance <applianceName> command
["<command>"]
where command must be enclosed in double quotation marks.
To execute a command on a group of appliances:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
426
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Network Security and Email Security — Server Edition Event Correlation
2. Execute the command:
hostname (config) # cmc execute group <groupName> command ["<command>"]
where command must be enclosed in double quotation marks.
IMPORTANT! You can cancel the execution of outstanding commands, as
described in Canceling Outstanding Commands on page 398.
Example
This example executes the show alerts summary command on behalf of the NX-04
appliance.
hostname (config) # cmc execute appliance NX-04 command "show alerts summary"
============ Appliance NX-04 ============
Execution was successful.
Execution output:
Domain Match
: 2182
Web Infection
: 6133
Malware Callback
: 27273
Infection Match
: 4035
Malware Object
: 12564
Total Alerts
: 52187
Network Security and Email Security —
Server Edition Event Correlation
When the Central Management appliance manages both Network Security appliances and
Email Security — Server Edition appliances, malicious Web events detected by the
Network Security appliances are correlated with email events detected by the Email
Security — Server Edition appliances, and malicious email events detected by the Email
Security — Server Edition appliances are correlated with Web events detected by the
Network Security appliances.
NOTE: For information about allowing two Central Management networks to share
information about malicious events, see CM Peer Distributed Correlation on
page 601.
Correlated events are displayed with the following icons in the Web UI:
l
Web Correlation — This icon in an email alert indicates that the alert is
correlated with a Web alert. It is typically in the URL column, depending on the tab
selected in Alerts > Email > eAlerts.
© 2022 FireEye Security Holdings US LLC
427
Central Management System Administration Guide
l
CHAPTER 28: Monitoring Aggregated Alert Data
Email Correlation — This icon in a Web alert indicates that the alert is
correlated with an email alert. It is in the Total column or the Alert Type column,
depending on the tab selected in Alerts > NX > Alerts.
Correlated events are displayed with the following badges:
l
l
Correlated NX Alert — This badge in an email alert indicates that the alert is
correlated with a Web alert. It is shown in the Badges column in the Alerts > Email
> eAlerts page. You can select it as a filter to find correlated Network Security
events.
Correlated EX Alert — This badge in a Web alert indicates that the alert is
correlated with an email alert. It is shown in the Badges column in Alerts > NX >
Alerts page. You can select it as a filter to find correlated Email Security — Server
Edition events.
Reviewing Email Alerts Correlated with Web Events
You can view the combined alert information or navigate to the list of correlated Network
Security alerts from the Email Security — Server Edition alerts.
Prerequisites
l
l
One or more Network Security appliances managed by the Central Management
appliance.
One or more Email Security — Server Edition appliances managed by the Central
Management appliance.
NOTE: By default, alert correlation is enabled on any Central Management
appliance that manages one or more Network Security appliances and one or more
Email Security — Server Edition appliances.
For details, see:
l
Reviewing Correlated Email and Web Alert Information in a Combined View below
l
Viewing Web Alerts for Correlated Malicious Behavior on page 430
Reviewing Correlated Email and Web Alert Information in a
Combined View
The combined view shows the high-level details of correlated Email Security — Server
Edition and Network Security alerts.
428
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Network Security and Email Security — Server Edition Event Correlation
To review the combined view of correlated email and Web alerts:
1. On the Alerts tab, select Email > eAlerts.
2. If there are many alerts, use the Filters panel on the left edge of the page to filter by
the Correlated NX Alert badge.
3. In the Recipient tab, click the number link beside the Web icon in the URL column.
The Network Security alerts correlated with the Email Security — Server Edition
alert are displayed.
4. In the list of correlated alerts in the Alerts tab, click a URL in the URL column.
The combined view displays the email details in the top section and the Web event
details in the bottom section.
© 2022 FireEye Security Holdings US LLC
429
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
Viewing Web Alerts for Correlated Malicious Behavior
From an email alert that has a malicious URL or attachment, you can navigate to the list of
Network Security alerts for the source IP addresses on which the same malicious URL or
attachment was identified. This view shows all malware objects and other events that
affected the source IP address for this email alert in the selected time period, including
those from other URLs or attachments, other Email Security — Server Edition alerts, and
other affected source IP addresses.
To review the list of Web alerts correlated with an email alert:
1. On the Alerts tab, select Email > eAlerts.
2. Select the Malicious Emails tab.
3. If there are many alerts, use the Filters panel on the left edge of the page to filter by
the Correlated NX Alert badge.
430
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Network Security and Email Security — Server Edition Event Correlation
4. In the URL or Attachment column of an email alert, click the Web icon link (
).
The NX > Alerts > Alerts tab displays the list of Network Security alerts from all
source IP addresses on which the same malicious URL or attachment was
identified.
The Network Security alerts marked with the email icon link (
) are correlated
with Email Security — Server Edition alerts.
The following example includes a malware object and callbacks for multiple malware
types.
Reviewing Web Alerts Correlated with Email Events
Follow these steps to review the malicious objects found by the Network Security appliance
and correlated to events on the Email Security — Server Edition appliance.
Prerequisites
l
l
One or more Network Security appliances managed by the Central Management
appliance.
One or more Email Security — Server Edition appliances managed by the Central
Management appliance.
NOTE: By default, alert correlation is enabled on any Central Management
appliance that manages one or more Network Security appliances and one or more
Email Security — Server Edition appliances.
© 2022 FireEye Security Holdings US LLC
431
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
To review Web alerts correlated with email events:
1. On the Alerts tab, click NX > Alerts.
2. If there are many alerts, use the Filters panel on the left edge of the page to filter by
the Correlated EX Alert badge.
3. On the Hosts tab, click the number link beside the email correlation icon (
) in the
Total column. The list of correlated Email Security — Server Edition alerts is
displayed in the Alerts tab.
4. In the correlated alerts, click an email correlation icon with the link superimposed
on it (
).
The correlated Email Security — Server Edition alert is displayed on the eAlerts >
Malicious Emails tab.
432
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Network Security and Email Security — Server Edition Event Correlation
Enabling Remote Email Security — Server Edition
Appliance Event Correlation
Follow these steps to enable remote Email Security — Server Edition appliance event
correlation on the Central Management appliance. When this is enabled, the Central
Management appliance will distribute the set of malicious URLs collected from the
Network Security appliances to all eligible managed Email Security — Server Edition
appliances.
Prerequisites
l
l
l
One or more Network Security appliances managed by the Central Management
appliance
One or more Email Security — Server Edition appliances managed by the Central
Management appliance
The managed Email Security — Server Edition appliances are release 7.9.x or later
NOTE: By default, alert correlation and remote correlation are enabled on any
Central Management appliance that manages one or more Network Security
appliances and one or more Email Security — Server Edition appliances of release
7.9.x or later.
To enable remote Email Security — Server Edition appliance alert correlation on the
Central Management appliance:
1. Log in to the Central Management CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
433
Central Management System Administration Guide
CHAPTER 28: Monitoring Aggregated Alert Data
3. Enable remote Email Security — Server Edition alert correlation:
hostname # (config) remote-correlation enable
4. Review the remote Email Security — Server Edition alert correlation configuration
settings:
hostname # (config) # show remote-correlation status
5. Save your changes:
hostname (config) # write memory
Endpoint Security Event Correlation
The Central Management appliance correlates Endpoint Security alerts with managed
appliance alerts and creates badges for the appropriate alerts. Correlated Network Security
alerts may have Endpoint Compromised, Endpoint Contained, and Containment
Requested badges. Correlated Email Security — Server Edition alerts may have a Related
Endpoint badge.
Endpoints Compromised, Related Endpoints, and Endpoints Contained links appear on
the Central Management Dashboard What's Happening panel if there are alerts with the
associated badges. Click a link to view the Alerts page with the list of alerts labeled with
the associated badge.
If available, you can download triage collections from the Central Management for alerts
that have endpoints that are compromised. Click the Endpoint Compromised badge or
Endpoints Compromised link, expand an alert and click the Download package link.
For details about how a managed appliance alert becomes an Endpoint Security alert and a
Central Management badge, see the Endpoint Security System Administration Guide.
For details on endpoint containment and triage collections, see the Endpoint Security User
Guide.
Collecting Information to Triage Alerts
Managed Network Security, Email Security — Server Edition, and Malware Analysis
appliances can collect information to help determine how and why an alert was triggered.
The information can help Trellix Technical Support determine how an alert was generated
and whether it is a false positive. This saves time spent manually searching for and
downloading alert data.
434
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Collecting Information to Triage Alerts
The information is gathered into a bundle. The bundle includes appliance and
configuration information, submission and email analysis data, alert information, artifacts,
samples, parsed logs, and so on, depending on the appliance type.
IMPORTANT: Use this feature only with guidance from Trellix Technical Support.
Only Technical Support can retrieve the bundle stored on the appliance and open
the password-protected bundle .zip file.
To collect the information:
1. Log into the Central Management Web UI.
2. Hover over Alerts and then select a Network Security or Email Security — Server
Edition alert page or a Malware Analysis analysis page.
3. Click the alert or analysis ID to open its detail page.
4. Click Prepare Triage Bundle.
5. When the bundle is ready, contact Technical Support to download and retrieve it.
NOTE: To collect the information using the API, you specify the alert UUID. See
the FireEye API Reference Guide for details.
© 2022 FireEye Security Holdings US LLC
435
Central Management System Administration Guide
436
CHAPTER 28: Monitoring Aggregated Alert Data
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About Reports
CHAPTER 29: Working with
Reports for Managed Appliances
This section covers the following information:
l
About Reports below
l
Customizing Reports for Managed Appliances on the next page
l
Generating and Scheduling Reports for Managed Appliances on page 479
About Reports
Reports can be customized only on managed Email Security — Server Edition,
Network Security, and File Protect appliances.
The Central Management allows you to generate reports about malicious behavior on the
network from all managed Email Security — Server Edition, Network Security, and File
Protect appliances. Reports include data accumulated from all appliances of the same type.
For example, if you specify the "Alert Details" report, the report will contain all data from
all Network Security appliances that are managed or have been managed during the
specified report time frame. You can create your own custom reports from scratch, use the
predefined reports, or clone a predefined report and use it as a template for a custom
report. You can also control access to the content of the report using roles. This content
includes the appropriate fields and filters that you want to include in each report.
Predefined Report Templates
Each predefined report template defines the individual sections in the report and the
presentation format (table or graph). You can choose the format (table or graph) for each
section individually.
© 2022 FireEye Security Holdings US LLC
437
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Custom Reports
You can configure any number of sections for a custom report on the Central Management
appliance. You can generate a custom report on the Central Management appliance to help
you retrieve and analyze the traffic pattern, appliance health, appliance performance, user
actions, or alert details about malware and infection trends for all managed appliances. A
custom report allows you to define the content and format of the data in each section of the
report and the attributes of the report such as the logo. You can configure the Central
Management appliance to send the generated custom report by email to the intended
recipients. You can schedule reports to be generated automatically.
Customizing Reports for Managed
Appliances
This section covers the following information about customizing reports for managed
appliances:
l
Task List for Customizing Reports for Managed Appliances below
l
Creating and Configuring Settings for a Custom Report on the facing page
l
Configuring Graphs for Custom Reports on page 444
l
Configuring Tables for Custom Reports on page 454
l
Creating a Custom Report from a Predefined Report Template on page 465
l
Editing and Cloning Reports That Have Been Generated on page 469
l
Sending, Downloading, and Deleting Custom Reports on page 475
You cannot customize a SmartVision Alerts report.
Task List for Customizing Reports for Managed
Appliances
Complete the steps for customizing reports for managed appliances in the following order:
1. Log in to the Central Management Web UI.
2. (Optional) Clone a predefined report template and edit its attributes to generate a
custom report. See Creating a Custom Report from a Predefined Report Template on
page 465.
3. Define the settings in a custom report. See Defining Settings in a Custom Report
Using the Web UI on page 440.
438
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
If desired, associate one logo with a PDF formatted custom report. See Adding or
Deleting a Logo Using the Web UI on page 443.
4. Determine the type of graphs that you want to define in a custom report. See
Configuring Graphs for Custom Reports on page 444.
5. Determine the type of tables and attributes that are the table columns that you want
to define in a custom report. See Configuring Tables for Custom Reports on
page 454.
If desired, define the match criteria for attributes that are the table columns
displayed in each section of the custom report. See Defining Filters for Table
Attributes on a Custom Report Section Using the Web UI on page 458.
Creating and Configuring Settings for a Custom Report
You can create and configure the report settings for your custom reports by using the
Central Management appliance Web UI:
l
Defining Settings in a Custom Report Using the Web UI on the next page
l
Editing Settings in a Custom Report Using the Web UI on page 441
l
Adding or Deleting a Logo Using the Web UI on page 443
Follow these usage guidelines when you configure the report settings for your custom
reports:
l
Output the report in XML, PDF, CSV, or JSON format
l
Associate only one logo with a PDF-formatted custom report
l
l
l
Specify a title and description that can include letters (a–z, A–Z), numbers, dashes
(-), underscores (_), and commas (,).
Set the time period the report covers. By default, the custom report display time zone
is UTC and is set for the past 24 hours.
Automatically generate reports on a schedule and email them to designated
recipients
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
© 2022 FireEye Security Holdings US LLC
439
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Defining Settings in a Custom Report Using the Web UI
Use the Custom Reports section to define settings in a new custom report for managed
appliances using the Central Management appliance Web UI.
You can define settings in a custom report only using the Web UI.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
To define the settings in a custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Report Title field, enter a name for your custom report.
3. In the Report Format drop-down menu, select the output format for the custom
report:
l
xml—Generate the report in XML format.
l
pdf—Generate the report in PDF format.
l
csv—Generate the report in CSV format.
l
json—Generate the report in JSON format.
4. (Optional) In the Description field, enter a description of your custom report. You
can specify any number of characters.
5. In the Time Zone to Convert Report Data to drop-down menu, select the time zone
for the custom report.
6. In the Date Range drop-down menu, select the time period for this custom report:
440
l
past hour—Report covers analysis generated during the past 1 hour.
l
past 7 hours—Report covers analysis generated during the past 7 hours.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
l
past 12 hours—Report covers analysis generated during the past 12 hours.
l
past 7 days—Report covers analysis generated during the past 7 days.
l
past 30 days—Report covers analysis during the past 30 days.
l
custom—Report covers analysis generated for a custom time period that
ranges from the last 15 minutes to the past 1 year.
Click Apply.
7. In the Report Recipients field, enter the email address of the report recipient. To add
multiple recipients, press Enter for each additional email address.
To delete a recipient, click X next to the email address you want to delete.
8. (Optional) If you want to schedule the generated custom report in the Reports >
Schedule Reports page, select the Make Schedulable checkbox. The custom report
that has been generated appears under "Custom Reports" in the Report Type dropdown menu.
For details about how to schedule a generated custom report, see Scheduling Reports
for Managed Appliances Using the Web UI on page 481.
9. Click Next Step to add a table or graph, or click Save if you are finished configuring
the custom report.
To add a table to a section of a custom report, see Adding Tables to a Custom
Report Using the Web UI on page 454.
To add a graph to a section of a custom report, see Adding Graphs to a Custom
Report Using the Web UI on page 445.
Editing Settings in a Custom Report Using the Web UI
Follow these steps to edit settings in a new custom report for managed appliances using
the Central Management appliance Web UI.
You can edit settings in a custom report only using the Web UI.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings in a custom report using the Central Management
Web UI. For details about how to define the settings in a custom report, see Defining
Settings in a Custom Report Using the Web UI on the previous page.
© 2022 FireEye Security Holdings US LLC
441
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
To edit the settings in a custom report:
1. Click Reports > Custom Reports.
2. In the Generated Custom Reports section, click the action icon (
).
3. Click Edit.
4. In the Custom Reports page, click the action icon (
).
5. Click Edit.
6. Modify the report setting you want to edit.
l
Report Title
l
Report Format
l
Description
l
Time Zone to Convert Report Data to
l
Date Range
l
Report Recipients
7. To enable or disable automatically generating a custom report on schedule, select or
clear the Make Schedulable checkbox.
8. Click Save.
442
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
To add a table to a section of a custom report for managed appliances, see Adding
Tables to a Custom Report Using the Web UI on page 454.
To add a graph to a section of a custom report for managed appliances, see Adding
Graphs to a Custom Report Using the Web UI on page 445.
Adding or Deleting a Logo Using the Web UI
Follow these steps to add a logo to a custom report or to delete a logo from a custom report
for managed appliances using the Central Management appliance Web UI.
You can associate only one logo with a PDF-formatted custom report. When you upload a
logo, the new logo overwrites the existing logo. The maximum size of the logo you upload
is 128 x 128 pixels.
You can add or delete a logo for a custom report only using the Web UI.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
To add a logo to a custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Logo field, click Choose File.
3. Select the logo file you want to add.
© 2022 FireEye Security Holdings US LLC
443
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
The image is uploaded to the Central Management appliance and it appears in the
Custom Reports page.
To delete a logo from a custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Logo field, click the X icon next to the logo.
A dialog box prompts you to confirm the changes.
3. Click Yes. The following message appears:
The logo is removed from the Custom Reports page.
Configuring Graphs for Custom Reports
You can configure any number of graph sections for your custom reports from scratch for
managed appliances by using the Central Management appliance Web UI:
l
Adding Graphs to a Custom Report Using the Web UI on the facing page
l
Editing the Graph Section of a Custom Report Using the Web UI on page 448
l
Cloning a Graph Section of a Custom Report Using the Web UI on page 450
l
Deleting a Graph Section From a Custom Report Using the Web UI on page 453
A custom report can contain one or more graph sections. You can choose the format of the
graph (line chart, pie chart, or bar chart) for each section individually.
444
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report. For details about how to define
the settings for the custom report, see Defining Settings in a Custom Report Using
the Web UI on page 440.
Adding Graphs to a Custom Report Using the Web UI
Follow these steps to add a graph to a section of a custom report for managed appliances
using the Central Management appliance Web UI.
You can add a graph to a section of a custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report. For details about how to define
the settings for the custom report, see Defining Settings in a Custom Report Using
the Web UI on page 440.
To add a graph to a section of a custom report:
1. In the Custom Reports page, enter the report title of the report to be modified.
2. Click Next Step.
3. In the next page, click Add Section. The Configure Section window opens.
4. Click the Graph icon. In the Visualization Type area, a green check mark indicates
that a graph is selected.
© 2022 FireEye Security Holdings US LLC
445
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
5. Click Next. The graph section details and settings are displayed.
6. In the Section Details area:
446
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
l
Enter the name of the graph for your custom report section.
l
(Optional) Enter a description to define the report section.
7. In the Graph Settings area, choose the type of graph you want from the Graph Type
drop-down menu. The available graph options depend on the appliance that is
connected to your Central Management appliance.
8. (Optional) To preview the graph settings, select the Preview checkbox. The graph
(such as a pie chart) that you selected is displayed.
If you need to refresh the content, click the refresh icon (
).
9. Click Save.
10. (Optional) If you want to delete the graph section completely, click Delete.
Click Yes.
You have the option to generate the report by clicking Generate Report.
The following message appears:
© 2022 FireEye Security Holdings US LLC
447
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
Editing the Graph Section of a Custom Report Using the Web
UI
Follow these steps to edit the graph section of a new custom report for managed
appliances using the Central Management appliance Web UI. You can change the graph
characteristics that you want displayed in the section of a custom report. When you change
characteristics of the graph section of a new custom report, the updated report section
overwrites the existing report section.
You can edit the graph section of a new custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
l
448
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have added one or more graph sections to the custom report using the Central
Management Web UI. For details about how to add a graph to a section of a custom
report, see Adding Graphs to a Custom Report Using the Web UI on page 445.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
To edit the graph section of a new custom report:
1. In the Custom Reports page, locate the report section whose graph you want to edit.
2. Click the action icon (
).
3. Click Edit. The Configure Section window opens.
4. Click the Graph icon. In the Visualization Type area, a green check mark indicates
that a graph is selected.
5. Click Next. The graph section details and settings are displayed.
6. In the Section Details area, change the name of the graph for your custom report
section.
7. In the Graph Type drop-down menu, change the graph selection you want to view
for the custom report. The available graph options depend on the appliance that is
connected to your Central Management appliance.
8. (Optional) To preview the graph settings, select the Preview checkbox. The
characteristics of the graph (such as a bar graph) that you changed is displayed.
If you need to refresh the content, click the refresh icon (
).
9. Click Save.
10. Drag the graph section to the intended position on the custom report.
You have the option to generate the report by clicking Generate Report.
The following message appears:
© 2022 FireEye Security Holdings US LLC
449
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
Cloning a Graph Section of a Custom Report Using the Web UI
Follow these steps to clone a graph section of a custom report and save it as a new section
using the Central Management appliance Web UI.
The new graph section inherits the characteristics from the existing graph section. When
you clone the characteristics of an existing report, the updated report will not overwrite the
existing section.
You can clone a graph section of a new custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page. A dialog box prompts you to confirm your changes.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To clone a graph section of a custom report:
1. In the Generated Custom Reports portion of the Custom Reportspage, locate the
report whose section or characteristics you want to clone.
2. Click the action icon (
450
).
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
3. Click Clone. The graph characteristics of the existing report section are copied as a
new section.
© 2022 FireEye Security Holdings US LLC
451
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
4. Click Edit. The Configure Section window opens for the relevant report section. In
the Visualization Type area, a green check mark indicates that a graph is selected.
5. Click Next. The graph section details and settings are displayed.
6. Change the data you want displayed.
7. Click Save.
8. Drag the section to the intended position in the custom report.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
452
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
Deleting a Graph Section From a Custom Report Using the Web
UI
Follow these steps to delete a graph section from a custom report for managed appliances
using the Central Management appliance Web UI.
You can delete a graph section from a custom report only using the Web UI.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have added one or more graph sections to a new custom report for a managed
appliance using the Central Management Web UI. For details about how to add a
graph to a section of a custom report, see Adding Graphs to a Custom Report Using
the Web UI on page 445.
To delete a graph section from a custom report:
1. In the Custom Reports page, locate the graph section you want to delete.
2. Click the action icon (
© 2022 FireEye Security Holdings US LLC
).
453
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
3. Click Delete.
The graph section is removed from the custom report.
You must generate the report for the changes to take effect.
Configuring Tables for Custom Reports
You can configure any number of table sections for your custom reports from scratch for
managed appliances by using the Central Management appliance Web UI:
l
l
Adding Tables to a Custom Report Using the Web UI below
Defining Filters for Table Attributes on a Custom Report Section Using the Web UI
on page 458
l
Editing the Table Section of a Custom Report Using the Web UI on page 460
l
Cloning a Table Section of a Custom Report Using the Web UI on page 472
l
Deleting a Table Section From a Custom Report Using the Web UI on page 464
A custom report can contain one or more table sections. You can choose the attributes for
each section individually. The attributes are the table columns that you can select in a
custom report. You can use filter options to define the match criteria for table columns that
are displayed in each section of the custom report. For details about how to define filters
for table attributes in a custom report section, see Defining Filters for Table Attributes on a
Custom Report Section Using the Web UI on page 458.
When you select the csv output format, xml output format, or json output format to
write the custom report to a CSV file, XML file, or JSON file, you can preview only 5
rows. When you select the pdf output format to write the custom report to an Adobe
PDF file, you can preview 5, 25, 50, or 100 rows.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report. For details about how to define
the settings for the custom report, see Defining Settings in a Custom Report Using
the Web UI on page 440.
Adding Tables to a Custom Report Using the Web UI
Follow these steps to add a table to a section of a custom report for managed appliances
using the Central Management appliance Web UI. You can modify the table settings to
454
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
change the content in the custom report.
You can add a table to a section of a custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
To add a table to a section of a custom report section:
1. In the Custom Reports page, enter the report title of the report to be modified.
2. Click Next Step.
3. In the next page, click Add Section. The Configure Section window opens.
4. Click the Table icon. In the Visualization Type area, a green check mark indicates
that a table is selected.
5. Click Next. The table section details and settings are displayed.
© 2022 FireEye Security Holdings US LLC
455
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
6. In the Section Details area:
l
Enter the name of the table for your custom report section.
l
(Optional) Enter a description to define the report section.
7. In the Table Settings area:
l
l
Choose the type of data and table from the Table Type drop-down menu.
The available table options depend on the appliance that is connected to your
Central Management appliance.
In the Select Table Columns area, select the columns you want to view for
the custom report. The available column options are based on the table
option you selected.
You cannot select the columns to view for the following table types:
l
Appliance Status Report
l
Sensor Status Report
l
Email Counters Hourly Stats
l
URL Counters in Email Hourly Stats
8. (Optional) To preview the table settings, select the Preview checkbox. The table
columns that you selected are displayed.
456
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
If you need to refresh the content, click the refresh icon (
).
This icon also allows you to preview the new settings while the Preview checkbox
is selected.
9. Click Save.
If you want to define the filter selection criteria of a table, click Next. For
details about how to filter table attributes on a report section, see Defining
Filters for Table Attributes on a Custom Report Section Using the Web UI on
the next page.
10. (Optional) If you want to delete the table section completely, click Delete.
Click Yes.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
© 2022 FireEye Security Holdings US LLC
457
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Defining Filters for Table Attributes on a Custom Report
Section Using the Web UI
Follow these steps to define filters for table attributes on a custom report section for
managed appliances using the Central Management appliance Web UI. You can use filter
options to define the match criteria for attributes that are the table columns displayed in
each section of the custom report.
You can define filters for table attributes on a custom report section only using the
Web UI.
You cannot define filters for the following table types:
l
Appliance Status Report
l
Sensor Status Report
l
Email Counters Hourly Stats
l
URL Counters in Email Hourly Stats
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
Prerequisites
l
l
l
458
Access to the Web UI of the Central Management appliance as Admin, Analyst or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have added one or more table sections to a custom report using the Central
Management Web UI. For details about how to add a table to a section of a custom
reports, see Adding Tables to a Custom Report Using the Web UI on page 454.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
To define filters for table attributes on a custom report section:
1. In the Settings page, click Next. The filter selection area is displayed.
2. In the Add Filters area:
l
l
Choose an attribute. The available options depend on the table option you
selected.
Choose the operation (for example, In, Not In, Like, or =) to match the
particular attribute. The available operations depend on the attribute you
selected.
l
Enter any value you want to associate with the attribute.
l
Choose And or Or as the logical operation to associate with the attribute.
l
Click Add Filter. You can add multiple filters at one time.
l
To delete a filter, click the Delete (trash can) icon.
3. Repeat the previous step for each filter you want to define.
4. In the Additional Filters area:
l
l
Select either Not Acknowledged, Acknowledged, or Both. The default value
is Not Acknowledged.
(Optional) In the Limit field, enter the number of rows that you want
displayed in the output.
© 2022 FireEye Security Holdings US LLC
459
Central Management System Administration Guide
l
CHAPTER 29: Working with Reports for Managed Appliances
Choose All Sensors or the applicable sensor or sensor-enabled integrated
appliance that is connected to this Central Management appliance.
The options in the Additional Filters area are based on the table option
you selected.
5. (Optional) To preview the table settings, select the Preview checkbox. The table
columns that you selected are displayed.
If you need to refresh the content, click the refresh icon (
).
This icon also allows you to preview the new settings while the Preview checkbox
is selected.
6. Click Save.
If there is a problem with the filter criteria that you defined, the following message
appears. Correct the filter definition.
Editing the Table Section of a Custom Report Using the Web UI
Follow these steps to edit the table section in a custom report for managed appliances
using the Central Management appliance Web UI. You can change the table columns that
you want displayed in the section of a custom report. When you change attributes of the
table section of a custom report, the updated report section overwrites the existing report
section.
You can edit the table section of a custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
460
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Customizing Reports for Managed Appliances
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have added one or more table sections to a new custom report for a managed
appliance using the Central Management Web UI. For details about how to add a
table to a section of a custom report, see Adding Tables to a Custom Report Using
the Web UI on page 454.
To edit the table section of a custom report:
1. In the Custom Reports page, locate the report section whose attribute you want to
edit.
2. Click Edit. The Configure Section window opens for the relevant report section. In
the Visualization Type area, a green check mark indicates that a table is selected.
3. Click Next. The table section details and settings are displayed.
4. In the Section Details area:
l
l
Change the name of the table for your custom report section.
(Optional) In the Description field, enter a description to define the report
section.
5. In the Table Settings area:
l
Change the table type and data from the Table Type drop-down menu. The
available table options depend on the appliance that is connected to your
Central Management appliance.
© 2022 FireEye Security Holdings US LLC
461
Central Management System Administration Guide
l
CHAPTER 29: Working with Reports for Managed Appliances
In the Select Table Columns area, select the columns you want to view for
the custom report. The available column options are based on the table
option you selected.
6. (Optional) To preview the graph settings, select the Preview checkbox. The table
attributes that you changed are displayed.
If you need to refresh the content, click the refresh icon (
).
7. Click Save.
8. Drag the table section to the intended position in the custom report.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
Cloning a Table Section of a Custom Report Using the Web UI
Follow these steps to clone a table section of a custom report and save it as a new table
section using the Central Management appliance Web UI.
The new table section inherits the attributes from the existing table section. When you clone
the attributes of an existing report, the updated report will not overwrite the existing
section.
You can clone a table section of a new custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
462
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Customizing Reports for Managed Appliances
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To clone a table section of a custom report:
1. In the Generated Custom Reports portion of the Custom Reportspage, locate the
report whose section or characteristics you want to clone.
2. Click the action icon (
).
3. Click Clone. The table attributes of the existing report section are copied as a new
section.
4. Click Edit. The Configure Section window opens for the relevant report section. In
the Visualization Type area, a green check mark indicates that a table is selected.
5. Click Next. The table section details and settings are displayed.
6. Change the data you want displayed.
7. Click Save.
© 2022 FireEye Security Holdings US LLC
463
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
8. Drag the section to the intended position in the custom report.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
Deleting a Table Section From a Custom Report Using the Web
UI
Follow these steps to delete a table section from a custom report for managed appliances
using the Central Management appliance Web UI.
You can delete a section from a custom report only using the Web UI.
Prerequisites
l
l
464
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have added one or more table sections to a new custom report for a managed
appliance using the Central Management Web UI. For details about how to add a
table to a section of a custom report, see Adding Tables to a Custom Report Using
the Web UI on page 454.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
To delete a table section from a custom report:
1. In the Custom Reports page, locate the table section you want to delete.
2. Click the action icon (
).
3. Click Delete.
The table section is removed from the custom report.
You must generate the report for the changes to take effect.
Creating a Custom Report from a Predefined Report
Template
You can clone a predefined report template and edit its attributes to generate a custom
report. When you select the Show Pre-populated Reports checkbox in the Generated
Custom Reports table, you can view all the available static reports as predefined report
templates. The available predefined report templates depend on the appliance that is
connected to your Central Management appliance. The predefined report template shows
data generated during the past 3 months by default. After you clone a predefined report
template, you can change the report settings, add sections, edit sections, clone sections, or
delete sections.
If your Central Management appliance is connected to an Email Security — Server Edition
appliance, you can create a custom report based on a clone of the following predefined
report templates:
l
Email Executive Summary
l
Email Activity
l
Email Hourly Stat
For detailed information about reports on the Email Security — Server Edition appliance,
refer to the "Reports" chapter of the Email Security — Server Edition User Guide.
© 2022 FireEye Security Holdings US LLC
465
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
If your Central Management appliance is connected to an File Protect appliance, you can
create a custom report based on a clone of the File Executive Summary predefined report
template. For detailed information about reports on the File Protect appliance, refer to the
"Reports" chapter of the File Protect User Guide.
If your Central Management appliance is connected to a Network Security appliance, you
can create a custom report based on a clone of the following predefined report templates:
l
Executive Summary
l
Callback Server
l
Infected Hosts Trend
l
Malware Activity
For detailed information about reports on the Network Security appliance, refer to the
"Reports" chapter of the Network Security User Guide.
If your Central Management appliance is connected to an IPS-enabled Network Security
appliance, you can create a custom report based on a clone of the following predefined
report templates as a PDF file or as a CSV file:
l
IPS Executive Summary
l
IPS Top N Attacks
l
IPS Top N Attackers
l
IPS Top N MVX-Correlated
l
IPS Top N Victims
For detailed information about IPS-specific reports, refer to the "IPS Reports" chapter of the
Network Security IPS Feature Guide.
You can clone a predefined report template only using the Web UI.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
Creating a Custom Report from a Predefined Report Template
Using the Web UI
Follow these steps to create a custom report from a predefined report template using the
Central Management appliance Web UI.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
466
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
To create a clone of a predefined report template:
1. In the Web UI, choose Reports > Custom Reports.
2. Select the Show Pre-populated Reports checkbox. All the available static reports are
displayed as predefined report templates.
3. In the Generated Custom Reports table, locate the report template you want to
clone.
4. Click the action icon (
) in the Action column.
5. Click Clone. The attributes or characteristics for each section of the report template
appear.
© 2022 FireEye Security Holdings US LLC
467
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
6. Drag the section to the intended position in the custom report.
7. To edit the table attributes or graph characteristics of a section and save it as part of
a new report, click Edit.
For details about how to edit a graph section, see Editing the Graph Section of a
Custom Report Using the Web UI on page 448. For details about how to edit a table
section, see Editing the Table Section of a Custom Report Using the Web UI on
page 460.
8. To create a clone of a section, click Clone. The attributes of the existing report
section are copied as a new section.
9. If you want to delete a clone of the applicable section from the report, click Delete.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
468
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
Editing and Cloning Reports That Have Been Generated
You can edit and clone reports that have been generated by using the Central Management
appliance Web UI:
l
l
l
l
Editing the Table Attributes of a Generated Custom Report Using the Web UI below
Editing the Graph Sections of a Generated Custom Report Using the Web UI on the
next page
Cloning a Table Section of a Custom Report Using the Web UI on page 472
Cloning a Graph Section of a Generated Custom Report Using the Web UI on
page 473
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
Editing the Table Attributes of a Generated Custom Report
Using the Web UI
Follow these steps to edit the attributes that are the table columns of a custom report that
have been generated for managed appliances using the Central Management appliance
Web UI. When you change the table attributes of a custom report that has been generated,
the updated report overwrites the existing report.
You can edit the table attributes of a custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
© 2022 FireEye Security Holdings US LLC
469
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To edit the table attributes of a generated custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Generated Custom Reports table, locate the custom report you want to edit.
3. Click the action icon (
) in the Action column.
4. Click Edit. Each section of the report appears in the custom report section
configuration page.
For details about how to edit the table section in a custom report, see Editing the
Table Section of a Custom Report Using the Web UI on page 460.
Editing the Graph Sections of a Generated Custom Report
Using the Web UI
Follow these steps to edit the graph sections of a custom report that have been generated
for managed appliances using the Central Management appliance Web UI. You can
change the graph characteristics that you want displayed in the report section of a custom
report that has been generated. When you change characteristics of the graph section of a
new custom report, the updated report overwrites the existing report.
You can edit the graph section of a generated custom report only using the Web UI.
470
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To edit the graph sections of a generated custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Generated Custom Reports table, locate the custom report you want to edit.
3. Click the action icon (
) in the Action column.
4. Click Edit. Each section of the report appears in the custom report section
configuration page.
For details about how to edit the graph section in a custom report, see Editing the
Graph Section of a Custom Report Using the Web UI on page 448.
© 2022 FireEye Security Holdings US LLC
471
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Cloning a Table Section of a Custom Report Using the Web UI
Follow these steps to clone a table section of a custom report and save it as a new table
section using the Central Management appliance Web UI.
The new table section inherits the attributes from the existing table section. When you clone
the attributes of an existing report, the updated report will not overwrite the existing
section.
You can clone a table section of a new custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To clone a table section of a custom report:
1. In the Generated Custom Reports portion of the Custom Reportspage, locate the
report whose section or characteristics you want to clone.
2. Click the action icon (
472
).
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
3. Click Clone. The table attributes of the existing report section are copied as a new
section.
4. Click Edit. The Configure Section window opens for the relevant report section. In
the Visualization Type area, a green check mark indicates that a table is selected.
5. Click Next. The table section details and settings are displayed.
6. Change the data you want displayed.
7. Click Save.
8. Drag the section to the intended position in the custom report.
You have the option to generate the report by clicking Generate Report.
The following message appears:
The custom report is added to the top of the generated custom report list. The report
status is displayed as "In progress" in the Generated Custom Reports table. The
status is updated as soon as the generated report is available.
Cloning a Graph Section of a Generated Custom Report Using
the Web UI
Follow these steps to clone a graph section of an existing custom report and save it as a
new section for managed appliances using the Central Management appliance Web UI.
You can create a new graph section based on a clone of an existing section. The new graph
section inherits the match characteristics from the graph section of the existing report.
© 2022 FireEye Security Holdings US LLC
473
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
When you clone the characteristics of an existing report, the updated report will not
overwrite the existing section.
You can clone a graph section of a generated custom report only using the Web UI.
If you want to completely delete a section of a custom report, click Delete in the
Configure Section page.
To preview your report, click the toggle button (
) in the custom report
configuration page. Click the button again to return to edit mode.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report. For details about how to define
the settings for the custom report, see Defining Settings in a Custom Report Using
the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To clone a graph section of a generated custom report:
1. In the Web UI, choose Reports > Custom Reports.
2. In the Generated Custom Reports table, locate the custom report you want to clone.
3. Click the action icon (
) in the Action column.
4. Click Clone. The characteristics for each section of the report appears.
For details about how to clone a graph section in a custom report, see Cloning a
Graph Section of a Custom Report Using the Web UI on page 450.
474
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
Sending, Downloading, and Deleting Custom Reports
You can send, download, and delete custom reports that have been generated by using the
Central Management appliance Web UI:
l
Sending Generated Custom Reports by Email Using the Web UI below
l
Downloading a Generated Custom Report Using the Web UI on page 477
l
Deleting a Generated Custom Report Using the Web UI on page 478
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
Sending Generated Custom Reports by Email Using the Web UI
Use the Generated Custom Reports table to automatically send a generated custom report
as an email attachment to a list of recipients for managed appliances using the Central
Management appliance Web UI.
You can send generated custom reports by email only using the Web UI.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report using the Central Management
Web UI. For details about how to define the settings for the custom report, see
Defining Settings in a Custom Report Using the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
© 2022 FireEye Security Holdings US LLC
475
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
To send a generated custom report by email:
1. In the Web UI, choose Reports > Custom Reports.
The page lists the custom reports for a managed appliance that have already been
generated in the custom reports database.
2. In the Generated Custom Reports table, select the generated custom report.
3. Click the action icon (
) in the Action column.
4. Click Email. The Email Report window opens.
5. In the Recipients field, enter the email address of the report recipient. To add
multiple recipients, press Enter for each additional email address.
To delete a recipient, click X next to the email address you want to delete.
476
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Customizing Reports for Managed Appliances
6. Click Send.
The Central Management appliance sends the generated custom report by email to
the intended recipients. The following message appears:
Downloading a Generated Custom Report Using the Web UI
Follow these steps to download a generated custom report from the Central Management
appliance to your local desktop using the Central Management appliance Web UI.
You can download a generated custom report only using the Web UI.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To download a generated custom report:
1. In the Web UI, choose Reports > Custom Reports.
The page lists the custom reports for a managed appliance that have already been
generated.
© 2022 FireEye Security Holdings US LLC
477
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
2. In the Generated Custom Reports table, locate the custom report you want to
download to your desktop.
3. Click the action icon (
) in the Action column.
4. Click Download.
Deleting a Generated Custom Report Using the Web UI
Use the Generated Custom Reports table to delete a custom report that has been generated
from the custom reports database for managed appliances using the Central Management
appliance Web UI.
You can delete a generated custom report only using the Web UI.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
You have defined the settings for the custom report. For details about how to define
the settings for the custom report, see Defining Settings in a Custom Report Using
the Web UI on page 440.
You have generated one or more custom reports for a managed appliance using the
Central Management Web UI.
To delete a generated custom report from the custom reports database:
1. In the Web UI, choose Reports > Custom Reports.
The page lists the custom reports for a managed appliance that have already been
generated in the custom reports database.
478
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Scheduling Reports for Managed Appliances
2. In the Generated Custom Reports table, select one or more custom reports to delete
from the custom reports database.
3. Click the action icon (
) in the Action column.
4. Click Delete. A dialog box prompts you to confirm your changes.
5. Click Yes.
The reports you selected are removed from the custom reports database.
Generating and Scheduling Reports for
Managed Appliances
All static reports that are available to all managed appliances can be generated or
scheduled. You also have the option to schedule a custom report that has been generated
on managed Email Security — Server Edition, Network Security, and File Protect
appliances. For example, the following illustration is from a Central Management
appliance that manages one or more IPS-enabled Network Security appliances. All IPSenabled Network Security static report types are included in the Report Type drop-down
list.
© 2022 FireEye Security Holdings US LLC
479
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
Generating Reports for Managed Appliances Using the
Web UI
Use the Generate Report page to generate static reports for managed appliances.
To generate static reports:
1. In the Web UI, choose Reports > Static Reports.
2. Generate the static reports as described in the User Guide for the managed appliance.
For information about generating a SmartVision alerts report, see the
Network Security SmartVision Feature Guide.
For SmartVision appliances, generate the SmartVision Alert static report as
described in the Network Security SmartVision Feature Guide. A SmartVision appliance
can be any of the following:
o
SmartVision Edition sensor
o
SmartVision-enabled Network Security sensor
o
SmartVision-enabled Network Security integrated appliance
You can generate a SmartVision Alerts report from the Web UI only. A
SmartVision Alerts report cannot be customized.
For IPS-enabled Network Security appliances, generate the static reports as described
in the Network Security IPS Feature Guide.
480
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Scheduling Reports for Managed Appliances
Scheduling Reports for Managed Appliances Using the
Web UI
Use the Schedule Report page to schedule static or custom reports for managed
appliances.
You can schedule custom reports that have been generated for managed Email
Security — Server Edition, Network Security, and File Protect appliances if you select
the Make Schedulable checkbox in the Reports > Custom Reports page on the
Central Management appliance.
To schedule static reports:
1. In the Web UI, choose Reports > Schedule Reports.
2. Schedule the static reports as described in the User Guide for the managed appliance.
For IPS-enabled Network Security appliances, schedule the static reports as
described in the IPS Feature Guide.
NOTE: You can schedule a SmartVision Alerts report from the Web UI only.
A SmartVision Alerts report cannot be customized.
To schedule custom reports:
1. In the Central Management appliance Web UI, choose Reports > Schedule Reports.
2. In the Report Type drop-down menu under "Custom Reports", select the custom
report that has been generated for managed Email Security — Server Edition,
Network Security, and File Protect appliances.
3. In the Scheduled drop-down menu, set the time frequency:
l
hourly
l
daily
l
weekly
l
monthly
4. In the Time drop-down menu, set the time of day in hours and minutes (00:00).
5. If you selected a weekly report, specify the report day of the week in the WeekDay
field.
6. If you selected a monthly report, specify the report day of the month in the
MonthDay field.
© 2022 FireEye Security Holdings US LLC
481
Central Management System Administration Guide
CHAPTER 29: Working with Reports for Managed Appliances
7. In the Delivery drop-down menu, specify the delivery method. The default delivery
is email.
l
email—Deliver the custom report as a file attached to email.
l
file—Deliver the custom report as a file linked from the Web UI.
8. In the Time Frame drop-down menu, select the time period for this custom report:
l
past day—Report covers analysis generated during the past 24 hours.
l
past week—Report covers analysis generated during the past 7 days.
l
past month—Report covers analysis generated during the past 1 month.
l
past 3 months—Report covers analysis generated during the past 3 months.
9. Click Schedule Report. The scheduled report is added to the top of the scheduling
list.
Generating and Scheduling Reports for Managed
Appliances Using the CLI
Use the commands in this section to generate and schedule static reports for managed
appliances. The commands are executed once; they are not stored.
NOTE: For comprehensive information about the reporting commands, see the User
Guide for the managed appliance.
NOTE: If you omit the command parameter from these commands, you will be
prompted for it, and the characters you enter will be masked for confidentiality.
NOTE: This topic describes how to execute a single command. You can also define
a profile of commands that run in sequence unattended. See Working with
Command Profiles on page 406.
To execute a command on an appliance:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Execute the command:
hostname (config) # cmc execute appliance <applianceName> command
["<command>"]
where command is a form of the report generate or report schedule command
and must be enclosed in double quotation marks.
482
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Scheduling Reports for Managed Appliances
To execute a command on a group of appliances:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Execute the command:
hostname (config) # cmc execute group <groupName> command ["<command>"]
where command is a form of the report generate or report schedule command
and must be enclosed in double quotation marks.
IMPORTANT: You can cancel the execution of outstanding commands, as
described in Canceling Outstanding Commands on page 398.
Example
This example generates an Alert Details report on behalf of the NX-04 appliance.
hostname (config) # cmc execute appliance NX-04 command "report generate type
Alert_Details report_format csv report_detail normal alert_type malwareobject time_frame past_month transport file"
Execute report command. Check email or WebUI for report.
© 2022 FireEye Security Holdings US LLC
483
Central Management System Administration Guide
484
CHAPTER 29: Working with Reports for Managed Appliances
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 30: Checking Status
and Health of Managed
Appliances
There are several ways to view the status and health of managed appliances. An
administrator can recheck the status and reset the connection status from the Central
Management Web UI. From the Central Management CLI, an administrator can define the
following settings for status and health checks on managed appliances:
l
l
l
l
l
Enable/Disable—Whether status checks will be performed on all managed
appliances or specific managed appliances. By default, status checks are enabled.
Interval—Time delay between the start of one check and the next check. The default
is 60 seconds.
Timeout—The amount of time to wait for an appliance to send its status to Central
Management appliance. If a timeout occurs, a status failure is logged and the
connection between the appliance and the Central Management appliance is broken.
The default is 30 seconds.
Force Check—Forces an immediate status check of all managed appliances, even if
checking is disabled overall with the no cmc status enable command.
Status Test Criteria—Enable or disable testing the status of a specific criterion (such
as the fan, support key, and so on) on all managed appliances.
NOTE: Forced checking and status tests are not performed on a specific appliance if
status checks are disabled for that appliance.
NOTE: See Defining Status and Health Check Settings for Managed Appliances
Using the CLI on page 492 for information about changing these settings.
© 2022 FireEye Security Holdings US LLC
485
Central Management System Administration Guide CHAPTER 30: Checking Status and Health of Managed Appliances
Prerequisites
l
Monitor, Operator, or Admin access to view status and health
l
Admin access to recheck and reset status and configure status check criteria
Checking Status and Health of Managed
Appliances Using the Web UI
Use the Sensors page to check the status and health of managed appliances.
The Connection and Health columns provide high-level information. Additional
information is displayed if you hover over an icon in the columns, as shown in the
following examples.
Detailed information is displayed when you click the appliance name in the Sensor
column, as shown in the following example and described in Appliance Information on
page 365.
486
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking Status and Health of Managed Appliances Using the Web UI
Refreshing the Status Information
An administrator can do the following when there are connectivity or health warnings:
l
l
Recheck collects the appliance details and health status, and updates the
information in the Connection and Health columns and the expanded section.
Reset checks the connection status when the Central Management appliance has no
connectivity to the appliance. Reset also restores the connectivity if the underlying
cause is removed. Connectivity loss can happen for the following reasons:
l
l
The appliance is offline.
The appliance is online but there is a serious issue (for example, the database
or a process is down, an out-of-memory condition exists, or an incorrect
IP address was configured for the appliance).
To check status and health:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Hover over icons in the Connection and Health columns to view additional
information.
3. Click the appliance name in the Sensor column to view appliance details.
To recheck the status:
l
Click Select > Recheck in the Action column in the row for the appliance you want
to recheck.
© 2022 FireEye Security Holdings US LLC
487
Central Management System Administration Guide CHAPTER 30: Checking Status and Health of Managed Appliances
IMPORTANT! The Recheck option is not available if the managed
appliance initiated the connection to the Central Management appliance, as
described in the System Administration Guide or Administration Guide for the
managed appliance.
To reset connectivity:
l
Click Reset in the Connection column for the appliance.
Checking Status and Health of Managed
Appliances Using the CLI
Use the commands in this section to check the status and health of managed appliances.
To view status:
1. Go to CLI enable mode:
hostname > enable
2. View status:
l
To view high-level status of all appliances:
hostname # show cmc appliances brief
l
To view health check criteria and detailed status information:
hostname # show cmc status
l
To view the connection status of all appliances:
hostname # show cmc appliances
l
To view comprehensive information about a specific appliance:
hostname # show cmc appliances <applianceName>
l
To view comprehensive information about all appliances:
hostname # show cmc appliances detail
NOTE: You can also run Network Security network deployment checks using the
cmc execute appliance <NXApplianceName> command deployment check
commands. For details, see the Network Security System Administration Guide.
488
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking Status and Health of Managed Appliances Using the CLI
Examples
show cmc appliances brief
This example shows that three appliances are enabled for Central Management
management, one appliance is disconnected, and two appliances failed status checks.
hostname # show cmc appliances brief
Appliance
Address
Enabled
--------------------ex-03
172.30.1.1
yes
nx-02
172.70.1.1
yes
fx-04
172.20.1.1
yes
nx-01
172.70.2.1
yes
nx-05
172.40.1.1
yes
Connected
--------no
yes
yes
yes
yes
Health
-----CRIT
ok
WARN
ok
ok
Product
------eMPS
wMPS
fMPS
wMPS
wMPS
show cmc status
This example shows the status check settings and criteria, and then shows the status of
each appliance that can be managed by this Central Management appliance.
hostname-01 # show cmc status
Status checking enabled: yes
Check interval:
60 seconds
Timeout:
30 seconds
Status criteria:
"alive" test enabled:
"content-key" test enabled:
"disk_space" test enabled:
"eula" test enabled:
"fan" test enabled:
"feature: test enabled:
"power_supply" test enabled:
"product_key" test enabled:
"raid" test enabled:
"support_key" test enabled:
"temperature" test enabled:
"user_role" test enabled:
Appliance ex-03:
Last checked:
Connected at last check:
Replied to last check:
Last check succeeded:
Failed checks:
alive failed
content_key failed
disk_space failed
eula failed
fan failed
feature failed
power_supply failed
product_key failed
raid failed
support_key failed
temperature failed
user_role failed
© 2022 FireEye Security Holdings US LLC
yes
yes
yes
yes
yes
yes
yes
yes
yes
yes
yes
yes
2014/12/23 21:28:02
no
no
no
489
Central Management System Administration Guide CHAPTER 30: Checking Status and Health of Managed Appliances
Appliance nx-02:
Last checked:
Connected at last check:
Replied to last check:
Last check succeeded:
Appliance fx-04:
Last checked:
Connected at last check:
Replied to last check:
Last check succeeded:
Failed checks:
content_key failed
2014/12/23 21:28:02
yes
yes
yes
2014/12/23 21:28:02
yes
yes
no
show cmc appliances
This example displays the status of each appliance that can be managed by this Central
Management appliance. In this case, the Network Security appliance initiated the request
to be managed, the Email Security — Server Edition appliance is not currently connected,
and the Central Management appliance initiated the connection between itself and the File
Protect appliance.
hostname # show cmc appliances
Appliance nx-02:
Address:
Enabled:
Connected:
Status check OK:
Version compatible:
172.70.1.1
yes
yes (client-initiated)
yes
yes
Appliance ex-03:
Address:
Enabled:
Connected:
Status check OK:
Version compatible:
172.30.1.1
yes
no
no
unknown
Appliance fx-04:
Address:
Enabled:
Connected:
Status check OK:
Version compatible:
172.20.1.1
yes
yes (server-initiated)
no
yes
show cmc appliances <applianceName>
This example displays the status and settings for the nx-02 appliance. The Central
Management appliance initiated the connection with the appliance.
hostname # show cmc appliances nx-02
Appliance nx-02
Connection status:
Connected:
Connection failure reason:
Connection last formed:
490
yes (server-initiated)
None
2014/12/23 21:13:37
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Checking Status and Health of Managed Appliances Using the CLI
Connection last broken:
Last connection attempt:
Next connection attempt:
Current time:
Status check OK:
Server username on client:
Client username on server:
Appliance Status:
Client software version:
Client product name:
Client software match:
Client software compatible:
Appliance ID:
Product model:
Content version:
Content channel:
Content sharing type:
Configuration:
Enabled:
Address:
SSH port:
Web UI protocol:
Web UI HTTP port:
Web UI HTTPS port:
Auto-connect:
Status check enabled:
Client requests enabled:
Comment:
Authentication:
Authentication type:
password username:
password password:
ssh-dsa2 username:
ssh-dsa2 identity:
ssh-rsa2 username:
ssh-rsa2 identity:
2014/12/23 21:13:36
2014/12/23 21:13:36
2014/12/23 21:25:36
yes
admin
cmcclient
wMPS (wMPS) 7.7.0.420682
wMPS Power
no
yes
002590AEE884
FireEyeNX900
432-lb.198
stable
all
yes
172.10.0.0
22
http
9023 (active)
443
yes
yes
yes
password
admin
********
admin
admin
Validation for client-initiated connections:
Source address:
(same as main address)
Source port:
(no restriction)
show cmc appliances detail
The show cmc appliances detail command output is the same as the show cmc
appliances <applianceID> command output, except it displays information about all
managed appliances, not just one.
© 2022 FireEye Security Holdings US LLC
491
Central Management System Administration Guide CHAPTER 30: Checking Status and Health of Managed Appliances
Defining Status and Health Check
Settings for Managed Appliances Using
the CLI
Use the commands in this section to define status and health check settings for managed
appliances.
To define status check settings:
1. Enable the CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Define settings:
l
To enable status checking on all managed appliances:
hostname (config) # cmc status enable
l
To disable status checking on all managed appliances:
hostname (config) # no cmc status enable
l
To enable status checking on a specific managed appliance:
hostname (config) # cmc appliance <applianceName> check-status
l
To disable status checking on a specific managed appliance:
hostname (config) # no cmc appliance <applianceName> check-status
l
To set the interval between status checks:
hostname (config) # cmc status check-interval <seconds>
l
To specify the amount of time to wait for an appliance to send its status:
hostname (config) # cmc status timeout <seconds>
l
To force an immediate check of all managed appliances:
hostname (config) # cmc status force-check
3. Save your changes:
hostname (config) # write memory
To define the status check criteria to include:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Display the current criteria status:
hostname (config) # show cmc status
492
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Defining Status and Health Check Settings for Managed Appliances Using the CLI
3. Specify the criteria to include:
l
To enable status checking of a specific criterion:
hostname (config) # cmc status criteria <criterionName> enable
l
To disable status checking of a specific criterion:
hostname (config) # no cmc status criteria <criterionName> enable
4. Repeat the previous step for each test you want to enable or disable.
5. Save your changes:
hostname (config) # write memory
Example
This example increases the time period between status checks to 90 seconds, and disables
the temperature and raid criteria.
hostname (config) cmc status check-interval 90
hostname (config) # no cmc status criteria temperature enable
hostname (config) # no cmc status criteria raid enable
© 2022 FireEye Security Holdings US LLC
493
Central Management System Administration Guide CHAPTER 30: Checking Status and Health of Managed Appliances
494
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
CHAPTER 31: Updating Managed
Appliances
You can update managed appliances with the latest appliance system image and guest
images from the Central Management Web UI or CLI. When the Central Management
appliance is in "online" mode (that is, connected to the DTI network), checks for newer
available versions are automatically performed for managed appliances that have the
appropriate licenses installed. In online mode, the Central Management appliance stores
the images in a DTI cache on the Central Management appliance. If an update is requested,
and the requested image is not already in the cache, the Central Management appliance
downloads it. A Central Management administrator can manually download images to the
cache when it is convenient instead of waiting for an update request. This can save
bandwidth and shorten the maintenance window for updating appliances. For details, see
Understanding the DTI Cache on page 117 and Downloading Software Updates to the DTI
Cache on page 119.
You can update multiple appliances at the same time. Each appliance is updated
independently and does not depend on updates being completed on other appliances.
However, if the images are not already in the cache, and if the DTI source server is very
busy or if the connection to it is slow, the update could time out.
System images should be updated before you install guest images. If you request system
image and guest images updates at the same time, the system image is updated first.
However, if the appliance is rebooted before the guest images are downloaded (for
example, if you choose to automatically reboot the appliance after the system image
update), the request to download guest images is lost, so you must request it again.
You could instead stagger the updates to minimize the impact to the system. For example,
you could update the appliance software images, but then wait until off-hours or a
maintenance window to update the guest images, because guest images take longer to
download and install.
© 2022 FireEye Security Holdings US LLC
495
Central Management System Administration Guide
CHAPTER 31: Updating Managed Appliances
IMPORTANT! If an appliance is running a system image version that your
Central Management appliance no longer supports, a message is displayed on
the Central Management Dashboard, and you should update the appliance
immediately. Data will not be aggregated from that appliance to the Central
Management appliance until you update, and you will be unable to make
configuration changes on behalf of the appliance.
NOTE: These procedures show how to update managed appliances when the
Central Management appliance is in "online" mode and connected to the
DTI network. When the Central Management appliance is not connected to the
DTI network, it can be in "local" or "URL" mode, in which it downloads the
updates from a file that is either stored locally or hosted on a local site identified
by a URL. For details, see the FireEye DTI Offline Update Portal Guide.
NOTE: These procedures show how to update software images and guest images.
By default, security content is automatically downloaded to the cache and
updated on managed appliances. For details about changing the update settings,
see the System Administration Guide or Administration Guide for the managed
appliance.
Prerequisites
l
Admin access
l
DTI network access
l
FIREEYE_SUPPORT license on each managed appliance for system image updates
l
CONTENT_UPDATES license on each managed appliance for security content
updates
Updating Managed Appliances Using the
Web UI
Use the appliance update page to determine whether the latest appliance system image
and guest images are installed, and to update them as needed. You can also use this page
to view the installed security content version.
NOTE: You can perform this procedure whether the managed appliance uses CMS,
CDN, or DTI as its DTI source server. (See Changing the Active Setting for a DTI
Service on page 109 for details about these options.)
496
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Updating Managed Appliances Using the Web UI
This page contains the information described in the following table.
Field
Description
Sensor
(hostname)
The display name of the appliance.
Connection
The status of the connection between the Central Management
appliance and the managed appliance.
The connection is established.
The connection failed; the appliance cannot be updated until
the connection is reestablished.
Product
The type of appliance.
System
Software
Status
The installed appliance software version. If other versions are available,
you can select a version or select none to do this later.
Detection
Engine Status
Whether the latest guest images are installed. If not, you can select latest
to install them or select none to do this later.
NOTE: This column is empty for an appliance in MVX sensor mode.
Sensor
Update Status
Info
Indicators and information about current and available versions or the
update being performed.
All available guest images and patches have been updated.
An error occurred, such as the update timing out.
New updates are available.
The installed appliance software version is not supported by
the Central Management appliance.
An immediate reload is required to complete the upgrade.
If updates are available for an appliance, the checkbox in the Sensor (hostname) column
can be selected, and a message is displayed in the column. For example:
© 2022 FireEye Security Holdings US LLC
497
Central Management System Administration Guide
CHAPTER 31: Updating Managed Appliances
To update an appliance:
1. Click the Appliances tab. The Sensors tab should be selected.
2. On the Sensors page, click Actions > Update Sensors.
3. If you want to filter by appliance group, select the group in the Sensor Group dropdown list.
4. Select the checkbox for each appliance you want to update.
5. To update the system image:
a. Select the version from the drop-down list in the System Software Status
column. For example:
If you want to postpone this update, select none.
b. The appliance must be rebooted after the upgrade. If you want this to happen
automatically, select the Auto Reboot checkbox.
6. If the guest images need to be updated, select latest in the Detection Engine Status
column. (If you want to postpone this update, select none.)
NOTE: Appliances in MVX sensor mode do not have guest images, so the
Detection Engine Status column is empty.
7. Click Update Selected Sensors.
Status messages will be displayed in the Sensor Update Status Info column. For
example:
498
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Updating Managed Appliances Using the CLI
8. If you did not select auto reboot, the following message is displayed after the update
is done:
Click the Reload checkbox, and then click OK when prompted to confirm the action.
Updating Managed Appliances Using the
CLI
Use the commands in this section to update the system image and guest images for
managed appliances.
NOTE: This section provides basic commands used to update software images and
download and install default guest images. For comprehensive information about
using the CLI to update appliances, see the System Administration Guide or
Administration Guide for your appliance or the CLI Command Reference.
NOTE: To update Virtual Execution appliances, use the fenet update appliance
commands, as described in the MVX Smart Grid Guide.
To install the latest system image and reboot the appliance:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Initiate the update process:
hostname (config) # fenet appliance manage <applianceName> upgrade
3. View the progress:
hostname (config) # cmc execute appliance <applianceName> command "show
fenet image status"
© 2022 FireEye Security Holdings US LLC
499
Central Management System Administration Guide
CHAPTER 31: Updating Managed Appliances
4. Save your changes:
hostname (config) # cmc execute appliance <applianceName> command
"write memory"
To download and install guest images:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Download the latest guest images:
hostname (config) # cmc execute appliance <applianceName> command
"guest-images download"
3. Verify that the guest images download is complete:
hostname (config) # cmc execute appliance <applianceName> command "show
guest-images download"
4. Install the guest images
hostname (config) # cmc execute appliance <applianceName> command
"guest-images install"
5. Verify that the guest images are installed properly:
hostname (config) # cmc execute appliance <applianceName> command "show
guest-images"
6. Save your changes:
hostname (config) # cmc execute appliance <applianceName> command
"write memory"
NOTE: It can take a long time to download guest images. If you need to cancel the
download, use the cmc execute appliance <applianceName> command "guestimages download cancel" command. To resume the download, use cmc execute
appliance <applianceName> command "guest-images download resume"
command.
Example
This example installs the latest guest images on the FX-05 appliance.
hostname (config) # cmc execute appliance FX-05 command "guest-images
install"
===========Appliance FX-05==========
Execution was successful.
Execution output:
Found guest-images that can be installed
Installing guest-images
Terminating running work orders and virtual analysis subsystem ........
Restarting WebUI ....
Installation complete!
500
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About Custom IOC Feeds
CHAPTER 32: Configuring Custom
IOC Feeds
This chapter covers the following information:
l
About Custom IOC Feeds below
l
Enabling or Disabling Custom IOC Feeds on page 503
l
Creating a Custom Blacklist from Third-Party Feeds on page 510
l
Uploading a Third-Party Feed on page 512
l
Viewing Custom Feed Details on page 514
l
Deleting Third-Party IOC Feeds Using the Web UI on page 517
l
Downloading a Third-Party Feed Using the Web UI on page 519
About Custom IOC Feeds
The Central Management appliance can receive indicators of compromise (IOCs) from the
following custom feeds.
l
l
l
Third-party feeds send IOCs to the Central Management appliance from a thirdparty (non-FireEye) product.
DTI feeds provide files from FireEye's Dynamic Threat Intelligence (DTI) cloud.
A single local feed sends IOCs to the Central Management appliance from Network
Security, Email Security — Server Edition, File Protect, and Malware Analysis
appliances. A local feed is a system-generated feed that is managed by the Central
Management appliance. You cannot upload, delete, edit, or download a local feed.
The IOCs from custom feeds are distributed to managed Network Security appliances in a
standard format. You can create customized lists of IOCs received from these feeds and use
them as a custom blacklist on the Central Management appliance. The types of IOCs are
URL indicators, IP address indicators, domain indicators, and indicators with hashes of
malicious files. You can create a list of for each type of indicator, or you can combine them
© 2022 FireEye Security Holdings US LLC
501
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
into a standard format called STIX (Structured Threat Information Expression). You
configure the managed Network Security appliances to block or allow traffic that matches
the custom blacklist. If traffic is blocked, you are notified that a block occurred. If traffic is
not blocked, an alert is created and you are notified that a match occurred.
Only one master custom blacklist is created from all the feeds. This master blacklist is
maintained on the Central Management appliance and is copied to all the managed
Network Security appliances.
IMPORTANT! Enabling third-party feeds or the local feed on the Central
Management appliance can negatively impact the performance of the appliance.
Task List for Managing Custom IOC Feeds
Complete the steps for managing custom IOC feeds in the following order:
1. Verify that the managed Network Security appliances are deployed in TAP mode or
inline mode.
2. On the Central Management appliance, enable custom IOC feeds. For details, see
Enabling or Disabling Custom IOC Feeds on the facing page.
3. Create a flat file or XML-based file in STIX format that contains custom blacklist
entries. Verify the file is accessible from the local desktop from which you access the
Central Management Web UI. For details about how to create a custom blacklist
from a third-party feed, see Creating a Custom Blacklist from Third-Party Feeds on
page 510.
4. Upload the third-party feed blacklist to a Central Management appliance. For details
about how to upload a third-party feed, see Uploading a Third-Party Feed on
page 512.
5. View the details of the malware events that matched the name of the custom
blacklist feed. For details, see Viewing Custom Feed Details Grouped by Alert Using
the Web UI on page 516.
502
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling Custom IOC Feeds
Enabling or Disabling Custom IOC Feeds
This section describes how to enable or disable a Central Management appliance to receive
indicators (IOCs) from a custom feed and distribute them to all managed Network Security
appliances or a specific managed Network Security appliance. When the custom IOC feed
feature is disabled, DTI feeds are not pushed to all managed Network Security appliances
or a specific managed Network Security appliance.
A Central Management appliance cannot distribute indicators of compromise (IOCs)
to managed SmartVision Edition sensors.
You can enable or disable the custom IOC feed features only using the CLI. Thirdparty feeds are enabled by default when you add the Network Security appliance
to the Central Management appliance. The local feed is disabled by default. DTI
feeds are automatically pushed to the managed Network Security appliance.
Enabling third-party feeds or the local feed on the Central Management appliance
can negatively impact the performance of the appliance.
IMPORTANT! IOC feeds are not supported on integrated Trellix NX 300 models
that are managed by the Central Management appliance.
When the same intel feed is added both to a standalone Network Security
appliance and to a Central Management appliance, and the Network Security
appliance is later added to the Central Management appliance, duplicate feeds are
displayed on the Network Security appliance.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
Managed Network Security appliance deployed in TAP mode or inline mode.
© 2022 FireEye Security Holdings US LLC
503
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
Enabling or Disabling Third-Party IOC Feeds on All
Appliances Using the CLI
These procedures describe how to enable or disable a Central Management appliance to
receive indicators (IOC) from a third-party feed and distribute them to all managed
Network Security appliances.
A Central Management appliance cannot distribute indicators of compromise (IOCs)
to managed SmartVision Edition sensors.
To enable a third-party feed for all managed Network Security appliances:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Enable IOCs from a third-party feed for all managed Network Security appliances.
cm-hostname (config) # custom content enable
4. Verify the status of third-party IOC feeds.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : enabled
LMS status
B9-vNX2500-1 : enabled
B9-vNX6500-1 : enabled
Bolt : enabled
SystemVX12500-1 : enabled
SystemVX12500-2 : enabled
5. Save your changes.
cm-hostname (config) # write memory
To disable a third-party feed for all managed Network Security appliances:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Disable IOCs from all third-party feeds on the CM.
cm-hostname (config) # no custom content enable
504
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling Custom IOC Feeds
4. Verify the status of IOC customizations.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : disabled
LMS status
B9-vNX2500-1 : enabled
B9-vNX6500-1 : enabled
Bolt : enabled
SystemVX12500-1 : enabled
SystemVX12500-2 : enabled
5. Save your changes.
cm-hostname (config) # write memory
Enabling or Disabling the Local Feed on All Appliances
Using the CLI
These procedures describe how to enable and disable a Central Management appliance to
receive indicators (IOCs) from the local feed and distribute them to all managed Network
Security appliances.
A Central Management appliance cannot distribute indicators of compromise (IOCs)
to managed SmartVision Edition sensors.
Enabling the local feed on the Central Management appliance can negatively impact
the performance of the appliance.
The local feed only provides data when there are actual alerts.
To enable the local feed for all managed Network Security appliances:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Enable local signature generation settings. The local feed does not work if this is not
enabled. By default, local signature generation is already enabled.
cm-hostname (config) # localsig enable
4. Enable IOCs from a third-party feed for all managed Network Security appliances.
The local feed does not work if third-party feeds are not enabled.
cm-hostname (config) # custom content enable
5. Enable IOCs from the local feed.
cm-hostname (config) # localsig localfeed enable
© 2022 FireEye Security Holdings US LLC
505
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
6. Verify the status of third-party IOC feeds.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : enabled
LMS status
B9-vNX2500-1 : enabled
B9-vNX6500-1 : enabled
Bolt : enabled
SystemVX12500-1 : enabled
SystemVX12500-2 : enabled
7. Verify the status of the local feed.
CMS1 > show localsig
LocalSig Generator
Enabled : YES
Running : running
Rule Versions : 1
Active rules : 1337
LocalFeed : Enabled
8. Save your changes.
cm-hostname (config) # write memory
To disable the local feed for all managed Network Security appliances:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. You can disable IOCs from the local feed in a number of ways:
l
Disable IOCs from the local feed on the CM.
cm-hostname (config) # no localsig localfeed enable
l
Disable IOCs from all third-party feeds on the CM. When you disable IOCs
from the third-party feeds, the IOCs from the local feed are also disabled.
cm-hostname (config) # no custom content enable
l
Disable local signature generation settings. When you disable local signature
generation settings, the IOCs from the local feed are also disabled.
cm-hostname (config) # no localsig enable
506
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling Custom IOC Feeds
4. Verify the status of third-party IOC feeds.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : disabled
LMS status
B9-vNX2500-1 : enabled
B9-vNX6500-1 : enabled
Bolt : enabled
SystemVX12500-1 : enabled
SystemVX12500-2 : enabled
5. Verify the status of the local IOC feed.
CMS1 > show localsig
LocalSig Generator
Enabled : YES
Running : running
Rule Versions : 1
Active rules : 1337
LocalFeed : Disabled
6. Save your changes.
cm-hostname (config) # write memory
Enabling or Disabling Third-Party IOC Feeds on a Specific
Appliance Using the CLI
These procedures describe how to enable or disable a Central Management appliance to
receive indicators (IOC) from a third-party feed and distribute them to a specific managed
Network Security appliance.
A Central Management appliance cannot distribute indicators of compromise (IOCs)
to managed SmartVision Edition sensors.
You can verify that this feature is disabled when you log in to the managed Network
Security appliance.
To enable a third-party feed for a specific managed Network Security appliance:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Enable IOCs from a third-party feed for a managed Network Security appliance.
cm-hostname (config) # custom content enable on lms <applianceID>
where applianceID is the Network Security appliance record name.
© 2022 FireEye Security Holdings US LLC
507
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
4. Verify the status of IOC customizations.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : enabled
LMS status
B9-vNX2500-1 : enabled
5. Save your changes.
cm-hostname (config) # write memory
To disable a third-party feed for a specific managed Network Security appliance:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Disable IOCs from a third-party feed for a specific managed Network Security
appliance.
cm-hostname (config) # no custom content enable on lms <applianceID>
where applianceID is the Network Security appliance record name.
4. Save your changes.
cm-hostname (config) # write memory
5. Log in to the CLI on the managed Network Security appliance.
6. Enable CLI configuration mode.
nx-hostname > enable
nx-hostname # configure terminal
7. Verify the status of third-party IOC feeds.
nx-hostname (config) # show custom content enable status
Custom content : disabled
508
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling Custom IOC Feeds
Enabling or Disabling the Local IOC Feed on a Specific
Appliance Using the CLI
The local feed is enabled or disabled for a specific managed appliance only by enabling or
disabling the third-party feed for the specific appliance.
A Central Management appliance cannot distribute indicators of compromise (IOCs)
to managed SmartVision Edition sensors.
To enable the local feed for a specific managed Network Security appliance:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Enable local signature generation settings. The local feed does not work if this is not
enabled. By default, local signature generation is already enabled.
cm-hostname (config) # localsig enable
4. Enable IOCs from a third-party feed for a managed Network Security appliance.
cm-hostname (config) # custom content enable on lms <applianceID>
where <applianceID> is the Network Security appliance record name. This thirdparty feed identifies the managed appliance for the local feed. The local feed does
not work if this third-party feed is not enabled.
5. Enable IOCs from the local feed.
cm-hostname (config) # localsig localfeed enable
6. Verify the status of IOC customizations.
cm-hostname (config) # show custom content enable status
CMS status
CM-1 : enabled
LMS status
B9-vNX2500-1 : enabled
7. Verify the status of the local IOC feed.
CMS1 > show localsig
LocalSig Generator
Enabled : YES
Running : running
Rule Versions : 1
Active rules : 1337
LocalFeed : Enabled
8. Save your changes.
cm-hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
509
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
To disable the local feed for a specific managed Network Security appliance:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
3. Disable IOCs from a third-party feed for a specific managed Network Security
appliance. When you disable IOCs from a third-party feed for a managed appliance,
the IOCs from the local feed for the appliance are also disabled.
cm-hostname (config) # no custom content enable on lms <applianceID>
where applianceID is the Network Security appliance record name.
4. Save your changes.
cm-hostname (config) # write memory
5. Log in to the CLI on the managed Network Security appliance.
6. Enable CLI configuration mode.
nx-hostname > enable
nx-hostname # configure terminal
7. Verify the status of third-party IOC feeds.
nx-hostname (config) # show custom content enable status
Custom content : disabled
Creating a Custom Blacklist from ThirdParty Feeds
You can upload up to 30 unique feeds to the Central Management appliance from a flat
file or an XML-based file in STIX 1.2 format. Configure a combined maximum of 25,000
custom blacklist entries on all of the feeds by specifying each blacklist entry on a separate
line. A unique name is required for each feed. The feed name that you specify appears as
the malware name in the Alerts > Alerts > Alerts page on the managed Network Security
appliance. For details about how to view the details of a custom feed, see Viewing Custom
Feed Details on page 514.
Trellix recommends that you make sure that there are no invalid or duplicate blacklist
entries so that you do not reach the allotted limit.
Follow these guidelines when you create a blacklist:
l
510
Trellix recommends that you specify only public IP addresses in the custom
blacklist.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
l
Creating a Custom Blacklist from Third-Party Feeds
Trellix recommends that you create the list of URLs in an ASCII text file. The
maximum number of characters is 2500 for all URLs.
Import STIX 1.2 files. The domain entries in STIX 1.0.1 are not supported.
Trellix recommends that you upload third-party feeds that contain only a .txt file
extension because incorrect file extensions can cause problems when creating a feed.
Specify URL entries in the custom blacklist at the subdirectory level (for example,
http://test.com/testfolder1/1.html). Malicious URLs are not blocked if they are
specified at the directory level (for example, http://test.com/testfolder1/).
To include an optional comment string as part of your feed entry, follow these guidelines:
l
Begin the comment with <feed>#
l
No spaces are allowed before the hash sign.
l
ASCII characters only.
l
Maximum characters of 62.
l
Comments are not supported in STIX files.
Use the Upload Feed page to import a custom blacklist specific to the following types of
content:
l
l
l
l
IP addresses—A custom list of remote addresses. You can specify the list of IP
addresses in a flat file. The IP address feed file is used as a flat file and provides the
same functionality as the corresponding XML-based file in STIX format.
Domain Names—A custom list that contains the entries of known suspicious or
malicious domains. You can specify the list of domains in a flat file. The domain
feed file is used as a flat file and provides the same functionality as the
corresponding XML-based file in STIX format.
URLs—A custom list that contains entries of known suspicious or malicious URLs.
You can specify the list of URLs in a flat file. The URL feed file is used as a flat file
and provides the same functionality as the corresponding XML-based file in STIX
format.
Hash Files—A custom list that contains entries of known suspicious or malicious
files that are represented as a list of MD5 or SHA-256 hashes in a flat file. The hash
feed file is used as a flat file and provides the same functionality as the
corresponding XML-based file in STIX format.
IMPORTANT! You cannot import hash files on FireEye NX 10000 models
that are managed by the Central Management appliance.
l
STIX—A shared list of suspected malicious URL indicators, list of IP address
indicators, list of domain indicators, and list of indicators with MD5 and SHA-256
hashes of malicious files. You can upload a standard STIX 1.2 file in place of the
other four feed files.
© 2022 FireEye Security Holdings US LLC
511
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
Uploading a Third-Party Feed
In the following example of the Appliance Settings: Third Party Feeds page, the managed
Network Security appliance does not yet contain third-party feeds.
NOTE: You can upload a third-party feed only using the Web UI.
The local feed is managed (uploaded and deleted) automatically by the Central
Management appliance. You cannot upload it.
Prerequisites
l
Log in to the Web UI of the Central Management appliance as Admin.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
A managed Network Security appliance is deployed in TAP mode or inline mode.
l
l
Enable IOCs from third-party feeds. For details, see Enabling or Disabling Custom
IOC Feeds on page 503.
Create a flat file or an XML-based file in STIX 1.2 format that contains custom
blacklist entries. Verify that the file is accessible from the local desktop from which
you access the Web UI. For details, see Creating a Custom Blacklist from Third-Party
Feeds on page 510.
Uploading a Third-Party Feed Using the Web UI
Follow these steps to upload a third-party feed to the Central Management appliance using
the Web UI.
512
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Uploading a Third-Party Feed
To upload a third-party feed to a Central Management appliance:
1. Log in to the Central Management appliance as an administrator.
2. In the Web UI, choose Settings > Appliance Settings.
3. Select the managed Network Security appliance and then select 3rd Party Feeds.
The page lists the custom feeds that are uploaded.
4. Click Upload New Feed.
5. Enter the name of the feed in the Feed Name field.
6. If you want to override an existing feed with an updated flat file, select the Override
checkbox.
7. Click Choose File to select the flat file or STIX file you want to import.
8. Choose content type from the Type drop-down menu.
l
IP
l
URL
l
Hash MD5
© 2022 FireEye Security Holdings US LLC
513
Central Management System Administration Guide
l
Hash SHA-256
l
Domain
l
STIX
CHAPTER 32: Configuring Custom IOC Feeds
9. Choose the feed action from the Action drop-down menu.
l
Alert
l
Block
10. (Optional) Enter explanatory information about the intelligence feed in the
Comment field.
11. Click Upload to upload the feed.
l
l
The system checks the entries in the custom blacklist file. A progress message
appears:
If there is a problem with the feed that you imported (for example, invalid
entries or the wrong format), the following message appears:
Viewing Custom Feed Details
View details about the status of custom IOC feeds, the total number of custom IOC feeds,
and the total number of all the custom blacklist entries that you configured on managed
Network Security appliances from the Central Management appliance.
View the local feed status using the CLI.
Track the number of blacklist entries that were configured for each third-party feed using
the CLI.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
A managed Network Security appliance is deployed in TAP mode or inline mode.
l
514
Enable IOCs from custom feeds. For details, see Enabling or Disabling Custom
IOC Feeds on page 503.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
Viewing Custom Feed Details
Create a flat file or an XML-based file in STIX 1.2 format that contains custom
blacklist entries. Verify that the file is accessible from the local desktop from which
you access the Web UI. For details, see Creating a Custom Blacklist from Third-Party
Feeds on page 510.
Upload one or more third-party feeds to a managed Network Security appliance
from a flat file or an XML-based file in STIX 1.2 format. For details about how to
upload a feed, see Uploading a Third-Party Feed on page 512.
Viewing Custom Feed Details Using the Web UI
In the following example of the Appliance Settings: Third Party Feeds page, the managed
Network Security appliance contains five custom feeds.
To view custom feed details:
1. In the Web UI, choose Settings > Appliance Settings.
2. Select the managed Network Security appliance and then select 3rd Party Feeds.
The page lists the custom feeds that are uploaded.
3. In the table, view the details of each type of custom blacklist entry that was
configured for a custom feed.
Viewing Custom Feed Details Using the CLI
Follow these steps to view custom feed details and to track the number of blacklist entries
that were configured for each third-party feed using the CLI. You can view the status of the
local feed in the CLI, but not local feed details.
To view the custom feed details in the CLI:
1. Log in to the Central Management CLI.
2. Enable CLI configuration mode.
cm-hostname > enable
cm-hostname # configure terminal
© 2022 FireEye Security Holdings US LLC
515
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
3. View the details for each type of blacklist entry that was configured for a third-party
feed.
cm-hostname (config) # show custom content feed status
Total no. of feeds: 5
Total count of all entries in feeds : 22
custom_feed_1
source: custom feed test
action: alert
type : url
url count : 6
update_date : 2017/07/06 22:38:26
custom_feed_2
source: IP feed
action: alert
type : ip
ip count : 4
update_date : 2017/07/06 22:24:25
custom_feed_3
source: URL flat file
action: alert
type : url
url count : 6
update_date : 2017/07/06 22:26:15
custom_feed_4
source: STIX domain watchlist
action: block
type : stix
domain count : 3
update_date : 2017/07/06 22:32:45
custom_feed_5
source: STIX URL watchlist
action: alert
type : stix
url count : 3
update_date : 2017/07/06 22:34:03
4. View the status of the local feed.
cm-hostname (config) # show localsig
LocalSig Generator
Enabled : YES
Running : running
Rule Versions : Active rules : 0
LocalFeed : Enabled
Viewing Custom Feed Details Grouped by Alert Using the
Web UI
The Alerts > Alerts > Alerts page lists the details of the event results table, grouped by
alert, of the malware events that matched the name of the custom blacklist feed that you
imported on a managed Network Security appliance from the Central Management
appliance. You can drill down to identify matched traffic that was either blocked or not
blocked for the following types of malware:
516
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
Deleting Third-Party IOC Feeds Using the Web UI
Domain Match—Domain that matches the name of the feed that contains the entries
of known suspicious or malicious domains that you imported.
Infection Match—Pattern that matches the name of the feed that contains entries of
known suspicious or malicious URLs or IP addresses that you imported.
Malware Object—Hash that matches the name of the feed that contains entries of
MD5 or SHA-256 file types that you imported.
To view the custom feed details grouped by alert on a managed Network Security
appliance:
1. Log in to the managed Network Security Web UI.
2. Choose Alerts > Alerts > Alerts.
3. To expand an entry, click the alert type in the Alert Type column.
Local feed data is automatically removed when the corresponding locally
generated rules (localsig rules) expire. You cannot delete local feed data.
Deleting Third-Party IOC Feeds Using
the Web UI
Follow these steps to delete third-party feeds from the Central Management appliance
using the Web UI.
NOTE: You can delete a third-party feed only using the Web UI.
The local feed is managed (uploaded and deleted) automatically by the Central
Management appliance. Local feed data is automatically removed when the
corresponding locally generated rules (localsig rules) expire. You cannot delete local
feed data.
© 2022 FireEye Security Holdings US LLC
517
Central Management System Administration Guide
CHAPTER 32: Configuring Custom IOC Feeds
IMPORTANT: When a file hash feed is added on the Central Management
appliance and you do not want to impact appliance performance, choose one of the
following options to stop calculating the MD5 or SHA-256 hashes that are detected
in network traffic:
l
l
Log in locally to each managed Network Security appliance to disable the file
inspection feature. Use the no bottracker fi-md5 enable command to
disable calculating MD5 hashes. Use the no bottracker fi-sha256 enable
command to disable calculating SHA-256 hashes.
Delete all the hash MD5 or SHA-256 feed files on the Central Management
appliance Web UI. However, all the hash MD5 or SHA-256 feed files will be
deleted from all the managed Network Security appliances that are connected
to this Central Management appliance.
For details about how to enable or disable the option to inspect and calculate MD5
or SHA-256 hash files, refer to the Network Security User Guide.
Prerequisites
l
l
Log in to the Web UI of the Central Management appliance as Admin.
Upload one or more feeds to a managed Network Security appliance from a flat file
or an XML-based file in STIX 1.2 format. For details about how to upload a feed, see
Uploading a Third-Party Feed on page 512.
To delete a third-party IOC feed:
1. In the Web UI, choose Settings > Appliance Settings.
2. Select the managed Network Security appliance and then select 3rd Party Feeds.
The page lists the custom feeds that are uploaded.
3. In the table, select the check box next to the third-party feed you want to delete. You
can select multiple feeds at one time.
4. Click Delete Feed. A dialog box prompts you to confirm your changes.
5. Click Yes.
The feed is removed from the table. The following message appears:
6. Close the message.
518
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Downloading a Third-Party Feed Using the Web UI
Downloading a Third-Party Feed Using
the Web UI
Follow these steps to download a third-party IOC feed from the Central Management
appliance using the Web UI.
NOTE: You can download a custom IOC feed only using the Web UI.
You cannot download the local feed.
Prerequisites
l
l
Log in to the Web UI of the Central Management appliance as Admin.
Upload one or more third-party feeds to a managed Network Security appliance
from a flat file or an XML-based file in STIX 1.2 format. For details about how to
upload a feed, see Uploading a Third-Party Feed on page 512.
To download a third-party IOC feed:
1. In the Web UI, choose Settings > Appliance Settings.
2. Select the managed Network Security appliance and then select 3rd Party Feeds.
The page lists the custom feeds that are uploaded.
3. In the table, locate the third-party feed you want to download to your local desktop.
4. In the Download column, click the download icon.
© 2022 FireEye Security Holdings US LLC
519
Central Management System Administration Guide
520
CHAPTER 32: Configuring Custom IOC Feeds
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Overview of Filtering Alerts Using Tags and Rules
CHAPTER 33: Filtering Alerts
Using Tags and Rules
This chapter covers the following information:
l
Overview of Filtering Alerts Using Tags and Rules below
l
Configuring Tags and Values on the next page
l
Configuring Rules to Manage Alert Tags on page 530
l
l
l
Viewing Tags for an Alert for Managed Email Security — Server Edition Appliances
Using the Web UI on page 545
Viewing Tags for an Alert for Managed Network Security Appliances Using the Web
UI on page 546
Adding Tags to Alerts Manually for Managed Appliances Using the Web UI on
page 546
Overview of Filtering Alerts Using Tags
and Rules
NOTE: Alerts can be filtered using tags and rules only on managed Email Security
— Server Edition and Network Security appliances.
The Central Management appliance allows you to define tags and rules so that they can be
used to filter alerts on managed appliances. You can define a number of tags to filter out
alerts that you want to retain on managed appliances. A tag can be used to filter related
alerts that contain the same tag name or value. For example, alerts can be tagged to
identify traffic that contains the specified virtual local area network (VLAN) or subnet on
managed appliances. Tags are automatically added to the database on the Central
Management appliance. A rule can be used to manage alert tags on managed appliances.
A rule can be configured based on different alert attributes (for example, source IP address,
© 2022 FireEye Security Holdings US LLC
521
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
target IP address, or severity type). Each rule can be associated with a relevant action and
applied to all incoming alerts that contain the matched alert attributes.
Task List for Filtering Alerts Using Tags and Rules
Complete the steps for filtering alerts using tags and rules in the following order:
1. Log in to the Central Management Web UI.
2. Add tags and values to the tag configuration table. See Adding Tags Using the Web
UI on the facing page and Adding Values to a Tag Using the Web UI on page 526.
3. Configure rules to manage alert tags on managed appliances. See Configuring Rules
to Manage Alert Tags on page 530.
4. View tags that are associated with an alert in the managed appliance Web UI. See
Viewing Tags for an Alert for Managed Email Security — Server Edition Appliances
Using the Web UI on page 545 and Viewing Tags for an Alert for Managed Network
Security Appliances Using the Web UI on page 546.
5. If desired, manually add tags to an alert in the Alerts page on a managed Network
Security appliance. See Adding a Tag to an Alert for Managed Appliances Using the
Web UI on page 547.
Configuring Tags and Values
You can configure tags and values that you associate with an alert on managed appliances
by using the Central Management appliance Web UI:
l
Adding Tags Using the Web UI on the facing page
l
Editing Tags Using the Web UI on page 524
l
Deleting Tags Using the Web UI on page 525
l
Adding Values to a Tag Using the Web UI on page 526
l
Editing Values for a Tag Using the Web UI on page 528
l
Deleting Values From a Tag Using the Web UI on page 529
You can configure restricted or unrestricted tags and associate them to filter incoming
alerts on the managed appliances. A restricted tag can be modified, deleted, or changed to
an unrestricted tag by a user that is assigned an Admin role. An unrestricted tag can be
modified or deleted by a user that is assigned an Admin role or Analyst role. The total
number of alerts and values are associated with a tag name. For example, you can define a
tag with the name "Region" and the value "US". All the incoming alerts are filtered by
"Region" as the tag name in the Alerts page on the managed appliances. Tags are
automatically added to the database on the Central Management appliance.
522
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Tags and Values
In the following example, the Central Management appliance does not yet contain tags.
Usage Guidelines
Follow these usage guidelines when you create tags and values to associate with an alert:
l
The name and value of the tag can contain alphanumeric characters only. Tag
names and values are case-sensitive. UTF-8 is also supported.
l
The name of the tag can contain up to 100 characters.
l
Only a user that is assigned an Admin role can restrict a tag from other users.
l
l
Only an Admin user can modify, delete, and change a restricted tag to an
unrestricted tag.
A restricted tag can be added only from the Settings > CM Settings > Alert
Management > Tags page on the Central Management appliance.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin, Analyst, or Monitor access to view restricted and unrestricted tags
Adding Tags Using the Web UI
Follow these steps to add tags to the tag configuration table that are associated with an
alert on managed appliances using the Central Management appliance Web UI.
NOTE: You can add tags to the table only using the Web UI.
To add a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. Click Create Tag. The Create Tag window opens.
© 2022 FireEye Security Holdings US LLC
523
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
3. In the Name field, enter the name of the tag.
4. (Optional) Select the Restricted checkbox to restrict the tag only to users that are
assigned an Admin role.
5. Click Apply.
The following message appears:
Editing Tags Using the Web UI
Follow these steps to edit tags on the tag configuration table that are associated with alerts
on managed appliances using the Central Management appliance Web UI.
NOTE: You can edit tags on the table only using the Web UI.
NOTE: If you change the name of an existing tag, the renamed tag retains all its tag
values and alerts.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin access to edit a restricted tag
l
Admin or Analyst access to edit an unrestricted tag
l
524
You have added one or more tags to a database on managed appliances using the
Central Management Web UI. For details about how to add a tag to an alert, see
Adding Tags Using the Web UI on the previous page.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Tags and Values
To edit a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. In the table, locate the tag you want to edit.
3. Click the action icon (
) in the Actions column.
4. Click Edit. The Edit Tag window opens.
5. In the Name field, edit the name of the tag.
6. (Optional) Select the Restricted checkbox to restrict the tag only to users that are
assigned an Admin role.
7. Click Apply.
The following message appears:
Deleting Tags Using the Web UI
Follow these steps to delete tags and all the associated values from the tag configuration
table using the Central Management appliance Web UI. All the tags and the associated
values are automatically removed from the associated alerts on the managed appliances.
© 2022 FireEye Security Holdings US LLC
525
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
NOTE: You can delete tags and all the associated values from the table only using
the Web UI.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin access to delete a restricted tag
l
Admin or Analyst access to delete an unrestricted tag
l
You have added one or more tags to a database on managed appliances using the
Central Management Web UI. For details about how to add a tag to an alert, see
Adding Tags Using the Web UI on page 523.
To delete a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. In the table, locate the tag you want to delete.
3. Click the action icon (
) in the Actions column.
4. Click Delete. A dialog box prompts you to confirm your changes.
5. Click Yes.
The tag is removed from the table. The following message appears:
Adding Values to a Tag Using the Web UI
Use the Settings > CM Settings > Alert Management > Tags page to add values to a tag
using the Central Management appliance Web UI. Click the plus icon (
526
) to expand the
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Tags and Values
tag entry. The drill-down view displays the values that have already been added to a tag
and the number of alerts associated with a tag. You can add multiple values to an alert
tag. An alert can be matched with any value that you configured.
The default value is an empty string that is associated with a tag.
NOTE: You can add values to a tag only using the Web UI.
Prerequisites
l
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
You have added one or more tags to a database on managed appliances using the
Central Management Web UI. For details about how to add a tag, see Adding Tags
Using the Web UI on page 523.
To add a value to a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. In the table, locate the tag to which you want to add a value.
3. Click the plus icon (
) to expand the tag entry.
4. Click Add Value. The Add Value window opens.
5. In the Value field, enter the value you want to associate with a tag.
6. Click Apply.
The following message appears:
© 2022 FireEye Security Holdings US LLC
527
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
7. Repeat the previous steps to configure additional values.
Editing Values for a Tag Using the Web UI
Follow these steps to edit values that are associated with a tag on the managed appliances
using the Central Management appliance Web UI.
NOTE: You can edit values to a tag only using the Web UI.
Prerequisites
l
Log in to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin access to edit a value for a restricted tag
l
Admin or Analyst access to edit a value for an unrestricted tag
l
l
You have added one or more tags using the Central Management Web UI. For
details about how to add a tag, see Adding Tags Using the Web UI on page 523.
You have added one or more values to a tag. For details about how to add a value
to a tag, see Adding Values to a Tag Using the Web UI on page 526.
To edit the values for a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. In the table, locate the tag whose value you want to edit.
3. Click the plus icon (
) to expand the tag entry.
4. In the table, locate the value you want to edit.
5. Click the action icon (
) in the Actions column.
6. Click Edit. The Edit Value window opens.
528
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Tags and Values
If a value has not yet been assigned, the Current Value line does not appear.
7. In the Value field, modify the value you want to associate with a tag.
8. Click Apply.
The following message appears:
Click Cancel to cancel the entry.
Deleting Values From a Tag Using the Web UI
Follow these steps to delete values from a tag and all associated alerts on the managed
appliances using the Central Management appliance Web UI.
NOTE: You can delete values from a tag only using the Web UI.
Prerequisites
l
Admin access to delete a value from a restricted tag
l
Admin or Analyst access to delete a value from an unrestricted tag
l
l
You have added one or more tags to a database on managed appliances using the
Central Management Web UI. For details about how to add a tag, see Adding Tags
Using the Web UI on page 523.
You have added one or more values to associate with a tag to a managed appliance
using the Central Management Web UI. For details about how to add a value to a
tag, see Adding Values to a Tag Using the Web UI on page 526.
© 2022 FireEye Security Holdings US LLC
529
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
To delete a value from a tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Tags.
2. Click the plus icon (
) to expand the tag entry.
3. In the table, locate the value you want to delete.
4. Click the action icon (
) in the Actions column.
5. Click Delete. A dialog box prompts you to confirm your changes.
6. Click Yes.
The value is removed from the tag entry. The following message appears:
Configuring Rules to Manage Alert Tags
You can configure rules that are used to manage alert tags on managed appliances by
using the Central Management appliance Web UI.
You can configure rules that match criteria and perform certain actions that are associated
with the user-defined tags to filter incoming alerts on the managed appliances. Each rule
can be associated with multiple actions. If the rule condition is matched, a tag will either
be added to an alert to include the matched condition or deleted from an alert to exclude
the matched condition. Each rule is carried out based on the priority order that you
specified in the rules configuration table.
In the following example, the Central Management appliance does not yet contain rules.
This section covers the following information:
l
530
Adding a Rule to Match a Condition for a Particular IP Address Using the Web UI
on the facing page
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
l
l
Configuring Rules to Manage Alert Tags
Adding a Rule to Match a Condition for a Particular VLAN Using the Web UI on
page 533
Adding a Rule to Match a Condition for a Particular Appliance Using the Web UI
on page 535
Adding a Rule to Match a Condition for a Particular Product Type Using the Web
UI on page 536
Adding a Rule to Match a Condition for a Particular Severity Type Using the Web
UI on page 538
Adding a Rule to Match a Condition for a Particular Email Using the Web UI on
page 539
l
Editing a Rule Using the Web UI on page 541
l
Deleting a Rule for an Alert Tag Using the Web UI on page 543
l
Setting or Changing the Priority of Rules Using the Web UI on page 544
Usage Guidelines
Follow these usage guidelines when you configure rules that are used to manage tags on
managed appliances:
l
The name of the rule can contain alphanumeric characters.
l
Only unrestricted tags can be created by using rules.
l
A rule must contain at least one condition and one action.
l
A rule cannot contain multiple values for a single condition.
l
A single rule can contain different criteria entries (but not duplicate entries).
l
A single rule can contain multiple actions.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
Adding a Rule to Match a Condition for a Particular IP
Address Using the Web UI
Follow these steps to add a rule to match a condition for a particular IP address using the
Central Management appliance Web UI.
You can configure a rule to match traffic from a particular target, identified by the victim
IP address. You can also configure a rule to match traffic from a particular source,
© 2022 FireEye Security Holdings US LLC
531
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
identified by an attacker appliance. You can add the relevant tag to this rule for all
incoming alerts that contain the specified source IP address or target IP address.
NOTE: You can add rules to match a condition for a particular IP address only
using the Web UI.
To add a rule to match a condition for a particular IP address:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
3. In the Rule Name field, enter the name of the rule.
4. In the Matching Criteria area:
l
l
l
l
Choose Source IP or Target IP.
Choose in prefix, not in prefix, present, not present, equal to, or not equal to
as the operation to match the particular IP address.
Enter the IP address of the source or target.
Click Add Condition. The source IP address or target IP address condition is
added to the match criteria table.
5. In the Associated Actions area:
l
l
l
532
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action is added to the associated tag table.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
6. Click Apply.
The following message appears:
Adding a Rule to Match a Condition for a Particular VLAN
Using the Web UI
Follow these steps to add a rule to match a condition for a particular VLAN using the
Central Management appliance Web UI.
You can configure a rule to match traffic from a particular VLAN. You can add the
relevant tag to this rule for all incoming alerts that contain the specified VLAN
identification value.
NOTE: You can add or delete rules to match a condition for a particular VLAN only
using the Web UI.
To add a rule to match a condition for a particular VLAN:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
© 2022 FireEye Security Holdings US LLC
533
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
3. In the Rule Name field, enter the name of the rule.
4. In the Matching Criteria area:
l
l
l
l
Choose VLAN.
Choose equal to, not equal to, greater than, less than, less than or equal to,
or greater than or equal to as the operation to match the particular VLAN.
Enter the VLAN ID. Valid characters are alphanumeric characters.
Click Add Condition. The VLAN condition is added to the match criteria
table.
5. In the Associated Actions area:
l
l
l
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action configuration is added to the associated tag
table.
6. Click Apply.
The following message appears:
534
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
Adding a Rule to Match a Condition for a Particular
Appliance Using the Web UI
Follow these steps to add a rule to match a condition for a particular appliance using the
Central Management appliance Web UI.
You can configure a rule to match traffic from a particular appliance that generated the
alerts. You can add the relevant tag to this rule for all incoming alerts that contain the
specified appliance record name.
NOTE: You can add or delete rules to match a condition for a particular appliance
only using the Web UI.
To add a rule to match a condition for a particular appliance:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
3. In the Rule Name field, enter the name of the rule.
© 2022 FireEye Security Holdings US LLC
535
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
4. In the Matching Criteria area:
l
l
l
l
Choose Appliance ID.
Choose equal to or not equal to as the operation to match the particular
appliance ID.
Enter the appliance ID. Choose Appliances > Sensors to obtain the appliance
ID of the managed Network Security appliance or the managed Email
Security — Server Edition appliance. The appliance ID is displayed in the
Sensor ID column.
Click Add Condition. The appliance ID condition is added to the match
criteria table.
5. In the Associated Actions area:
l
l
l
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action configuration is added to the associated tag
table.
6. Click Apply.
The following message appears:
Adding a Rule to Match a Condition for a Particular
Product Type Using the Web UI
Follow these steps to add a rule to match a condition for a particular product type that is
connected to this Central Management appliance using the Central Management appliance
Web UI.
You can configure a rule to match traffic from a particular product type. You can add the
relevant tag to this rule for all incoming alerts that contain the specified product type that
is connected to this Central Management appliance.
NOTE: You can add or delete rules to match a condition for a particular product
type only using the Web UI.
536
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
To add a rule to match a condition for a particular product type:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
3. In the Rule Name field, enter the name of the rule.
4. In the Matching Criteria area:
l
l
l
l
Choose Product Type.
Choose equal to or not equal to as the operation to match the particular
product type.
Choose a product type from the drop-down list.
Click Add Condition. The product type condition is added to the match
criteria table.
5. In the Associated Actions area:
l
l
l
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action configuration is added to the associated tag
table.
© 2022 FireEye Security Holdings US LLC
537
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
6. Click Apply.
The following message appears:
Adding a Rule to Match a Condition for a Particular
Severity Type Using the Web UI
Follow these steps to add a rule to match a condition for a particular severity type using
the Central Management appliance Web UI.
You can configure a rule to match traffic from a particular severity type. You can add the
relevant tag to this rule for all incoming alerts that contain the specified severity type.
NOTE: You can add or delete rules to match a condition for a particular severity
type only using the Web UI.
To add a rule to match a condition for a particular severity type:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
538
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
3. In the Rule Name field, enter the name of the rule.
4. In the Matching Criteria area:
l
l
l
l
Choose Severity.
Choose equal to, not equal to, greater than, less than, less than or equal to,
or greater than or equal to as the operation to match the particular severity
type.
Depending on the operation for the severity criteria, choose critical, major, or
minor as the severity type.
Click Add Condition. The severity condition is added to the match criteria
table.
5. In the Associated Actions area:
l
l
l
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action configuration is added to the associated tag
table.
6. Click Apply.
The following message appears:
Adding a Rule to Match a Condition for a Particular Email
Using the Web UI
Follow these steps to add a rule to match a condition for a particular email address using
the Central Management appliance Web UI.
You can configure a rule to match traffic sent from a particular sender email address or
sent to a recipient email address. You can add the relevant tag to this rule for all incoming
alerts that contain the specified sender email address or recipient email address.
NOTE: You can add or delete rules to match a condition for a particular email only
using the appliance Web UI.
© 2022 FireEye Security Holdings US LLC
539
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
To add a rule to match a condition for a particular email:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. Click Create Rule. The Create Rule window opens.
3. In the Rule Name field, enter the name of the rule.
4. In the Matching Criteria area:
l
l
l
l
Choose Email Sender or Email Recipient.
Choose equal to, not equal to, present, or not present as the operation to
match the particular email.
Enter the email address of the sender or recipient.
Click Add Condition. The sender email or recipient email condition is added
to the match criteria table.
5. In the Associated Actions area:
l
l
540
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
l
Click Add Action. The rule action configuration is added to the associated tag
table.
6. Click Apply.
The following message appears:
Editing a Rule Using the Web UI
Follow these steps to edit a rule that is used to manage an alert tag on a managed
appliance using the Central Management appliance Web UI.
NOTE: You can edit rules for an alert tag only using the Web UI.
Usage Guidelines
Follow these usage guidelines when you edit a rule to manage an alert tag on a managed
appliance:
l
l
l
A rule must contain at least one condition and one action. If you want to delete a
condition or action, you must delete a rule.
A rule can contain one condition and multiple actions. If you want to delete an
action, you must delete the action. If you want to delete a condition, you must delete
a rule.
A rule can contain multiple conditions and one action. If you want to delete a
condition, you must delete the condition. If you want to delete an action, you must
delete a rule.
Prerequisites
l
l
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
You have added one or more tags to a database on a managed appliance. For
details about how to add a tag to an alert, see Adding Tags Using the Web UI on
page 523.
You have added one or more rules to a managed appliance. For details about how
to configure rules to manage a tag, see Configuring Rules to Manage Alert Tags on
page 530.
© 2022 FireEye Security Holdings US LLC
541
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
To edit a rule for an alert tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. In the table, locate the rule you want to edit.
3. Click the action icon (
) in the Actions column.
4. Click Edit. The Edit Rule window opens.
5. In the Rule Name field, edit the name of the rule.
6. In the Matching Criteria area:
542
l
Choose the relevant match criteria and operation from the drop-down list.
l
Enter the relevant value.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Rules to Manage Alert Tags
l
Click Add Condition. The condition is added to the match criteria table.
l
Locate the condition you want to delete in the table.
l
Click the Delete (trash can) icon. The condition that was previously used in
the rule is deleted.
7. In the Associated Actions area:
l
l
l
l
Choose Alert Tag Add to add a tag to an alert that includes the rule that
contains the matched condition. Or choose Alert Tag Delete to delete a tag
from an alert that includes the rule that contains the matched condition.
Enter any value you want to associate with the tag. Select an existing tag or
tag/value pair, or enter a new tag or tag/value pair.
Click Add Action. The rule action configuration is added to the associated tag
table.
Click the Delete (trash can) icon. The tag that was previously used in the rule
is deleted.
8. Click Apply.
The following message appears:
Deleting a Rule for an Alert Tag Using the Web UI
Follow these steps to delete a rule completely for an alert tag on a managed appliance
using the Central Management appliance Web UI.
NOTE: You can delete rules for an alert tag only using the Web UI.
Prerequisites
l
l
l
Log in to the Web UI of the Central Management appliance as Admin or Analyst
You have added one or more tags to a database on a managed appliance. For
details about how to add a tag to an alert, see Adding Tags Using the Web UI on
page 523.
You have added one or more rules to a managed appliance. For details about how
to configure rules to manage a tag, see Configuring Rules to Manage Alert Tags on
page 530.
© 2022 FireEye Security Holdings US LLC
543
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
To delete a rule for an alert tag:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. In the table, locate the rule you want to delete.
3. Click the action icon (
) in the Actions column.
4. Click Delete. A dialog box prompts you to confirm your changes.
5. Click Yes.
The applicable rule is removed from the table. The following message appears:
Setting or Changing the Priority of Rules Using the Web
UI
Follow these steps to set or change the priority order of the rules to filter incoming alerts on
managed appliances using the Central Management appliance Web UI.
NOTE: You can change the priority of the rules only using the Web UI.
Prerequisites
l
l
l
544
Access to the Web UI of the Central Management appliance as Admin or Analyst
You have added one or more tags to a managed appliance. For details about how to
add a tag to an alert, see Adding Tags Using the Web UI on page 523.
You have added one or more rules to a managed appliance. For details about how
to configure rules to manage a tag, see Configuring Rules to Manage Alert Tags on
page 530.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing Tags for an Alert for Managed Email Security — Server Edition Appliances Using the Web UI
To set or change the priority of the rules:
1. In the Web UI, choose Settings > CM Settings > Alert Management > Rules.
2. In the Order column, enter the priority for the rule you want to change. Then press
Enter. Each rule priority can be changed one at a time.
The priority order for this rule is changed and the priority order for all the rules
affected by the change is changed. The following message appears:
Viewing Tags for an Alert for Managed
Email Security — Server Edition
Appliances Using the Web UI
The Email Alerts page on the Central Management appliance lists the tags associated
with an email alert that is tagged based on the matched criteria that you defined in the
tags and rules. If an alert contains a restricted tag, the letter "[R]" is displayed next to the
tag entry.
© 2022 FireEye Security Holdings US LLC
545
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor.
Viewing Tags for an Alert for Managed
Network Security Appliances Using the
Web UI
The Alerts > NX > Alerts page on the Central Management appliance lists the tags
associated with an alert based on the matched criteria that you defined in the tags and
rules. If an alert contains a restricted tag, the letter "[R]" is displayed next to the tag entry.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin, Analyst, or
Monitor
Adding Tags to Alerts Manually for
Managed Appliances Using the Web UI
You can manually add tags to associate with a Network Security alert on the Alerts page
by using the Central Management appliance Web UI. The tags that you add manually
affect only the alert to which they were added.
This section covers the following information:
546
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
l
l
l
Adding Tags to Alerts Manually for Managed Appliances Using the Web UI
Adding a Tag to an Alert for Managed Appliances Using the Web UI below
Editing a Tag for an Alert for Managed Appliances Using the Web UI on the next
page
Deleting a Tag From an Alert for Managed Appliances Using the Web UI on
page 549
NOTE: You cannot manually add, edit, or delete tags for an alert in the Email Alerts
page using the Central Management appliance Web UI.
Adding a Tag to an Alert for Managed Appliances Using
the Web UI
Follow these steps to manually add a tag to a Network Security alert in the Alerts page on
a Central Management appliance using the Web UI.
NOTE: You can manually add tags to a Network Security alert in the Alerts page
only using the Central Management appliance Web UI.
NOTE: You can manually add only unrestricted tags to a Network Security alert in
the Alerts page on the Central Management appliance.
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
To add tags to alerts for a managed Network Security appliance:
1. In the Central Management appliance Web UI, choose Alerts > NX > Alerts.
2. In the table on the NX: Alerts page, locate the alert you want to tag. You can select
one or more tags at the same time.
3. Click the action icon (
) in the Actions column.
4. Click Add Tag. The Add Tag window opens.
© 2022 FireEye Security Holdings US LLC
547
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
5. In the field, enter the tag. You can enter multiple tags at one time.
The list of existing tags is also displayed when you create a new tag. You can select
multiple existing tags.
NOTE: A user that is assigned an Analyst role can view only unrestricted
tags in the list.
6. If you want to save your changes, click Apply. Otherwise, click Cancel.
The following message appears:
Editing a Tag for an Alert for Managed Appliances Using
the Web UI
Follow these steps to manually edit a tag that is associated with a Network Security alert
in the Alerts page on a Central Management appliance using the Web UI.
NOTE: You can manually edit tags in the Alerts page only using the Central
Management appliance Web UI.
NOTE: You can manually edit only unrestricted tags in the Alerts page on the
Central Management appliance.
NOTE: A user that is assigned an Admin Role can edit a restricted tag.
Prerequisites
548
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin access to edit a restricted tag
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Adding Tags to Alerts Manually for Managed Appliances Using the Web UI
To edit tags for an alert for a managed Network Security appliance:
1. In the Central Management appliance Web UI, choose Alerts > NX > Alerts.
2. In the table on the NX: Alerts page, locate the tag you want to edit for an alert.
3. Click the edit icon (blue pencil) next to the tag you want to edit. The Edit Tag
window opens.
4. In the Name field, modify the name of the tag that is associated with an alert.
5. In the Value field, modify the name of the value that is associated with a tag.
6. Click Apply.
The following message appears:
Deleting a Tag From an Alert for Managed Appliances
Using the Web UI
Follow these steps to manually delete a tag from a Network Security alert in the Alerts
page on a Central Management appliance using the Web UI.
NOTE: You can delete tags in the Alerts page only using the Central Management
appliance Web UI.
© 2022 FireEye Security Holdings US LLC
549
Central Management System Administration Guide
CHAPTER 33: Filtering Alerts Using Tags and Rules
Prerequisites
l
Access to the Web UI of the Central Management appliance as Admin or Analyst
l
Admin access to delete a restricted tag
To delete a tag from an alert for a managed Network Security appliance:
1. In the Central Management appliance Web UI, choose Alerts > NX > Alerts.
2. In the table on the NX: Alerts page, locate the tag you want to delete from an alert.
3. Click the delete icon (blue trash can) next to the tag you want to delete. A dialog box
prompts you to confirm your changes.
4. Click Yes.
The tag is removed from the alert on the event results table. The following message
appears:
550
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
PART V: Appendices
l
Configuring Secure Shell (SSH) Authentication on page 553
l
Configuring Network Address Translation (NAT) on page 571
l
Configuring the CM Peer Service on page 589
l
Monitoring Email Alerts from the Email Security - Cloud Edition on page 611
© 2022 FireEye Security Holdings US LLC
551
Central Management System Administration Guide
552
PART V: Appendices
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About SSH Authentication
APPENDIX A: Configuring Secure
Shell (SSH) Authentication
This section covers the following information:
l
About SSH Authentication below
l
User Authentication on the next page
l
Host-Key Authentication on page 561
About SSH Authentication
The Secure Shell (SSH) protocol is used for secure communication between the Central
Management appliance and the appliances it manages. When the Central Management
appliance initiates the connection, it logs in as a remote "admin" user on the managed
appliance. When the managed appliance initiates the connection, it logs in as a remote
"admin" user on the Central Management appliance. SSH user authentication verifies the
identity of the remote user attempting the connection.
SSH host authentication verifies the identity of the Central Management appliance to the
managed appliance and verifies the identity of the managed appliance to the Central
Management appliance.
NOTE: The topics in this section describe how to configure SSH authentication for a
server-initiated connection (where the Central Management administrator adds an
appliance directly from the Central Management Web UI or CLI). For information
about a client-initiated connection (where a managed appliance administrator sends a
request for management to the Central Management appliance, and a Central
Management administrator accepts or rejects the request), see the System Administration
Guide or Administration Guide for the managed appliance.
© 2022 FireEye Security Holdings US LLC
553
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
User Authentication
The remote user can authenticate using either a password or a public key. After the
connection is established, it is controlled by the configured password or the public key.
Password Authentication
With password authentication, a password is configured for the remote user. This is the
initial authentication type for an appliance that is added to the Central Management
appliance using the Web UI.
Public Key Authentication
Public key authentication uses a pair of keys—a public key and a private key. With public
key authentication, an SSH-DSA2 or SSH-RSA2 identity is configured for the remote user
and is pushed to the managed appliance.
Benefits of public key authentication include:
l
l
The private key remains on the CM appliance and cannot be computed from the
public key. This is an advantage over password authentication, where the password
could be cracked.
If you use password authentication, password change policies can break the
connection between the Central Management platform and the managed appliance.
For example, suppose users on a managed Email Security — Server Edition
appliance must change their passwords every 90 days. As a Central Management
administrator, you might be unaware of this policy. After the password for the
remote user changes, the connection to the Email Security — Server Edition
appliance will be broken until you change the password on the Central
Management appliance.
Best Practice: Because password change policies apply only to password
authentication, Trellix recommends using public key authentication for this
connection.
For details, see the following topics:
554
l
Creating a Public Key Using the CLI on the facing page
l
Configuring User Authentication Using the Web UI on page 558
l
Configuring User Authentication Using the CLI on page 559
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
User Authentication
Creating a Public Key Using the CLI
Use the commands in this section to create a new public key for SSH user authentication.
You can use this key instead of the password to authenticate the remote user.
NOTE: If no SSH-DSA2 or SSH-RSA2 public keys exist, you can use the Web UI to
create an "admin" SSH-DSA2 key and an "admin" SSH-RSA2 key. For details, see
Importing a Host Key into the Global Host-Keys Database Using the Web UI on
page 564.
To create a public key:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Create the public key:
hostname (config) # cmc auth <keyType> identity <identityName> generate
where <keyType> can be ssh-dsa2 or ssh-rsa2 and <identityName> is a userfriendly name.
3. Verify your changes:
hostname (config) # show cmc auth identities
4. Save your changes:
hostname (config) # write memory
5. Push the key to the managed appliance as described in Pushing a Public Key Using
the CLI on the next page.
To remove a public key:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Remove the public key:
hostname (config) # no cmc auth <keyType> identity <identityName>
3. Verify your change:
hostname (config) # show cmc auth identities
4. Save your changes:
hostname (config) # write memory
Example
The following example creates an SSH-DSA2 identity named "admin4" on the NX-04
appliance.
© 2022 FireEye Security Holdings US LLC
555
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
NX-04 (config) # cmc auth ssh-dsa2 identity admin4
NX-04 (config) # show cmc auth identities
DSA2 identity admin4:
Public Key:
ssh-dss AAA3NzaC1kc3MAAACBAJl3PisWNnz/gYLvL4JC7xFMoq3HE89rai7trnJmpxjylArYhf
MzaGndFA4qGRZMFzhiz9Jhi/+W1ufIrXLGzakC0lAAAAFQCuMCsMwMGN9zT5w2JCiDt7D6orNwAA
.
.
.
NOTE: This example is from a Network Security appliance, but it is representative
of CM appliances as well.
Pushing a Public Key Using the CLI
Use the commands in this section to push the public key of an SSH-DSA2 or SSH-RSA2
identity to the managed appliance. When a remote Central Management user and this
identity are used to authenticate against the appliance, the connection is established only if
the appliance already has this key.
NOTE: You can also use the Central Management Web UI to push the key. For
details, see Importing a Host Key into the Global Host-Keys Database Using the
Web UI on page 564.
To push a public key:
1. Log in to the Central Management CLI.
2. Go to CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
3. Push the key to the appliance:
cm-hostname (config) # cmc appliance <applianceID> auth <keyType>
identity <identityName> push [username <username> password <password>]
where the username and password options allow the remote user to log in to the
appliance to push the public key before the appliance is connected.
4. Verify your change:
a. Log in to the managed appliance CLI.
b. Go to CLI enable mode:
appl-hostname > enable
c. Verify that the key is present:
appl-hostname # show ssh client
556
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
User Authentication
Examples
Pushing an SSH-DSA2 Public Key
The following example displays the public key string of the Central Management SSHDSA2 identity named "admin4," and then pushes it to the Email Security — Server Edition
appliance. It then displays the SSH authorized keys on the Email Security — Server Edition
appliance to verify that the key was pushed.
CM-08 (config) # cmc auth ssh-dsa2 identity admin4
CM-08 (config) # show cmc auth identities
DSA2 identity admin4:
Public Key:
ssh-dss AAA3NzaC1kc3MAAACBAJl3PisWNnz/gYLvL4JC7xFMoq3HE89rai7trnJmpxjylArYhf
MzaGndFA4qGRZMFzhiz9Jhi/+W1ufIrXLGzakC0lAAAAFQCuMCsMwMGN9zT5w2JCiDt7D6orNwAA
.
.
CM-08 (config) # cmc appliance EX-03 auth ssh-dsa2 identity admin4 push
Push of identity for user admin onto EX-03 succeeded.
EX-03 # show ssh client
.
.
SSH authorized keys:
User admin:
Key 1:
ssh-dss AAA3NzaC1kc3MAAACBAJl3PisWNnz/gYLvL4JC7xFMoq3HE89rai7trnJmpxjylArYhf
MzaGndFA4qGRZMFzhiz9Jhi/+W1ufIrXLGzakC0lAAAAFQCuMCsMwMGN9zT5w2JCiDt7D6orNwAA
.
.
.
Pushing an SSH-RSA2 Public Key and Establishing a Connection
The following example logs the remote user into the Email Security — Server Edition
appliance to push the Central Management SSH-RSA2 identity named "admin6" to the
Email Security — Server Edition appliance. It then establishes the connection between the
Central Management platform and the Email Security — Server Edition appliance.
CM-02 (config) # cmc appliance EX-05 address 172.17.74.54
CM-02 (config) # cmc appliance EX-05 auth ssh-rsa2 identity admin6 push
username admin password admin
CM-02 (config) # cmc appliance EX-05 authtype ssh-rsa2
CM-02 (config) # cmc appliance EX-05 auth ssh-rsa2 identity admin6
CM-02 (config) # show cmc appliances EX-05
Appliance EX-05:
Connection status:
Connected:
yes (server-initiated)
.
.
.
Authentication:
Authentication type:
ssh-rsa2
password username:
admin
password password:
********
ssh-dsa2 username:
admin
ssh-dsa2 identity:
© 2022 FireEye Security Holdings US LLC
557
Central Management System Administration Guide
ssh-rsa2 username:
ssh-rsa2 identity:
APPENDIX A: Configuring Secure Shell (SSH) Authentication
admin
admin6
Configuring User Authentication Using the Web UI
Use the Sensors page to configure authentication parameters for the remote user the
Central Management appliance uses to log in to an appliance to establish the connection.
This is an existing "admin" user on the managed appliance.
When you add an appliance using the Web UI, you must configure a username and
password, so the Central Management appliance initially uses password authentication.
After the appliance is connected, you can select an SSH-DSA2 or SSH-RSA2 key, which
changes the authentication type accordingly.
IMPORTANT! After you configure SSH-DSA2 or SSH-RSA2 authentication, the only
way to return to password authentication using the Web UI is to delete the
appliance and then add it again.
To configure SSH-RSA2 or SSH-DSA2 authentication:
1. In the appliance row, click Select > Use CMS Public Key to Connect. The Password
field is replaced by the CMS Public Key field.
2. Click the Select a key drop-down list.
558
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
User Authentication
3. To configure SSH-RSA2 authentication, do one of the following:
l
l
Select an existing key.
Select No RSA keys. Create one, and then select the rsa-admin key that is
created.
4. To configure SSH-DSA2 authentication, do one of the following:
l
l
Select an existing key.
Select No DSA keys. Create One, and then select the dsa-admin key that is
created.
5. Click Update.
NOTE: The connection will be interrupted briefly. Error messages and
indicators will be displayed, but they will clear as soon as the connection is
reestablished.
6. Verify that the key is displayed in the Public Key Used column for the appliance.
Configuring User Authentication Using the CLI
Use the commands in this section to configure authentication parameters for the remote
user the Central Management appliance uses to log in to a managed appliance to establish
the connection. This is an existing "admin" user on the managed appliance.
NOTE: See the ssh and cmc commands in the CLI Command Reference for
advanced authentication options.
To configure password authentication:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the "password" authentication type:
hostname (config) # cmc appliance <identityID> authtype password
3. Specify the remote user to log in to the managed appliance:
hostname (config) # cmc appliance <applianceID> auth password username
<username>
4. Specify the password used to authenticate the remote user:
hostname (config) # cmc appliance <applianceID> auth password password
<password>
5. Save your changes:
hostname (config) # write memory
© 2022 FireEye Security Holdings US LLC
559
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
To configure SSH-DSA2 authentication:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the SSH-DSA2 authentication type:
hostname (config) # cmc appliance <applicationID> authtype ssh-dsa2
3. Specify the remote user to log in to the managed appliance:
hostname (config) # cmc appliance <applianceID> auth ssh-dsa2 username
<username>
4. Specify the named identity used to authenticate the remote user:
hostname (config) # cmc appliance <applianceID> auth ssh-dsa2 identity
<identityName>
where <identityName> is the name of an existing identity.
5. Save your changes:
hostname (config) # write memory
To configure SSH-RSA2 authentication:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. Specify the SSH-RSA2 authentication type:
hostname (config) # cmc appliance <applianceID> authtype ssh-rsa2
3. Specify the remote user to log in to the managed appliance:
hostname (config) # cmc appliance <applianceID> auth ssh-rsa2 username
<username>
4. Specify the named identity used to authenticate the remote user:
hostname (config) # cmc appliance <applianceID> auth ssh-rsa2 identity
<identityName>
where <identityName> is the name of an existing identity.
5. Save your changes:
hostname (config) # write memory
Example
The following example configures SSH-RSA2 authentication parameters used to log in to
the NX-04 appliance.
hostname (config) # cmc appliance NX-04 auth authtype ssh-rsa2
hostname (config) # cmc appliance NX-04 auth ssh-rsa2 username cmcadmin2
hostname (config) # cmc appliance NX-04 auth ssh-rsa2 identity admin2
560
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Host-Key Authentication
Host-Key Authentication
Host-key authentication can be used to prevent man-in-the-middle attacks, in which
another server poses as the managed appliance or the Central Management appliance and
intercepts the traffic between them. When the Central Management appliance and the
managed appliance connect the first time using a server-initiated connection, a key
exchange takes place. The managed appliance sends a copy of its host key to the Central
Management appliance, where it is compared to the keys in the Central Management hostkeys database.
If strict host-key checking is enabled, the connection can be established only if the key that
is sent matches an entry in the local host-keys database for the Central Management
remote user. If global host-key checking is enabled, the connection can be established only
if the key that is sent matches an entry in the Central Management global host-keys
database.
You can enforce strict host-key checking, global host-key checking, or both.
IMPORTANT: Host keys are stored in the configuration database, so they are
included in the backup file.
NOTE: In compliance mode, both strict and global host-key checking is enforced.
For details, see the FIPS 140-2 and Common Criteria Addendum.
NOTE: The same scenario pertains to the primary and secondary Central
Management platforms in a Central Management High-Availability (HA)
deployment. In this case, the two Central Management platforms exchange keys,
and the connection is established if the keys match. For details, see the Central
Management High Availability Guide.
For details, see the following topics:
l
Obtaining a Host Key Using the Web UI on the next page
l
Obtaining a Host Key Using the CLI on page 563
l
l
l
Importing a Host Key into the Global Host-Keys Database Using the Web UI on
page 564
Importing a Host Key into the Global Host-Keys Database Using the CLI on
page 566
Enabling Strict and Global Host-Key Checking Using the CLI on page 568
Prerequisites
l
Admin access to configure authentication and create keys.
l
Monitor, Operator, or Admin access to obtain managed appliance host keys.
© 2022 FireEye Security Holdings US LLC
561
Central Management System Administration Guide
l
APPENDIX A: Configuring Secure Shell (SSH) Authentication
The private key remains on the Central Management appliance and cannot be
computed from the public key.
Obtaining a Host Key Using the Web UI
Use the Certificate Management page to obtain the host key of the managed appliance.
This is the key that you will import into the global host-keys database of the Central
Management appliance.
NOTE: This procedure applies to managed appliances running Release 7.6.0 or
later. If the appliance is running an earlier release, see Obtaining a Host Key Using
the CLI on the facing page.
NOTE: You must use the CLI to obtain the host key of a managed Virtual Execution
appliance.
IMPORTANT! The host-key string may need to be modified in a Network Address
Translation (NAT) deployment. For details, see Configuring Global Host-Key
Authentication in a NAT Deployment on page 586.
To obtain a host key:
1. Log in to the managed appliance Web UI.
2. Click the Settings tab.
3. Click Certificates/Keys on the sidebar.
4. Copy the string starting with the IP address.
5. Do one of the following:
l
l
l
562
Paste the key into the Central Management CLI, as described in Importing a
Host Key into the Global Host-Keys Database Using the CLI on page 566.
Paste the key into the Central Management Web UI, as described in Importing
a Host Key into the Global Host-Keys Database Using the Web UI on
page 564.
Paste the key into a text file and save it for later.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Host-Key Authentication
Obtaining a Host Key Using the CLI
Use the command in this section to obtain the host key of the managed appliance. This is
the key that you will import into the global host-keys database of the Central Management
appliance.
IMPORTANT! You must obtain the RSA v2 key.
IMPORTANT! The host-key string may need to be modified in Network Address
Translation (NAT) deployments. For details, see Configuring Global Host-Key
Authentication in a NAT Deployment on page 586.
To obtain the host key:
1. Log in to the managed appliance CLI.
2. View the keys:
l
If the appliance is running Release 7.6.0 or later:
hostname > show ssh server host-keys interface ether1
l
If the appliance is running an earlier release:
hostname > show ssh server host-keys
3. Locate the RSA v2 host key entry.
4. Do one of the following, depending on whether you will add the key using the
Central Management Web UI or CLI:
l
l
Web UI: Copy the key string, starting with the IP address and ending with
the last character. Omit the double quotation marks at the beginning and end
of the host key entry.
CLI: Copy the key string as described above, but include the double
quotation marks.
5. Do one of the following:
l
l
l
Paste the key into the Central Management Web UI, as described in Importing
a Host Key into the Global Host-Keys Database Using the Web UI on the next
page.
Paste the key into the Central Management CLI, as described in Importing a
Host Key into the Global Host-Keys Database Using the CLI on page 566.
Paste the key into a text file and save it for later.
Example
This example displays the host keys for a managed appliance. The RSA v2 key is
highlighted for illustration.
Acme-05 > show ssh server host-keys interface ether1
© 2022 FireEye Security Holdings US LLC
563
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
SSH server configuration:
SSH server enabled:
yes
.
.
.
Interface listen enabled: yes
Listen Interfaces:
Interface: ether1
Host Key Finger Prints and Key Lengths:
RSA v1 host key: 33:20:5f:af:65:33:e8:62:26:3c:25:d0:1f:2d:8a:54 (2048)
RSA v2 host key: 54:fa:10:2a:f4:c2:cf:3a:46:b1:a4:ed:72:78:b8:22 (2048)
DSA v2 host key: 99:59:a8:a1:d8:3e:df:2e:74:fc:6a:be:be:d2:62:32 (1024)
Host Keys:
RSA v1 host key: "172.17.74.40 2048 65537 2767892723557105143394492343612763
94200729942394341979526174787907308831935615818924165744283828800766510523178479
02037474895252247975570054315595358600142845914848782710493540937857691486699538
04205200729560274476403668156602030333253822356382587237819555941646603447324517
63747513796533041848893042157553987170029619742182277730552872281173097286794724
22744200184844597327452806661880313000836518022137675657765205670872217927843062
15703217249958957713631587970078908302914798758861955796169110420493384623007632
35665546051494669314340340626018765311569680255688151929860734984461083957535425
72032093143856912019598"
RSA v2 host key : "172.17.74.40 ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCzd5JwK
BjHLe/jxkF0JzWcXOTw9l0bz2SctkQrihkqg/zXqrmxAfgbzYulDSIxOKZTh2VBnKsy0qRWrCps64Itl
h6iRlr7Jxa+jAtTAGsygD0GsSKy13wfsJDhMfWk/nrEqicQ4BJN4M/8AzP+0ATQ2QeZ3nGRRzAiyqkn4
K8cRLJ1E80SnLrwElvw805LZWqNLSQwz6tF+8L1vrmr1kzutl082NBV548AU0wptE6Z2f2oxUobcax+e
qS6QMp5nnbPTDLJTbHChsVVrchTCwfGdNnjkawdDC6IhLk0BdncChpTS9E+ZF/F67YwpuIpgraWcoXuZ
xZDTwHDYPZfNtk5"
DSA v2 host key: "172.17.74.40 ssh-dss AAAAB3NzaC1kc3MAAACBAMY7tSZt46Qrv/hqL
1tazYjXNzkyLTWp54DjfkxzE//+qjE0AUr9hTU3ZmHYChzUVTEKj7syaxd+4Y+8IZ94eRVcnrH/jrqtE
aJ64SvoUqGkbKKezUbCVfSrzGgTV/A0dUzLYMLbOEMrTMcXki+DnaUSd80PCWLvq0Mcg0IpXAAAAFQDI
tRIv/iH3AAy23h3cnWzp3dpOXQAAAIAS0AONTi0O8A+f1HNOm3PzS02ZQ9ittHxA1ISs7yE6dcbj9JrW
Vf1w2lJTEZAJPQz/c9NysGVJusll6Aj1aqQ6EKuhKlPcpY0PyCVKT3TGgY93i648umYZSs9+HzoLY1/a
TnnkBGDQ8mFbjhyw3UdeiFjamVVr+4o8QwMbDXAfXAAAAIEAjBMXsp4gK5yvsAgBqcZeZm3vW4zYUpZZ
374A3ANXENWTh2yyQd8Ig1gB0YKDBhSHD6sZpPg88WSDxK3IAdifYGx+FAhowiuWcI+kA0UeiAb9/C+A
653zii1Nc85/fsIwl3GIjmp/xO23b+9YmHY8V5CsT+mmSIYQutCIzUVWbcYvEc="
Importing a Host Key into the Global Host-Keys Database
Using the Web UI
Use the Add Sensor Host Key dialog box to import the host keys of managed appliances
into the Central Management global host-key database. You can import keys from
managed appliances and appliances that are not currently being managed by the Central
Management appliance.
IMPORTANT: The key you import must start with the appliance IP address and it
must not be enclosed in double quotation marks. If the key starts with the hostname,
replace the hostname with the IP address.
564
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Host-Key Authentication
Alternatively, you can import the key for a specific appliance as part of the connection
settings. You can edit the settings of an existing managed appliance in the Edit Sensor
dialog box, or import the key while you are configuring the initial connection with an
appliance in the Add New Sensor dialog box. (See Adding an Appliance Using the Central
Management Web UI on page 354 and Modifying Managed Appliance Information Using
the Web UI on page 371 for instructions.)
CAUTION! If compliance mode is not enabled, global host-key authentication is
optional. If you choose to use global host-key authentication, you must explicitly
enable it in addition to importing the global host key. For details, see Enabling Strict
and Global Host-Key Checking Using the CLI on page 568.
IMPORTANT: Before you perform this procedure, you must obtain the host key
from the managed appliance. For appliances running Release 7.6.0 or later, you can
obtain this key from the appliance Web UI or CLI. For appliances running an earlier
release, you must obtain this key from the CLI. For details, see Obtaining a Host Key
Using the Web UI on page 562 or Obtaining a Host Key Using the CLI on page 563.
To import a host key:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Actions > Sensor Host Keys. The Add Sensor Host Key dialog box opens.
3. Paste the key into the Host Key field.
4. Click Add Key.
To remove a host key:
1. Click the Appliances tab. The Sensors tab should be selected.
2. Click Actions > Sensor Host Keys.
© 2022 FireEye Security Holdings US LLC
565
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
3. Locate the key in the Sensor Host Key section of the Add Sensor Host Key dialog
box.
4. Click Remove.
5. Click OK to confirm the action.
CAUTION! If you remove a host key that is in use, the connection between the
Central Management appliance and the managed appliance is broken.
Importing a Host Key into the Global Host-Keys Database
Using the CLI
Use the commands in this section to import the host key from an appliance into the
Central Management global host-keys database. This procedure is required for global hostkey authentication, in which the connection will be allowed only if the host key the
appliance sends is already in this database.
CAUTION! If you choose to use global host-key authentication, you must explicitly
enable the feature in addition to importing the host key. For details, see Enabling
Strict and Global Host-Key Checking Using the CLI on page 568.
IMPORTANT! Before you perform this procedure, you must obtain the host key
from the managed appliance. You can obtain this key from the appliance Web UI or
CLI. For details, see Obtaining a Host Key Using the Web UI on page 562 or
Obtaining a Host Key Using the CLI on page 563.
IMPORTANT! The host-key string may need to be modified in a Network Address
Translation (NAT) deployment. For details, see Configuring Global Host-Key
Authentication in a NAT Deployment on page 586.
NOTE: See the ssh commands in the CLI Command Reference for advanced
authentication options.
To import a host key:
1. Log in to the Central Management CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
566
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Host-Key Authentication
3. Import the key into the global host-keys database:
hostname (config) # ssh client global known-host "<keyString>"
IMPORTANT! The key must start with the managed appliance IP address,
and it must be enclosed in double quotation marks. If the key starts with
the hostname, replace the hostname with the IP address.
4. Verify your change:
hostname (config) # show ssh client
5. Save your changes:
hostname (config) # write memory
To remove a host key:
1. Log in to the Central Management CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Remove the key:
hostname (config) # no ssh client global known-host "<keyString>"
4. Verify your change:
hostname (config) # show ssh client
5. Save your changes:
hostname (config) # write memory
CAUTION! If you delete a host key that is in use, the connection between the
Central Management appliance and the managed appliance is broken.
Example
This example imports the host key from a managed appliance into the Central
Management platform global host-key database.
hostname (config) # ssh client global known-host "172.17.74.54 ssh-rsa AAAAB3
NAfgbzYulDSIxOKZTh2VBnKsy0qRWrCps64Itlh6iRlr7JxazaC1yc2EAAAADAQABAAABAQCzd5Jw
Ktk5BjHLe/jxkF0JzWcXOTw9l0bz2SctkQrihkqg/zXqrmxtE6Z2f2oxUobcax+eqS6QMp5nnbPTD
LJTbHCNnjkawdDC6IhLk0BdncChpTS9E+ZF/F67YwpuIpgraWrchTCwfG+jAtTAGsygD0VVrchTCc
ncChpTS9E+ZF/F67YwpuIpgraWcoXuZxZKy13wfsJDhMfWk/nrEqicQ4BJN4M/8AzP+fd9sda3li"
hostname (config) # show ssh client
SSH client Strict Hostkey Checking: ask
Minimum protocol version: 2
Cipher list: compatible
Minimum key length: 1024 bits
SSH Global Known Hosts:
Entry 1:
Host:
© 2022 FireEye Security Holdings US LLC
172.17.74.54
567
Central Management System Administration Guide
APPENDIX A: Configuring Secure Shell (SSH) Authentication
Finger Print:
54:fa:10:2a:f4:c2:cf:3a:46:b1:a4:ed:72:78:b8:22
Key Length (bits): 2048
...
Enabling Strict and Global Host-Key Checking Using the
CLI
Use the commands in this section to enable strict host-key checking, global host-key
checking, or both.
l
l
With strict host-key checking, the connection will be allowed only if the local hostkeys database for the Central Management remote user already has an entry that
matches the key the managed appliance sends.
With global host-key checking, the connection will be allowed only if the Central
Management global host-keys database already has an entry that matches the key
the managed appliance sends.
CAUTION! When you enable global host-key authentication, any established
connections will be broken until you explicitly add the host key to the global hostkeys database. See Importing a Host Key into the Global Host-Keys Database Using
the Web UI on page 564 or Importing a Host Key into the Global Host-Keys
Database Using the CLI on page 566 for instructions.
NOTE: See the ssh and cmc commands in the CLI Command Reference for
advanced authentication options.
To enable strict host-key checking:
1. Log in to the CM CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Enable strict host-key checking:
hostname (config) # cmc auth ssh host-key strict
4. Verify your changes:
hostname (config) # show cmc auth ssh
5. Save your changes:
hostname (config) # write memory
568
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Host-Key Authentication
To enable global host-key checking:
1. Log in to the CM CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Enable global host-key checking:
hostname (config) # cmc auth ssh host-key global-only
4. Verify your changes:
hostname (config) # show cmc auth ssh
5. Save your changes:
hostname (config) # write memory
To disable strict or global host-key authentication:
1. Log in to the CM CLI.
2. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
3. Perform the following steps as needed.
l
To disable strict host-key checking:
hostname (config) # no cmc auth ssh host-key strict
l
To disable global host-key checking:
hostname (config) # no cmc auth ssh host-key global
4. Verify your changes:
hostname (config) # show cmc auth ssh
5. Save your changes:
hostname (config) # write memory
Example
This example enforces both strict and global host-key checking on a Central Management
appliance.
hostname (config) # cmc auth ssh host-key strict
hostname (config) # cmc auth ssh host-key global-only
hostname (config) # show cmc auth ssh
CMC SSH configuration:
Strict host key checking enabled:
Global only known hosts enabled:
Minimum protocol version:
Cipher list:
Minimum key length:
© 2022 FireEye Security Holdings US LLC
yes
yes
2
compatible
1024 bits
569
Central Management System Administration Guide
570
APPENDIX A: Configuring Secure Shell (SSH) Authentication
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About NAT Address Mapping
APPENDIX B: Configuring
Network Address Translation
(NAT)
The following sections describe how to add an appliance to the Central Management
platform for management in a deployment in which the Central Management platform, the
appliance, or both are behind a NAT gateway.
l
l
About NAT Address Mapping below
Mappings Used When the Central Management Appliance Initiates the Connection
on the next page
l
Mappings Used When the Managed Appliance Initiates the Connection on page 576
l
Configuring Global Host-Key Authentication in a NAT Deployment on page 586
l
l
Adding an Appliance in a NAT Deployment (Using the Central Management
Appliance) on page 580
Accepting a Management Request in a NAT Deployment on page 582
IMPORTANT! Network address translation (NAT) is not supported in Central
Management high availability (HA) deployments.
About NAT Address Mapping
To implement NAT deployment in a Central Management network, a network
administrator needs to map source-to-destination IP address and port pairs so a
connection to the managed appliance behind the NAT gateway can be established.
Managed appliances can use either one or two ports for the connection and for the
management and DTI network traffic. By default, one port is used. The steps for switching
between single-port and dual-port communication in a NAT deployment are described in
the System Administration Guide or Administration Guide for the managed appliance.
© 2022 FireEye Security Holdings US LLC
571
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Port Accessibility for Single-Port Communication
For a single-port configuration, the remote management (SSH) port needs to be accessible.
This port is used to initiate the connection, to configure and monitor the appliance, and to
request software updates (such as security content, guest images, and system images) from
the DTI source server. Port 22 is the default.
Port Accessibility for Dual-Port Communication
For a dual-port configuration, the following ports need to be accessible:
l
l
l
Remote management (SSH) port—The management port used to initiate the
connection, and for the Central Management appliance to use to configure and
monitor the appliance. Port 22 is the default.
DTI network service (HTTPS) port—The port used to request software updates (such
as security content, guest images, and system images) from the DTI source server.
Port 443 is the default.
DTI address for the Central Management platform—If the Central Management
appliance is behind a NAT gateway, the network administrator must map an
accessible DTI server IP address and HTTPS port. For details, see the System
Administration Guide or Administration Guide for the managed appliance.
Mappings Used When the Central
Management Appliance Initiates the
Connection
This topic shows the NAT address mapping required for each supported topology in
which the Central Management appliance initiates the process of adding an appliance for
management.
l
Central Management Appliance Is Behind a NAT Gateway on the facing page
l
Managed Appliance Is Behind a NAT Gateway on page 574
l
l
Central Management and Managed Appliance Are Behind Different NAT Gateways
on page 575
Central Management and Managed Appliance Are In an External Network on
page 576
Some topologies use virtual IP addresses. These addresses are mapped on the NAT
gateway to reach a Central Management platform or managed device that is in an internal
network behind the gateway.
572
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Mappings Used When the Central Management Appliance Initiates the Connection
NOTE: Only those addresses that need mapping are shown. If no mapping is
indicated, the default IP addresses and default ports (22, or 22 and 443) will be
used.
Central Management Appliance Is Behind a NAT Gateway
This section describes the mappings required for deployments in which the Central
Management platform is behind the NAT gateway and initiates the connection to configure
and manage the appliance.
NOTE: The following single-port diagrams use the Email Security — Server Edition
appliance as the managed appliance, and the dual-port diagrams use the Network
Security appliance as the managed appliance. However, they are representative of
other managed appliances as well.
Single-Port Communication
No NAT address mapping is required if the Central Management appliance initiates the
connection and the managed appliance is in an external network and configured for
single-port communication.
© 2022 FireEye Security Holdings US LLC
573
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Dual-Port Communication
No NAT address mapping is required if the Central Management appliance initiates the
connection and the managed appliance is in an external network and configured for dualport communication.
However, because the Central Management platform is in an internal network, the
accessible DTI server IP address and HTTPS port must be mapped to the Central
Management internal IP address and port 443 so that the managed appliance can request
software updates.
Managed Appliance Is Behind a NAT Gateway
NAT address mapping is required for deployments in which the Central Management
appliance initiates the connection to configure and manage the managed appliance that is
behind a NAT gateway. The mapping details depend on whether the managed appliance
is configured for single-port or dual-port communication.
Single-Port Communication
If the Central Management appliance initiates the connection to the managed appliance
that is behind a NAT gateway and configured for single-port communication, a virtual
NAT IP address and port must be mapped to the managed appliance internal IP address
and port 22.
The mapping enables the Central Management appliance to initiate the connection and
then configure and monitor the managed appliance. The managed appliance uses the
mapping to request software updates.
574
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Mappings Used When the Central Management Appliance Initiates the Connection
Dual-Port Communication
If the Central Management appliance initiates the connection to the managed appliance
that is behind a NAT gateway and configured for dual-port communication, a virtual
NAT IP address and port must be mapped to the managed appliance internal IP address
and port 22.
The Central Management appliance uses the mapping to initiate the connection and then
configure and manage the managed appliance. Because the Central Management
appliance is in an external network, no mapping is required for the managed appliance to
request software updates.
Central Management and Managed Appliance Are Behind
Different NAT Gateways
NAT address mappings are required for deployments in which the Central Management
appliance initiates the connection to the managed appliance and where the two devices are
behind different NAT gateways. The mapping details depend on whether the managed
appliance is configured for single-port or dual-port communication.
Single-Port Communication
If the Central Management appliance initiates the connection, the managed appliance is
configured for single-port communication, and the two devices are behind different NAT
gateways, the virtual IP address and port of NAT gateway 2 must be mapped to the
internal IP address and port 22 of the managed appliance.
The mapping enables the Central Management appliance to initiate a connection and then
configure and monitor the managed appliance, and for the managed appliance to request
software updates.
© 2022 FireEye Security Holdings US LLC
575
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Dual-Port Communication
If the managed appliance is configured for dual-port communication and if the managed
appliance and the Central Management appliance are behind different NAT gateways, the
following NAT address mappings are required:
l
l
A virtual NAT gateway 2 IP address and port must be mapped to the managed
appliance internal IP address and port 22. The mapping enables the Central
Management appliance to initiate the connection and then configure and monitor
the appliance.
The accessible DTI server IP address and HTTPS port must be mapped to a virtual
NAT gateway 1 IP address and port, and the virtual NAT gateway 1 IP address and
port must be mapped to the Central Management internal IP address and port 443.
These mappings enable the managed appliance to request software updates.
Central Management and Managed Appliance Are In an
External Network
No NAT address mapping is required if the Central Management appliance initiates the
connection and the managed appliance is in an external network.
Mappings Used When the Managed
Appliance Initiates the Connection
This section shows the NAT address mapping required for each supported topology in
which the managed appliance initiates the connection with the Central Management
appliance:
l
Central Management Appliance Is Behind a NAT Gateway on the facing page
l
Managed Appliance Is Behind a NAT Gateway on page 578
l
l
576
Central Management and Managed Appliance Are Behind Different NAT Gateways
on page 578
Central Management and Managed Appliance Are in External Networks on
page 580
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Mappings Used When the Managed Appliance Initiates the Connection
Some topologies use virtual IP addresses. These addresses are mapped on the NAT
gateway to reach a Central Management appliance or managed device that is in an
internal network behind the gateway.
NOTE: Only those addresses that need mapping are shown. If no mapping is
indicated, the default IP addresses and default ports (22, or 22 and 443) will be
used.
Central Management Appliance Is Behind a NAT Gateway
NAT address mappings are required for deployments in which the managed appliance
initiates a connection to the Central Management appliance behind a NAT gateway. The
mapping details depend on whether the managed appliance is configured for single-port
or dual-port communication.
Single-Port Communication
If the managed appliance is configured for single-point communication and initiates a
connection with the Central Management appliance behind a NAT gateway, a virtual NAT
IP address and port must be mapped to the internal Central Management IP address and
port 22.
The managed appliance uses the mapping to send a request to be added to the Central
Management appliance for management and also to request software updates.
© 2022 FireEye Security Holdings US LLC
577
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Dual-Port Communication
If the managed appliance is configured for dual-port communication and initiates a
connection with the Central Management appliance behind a NAT gateway, a virtual NAT
IP address and port must be mapped to the internal Central Management IP address and
port 22.
The managed appliance uses the mapping in order to send a request to be added to the
Central Management appliance for management and also to request software updates.
However, because the Central Management appliance is in an internal network, the
accessible DTI server IP address and HTTPS port must be mapped to the Central
Management internal IP address and port 443 so that the managed appliance can request
software updates.
Managed Appliance Is Behind a NAT Gateway
No mapping is required because the Central Management appliance is in an external
network and the managed appliance can access it.
Central Management and Managed Appliance Are Behind
Different NAT Gateways
NAT address mappings are required for deployments in which the managed appliance
initiates a connection to the Central Management appliance and where the two devices are
behind different NAT gateways. The mapping details depend on whether the managed
appliance is configured for single-port or dual-port communication.
578
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Mappings Used When the Managed Appliance Initiates the Connection
Single-Port Communication
If the managed appliance is configured for single-port communication and if the managed
appliance and the Central Management appliance are behind different NAT gateways, the
virtual NAT gateway 1 IP address and port must be mapped to the Central Management
internal IP address and port 22.
The Central Management appliance uses the mapping to configure and monitor the
appliance. The managed appliance uses the mapping to send a request to be added to the
Central Management appliance for management and also to request software updates.
Dual-Port Communication
If the managed appliance is configured for dual-port communication and if the managed
appliance and the Central Management appliance are behind different NAT gateways, the
following NAT address mappings are required:
l
l
The virtual NAT gateway 1 IP address and port must be mapped to the Central
Management internal IP address and port 22. The mapping enables the managed
appliance to send a request to be added to the Central Management appliance for
management and for the Central Management appliance to configure and manage
the appliance.
The managed appliance internal IP address and port 443 must be mapped to a
virtual NAT gateway 2 IP address and port. The virtual NAT gateway 1 IP address
and port must be mapped to the Central Management internal IP address and port
443 for the appliance. The mappings enable the appliance to request software
updates.
© 2022 FireEye Security Holdings US LLC
579
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Central Management and Managed Appliance Are in
External Networks
No NAT address mapping is required if the two devices are in external networks and the
managed appliance initiates the connection.
Adding an Appliance in a NAT
Deployment (Using the Central
Management Appliance)
A Central Management administrator can add an appliance that is behind a NAT gateway
to the Central Management appliance.
NOTE: This procedure must be performed using the Central Management CLI, not
the Web UI.
Prerequisites
l
l
l
l
Operator or Admin access
Network address translation (NAT) mapping as described in About NAT Address
Mapping on page 571.
The virtual NAT IP address and port that map to the appliance internal IP address
and SSH port
Unique hostname for each appliance being added
Adding an Appliance in a NAT Deployment Using the
Central Management CLI
Use the commands in this section to add an appliance that is behind a NAT gateway to
the Central Management appliance.
NOTE: The procedure in this section includes the basic steps for adding an
appliance. Additional options are available. See the CLI Command Reference for a full
list of the cmc commands and details about their parameters and usage.
580
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Adding an Appliance in a NAT Deployment (Using the Central Management Appliance)
To add an appliance:
1. Log in to the Central Management CLI.
2. Go to CLI configuration mode:
cm-hostname > enable
cm-hostname # configure terminal
3. Specify the virtual NAT IP address that is mapped to the appliance internal IP
address:
cm-hostname (config) # cmc appliance <applianceID> address
where applianceID is the appliance record name.
IMPORTANT: Specify the IP address, not the hostname. Otherwise, if the
hostname changes later, the connection will be broken and the appliance will
need to be added again.
4. (Optional) Specify the virtual NAT port that is mapped to the appliance internal
SSH port:
cm-hostname (config) # cmc appliance port <port>
The port defaults to 22 if it is not specified.
5. Configure authentication:
cm-hostname (config) # cmc appliance <applianceID> authtype <authtype>
cm-hostname (config) # cmc appliance <applianceID> auth <authtype>
username <username>
cm-hostname (config) # cmc appliance <applianceID> auth <authtype>
password <password> | identity <identity>
where authtype can be password, ssh-dsa2, or ssh-rsa-2. (See Configuring User
Authentication Using the CLI on page 559 for details.)
6. (Optional) Add a comment describing the appliance:
cm-hostname (config) # cmc appliance <applianceID> comment <comment>
7. Save your changes:
cm-hostname (config) # write memory
Example
The following example adds Acme-NX to the Central Management appliance and
configures password authentication.
cm-hostname (config) # cmc appliance Acme-NX address 10.3.3.6
cm-hostname (config) # cmc appliance Acme-NX port 1000
cm-hostname (config) # cmc appliance Acme-NX authtype password
cm-hostname (config) # cmc appliance Acme-NX password username admin3
cm-hostname (config) # cmc appliance Acme-NX password password 12345abcde
cm-hostname (config) # cmc appliance Acme-NX comment New York NX Series
© 2022 FireEye Security Holdings US LLC
581
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Accepting a Management Request in a
NAT Deployment
A Central Management administrator can view a list of appliances that requested to be
added for management, and accept or reject them. After a request is accepted, the appliance
is added to the Central Management appliance.
Requirements for Establishing a Successful Connection
To accept a management request and successfully establish and maintain the connection,
the following must be in place:
l
l
l
The rendezvous process is enabled on the Central Management appliance (enabled
by default). To verify and enable the process, see Preparing to Accept a Management
Request Using the CLI on page 358.
The appliance has a permanent hostname. If the hostname is changed, the
connection will be broken and cannot be reset. If this happens, the appliance must
be removed from the Central Management appliance and then added again using
the new hostname.
The Central Management appliance and the requesting appliance have the same
rendezvous service name. The rendezvous process has an identifier (known as
service name) that is set to "cmc" by default. The Central Management appliance and
the requesting appliance must have the same service name; if you change the
service name on one, you must change it on the other as well. The cmc rendezvous
service-namehostname command changes the service name; the no cmc rendezvous
service-name command restores the default value. For details, see the CLI Command
Reference.
The auto-connect feature must be enabled on the requesting appliance. To prevent
future connection issues, do not enable the auto-connect feature from the Central
Management appliance on behalf of a managed appliance that was added using
a client-initiated connection. The value of the Auto-connect field in the output of
the show cmc client command on the managed appliance is yes. The value of
the Auto-connect field in the output of the show cmc appliance <appliance
ID> command on the Central Management appliance is no.
Prerequisites
l
582
Operator or Admin access
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Accepting a Management Request in a NAT Deployment
Accepting a Management Request in a NAT Deployment
Using the Central Management Web UI
Use the Connection Requests dialog box to accept or reject a request to be managed.
NOTE: If requests from appliances are waiting for approval., a message is displayed in the
notification bell at the top right of the Central Management Web UI.
To accept a request to be managed from an appliance:
1. If the Central Management appliance has never accepted a request for management,
ensure that it meets the requirements described in Preparing to Accept a
Management Request Using the CLI on page 358.
2. Log in to the Central Management Web UI.
3. Do one of the following to open the Connection Requests dialog box:
l
l
Click the button in the notification bell message.
Click the Appliances tab. The Sensors tab should be selected. Click Actions >
Waiting Connection Requests.
The IP address and hostname of the requesting appliances are displayed.
© 2022 FireEye Security Holdings US LLC
583
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
4. To approve the request and add the appliance:
a. Select its checkbox and then click Accept.
b. When prompted, confirm your action.
The appliance is added to the list on the page, and it becomes a member of the
system group for that appliance type. The appliance hostname becomes the display
name shown in the Sensor column. You can add the appliance to a different group
or create a new group for the appliance as described in Grouping Appliances on
page 399.
5. To reject the request (for example, if you do not recognize the appliance):
a. Select its checkbox and then click Reject.
b. When prompted, confirm your action.
NOTE: See Viewing Managed Appliance Information Using the Web UI on
page 367 for information about the status indicators and the actions you can take
from this page.
Accepting a Management Request in a NAT Deployment
Using the Central Management CLI
Use the commands in this section to accept or reject a request by an appliance to be added
to the Central Management appliance for management.
To accept a request to be managed:
1. If the Central Management appliance has never accepted a request for management,
ensure that it meets the requirements described in Preparing to Accept a
Management Request Using the CLI on page 358.
2. Log in to the Central Management CLI.
3. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
584
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Accepting a Management Request in a NAT Deployment
4. Accept one or more requests.
l
To accept a specific appliance:
cm-hostname (config) # cmc rendezvous server accept client
<hostname>
where <hostname> is the hostname of the requesting appliance. Do not
specify the IP address, because multiple appliances behind the same NAT
gateway have the same IP address.
l
To accept all appliances in the list:
cm-hostname (config) # cmc rendezvous server accept all
5. Save your changes.
hostname (config) # write memory
To reject a request from an appliance to be managed:
1. Go to CLI configuration mode:
hostname > enable
hostname # configure terminal
2. View the list of requests:
cm-hostname (config) # show cmc rendezvous
3. Reject one or more requests:
l
To reject a specific appliance:
cm-hostname (config) # no cmc rendezvous server accept client
<hostname>
where <hostname> is the hostname of the requesting appliance. Do not
specify the IP address, because multiple appliances behind the same NAT
gateway have the same IP address.
l
To reject all appliances in the list:
cm-hostname (config) # no cmc rendezvous server accept all
4. Save your changes.
hostname (config) # write memory
Example
In this example, the request from the nx-02 appliance is accepted and the request from the
nx-04 appliance is rejected.
cm-hostname (config) # show cmc rendezvous
CMC rendezvous service name: cmc
CMC server:
Server rendezvous enabled: yes
Auto-accept enabled:
no
© 2022 FireEye Security Holdings US LLC
585
Central Management System Administration Guide
APPENDIX B: Configuring Network Address Translation (NAT)
Clients waiting approval:
nx-02 (3.3.3.6)
nx-04 (3.3.3.6)
...
cm-hostname (config) # cmc rendezvous server accept client nx-02
cm-hostname (config) # no cmc rendezvous server accept client nx-04
cm-hostname (config) # write memory
Configuring Global Host-Key
Authentication in a NAT Deployment
When global host-key authentication is enforced on the Central Management appliance,
you must obtain the public host key from managed appliance and import it into the
Central Management global host-keys database. This is described in Configuring Secure
Shell (SSH) Authentication on page 553.
The managed appliance host-key string includes its IP address. If the managed appliance
is in an internal network behind a NAT gateway, the IP address in the key string you
obtain from the managed appliance Web UI or CLI must be replaced with the virtual
IP address that is mapped to the managed appliance on the NAT gateway.
Example
In this example, the Email Security — Server Edition appliance is behind the NAT
gateway. Its IP address is 2.2.2.5, and its virtual IP address is 3.3.3.5.
The host-key string you obtain from the appliance Web UI or CLI starts with "2.2.2.5". For
example:
2.2.2.5 ssh-rsa BEWDS4d65dj/T29+6a38loABAAABAQDZZJLE/ftkUddyNW6KdqEQXjS0Pjb
tzTn3OB51Qg0fdeQHrJgFHM2/4C9WtDkwuX5jd7gdWnSWYwrXDv657thlyRPIt4Wxjf0bpOolPKAe
...
Before you import the host-key into the Central Management global host-keys database,
you must replace "2.2.2.5" with "3.3.3.5." For example:
3.3.3.5 ssh-rsa BEWDS4d65dj/T29+6a38loABAAABAQDZZJLE/ftkUddyNW6KdqEQXjS0Pjb
tzTn3OB51Qg0fdeQHrJgFHM2/4C9WtDkwuX5jd7gdWnSWYwrXDv657thlyRPIt4Wxjf0bpOolPKAe
...
586
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Configuring Global Host-Key Authentication in a NAT Deployment
NOTE: This example is from an Email Security — Server Edition appliance, but it is
representative of CM appliances as well.
© 2022 FireEye Security Holdings US LLC
587
Central Management System Administration Guide
588
APPENDIX B: Configuring Network Address Translation (NAT)
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
About CM Peer Service
APPENDIX C: Configuring the
CM Peer Service
This appendix describes how to configure the CM Peer Service, and addresses the
following topics:
l
About CM Peer Service below
l
Enabling or Disabling the CM Peer Service on page 591
l
Generating and Importing Authentication Tokens Between CM Peers on page 593
l
Enabling or Disabling All the Features of the CM Peer Service on the Peers on
page 598
l
CM Peer Distributed Correlation on page 601
l
CM Peer Signature Sharing on page 605
l
Allowing or Preventing a CM Peer to Use a Proxy Server on page 608
About CM Peer Service
Large enterprise customers often use separate networks where each network is managed by
a separate Central Management appliance and a separate team within the enterprise. For
instance, one enterprise might configure their network into email and Web networks, where
the email team manages all Email Security — Server Edition appliances, and the Web team
manages all Network Security appliances. Another enterprise might use geographically
distributed Central Management networks (for example, US, EU, APAC).
Customers can benefit from using the CM Peer Service when they have multiple Central
Management appliances that are managing multiple appliances as independent groups
within the same environment. The CM Peer Service enables two Central Management
appliances to communicate with each other to share local detection information, such as
Network Security and Email Security — Server Edition URL correlation and locally
generated signatures.
© 2022 FireEye Security Holdings US LLC
589
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
The CM Peer Service provides a backbone to connect distributed Central Management
networks. It enables two-way (CM-to-CM) interactions that allow enterprises to share vital
information, such as alerts and signatures, between two or more separate Central
Management networks. The CM Peer Service is used when one or more Central
Management appliances are managing different appliances.
The following diagram shows how the CM Peer Service is configured for two separate
Central Management networks on a WAN. The CM Peer Service supports both LANs and
WANs.
When the CM Peer Service is enabled, you can access the following features:
l
l
l
CM Peer Distributed Correlation—Enables CM peers in one network to correlate
email events detected by their Email Security — Server Edition appliance with
malicious URLs detected by the Network Security appliance that is managed by
CM peers in a different network. For details about the CM Peer Distributed
Correlation feature, see CM Peer Distributed Correlation on page 601.
CM Peer Signature Sharing— Allows CM peers to share locally generated signatures
with remote CM peers. For details about the CM Peer Signature Sharing feature, see
CM Peer Signature Sharing on page 605.
CM Peer Update—Sends the new primary node's address information to the original
primary node's peer after a failover. This feature allows seamless routing to the new
primary node peer, and it is used in a Central Management High Availability (HA)
configuration.
IMPORTANT: The CM Peer Distributed Correlation and CM Peer Signature
Sharing features must both be enabled when one Central Management platform
manages both the Network Security and Email Security — Server Edition
appliances. Otherwise, you need to enable only CM Peer Signature Sharing.
For information on how the CM Peer Service (and associated features) works in a Central
Management HA configuration, refer to the Central Management High Availability Guide.
Task List for Configuring the CM Peer Service
Complete the steps for configuring the CM Peer Service in the following order:
590
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling the CM Peer Service
1. Log in to the CLI.
2. Enable the CM Peer Service on each of the participating Central Management
appliances. For details about how to enable the peer service, see Enabling or
Disabling the CM Peer Service below.
3. Generate and import authentication tokens to provide communication between CM
peers. You must configure at least one relationship with two CM peers. Each peer
must import a unique authentication token from every other CM peer. For details
about how to generate and import authentication tokens, see Generating and
Importing Authentication Tokens Between CM Peers on page 593.
4. Enable the CM Peer Distributed Correlation and CM Peer Signature Sharing features
of the CM Peer Service on each CM peer. For details about how to enable all the
features on each CM peer, see Enabling or Disabling All the Features of the CM Peer
Service on the Peers on page 598.
5. Enable the malware-object notification setting on all the CM peers. For details about
how to configure event notifications, see Event Notifications on page 285.
6. Enable the local signature generation settings on all the CM peers. Use the localsig
enable command.
7. Verify the details for all the connected CM peers. For details about how to verify the
details of the CM Peer Service on each peer, see Enabling or Disabling All the
Features of the CM Peer Service on the Peers on page 598.
Enabling or Disabling the CM Peer
Service
Use the CLI commands to enable or disable the CM Peer Service on each of the
participating Central Management appliances. When you disable the CM Peer Service on a
Central Management appliance, it can no longer interact with other CM peers.
NOTE: You can enable or disable CM Peer Service only using the CLI. CM Peer
Service is enabled by default.
IMPORTANT: You cannot make configuration changes when the CM Peer
Service is disabled. If you want to make peer service configuration changes and
enable the CM Peer Service later, use the cms peer-service enable command
later.
© 2022 FireEye Security Holdings US LLC
591
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
Enabling or Disabling the CM Peer Service Using the CLI
Follow these steps to enable or disable the CM Peer Service using the CLI.
To enable the CM Peer Service:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Enable CM Peer Service on the platform.
CMS1 (config) # cms feature peer-service enable
3. Verify the status of the CM Peer Service.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
4. Repeat this procedure for each CM peer.
To disable the CM Peer Service:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Disable CM Peer Service on the Central Management appliance.
CMS1 (config) # no cms feature peer-service enable
3. Verify the status of the CM Peer Service.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
no
4. Repeat this procedure for each CM peer.
592
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Importing Authentication Tokens Between CM Peers
Generating and Importing Authentication
Tokens Between CM Peers
Every CM peer has its own unique CM Peer Service authentication token (auth-token). The
token is required for communication with each peer based on the following secure
interactions:
l
l
Authentication—Authenticates each CM peer based on public or private keys.
Authorization—Authorizes each peer to access only the CM Peer Service on the
local system. All other management access is protected. In addition, each peer's
access is limited to specific features that are enabled locally for that peer through the
CM Peer Service interface.
l
Confidentiality—Provides encryption for all CM Peer Service communications.
l
Integrity—Provides communication integrity.
In order for the CM peers to interact, each peer that wants to participate in the CM Peer
Service must import the unique authentication token from the other CM peers.
When a peer’s authentication token is imported, the peer is approved for CM Peer Service
(and associated features) with your Central Management appliance. Importing a token is
similar to creating an account. Therefore, the token must be from a trusted source that is
authenticated with a secure out-of-band mechanism. For example, if the token is sent in a
signed email, the sender of the email can be validated to be the administrator of the
originating CM peer.
After the token is generated, it can be reused for the token exchange with all other peers.
Trellix recommends that you reuse the same token for each exchange. If you generate a
new token, it must be reimported on all the other participating CM peers to resume CM
Peer Service functionality.
IMPORTANT: If you change the hostname or IP address of any CM peer, you
must generate a new token for that CM peer and import it on all the peers of that
Central Management network.
NOTE: You can generate and import authentication tokens only using the CLI.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
© 2022 FireEye Security Holdings US LLC
593
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
l
Each CM peer must have a unique hostname.
l
CM Peer Service must be enabled on your Central Management appliance.
Generating and Importing Tokens for CM Peers Using the
CLI
Use the CLI commands to generate and import authentication tokens for CM peers. This
section describes how to configure a single relationship with two CM peers. In this
example, CM peer 1 (CMS1) is administered by Admin1 and CM peer 2 (CMS2) is
administered by Admin2.
IMPORTANT: After you import the token, a CM peer is able to interact with the
CM Peer Service on your Central Management appliance. The hostname of the
CM peer is automatically used as the name of the peer, and the IP address is
determined by the value of the token. All CM peers must have unique IP addresses
and hostnames.
NOTE: You can export an existing token from a CM peer if you do not want to
generate a new token. For details about how to export an existing authentication
token, see Exporting an Existing Token from a CM Peer Using the CLI on
page 597.
When you import the token, a CM peer is disabled, by default, while the features
are enabled by default.
To generate an authentication token for a CM peer:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. (Admin1) Generate an authentication token. Partial output of the generated token is
displayed.
CMS1 (config) # cms peer-service auth-token generate
AUTH-TOKEN = "PD94bWwg.........."
AUTH-TOKEN CHECKSUM = "cc47ba112df7e0743a41761491435ffb"
.
.
.
3. (Admin1) Copy all the characters within the quotes, but do not copy the quotes,
from the generated auth-token.
594
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Importing Authentication Tokens Between CM Peers
4. (Admin1) Paste the token of CMS1 to an out-of-band mechanism (for example, a
signed email).
5. (Admin1) Send the generated token of CMS1 to Admin2 through a secure out-ofband mechanism (for example, a signed email).
To import an authentication token for peer setup:
1. Go to CLI configuration mode.
CMS2 > enable
CMS2 # configure terminal
2. (Admin2) Import the authentication token from CMS1. Paste the generated token of
CMS1 on the same line as the command.
CMS2 (config) # cms peer-service auth-token import <CMS_peer_one_token>
NOTE: The actual hostname of CMS1 is automatically used after the token
has been imported.
3. (Admin2) Generate an authentication token for CMS2.
CMS2 (config) # cms peer-service auth-token generate
AUTH-TOKEN = "PD94bWwg.........."
AUTH-TOKEN CHECKSUM = "360a37cc532b9e2e75b674eb3b5fe2e0"
.
.
.
4. (Admin2) Copy all the characters within the quotes, but do not copy the quotes,
from the generated auth-token.
5. (Admin2) Paste the token of CMS2 to an out-of-band mechanism (for example, a
signed email).
6. (Admin2) Send the generated token of CMS2 to Admin1 through a secure out-ofband mechanism (for example, a signed email).
7. (Admin1) Import the authentication token from CMS2. Paste the generated token of
CMS2 on the same line as the command.
CMS1 (config) # cms peer-service auth-token import <CMS_peer_two_token>
NOTE: The actual hostname of the CMS2 is automatically used
after the token has been imported.
8. (Admin1) Verify that CMS1 is connected to CMS2.
CMS1 (config) # show cms peer-service
© 2022 FireEye Security Holdings US LLC
595
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
no
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
.
.
.
-----------------------------------------------------------------------
9. (Admin2) Verify that CMS2 is connected to CMS1.
CMS2 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS1:
Enabled:
no
Hostname:
CMS1
Address:
10.11.121.13
Auth-token checksum:
cc47ba112df7e0743a41761491435ffb
.
.
.
-----------------------------------------------------------------------
NOTE: For multiple CM peers, repeat these steps on each CM peer until all the
authentication tokens are imported on all the peers.
Importing New Tokens for an Existing CM Peer Using the
CLI
Use the CLI commands to import new authentication tokens for an existing CM peer. If
you have already imported the authentication token for an existing peer and you want to
import a new token for that peer, you must delete the connection to the CM peer first before
importing the new token.
596
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Generating and Importing Authentication Tokens Between CM Peers
To import a new authentication token for an existing CM peer:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Delete a CM peer connection.
CMS1 (config) # cms peer <peer_hostname> delete
3. Import the new token from the specified CM peer. Paste the token of the specified
CM peer on the same line as the command.
CMS1 (config) # cms peer-service auth-token import <peer_token>
Exporting an Existing Token from a CM Peer Using the
CLI
Use the CLI commands to export an existing authentication token from a CM peer. Use this
procedure when you want to use an existing token with another CM peer but do not want
to generate a new token. When a token is exported, it is displayed. You can copy the
existing token and send it to the administrator of a CM peer.
To export an existing authentication token with a CM peer:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Export an existing token. Partial output of the existing token is displayed.
CMS1 (config) # cms peer-service auth-token export
AUTH-TOKEN = "PD94bWwg.........."
AUTH-TOKEN CHECKSUM = "234b19a369887ef5b0bbfd269c477704"
.
.
.
3. Copy all the characters of the existing token within the quotes, but do not copy the
quotes, from the exported auth-token.
4. Paste the exported token to an out-of-band mechanism (for example, a signed email).
5. Send the exported token to the administrator of the CM peer.
© 2022 FireEye Security Holdings US LLC
597
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
Enabling or Disabling All the Features of
the CM Peer Service on the Peers
Use the CLI commands in this topic to enable or disable the CM Peer Distributed
Correlation and CM Peer Signature Sharing features of the CM Peer Service on each
CM peer. When you enable each CM peer, all the features are enabled. When you disable
the CM Peer Service, CM peers can no longer interact with your Central
Management appliance. However, you can enable or disable access to the CM Peer
Distributed Correlation and CM Peer Signature Sharing features individually on each
CM peer.
Each administrator must verify the CM Peer Service connection to all CM peers. A status
refresh is triggered in the following instances:
l
l
l
Periodically about every 1 to 5 minutes. Different interactions and different peers
can be refreshed at different 1—minute to 5—minute intervals.
Whenever any peer service configuration changes (for example, a new token is
imported, a feature on a CM peer is disabled, and so on).
When Central Management high availability (HA) failover occurs (when the
secondary node becomes the new primary node). For information about how the CM
Peer Service (and associated features) works in a HA configuration, refer to the
Central Management High Availability Guide.
The status might display "UNKNOWN" temporarily until the status is retrieved at the
beginning of the refresh cycle.
NOTE: You can enable or disable the CM Peer Service features on each CM peer
only using the CLI.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
l
l
598
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
CM Peer Service must be enabled on each of the participating Central Management
appliances.
Authentication tokens must be exchanged for communication between CM peers.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Enabling or Disabling All the Features of the CM Peer Service on the Peers
Enabling or Disabling All the Features of the CM Peer
Service on the Peers Using the CLI
Follow these steps to enable or disable all the features of the CM Peer Service on each CM
peer using the CLI.
To enable all the features of the CM Peer Service:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Enable all the CM Peer Service features on a CM peer.
CMS1 (config) # cms peer <peer_hostname> enable
3. Save your changes.
CMS1 (config) # write memory
4. Repeat this procedure for each CM peer.
5. Verify the status for all the connected CM peers. The following example verifies that
CMS1 is connected to CMS2.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
18:58:51
Dynamic Threat Intelligence (DTI):
Enabled:
no
Proxy mode:
No proxy
Status:
UNKNOWN
@ N/A
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
18:56:30
© 2022 FireEye Security Holdings US LLC
599
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
-----------------------------------------------------------------------
To disable all the features of the CM Peer Service:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Disable all the CM Peer Service features on a CM peer.
CMS1 (config) # no cms peer <peer_hostname> enable
3. Save your changes.
CMS1 (config) # write memory
4. Repeat this procedure for each CM peer.
5. Verify the status for all the CM peers. The following example verifies that CMS1 is
not connected to CMS2.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
no
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
18:58:51
Dynamic Threat Intelligence (DTI):
Enabled:
no
Proxy mode:
No proxy
Status:
UNKNOWN
@ N/A
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
18:58:51
-----------------------------------------------------------------------
600
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
CM Peer Distributed Correlation
Deleting a CM Peer Using the CLI
Follow these steps to delete a CM peer from the Peer Service relationship (not from the
network) using the CLI. All configuration information and data associated with that peer
will be removed, including the IP address and peer name. The CM peer is no longer
connected to the Peer Service. If you want to reconnect to the same peer, you must import
the existing token again.
IMPORTANT: If you delete a CM peer and then want to add the CM peer back, you
must import the token again. For information about how to import a token for an
existing CM peer, see Importing New Tokens for an Existing CM Peer Using the CLI
on page 596.
To delete a CMS peer:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Delete a CMS peer.
CMS1 (config) # cms peer <peer_hostname> delete
3. Save your changes.
CMS1 (config) # write memory
4. Verify that all configuration information associated with that peer is removed. The
following example verifies that all information associated with CMS2 is removed.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
CM Peer Distributed Correlation
CM Peer Distributed Correlation matches events detected by an appliance with events that
are received from a CM peer in another network. CM Peer Distributed Correlation allows
two Central Management networks to share information. Information about a malicious
URL found in one Central Management network is shared with other Central Management
networks.
A typical correlation matches malicious URL events detected by the Network Security
appliance with email events detected by the Email Security — Server Edition appliance.
URL events and email events are linked to each other in the Web UI after they have been
matched. For example, when a malicious URL is detected by the Network Security
appliance, the URL is correlated by the Central Management appliance with the
originating email on the Email Security — Server Edition appliance. For details about
© 2022 FireEye Security Holdings US LLC
601
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
Network Security and Email Security — Server Edition event correlation, see Reviewing
Email Alerts Correlated with Web Events on page 428.
Alert notifications from a CM peer are missing the missing product and version attributes
in the <alert> tag of the notification. When the malware-object notification setting is
enabled on the Central Management appliance, Distributed Cross-CM alert notifications
that contain information about the sender, intended recipient(s), and malicious URL are
sent from the Central Management appliance or managed appliances. For details about
how to manage the distribution of alert notifications for the Central Management appliance
and managed appliances, see Managing the Distribution of Alert Notifications on
page 415.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
l
l
l
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
CM Peer Service must be enabled on each of the participating Central Management
appliances.
Authentication tokens must be exchanged for communication between the
CM peers.
The malware-object notification setting must be enabled on all the CM peers. For
details about how to configure event notifications, see Event Notifications on
page 285.
Enabling or Disabling CM Peer Distributed Correlation
Using the CLI
Follow these steps to enable or disable the CM Peer Distributed Correlation feature on each
CM peer using the CLI.
To enable the CM Peer Distributed Correlation feature:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Enable the CM Peer Distributed Correlation feature on a CM peer.
CMS1 (config) # cms peer <peer_hostname> interaction dist-correlation
enable
3. Save your changes.
602
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
CM Peer Distributed Correlation
CMS1 (config) # write memory
4. Verify the Distributed Correlation status on a CM peer. The following example
verifies that Distributed Correlation is enabled on CMS2.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
18:59:38
Dynamic Threat Intelligence (DTI):
Enabled:
yes
Proxy mode:
No proxy
Status:
OK
@ 2016/01/27
18:59:38
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:02:23
-----------------------------------------------------------------------
To disable the CM Peer Distributed Correlation feature:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Disable the CM Peer Distributed Correlation feature on a CM peer.
CMS1 (config) # no cms peer <peer_hostname> interaction distcorrelation enable
3. Verify the Distributed Correlation status on a CM peer. The following example
verifies that Distributed Correlation is disabled on CMS2.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
© 2022 FireEye Security Holdings US LLC
603
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
no
Status:
UNKNOWN
@ N/A
Dynamic Threat Intelligence (DTI):
Enabled:
yes
Proxy mode:
No proxy
Status:
OK
@ 2016/01/27
18:59:38
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:02:23
-----------------------------------------------------------------------
Viewing CM Peer Distributed Correlation Alerts in the
Web UI
When CM Peer Distributed Correlation is enabled, a globe icon in the URL column on the
Email Security — Server Edition: Email Alerts page indicates that a user clicked a
malicious URL that was detected by a Network Security appliance that was managed by
CM peers.
The Email Alerts page lists the results, grouped by recipient, of the correlated email events
detected by the Email Security — Server Edition appliance in one network with malicious
URLs detected by the Network Security appliance that was managed by a CM peer in a
different network.
604
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
CM Peer Signature Sharing
CM Peer Signature Sharing
The CM Peer Signature Sharing feature allows CM peers to share locally generated
signatures with remote CM peers using the CM Peer Service. When local signature
generation settings are enabled, you can verify the number of active rules that are shared
with local and remote CM peers by using the show localsig command. When CM Peer
Signature Sharing is disabled, local and remote peers do not share locally generated
signatures.
An enterprise customer can have geographically distributed Central Management networks
(for example, US, EU, APAC) with separate Central Management appliances that are all
connected using the CM Peer Service. CM Peer Signature Sharing allows the Central
Management appliance in the Central Management network in the US to share locally
generated signatures with the other platforms in the EU and APAC. When one peered
Central Management network identifies a malicious URL, the signature is shared with all
the other peered Central Management networks. When deployed inline, any appliance in
the EU or APAC automatically blocks a malicious URL identified in the US. Therefore, all
users are protected in all peered Central Management networks.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
l
l
l
l
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
The Network Security appliance must be deployed inline.
CM Peer Service must be enabled on each of the participating Central Management
appliances.
Authentication tokens must be exchanged for communication between the
CM peers.
The local signature generation settings must be enabled on all the CM peers using
the localsig enable command.
Enabling or Disabling CM Peer Signature Sharing Using
the CLI
Follow these steps to enable or disable DTI interaction between CM peers for CM Peer
Signature Sharing using the CLI.
© 2022 FireEye Security Holdings US LLC
605
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
To enable CM Peer Signature Sharing:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Generate a key file to enable DTI interaction between CM peers to share locally
generated signatures with remote CM peers.
CMS1 (config) # cms peer <peer_hostname> interaction dti enable
3. Save your changes.
CMS1 (config) # write memory
4. Verify the DTI interaction status with a CM peer for CM Peer Signature Sharing. The
following example verifies that DTI interaction with CMS2 is enabled for CM Peer
Signature Sharing.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
Dynamic Threat Intelligence (DTI):
Enabled:
yes
Proxy mode:
No proxy
Status:
OK
@ 2016/01/27
19:07:26
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
-----------------------------------------------------------------------
To disable DTI interaction with a CM peer for CM Peer Signature Sharing:
1. Go to CLI configuration mode.
CMS1 > enable
606
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
CM Peer Signature Sharing
CMS1 # configure terminal
2. Disable DTI interaction with a CM peer for CM Peer Signature Sharing.
CMS1 (config) # no cms peer <peer_hostname> interaction dti enable
3. Save your changes.
CMS1 (config) # write memory
4. Verify the DTI interaction status with a CM peer for CM Peer Signature Sharing. The
following example verifies that DTI interaction with CMS2 is disabled for CM Peer
Signature Sharing.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
Dynamic Threat Intelligence (DTI):
Enabled:
no
Proxy mode:
No proxy
Status:
UNKNOWN
@ N/A
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
-----------------------------------------------------------------------
Viewing the Number of Rules for CM Peer Signature
Sharing Using the CLI
Follow these steps to view the number of active rules that are shared between local and
remote CM peers for CM Peer Signature Sharing using the CLI.
© 2022 FireEye Security Holdings US LLC
607
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
NOTE: When the DTI feature is enabled, there will be a slight discrepancy in the
Active rules value in the show localsig command output. This discrepancy is
due to the way data is aggregated and synchronized.
To view the number of active rules for CM Peer Signature Sharing:
1. Go to CLI enable mode.
CMS1 > enable
2. Verify the number of active rules that are shared between CM peers.
CMS1 > show localsig
LocalSig Generator
Enabled : YES
Running : running
Rule Versions : 1
Active rules : 1337
LocalFeed : Disabled
Allowing or Preventing a CM Peer to Use
a Proxy Server
Use the CLI commands to allow or prevent a CM peer to use a proxy server to connect to
other remote CM peers. If you allow a CM peer to use a proxy server, the proxy settings
will be the same as those configured for DTI interaction to connect to other remote CM
peers. By default, a CM peer does not use a proxy server to connect to other remote peers.
NOTE: You can allow or prevent a CM peer to use a proxy server only using the
CLI.
Prerequisites
l
Admin access to the Central Management appliance.
l
A connection to the Dynamic Threat Intelligence (DTI) Cloud.
l
l
l
608
Network connectivity over SSH (port 22) and HTTPS (port 443) must be allowed on
each of the participating Central Management appliances.
CM Peer Service must be enabled on each of the participating Central Management
appliances.
Authentication tokens must be exchanged for communication between the
CM peers.
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Allowing or Preventing a CM Peer to Use a Proxy Server
Allowing or Preventing a CM Peer to Use a Proxy Server
Using the CLI
Follow these steps to allow or to prevent a CM peer to use a proxy server to connect to
other remote CM peers.
To allow a CM peer to use a proxy server:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Identify a CM peer to use the same proxy server settings that are configured for DTI
interaction to connect to other remote CM peers.
CMS1 (config) # cms peer <peer_hostname> interaction dti proxy mode
use-fenet
3. Save your changes.
CMS1 (config) # write memory
4. Verify the proxy server status on a CM peer. The following example verifies that
CMS2 is allowed to use a proxy server.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
Status:
19:12:59
yes
OK
@ 2016/01/27
Dynamic Threat Intelligence (DTI):
Enabled:
yes
Proxy mode:
Use FENET proxy settings
Status:
OK
@ 2016/01/27
19:12:59
Update Peer:
Enabled:
© 2022 FireEye Security Holdings US LLC
yes
609
Central Management System Administration Guide
APPENDIX C: Configuring the CM Peer Service
Status:
OK
@ 2016/01/27
19:12:59
-----------------------------------------------------------------------
To prevent a CM peer from using a proxy server:
1. Go to CLI configuration mode.
CMS1 > enable
CMS1 # configure terminal
2. Prevent a CM peer from using any proxy server to connect to other remote CM peers
for DTI interaction.
CMS1 (config) # cms peer <peer_hostname> interaction dti proxy mode noproxy
3. Save your changes.
CMS1 (config) # write memory
4. Verify the proxy server status on a CM peer. The following example verifies that
CMS2 is not allowed to use a proxy server.
CMS1 (config) # show cms peer-service
CMS peer-service enabled:
yes
----------------------------------------------------------------------CMS peer CMS2:
Enabled:
yes
Hostname:
CMS2
Address:
172.16.216.51
Auth-token checksum:
360a37cc532b9e2e75b674eb3b5fe2e0
Interactions with peer:
Distributed CMS Correlation:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
Dynamic Threat Intelligence (DTI):
Enabled:
yes
Proxy mode:
No proxy
Status:
OK
@ 2016/01/27
19:07:26
Update Peer:
Enabled:
yes
Status:
OK
@ 2016/01/27
19:07:26
-----------------------------------------------------------------------
610
© 2022 FireEye Security Holdings US LLC
Central Management System Administration Guide
Enabling the ETP Cloud Endpoint Using the CLI
APPENDIX D: Monitoring Email
Alerts from the Email Security Cloud Edition
You can configure the Central Management Appliance Dashboard to monitor email alerts
from the Email Security Cloud.
On the Central Management appliance, you need a license with your client ID. To see if it
is configured, log in to your Central Management appliance and look for Customer ID
(under the username drop-down) in the Web UI, or enter the show version command in
the CLI.
If you do not have a customer ID, contact FireEye Support.
The protocol is Web Socket over TLS using port 443.
The access points are us1.fireeyecloud.com and us2.fireeyecloud.com. These are both
needed and back each other up.
The Central Management appliance has a 1-hour idle connection timeout and
therefore will disconnect from ETP occasionally.
Enabling the ETP Cloud Endpoint Using
the CLI
The ETP Cloud endpoint has to be enabled before the Central Management appliance can
monitor alerts from ETP Cloud. The following are the CLI provisioning commands to enter
from the CLI. You will create two access points using the destination URLs, (one endpoint
and the URL). You will specify a nickname, such as, "email-server" and specify the URL.
The nickname you define for the access point has local significance, so you can use
whatever you like as long as it is consistent.
© 2022 FireEye Security Holdings US LLC
611
Central Management System Administration
Guide
APPENDIX D: Monitoring Email Alerts from the Email Security - Cloud
Edition
To enable the ETP endpoint:
1. Go to CLI configuration mode:
cm-1 > enable
cm-1 # configure terminal
2. Specify the endpoint name and access point:
cm-1 (config) # cloud etp endpoint <etp-endpoint-name> uri <cloud etp
uri>
3. If you are prompted, enter your username and password:
cm-1 (config) # cloud etp endpoint <etp-endpoint-name> username <fenet_
username> password <fenet_password>
4. Enable the endpoint:
cm-1 (config) # cloud etp endpoint <etp-endpoint-name> enable
5. Save your changes:
cm-1 (config) # write memory
6. Verify the configuration:
cm-1 (config) # show cloud etp status
Endpoint: everest:
Address:
wss://iad-cc-api-vip-stage1.cso.fireeye.com:443
Enabled:
yes
JobWorker Connected:
yes
NotifHandler Connected: yes
7. To show the configured ETP instances:
cm-1 (config) # show cloud etp configuration
To remove the configuration and all its associated objects and alerts from the CM:
cm-1 (config) # no cloud etp endpoint <etp-endpoint-name>
ETP Cloud Aggregation
An aggregator process receives data from the ETP Cloud and aggregates it into the Central
Management appliance database for display on the Central Management appliance Web
UI.
To display the configuration of the aggregator:
cm-1 (config) # show aggregator configuration
To display the configuration of the aggregator endpoints:
cm-1 (config) # show aggregator endpoints configuration
612
© 2022 FireEye Security Holdings US LLC
Release 9.1.4
Viewing Email Alerts from the ETP Cloud in the Web UI
Solving Connection Issues
The following commands are usedto troubleshoot connection issues and used only when
asked to do so by FireEye Support.
To enable/disable SSL certification verification in the aggregator:
cm-1 (config) # [no] aggregator ssl cert-verify
To set the aggregator log level:
cm-1 (config) # aggregator consumer logging level
[debug|info|notice|warning|error]
To set the SSL cipher list to use with the WebSocket connection:
cm-1 (config) # aggregator ssl cipher-list
To set the minimum TLS version to use with the WebSocket connection:
cm-1 (config) # aggregator ssl min-version
Viewing Email Alerts from the ETP Cloud
in the Web UI
On the Central Management appliance Dashboard, you can select ETP from the All
Groups menu or an ETP instance from the All Appliances menu.
For the selected groups and instances, you can view:
l
Total Malicious emails
l
Malicious URLs
l
Malicious Attachments
l
ETP Alerts
You can view email alerts on the Central Management Dashboard by going to the Alerts
tab and selecting one of the categories displayed under What's Happening:
© 2022 FireEye Security Holdings US LLC
613
Central Management System Administration
Guide
APPENDIX D: Monitoring Email Alerts from the Email Security - Cloud
Edition
You can view detailed status of the ETP instance's connection by selecting an instance
from the All Appliances drop-down to view the Summary. Note that ETP Cloud instances
are not listed on the Appliances tab:
614
© 2022 FireEye Security Holdings US LLC
Technical Support
For technical support, contact Trellix through the Support portal:
https://csportal.fireeye.com
Documentation
Documentation for all FireEye products is available on the FireEye Documentation Portal
(login required):
https://docs.fireeye.com/
© 2022 FireEye Security Holdings US LLC
615
Trellix | 601 McCarthy Blvd. | Milpitas, CA | 1.408.321.6300 | 1.877.FIREEYE | www.fireeye.com
© 2022 FireEye Security Holdings US LLC. All rights reserved.Trellix, FireEye, and Skyhigh Security are the trademarks or
registered trademarks of Musarubra US LLC, FireEye Security Holdings US LLC, and their affiliates in the US and/or other
countries.